All Articles
Cybersecurity tutorials, hacking guides, and security research.
Cisco CVE-2026-20093 — CVSS 9.8 Authentication Bypass Explained: How Hackers Get Admin Access Without a Password (2026)
Cisco patched Cisco CVE-2026-20093 authentication bypass, a CVSS 9.8 critical flaw letting unauthenticated attackers bypass authentication and gain admin access.…
Day 11: Open Redirect Bug Bounty Hunting 2026 — Find, Chain and Report the Vulnerability That Turns $200 Bugs Into $5,000 Findings
Day 11 of 60. Master open redirect bug bounty hunting with manual testing, bypass techniques, OAuth chaining for account takeover,…
ShinyHunters Stole 3 Million Cisco Records — Here’s Exactly How (2026)
Cisco Data Breach 2026 by ShinyHunters via Salesforce and AWS, exposing 3M+ records. Full attack breakdown, exploited vectors, and key…
2.3 Million Android Phones Were Infected via Google Play — How the NoVoice Rootkit Works (2026)
Operation NoVoice Android Malware hid a rootkit in 50+ Google Play apps with 2.3M downloads. Factory reset won’t remove it.…
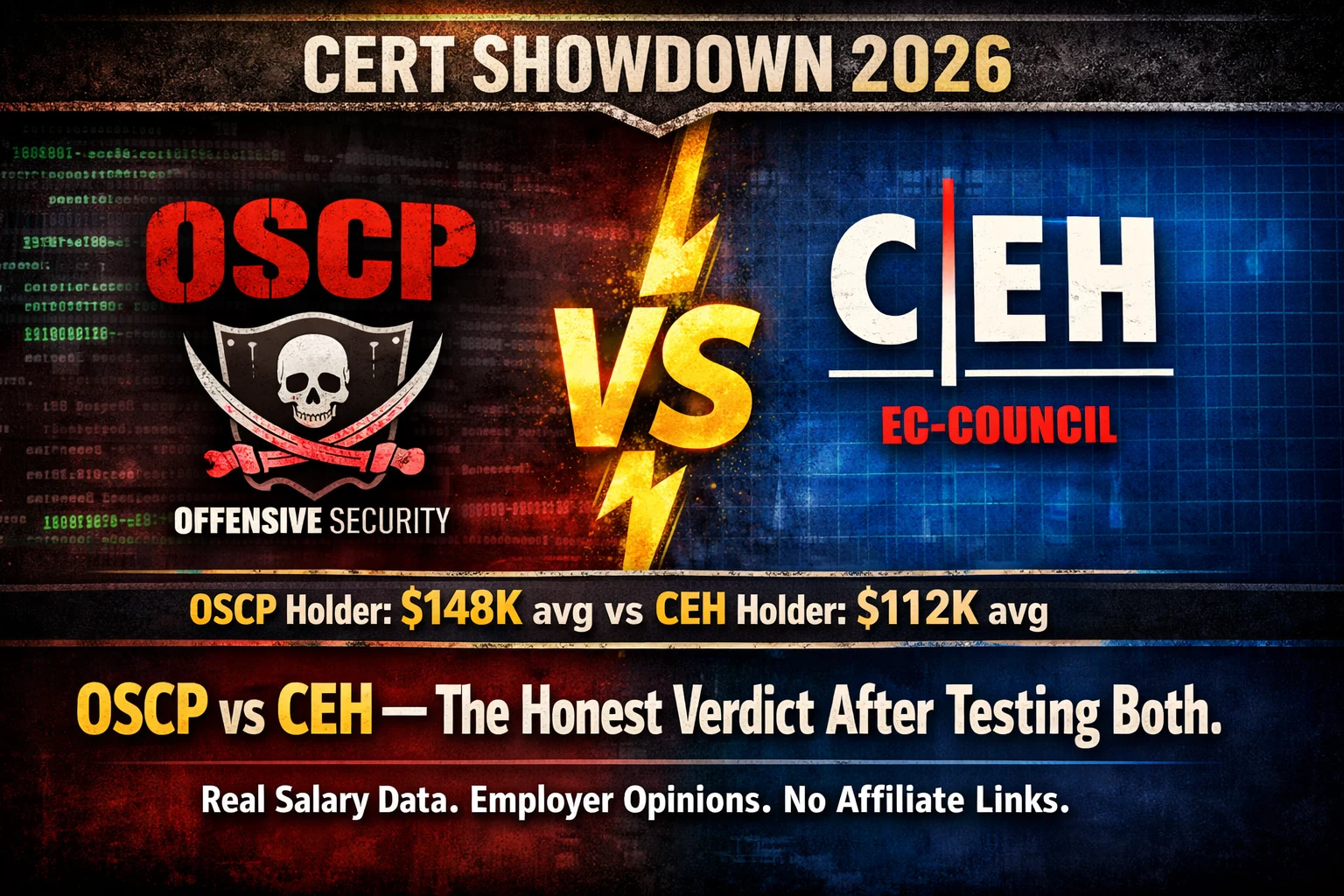
OSCP vs CEH 2026 — Which Certification Is Actually Worth Your Money
OSCP vs CEH 2026 — the complete unbiased comparison. Real salary data, employer opinions, difficulty, cost, and the honest verdict…
Cloud Security Hacking 2026 — How Attackers Exploit AWS, Azure & GCP (Ethical Hacker’s Guide)
Cloud security hacking is the highest-demand offensive skill of 2026. Learn IAM misconfiguration exploitation, S3 bucket attacks, SSRF to cloud…