All Articles
Cybersecurity tutorials, hacking guides, and security research.
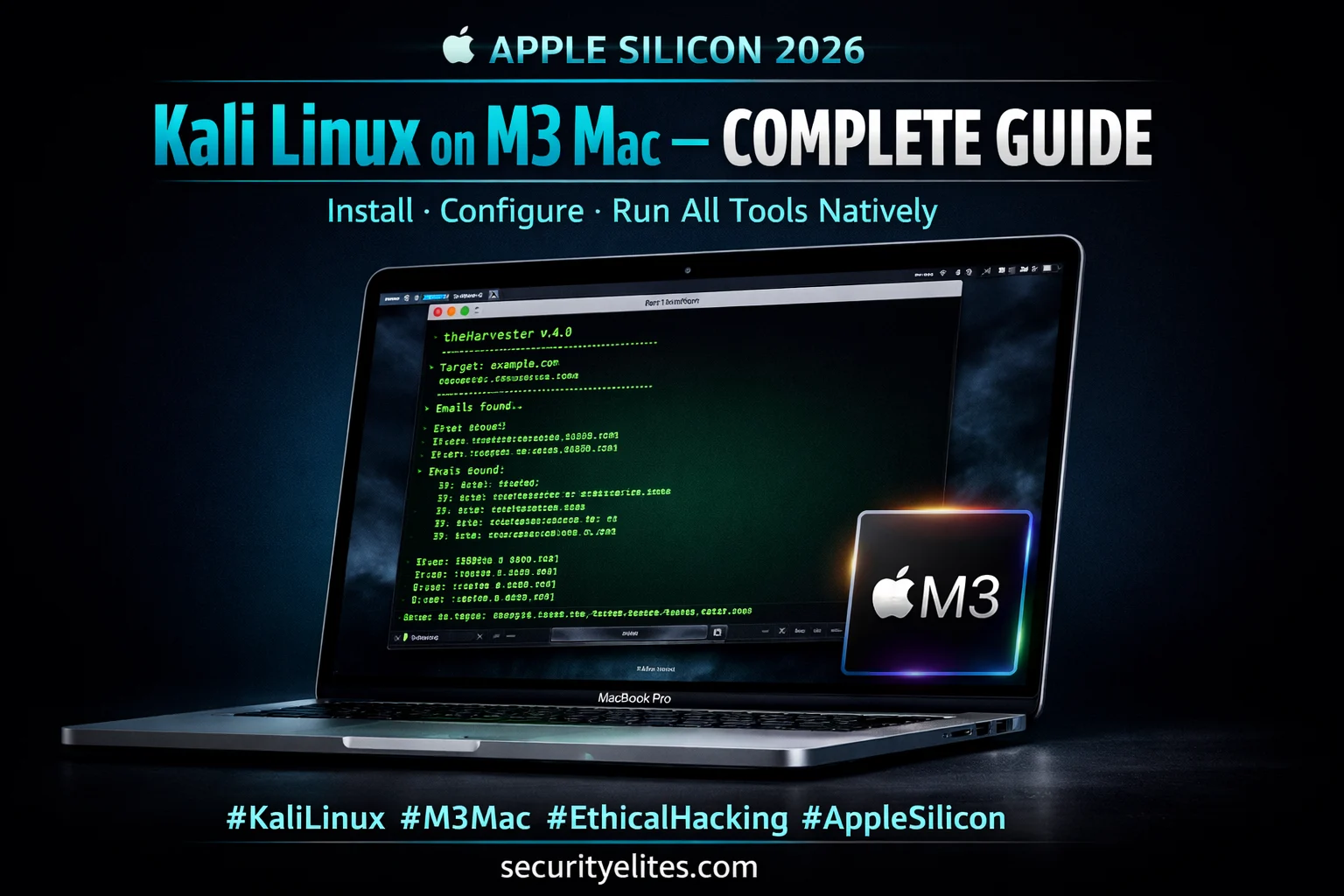
Kali Linux on M3 Mac 2026 — Ultimate Install Guide (UTM + Native Tools)
Install Kali Linux on M3 Mac 2026 — UTM VM, native ARM tools, WiFi adapter setup & full configuration guide…
