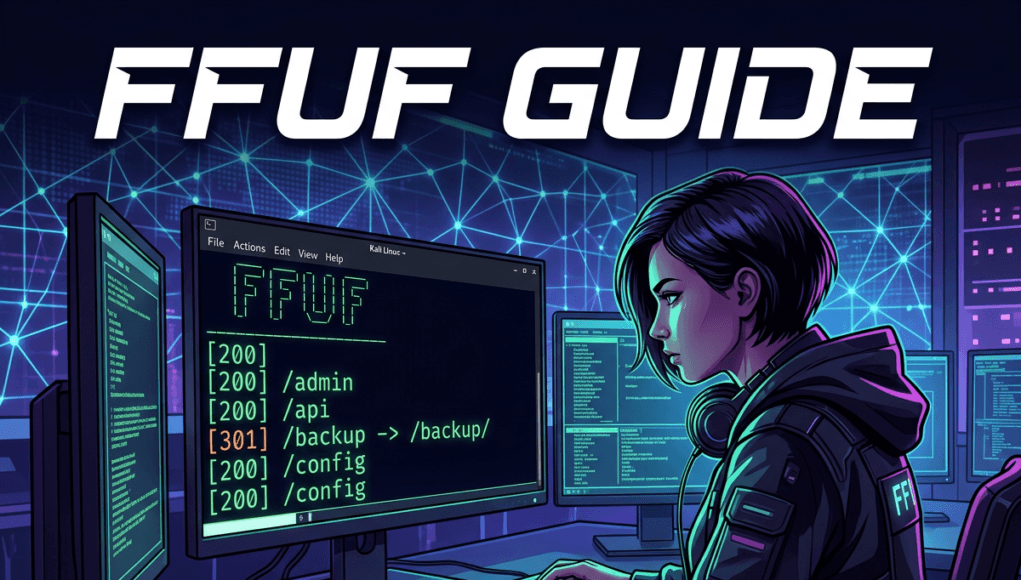
This FFUF Guide explains how ethical hackers use FFUF (Fuzz Faster U Fool) to discover hidden directories, files, parameters, and endpoints on web servers. FFUF is a web fuzzing tool used in penetration testing and bug bounty hunting to automatically test thousands of possible URLs against a website.
In simple terms, FFUF tries many possible paths like /admin, /backup, /config, or /login to see which ones actually exist on the server. These hidden paths may contain sensitive information, developer panels, or misconfigured applications.
Ethical hackers use FFUF during web reconnaissance and attack surface discovery to identify hidden resources that normal users cannot see. This FFUF Guide helps cybersecurity beginners learn how attackers discover hidden web infrastructure and how defenders detect and stop fuzzing attacks.
This FFUF Guide teaches beginners how to use FFUF safely in Kali Linux labs while understanding how attackers think during reconnaissance.
Table of Contents
Core Concept – Understanding FFUF
To understand this FFUF Guide, we must first understand what web fuzzing means in cybersecurity.
Web applications are made of many directories, files, APIs, and internal tools. When users visit a website, they only see the pages linked in the navigation menu.
Example:
https://example.com
Users may see:
/home
/about
/blog
/contact
But websites often contain hidden directories that are not visible to normal users.
Examples include:
/admin
/dev
/staging
/api
/test
/backup
/config
These directories may exist because developers created them during development or forgot to remove them.
FFUF is one of the most popular web fuzzing tools used in penetration testing. It is widely used by ethical hackers and bug bounty hunters because of its speed and flexibility. The official documentation for the FFUF tool can be found on the FFUF GitHub repository, which explains installation, configuration, and advanced fuzzing techniques.
This FFUF Guide focuses on discovering these hidden paths using automation.
Why Hidden Directories Exist ?
Modern web applications are extremely complex.
Large companies may run hundreds of internal tools.
Examples include:
• developer dashboards
• testing environments
• backup storage
• debug pages
• internal APIs
Sometimes these resources remain publicly accessible by mistake.
This is where this FFUF Guide becomes important.
Ethical hackers use FFUF to discover these hidden resources before attackers exploit them.
How FFUF Works
This FFUF Guide teaches that FFUF works by replacing a placeholder called FUZZ with words from a wordlist.
Example URL:
https://target.com/FUZZ
If the wordlist contains:
admin
login
backup
api
dashboard
FFUF will automatically test:
https://target.com/admin
https://target.com/login
https://target.com/backup
https://target.com/api
https://target.com/dashboard
The tool sends thousands of requests and analyzes server responses.
Example responses:
| Response | Meaning |
|---|---|
| 200 | Page exists |
| 301 | Redirect |
| 403 | Forbidden but real |
| 404 | Page not found |
In this FFUF Guide, ethical hackers focus on responses like 200, 301, and 403, because these often indicate real directories.
What is Fuzzing – absolute basics
Imagine a school building with 500 rooms.
Students only know about:
• classroom
• library
• playground
But the building may also contain hidden rooms like:
• teacher office
• storage room
• server room
This FFUF Guide teaches how hackers try every possible room number automatically to see which doors exist.
That process is called fuzzing.
