Reconnaissance Tools
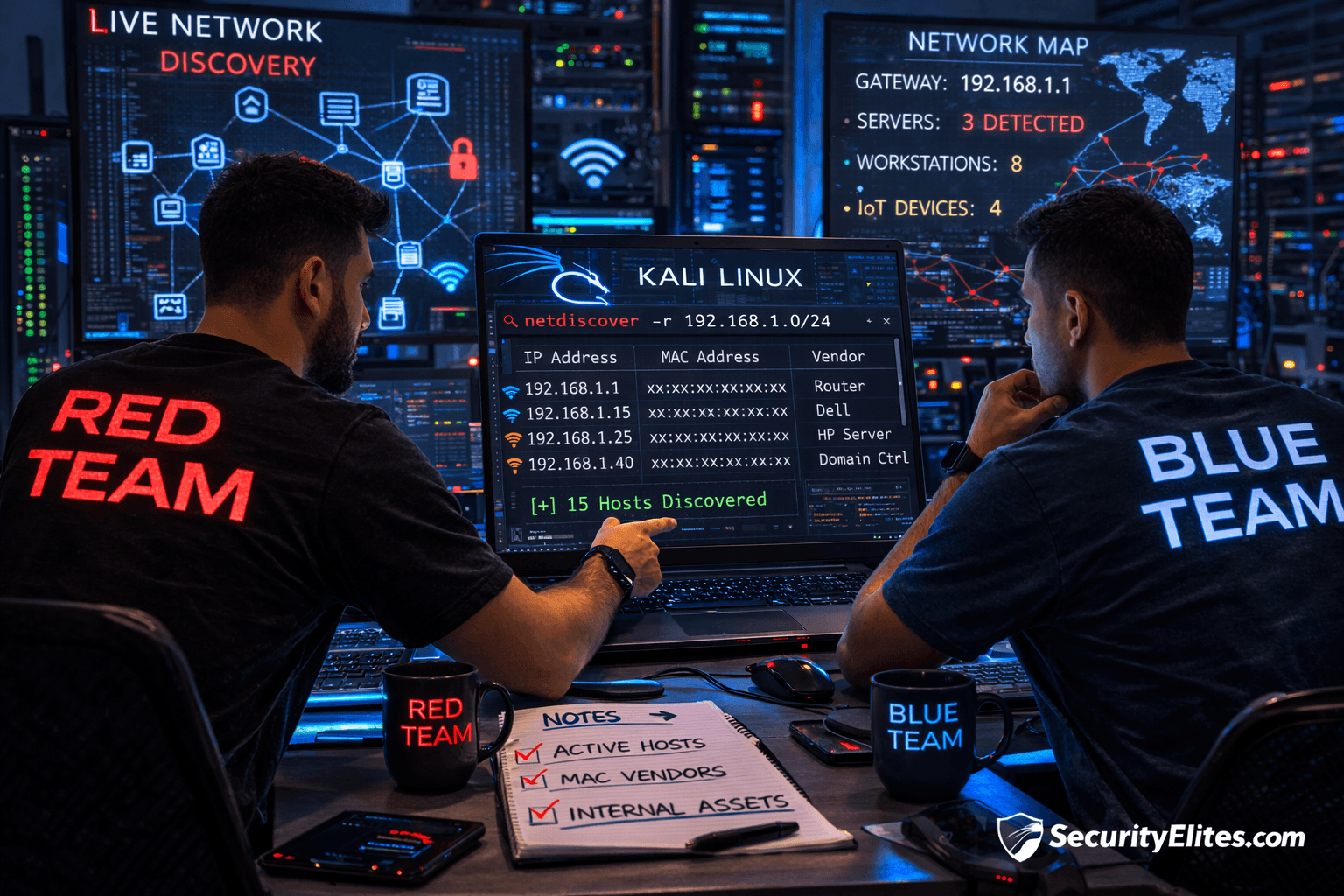
econnaissance tools for hacking are essential in the information-gathering phase of ethical hacking and penetration testing. In this section, you will explore powerful reconnaissance tools used to discover domains, subdomains, IP addresses, exposed services, and publicly available data. Tutorials cover tools like Nmap, Amass, Sublist3r, theHarvester, and Shodan with step-by-step setup and usage guides. Each article explains how security professionals map attack surfaces, automate recon workflows, and interpret scanning results safely. You will also learn how organizations defend against reconnaissance attempts and reduce information exposure. This category is ideal for bug bounty hunters, penetration testers, and cyber security students building their toolkit.