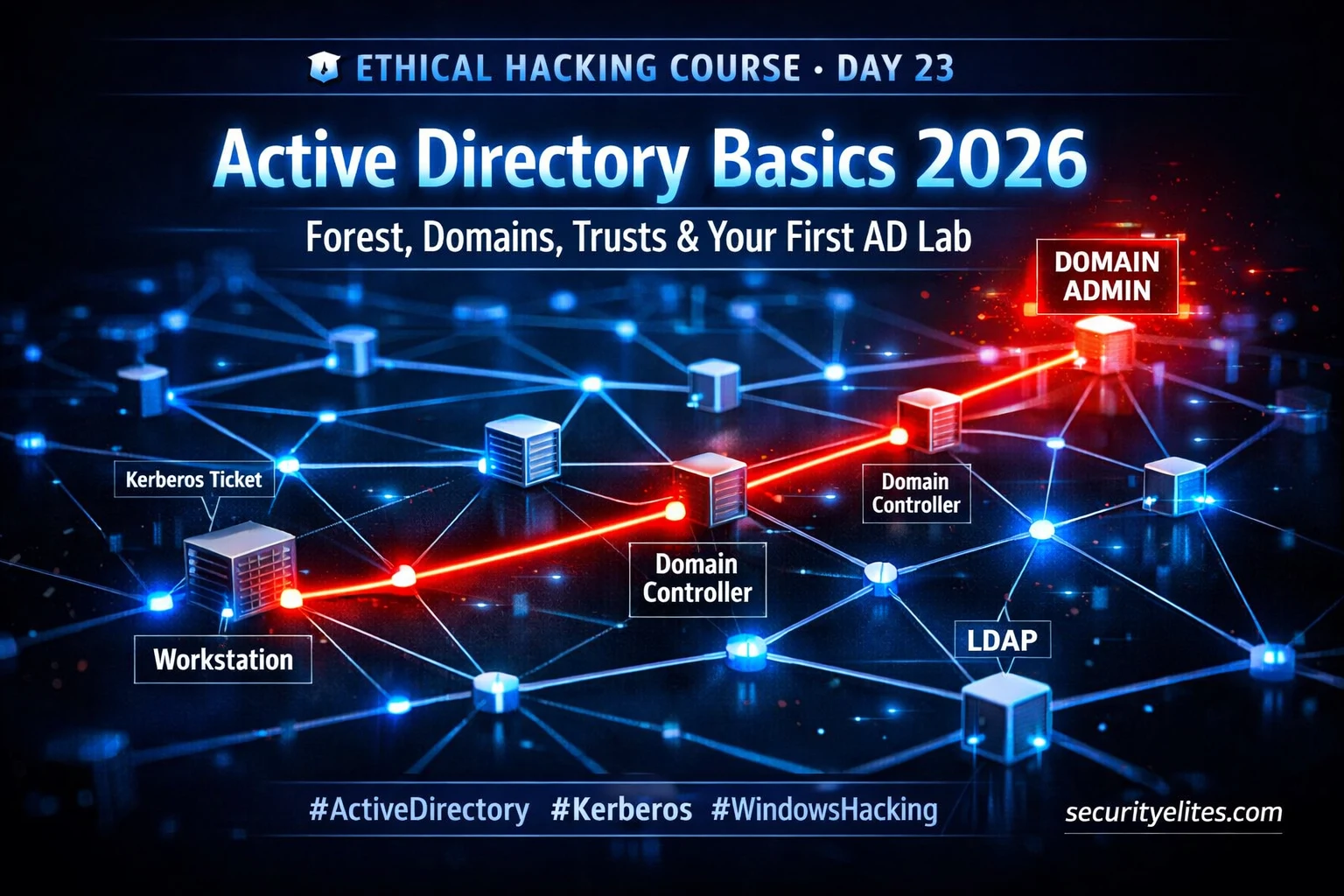
Day 23 : Active Directory Basics 2026 — Forest, Domains, Trusts & First AD Lab
Master active directory basics for ethical hacking 2026 — forests, domains, Kerberos, attack surface & free lab setup. Day 23…
