Metasploitable Labs
This metasploitable labs walkthrough guide explains how to exploit intentionally vulnerable machines using penetration testing tools. Step-by-step labs demonstrate scanning, exploitation, and privilege escalation techniques.
18 articles
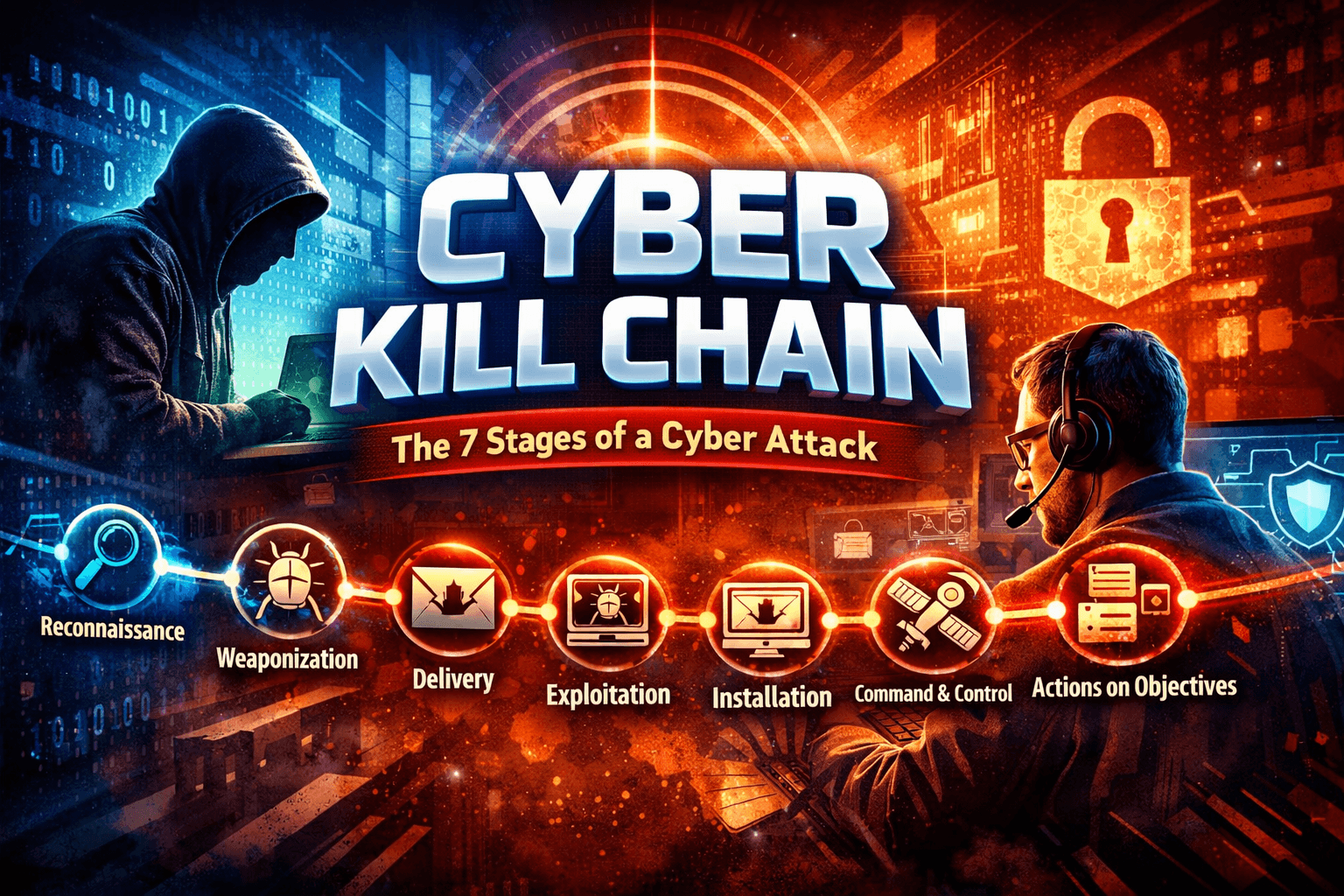
Cyber Kill Chain Explained: 7 Stages of a Cyber Attack
Learn the Cyber Kill Chain explained with ethical hacking examples, attacker mindset, hands-on labs, and defense strategies.
Beginner Exploitation Guide: 10 Ethical Hacking Techniques Every Pentester Should Know
Learn exploitation in ethical hacking with this beginner exploitation guide. Includes penetration testing labs, attacker mindset, and Metasploit tutorial.
20 AI Penetration Testing Tools Ethical Hackers Use (Kali Linux Guide)
Discover 20 AI penetration testing tools ethical hackers use. Learn how AI automates reconnaissance, vulnerability discovery, and cybersecurity testing.
ChatGPT Penetration Testing Automation: 7 Powerful Techniques Ethical Hackers Use
Learn how ethical hackers use ChatGPT penetration testing automation with Kali Linux labs, vulnerability discovery, and AI-assisted exploitation workflows.
Claude AI Kali Linux MCP Penetration Testing: 7 Powerful AI Automation Techniques
Learn Claude AI Kali Linux MCP Penetration Testing automation with a step-by-step guide. Discover how AI runs Nmap, Gobuster, and…
6 Powerful Stages of the Pentesting Lifecycle: Complete Penetration Testing Guide
Learn the 6 powerful stages of the Pentesting Lifecycle used by ethical hackers. Step-by-step penetration testing process, tools, labs, and…
First Pentest Walkthrough – Step-by-Step Ethical Hacking Guide
Before we start our first Pentest Walkthrough we should first understand What is Pentest or Penetration testing. Later in tutorial…