How Attackers Use This Technique (Hacker Mindset)
Understanding the attacker mindset is the most important lesson in this FFUF Guide.
Hackers rarely attack randomly. They follow a logical process.
Step 1 – Reconnaissance
Attackers start by identifying the target domain.
Example:
target.com
Then they identify subdomains:
admin.target.com
api.target.com
dev.target.com
This process is called attack surface mapping.
Step 2 – Directory Discovery
Next, attackers try to discover hidden directories.
Examples include:
/admin
/backup
/dev
/internal
These directories may contain:
• login panels
• backup files
• configuration files
• debugging tools
This FFUF Guide explains that attackers use fuzzing tools to discover these paths.
Step 3 – Automated Scanning
Attackers load large wordlists with thousands of directory names.
Examples:
admin
administrator
backup
config
portal
api
dev
internal
This FFUF Guide shows how FFUF tests these automatically.
Step 4 – Response Analysis
Attackers analyze the server response.
Example output:
/admin Status:403
/backup Status:200
/dev Status:404
This FFUF Guide teaches that even a 403 response is useful because it confirms the directory exists.
Step 5 – Exploitation
Once attackers find hidden directories, they explore them further.
Examples:
/admin/login
/api/debug
/config.php
/backup.zip
These may reveal:
• credentials
• source code
• database backups
• API tokens
This is why directory fuzzing is a powerful reconnaissance technique.
SecurityElites Hands-on Lab Exercise — FFUF Guide Practical Tutorial
In this part of the FFUF Guide, we will learn how to actually use the FFUF tool step by step. This section is the most important part of the FFUF Guide because cybersecurity is not only about reading theory — it is about practicing in real environments.
Do not worry if you have never used Kali Linux before. This FFUF Guide lab will explain everything slowly and clearly so even a beginner or a young student can follow along.
Think of this lab like a cybersecurity classroom exercise where we learn how ethical hackers discover hidden parts of websites.
Important rule before starting the FFUF Guide lab:
Only practice on systems where you have permission.
Safe practice targets include:
• DVWA (Damn Vulnerable Web App)
• OWASP Juice Shop
• TryHackMe labs
• Hack The Box labs
• VulnWeb test sites
For this FFUF Guide, we will use an example training website:
http://testphp.vulnweb.com
This website is intentionally vulnerable and safe for learning.
Step 1 — Understanding the Goal of the FFUF Guide Lab
Before typing commands, we must understand what we are trying to discover.
Websites often contain hidden directories and files that are not visible from the homepage.
Example visible pages:
/home
/contact
/about
But the server may also contain hidden pages like:
/admin
/config
/dev
/api
These hidden directories are important because they may contain:
• login panels
• internal dashboards
• configuration files
• backup files
This FFUF Guide lab teaches us how to automatically search for these hidden paths.
Step 2 — Install FFUF in Kali Linux
Most Kali Linux installations already include FFUF.
First open your terminal.
Check if FFUF is installed.
ffuf -h
If FFUF is installed, you will see help instructions.
If FFUF is not installed, install it using:
sudo apt update
sudo apt install ffuf
After installation, verify again.
ffuf -V
If the version appears, FFUF is ready.
In this FFUF Guide, we will now begin discovering hidden directories.
Step 3 — Understanding the Basic FFUF Command
The most important concept in this FFUF Guide is the FUZZ keyword.
The word FUZZ acts like a placeholder.
Basic command:
ffuf -u URL -w WORDLIST
Example used in the FFUF Guide:
ffuf -u http://target.com/FUZZ -w wordlist.txt
Here is what each part means.
| Parameter | Meaning |
|---|---|
| -u | target URL |
| -w | wordlist file |
| FUZZ | position where words will be tested |
FFUF will replace FUZZ with every word in the wordlist.
For example:
If the wordlist contains:
admin
login
backup
config
api
Then FFUF will test:
http://target.com/admin
http://target.com/login
http://target.com/backup
http://target.com/config
http://target.com/api
This is how the FFUF Guide helps ethical hackers discover hidden directories.
Step 4 — Choosing a Wordlist
Wordlists are extremely important in the FFUF Guide.
A wordlist is simply a file containing many possible directory names.
Kali Linux already includes many wordlists.
Location:
/usr/share/wordlists/
A good beginner wordlist is:
/usr/share/wordlists/dirb/common.txt
This file contains hundreds of common directory names.
In this FFUF Guide, we will use that wordlist.
Step 5 — Running the First FFUF Scan
Now we run our first scan in this FFUF Guide lab.
Command:
ffuf -u http://testphp.vulnweb.com/FUZZ -w /usr/share/wordlists/dirb/common.txt
When this command runs, FFUF starts testing hundreds of directory names.
The output may look like this:
images Status:301
css Status:301
admin Status:403
uploads Status:200
In the FFUF Guide, we now analyze what this means.
Step 6 — Understanding the Results
Each result contains a status code.
Status codes tell us how the server responded.
| Code | Meaning |
|---|---|
| 200 | Page exists |
| 301 | Redirect |
| 403 | Forbidden |
| 404 | Page not found |
In this FFUF Guide, ethical hackers focus on:
• 200
• 301
• 403
Why?