38 articles
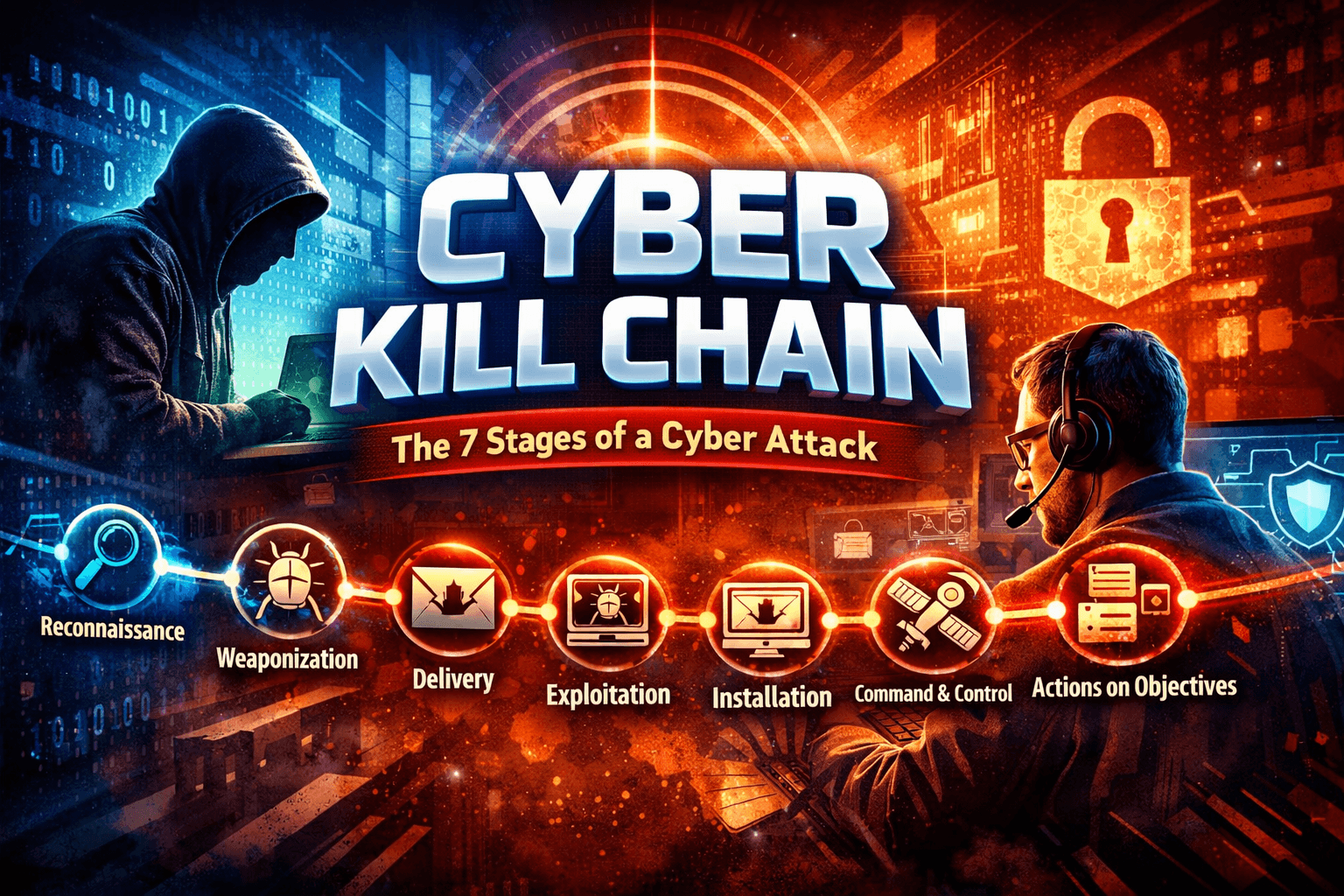
Cyber Kill Chain Explained: 7 Stages of a Cyber Attack
Learn the Cyber Kill Chain explained with ethical hacking examples, attacker mindset, hands-on labs, and defense strategies.