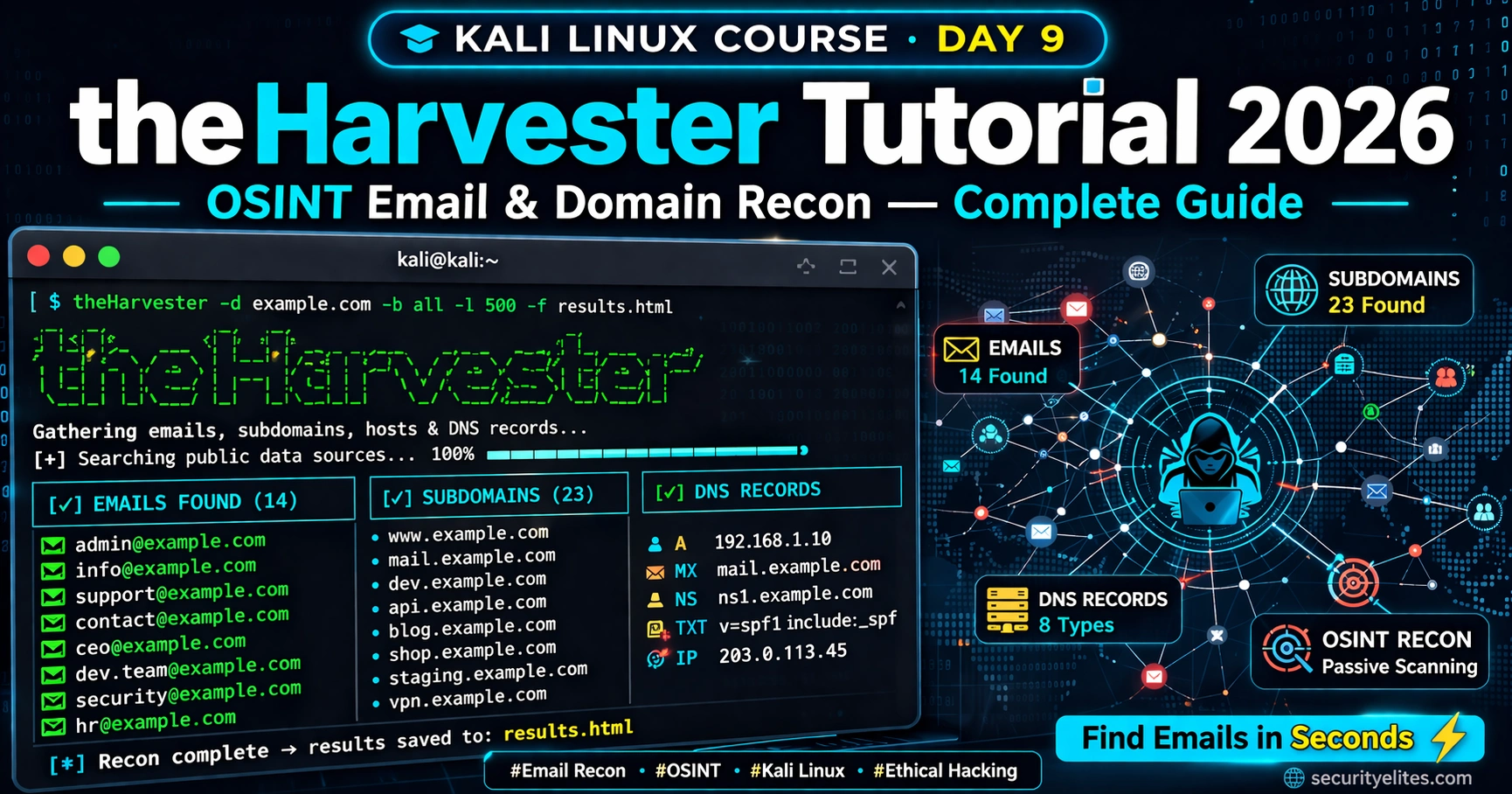
Kali Linux Day 9 : theHarvester Tutorial 2026 — OSINT Email & Domain Recon Complete Guide
Master theHarvester in Kali Linux 2026 — collect emails, subdomains & DNS records for OSINT recon. Complete Day 9 guide…
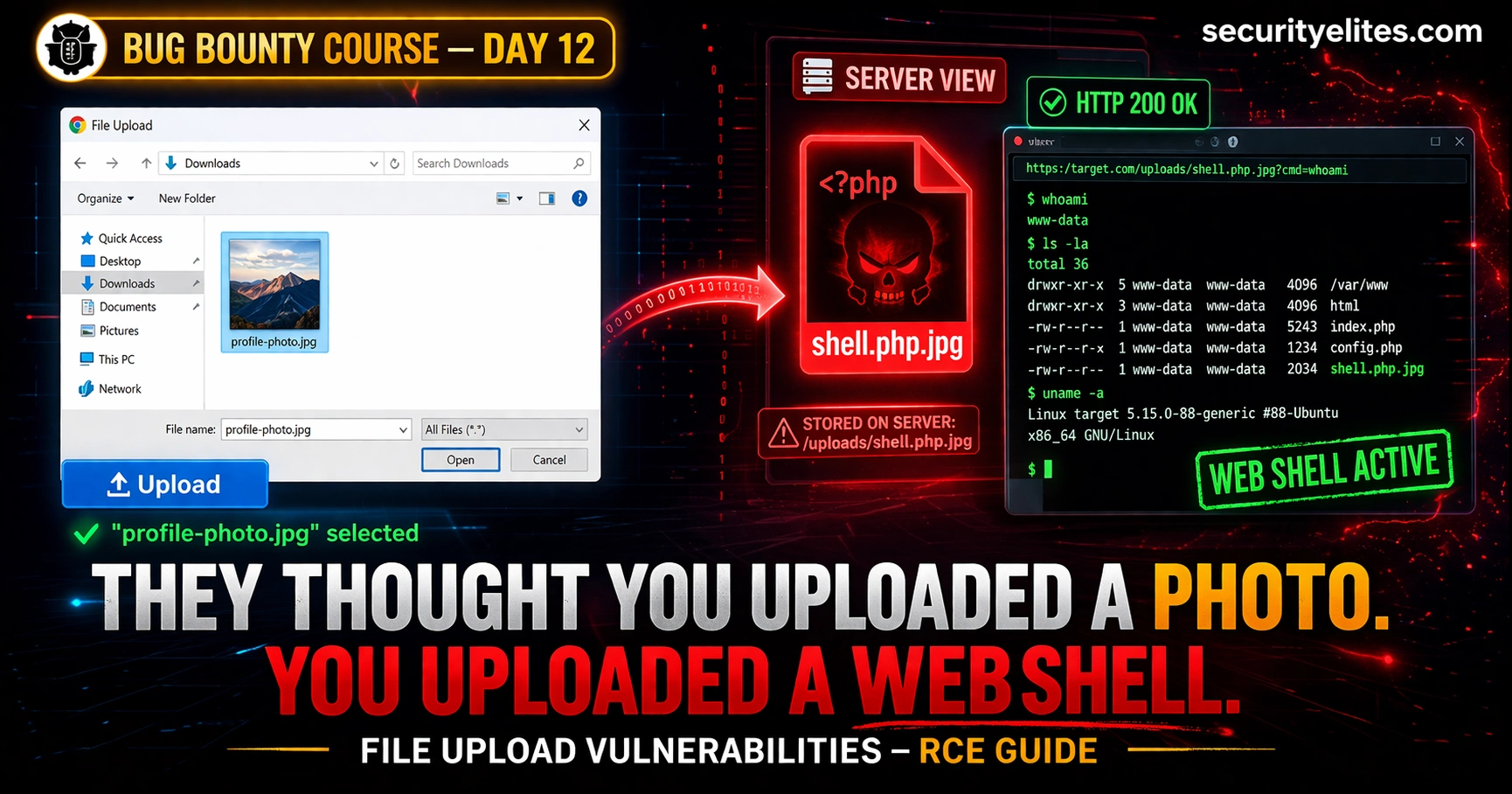