Because these responses indicate the directory exists.
Example:
/admin 403
Even though access is forbidden, the admin directory still exists.
That information is valuable during reconnaissance.
Step 7 — Filtering Unnecessary Results
Sometimes FFUF returns many useless results.
For example, most responses may be 404 not found.
The FFUF Guide teaches filtering to remove noise.
Command:
ffuf -u http://target.com/FUZZ -w wordlist.txt -fc 404
Explanation:
-fc = filter status code
This removes all 404 results.
Now the output only shows interesting directories.
Filtering is a very important technique in the FFUF Guide.
Step 8 — Discovering Hidden Files
This FFUF Guide also teaches how to find hidden files.
Some servers contain files like:
config.php
backup.zip
login.php
To search for files we run:
ffuf -u http://target.com/FUZZ.php -w wordlist.txt
Now FFUF will test:
config.php
admin.php
login.php
Hidden files often contain sensitive information.
Step 9 — Parameter Fuzzing
Another powerful technique in this FFUF Guide is parameter discovery.
Web applications often accept parameters.
Example:
http://target.com/page.php?id=1
But there may also be hidden parameters like:
debug
token
user
admin
In the FFUF Guide, we test parameters like this:
ffuf -u "http://target.com/page.php?FUZZ=test" -w params.txt
FFUF replaces FUZZ with parameter names.
Example results:
id
debug
token
user
Hidden parameters sometimes reveal vulnerabilities.
Step 10 — Recursive Directory Discovery
After discovering directories like:
/admin
/uploads
/api
The FFUF Guide teaches us to scan inside them.
Example:
ffuf -u http://target.com/admin/FUZZ -w wordlist.txt
This may reveal deeper paths like:
/admin/login
/admin/config
/admin/users
This process helps ethical hackers fully map the web application.
How Organizations Stop FFUF Attacks ?
While the FFUF Guide teaches offensive techniques, defenders must also understand them.
Organizations use multiple defenses against fuzzing attacks.
1. Web Application Firewall
A Web Application Firewall monitors incoming requests.
Fuzzing attacks generate patterns like:
• thousands of requests
• dictionary based URLs
• repeated scanning attempts
WAF tools can block these patterns.
Popular WAF systems include:
Cloudflare
AWS WAF
Imperva
2. Rate Limiting
Servers can limit how many requests an IP address can send.
Example rule:
100 requests per minute
This slows automated fuzzing tools.
3. Authentication Protection
Sensitive directories like:
/admin
/internal
/config
Should require authentication.
Even if discovered, attackers cannot access them.
4. Security Monitoring
Security teams analyze server logs.
Example suspicious activity:
/admin
/admin1
/admin2
/admin-test
/admin-old
This pattern clearly indicates fuzzing attempts.
Organizations use this data to block attackers.
FAQs
What is FFUF in ethical hacking?
FFUF is a fast web fuzzing tool used in penetration testing to discover hidden directories, files, and parameters on web servers. Ethical hackers use FFUF during reconnaissance to map the attack surface of web applications. The FFUF Guide teaches beginners how to perform fuzzing safely in controlled environments.
Why do hackers use FFUF?
Hackers use FFUF because it is extremely fast and capable of testing thousands of URLs automatically. This allows attackers to discover hidden endpoints like /admin, /backup, or /api that may contain sensitive functionality. The FFUF Guide explains how attackers analyze these results to find potential vulnerabilities.
Is FFUF better than Dirbuster?
Yes. FFUF is faster and more flexible than older directory scanning tools. It supports advanced filtering, parameter fuzzing, recursion, and automation. Because of these capabilities, the FFUF Guide recommends FFUF as one of the best modern fuzzing tools.
Is using FFUF illegal?
The tool itself is legal. However scanning systems without authorization may violate laws or company policies. Ethical hackers must always obtain permission before testing systems. The FFUF Guide emphasizes responsible security testing.
Can beginners learn FFUF easily?
Yes. The FFUF Guide is designed so beginners can learn fuzzing step by step using Kali Linux labs. By practicing in environments like DVWA or TryHackMe, students can safely learn how web reconnaissance works.
Conclusion & Key Takeaways
This FFUF Guide introduced one of the most important tools used in web application reconnaissance.
We learned that FFUF helps ethical hackers:
• discover hidden directories
• find forgotten files
• identify undocumented APIs
• expand the attack surface
The biggest lesson from this FFUF Guide is that cybersecurity attacks begin with discovery and reconnaissance.
Attackers rarely exploit vulnerabilities immediately.
They first map the system carefully.
This is why fuzzing tools like FFUF are essential in penetration testing.
Next Cybersecurity Skills to Learn
After mastering this FFUF Guide, students should learn:
• Subdomain enumeration
• API security testing
• Burp Suite interception
• vulnerability scanning
• web exploitation techniques
Practice Platforms
Recommended cybersecurity training labs:
• TryHackMe
• HackTheBox
• PortSwigger Web Security Academy
• OWASP Juice Shop
Practicing these labs will help you develop the attacker mindset required for ethical hacking careers.