Information Gathering Using Kali Linux Day 8: Attack Surface Mapping with Amass
Information Gathering Using Kali Linux Day 8 - Learn Information Gathering using Kali Linux with Amass step-by-step. Discover hidden domains…
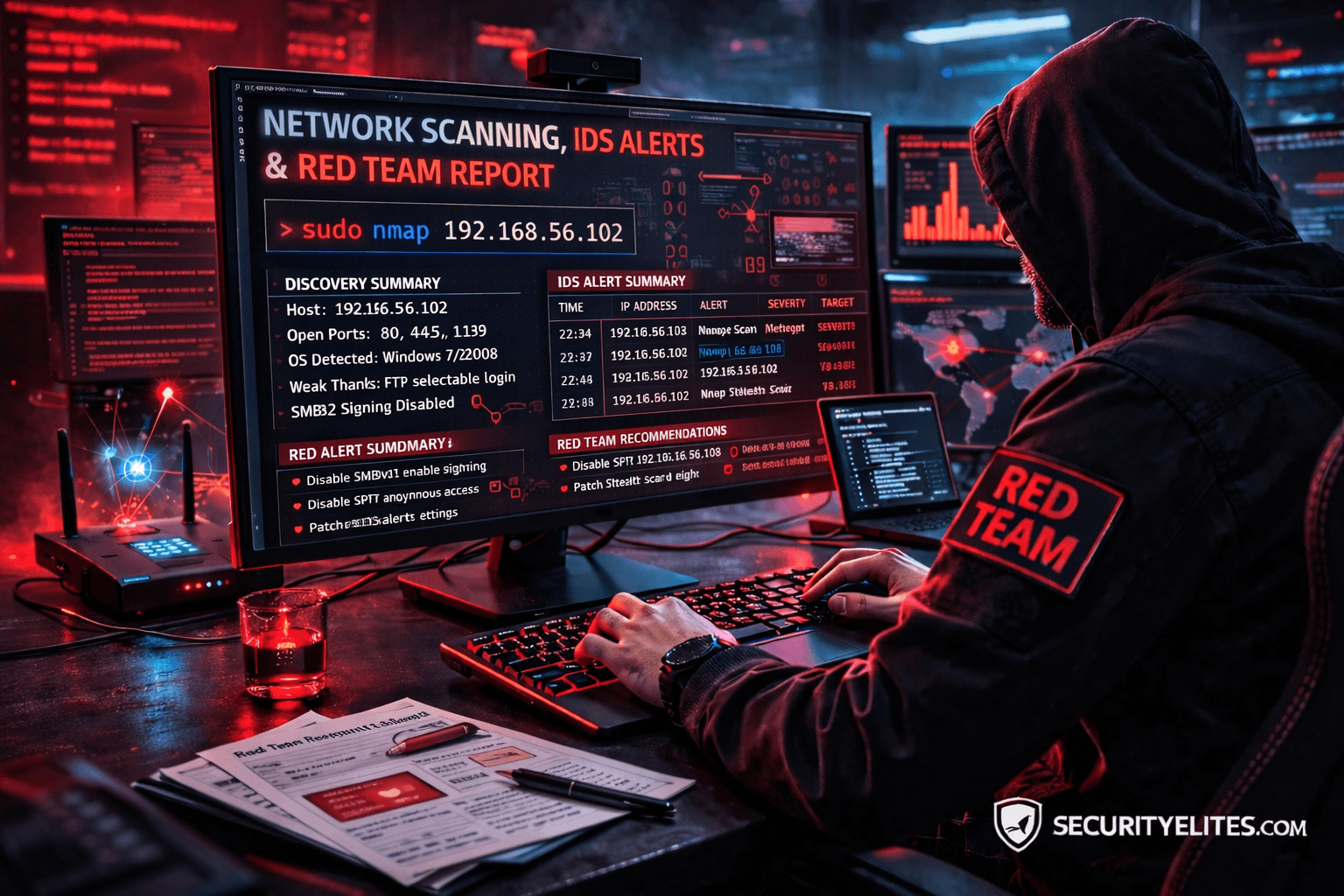
Network Scanning Tutorial Using Nmap Day 7 — Stealth Scanning, IDS Evasion & Red Team Techniques