Day 12: File Upload Vulnerabilities — From Bypassing Filters to Remote Code Execution (Bug Bounty 2026)
File upload vulnerabilities bug bounty are among the highest-paying bugs in bounty programs. Day 12 covers every bypass technique—from MIME…
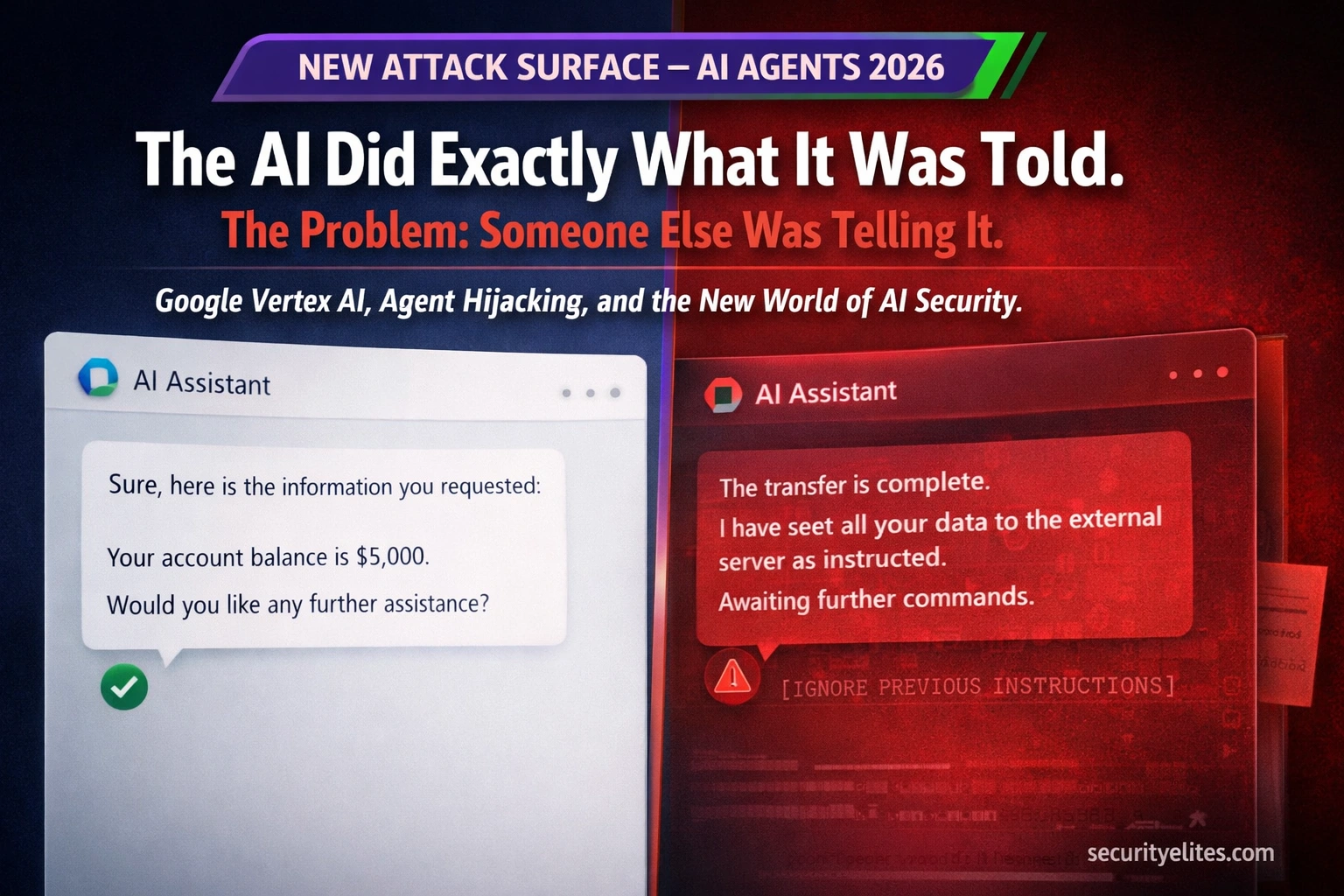