Network Scanning Tutorial Using Nmap Day 7 - Learn stealth scanning, IDS evasion, and advanced Red Team Nmap techniques used…
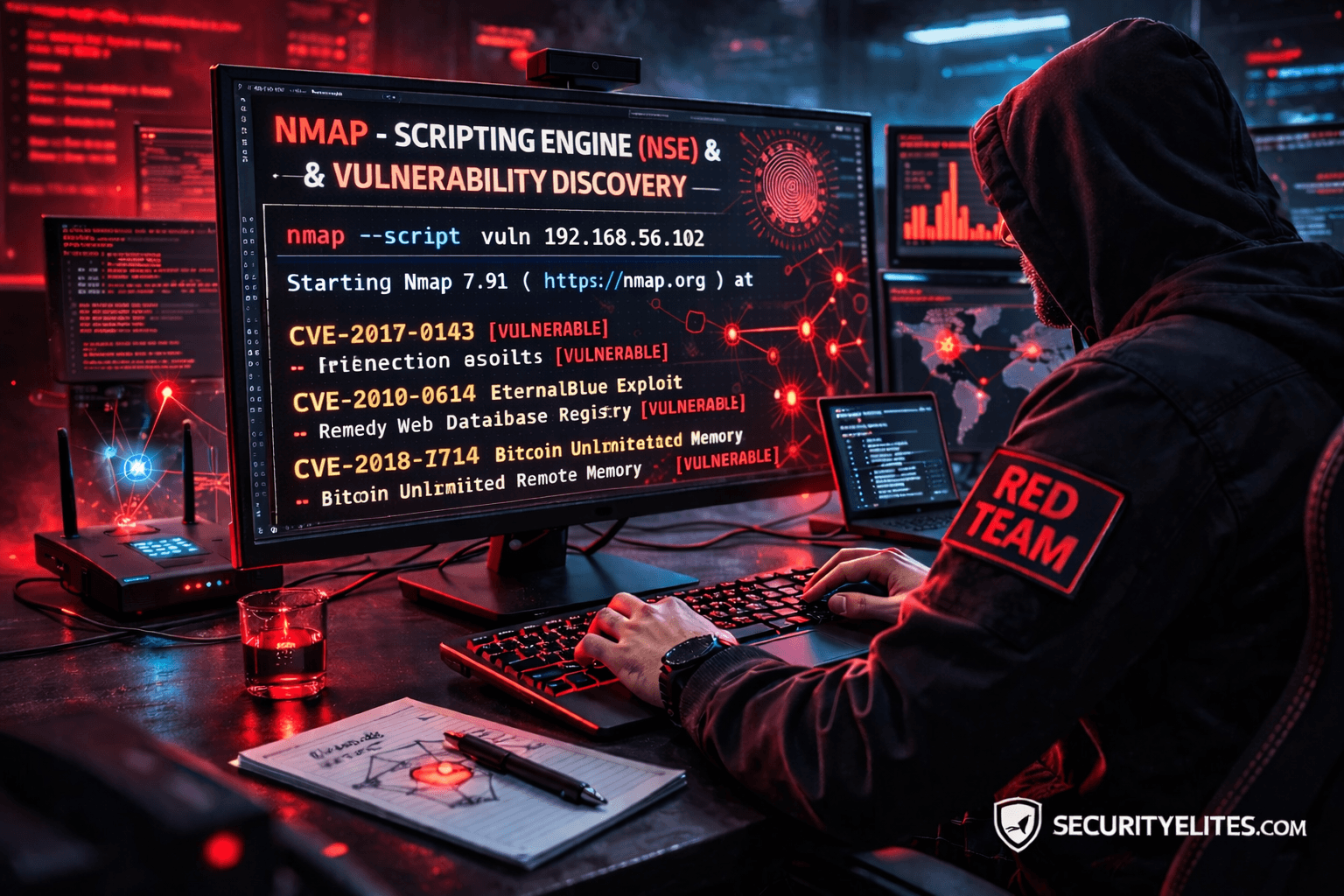
Network Scanning Tutorial Using Nmap Day 6— Nmap Scripting Engine (NSE) & Vulnerability Discovery
Network Scanning Tutorial Using Nmap Day 6 - Learn Nmap Scripting Engine (NSE) for vulnerability discovery and automated reconnaissance. Day…
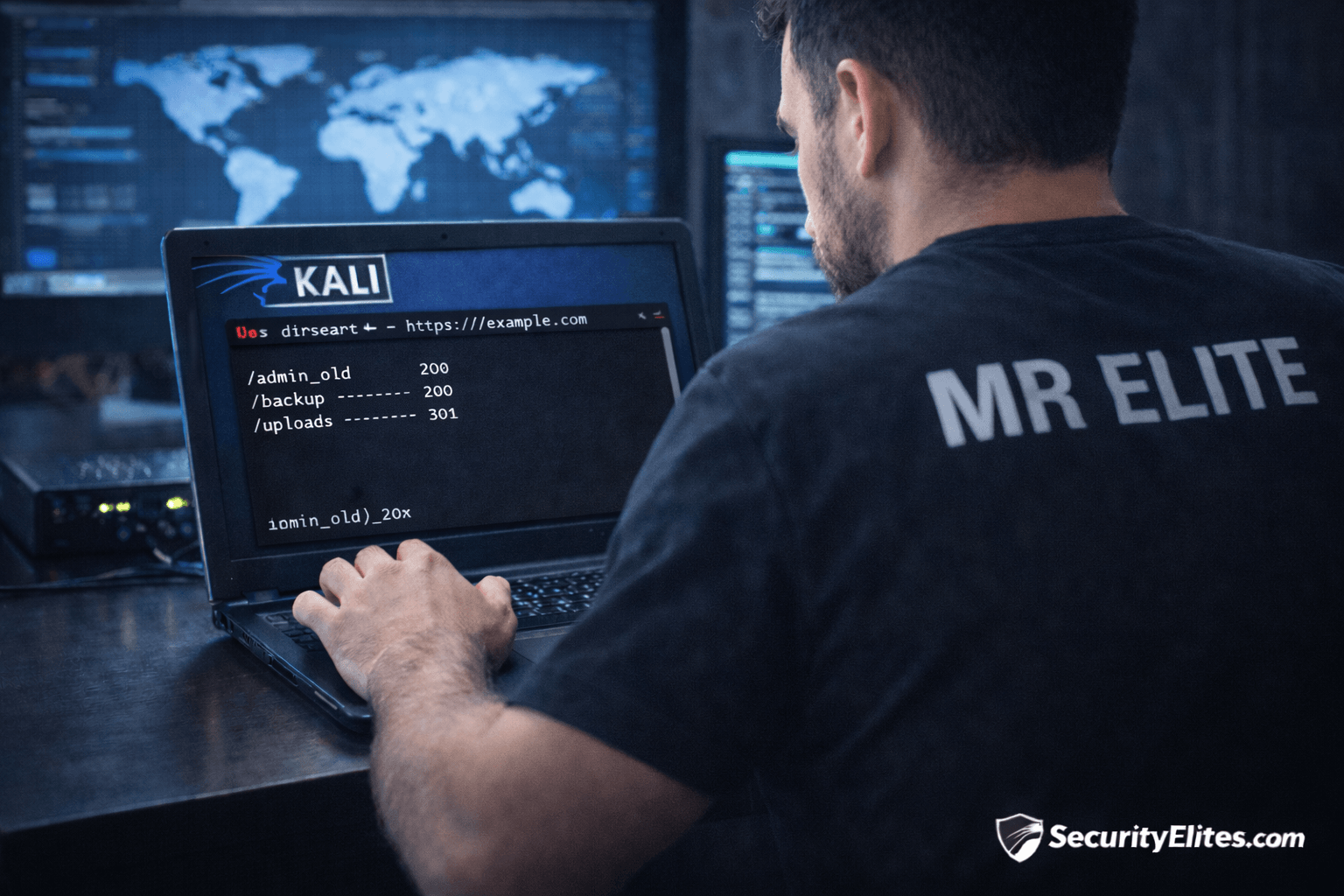
Information Gathering Using Kali Linux Day 7: Directory Discovery with Dirsearch
Information Gathering Using Kali Linux Day 7 - Learn Information Gathering using Kali Linux with Dirsearch step-by-step. Discover hidden directories…