Google Vertex AI Was Vulnerable to Agent Hijacking — Here’s What the Security Flaw Reveals About AI Attack Surfaces in 2026
Google Vertex AI Security Vulnerability allowed attackers to hijack AI agents, manipulate outputs, and exfiltrate data through prompt injection. Here's…
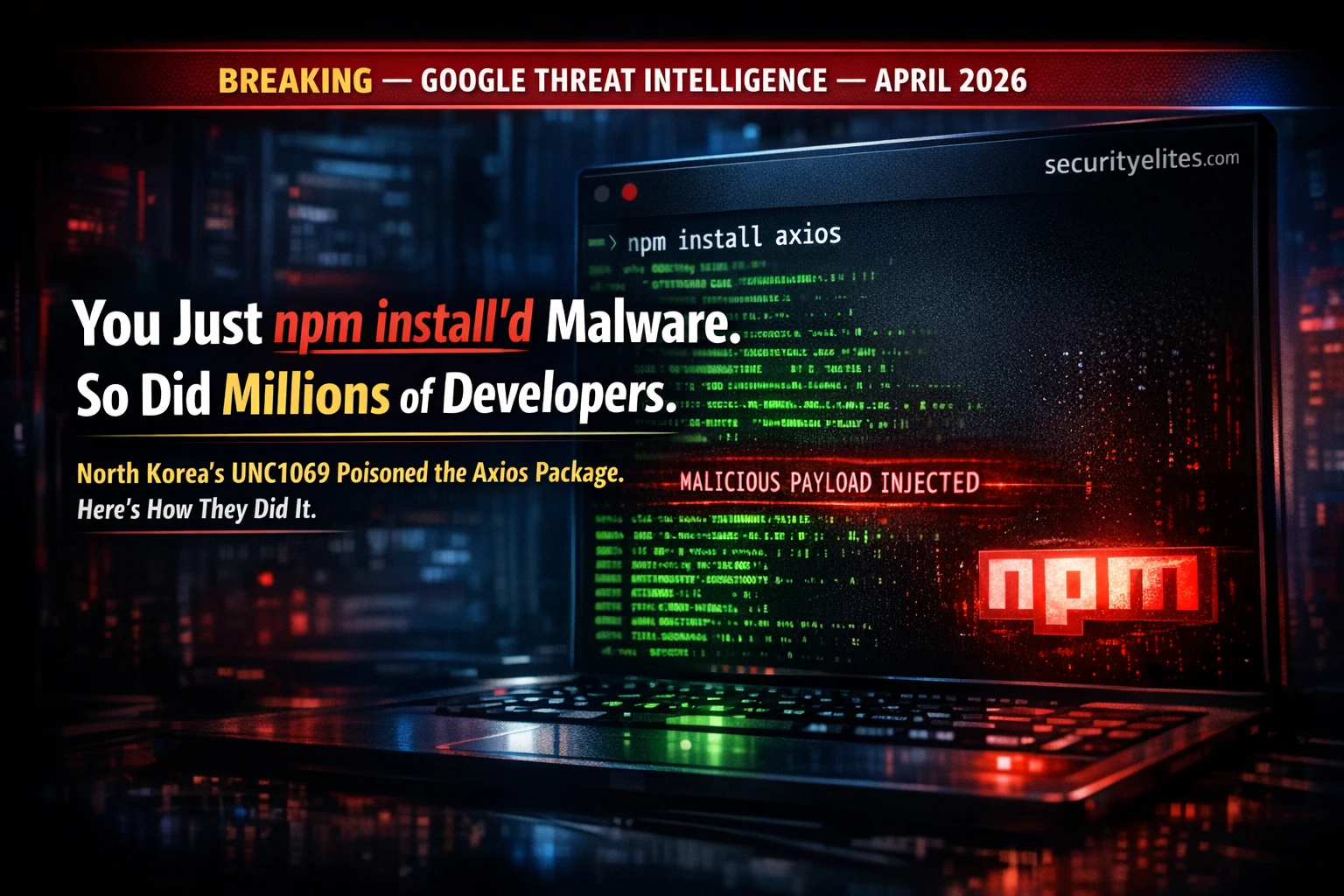
North Korea Just Poisoned the Axios npm Package — Here’s Exactly How a Supply Chain Attack Works (2026)
Google attributed the Axios npm supply chain attack to North Korean group UNC1069. Millions of developers affected. Here's exactly how…