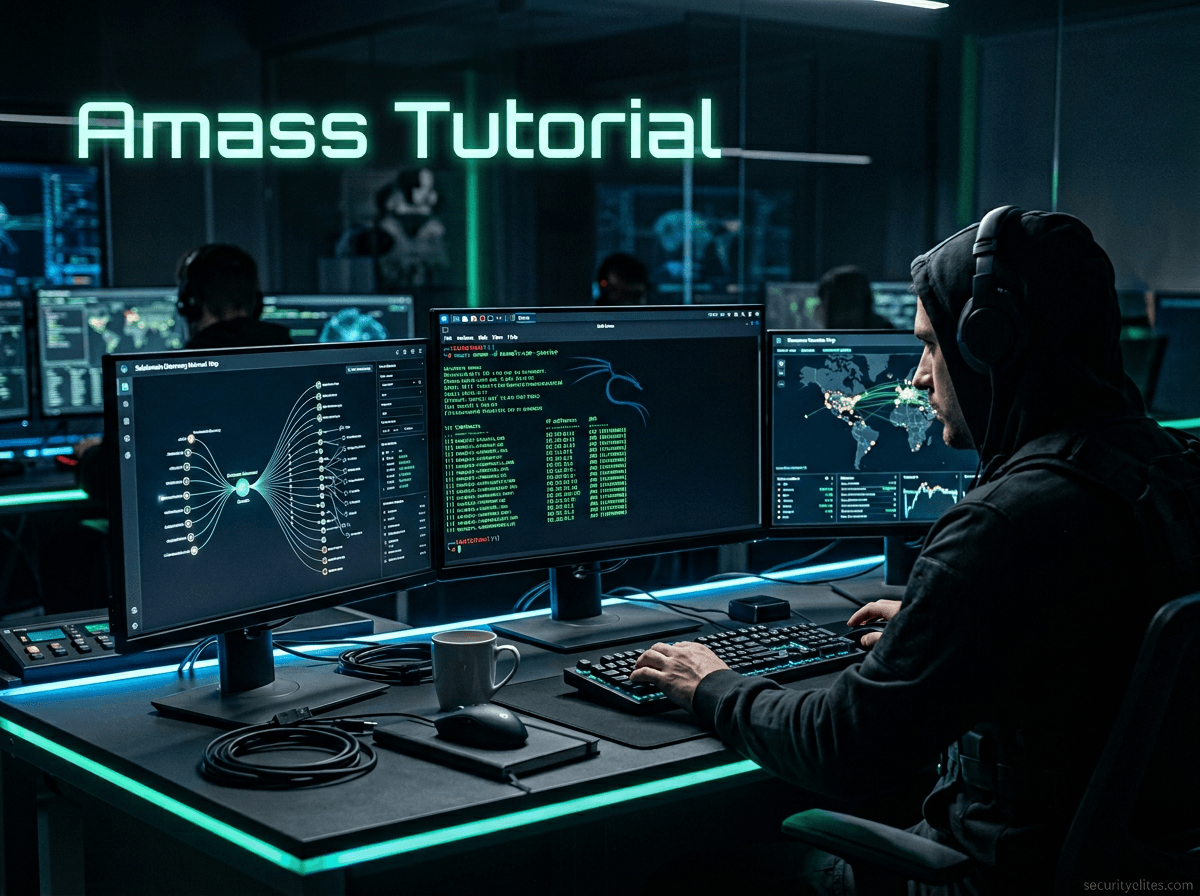
Amass Tutorial (2026): Powerful Subdomain Enumeration Guide for Kali Linux
Learn Amass tutorial for subdomain enumeration and reconnaissance in Kali Linux. Step-by-step ethical hacking guide used by penetration testers and…
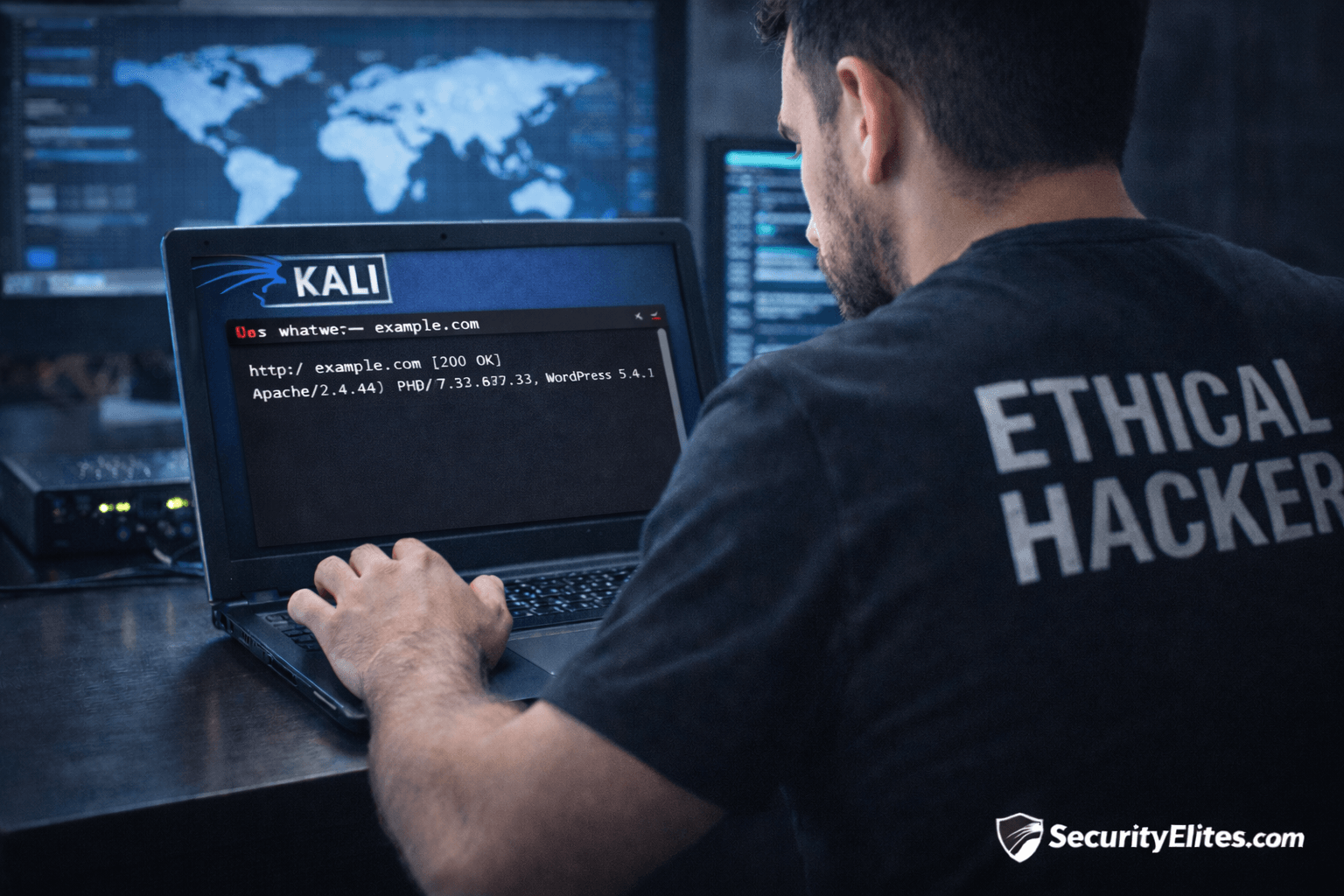
Information Gathering Using Kali Linux Day 6: Technology Fingerprinting with WhatWeb
Information Gathering Using Kali Linux Day 6 - Learn Information Gathering using Kali Linux with WhatWeb step-by-step. Detect website technologies,…
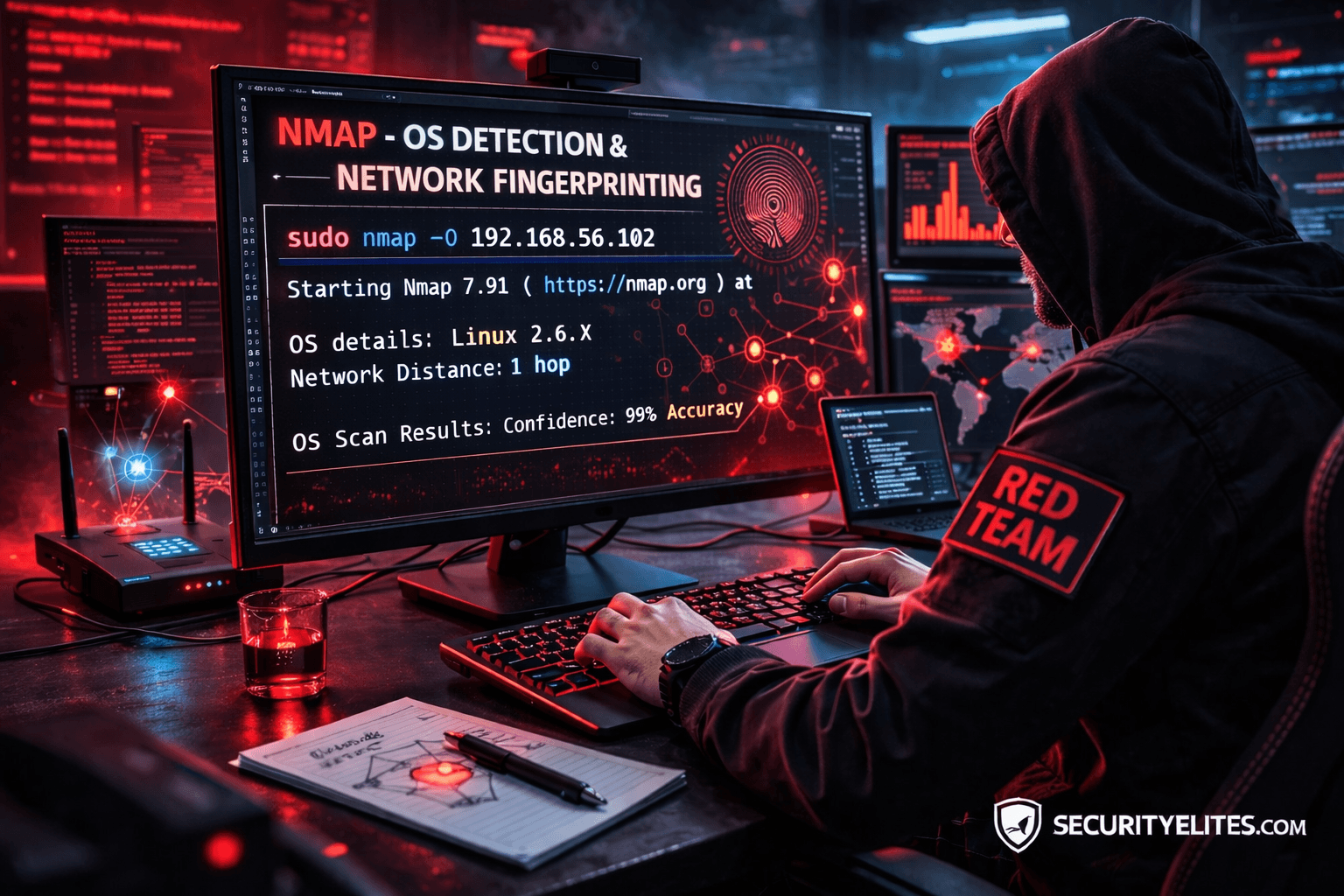
Network Scanning Tutorial Using Nmap Day 5— OS Detection & Network Fingerprinting (Professional Level)
Network Scanning Tutorial Using Nmap Day 5 - Learn operating system detection and network fingerprinting using Nmap like professional penetration…
Claude AI Kali Linux MCP Penetration Testing: 7 Powerful AI Automation Techniques
Learn Claude AI Kali Linux MCP Penetration Testing automation with a step-by-step guide. Discover how AI runs Nmap, Gobuster, and…