All Articles
Cybersecurity tutorials, hacking guides, and security research.
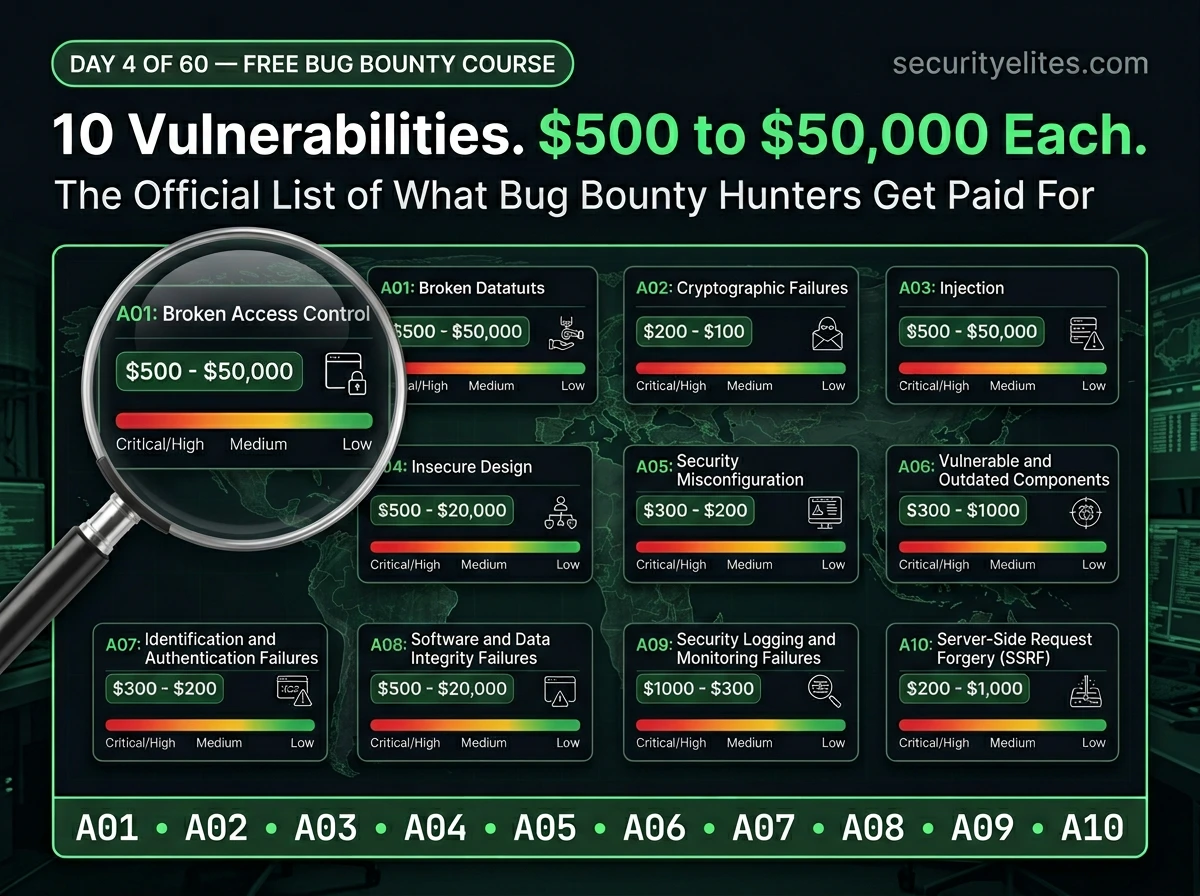
Day 4: OWASP Top 10 Explained — The Official Bug Bounty Vulnerability Map Every Hunter Needs (2026)
Day 4 of 60. Learn the OWASP Top 10 in plain English — what each vulnerability is, how it’s exploited,…
Day 15: CSRF & Authentication Bypass — When Web Requests Get Forged (2026)
Day 15 of 100. CSRF attacks explained, understand authentication bypass — how forged requests exploit user trust, CSRF tokens, SameSite…
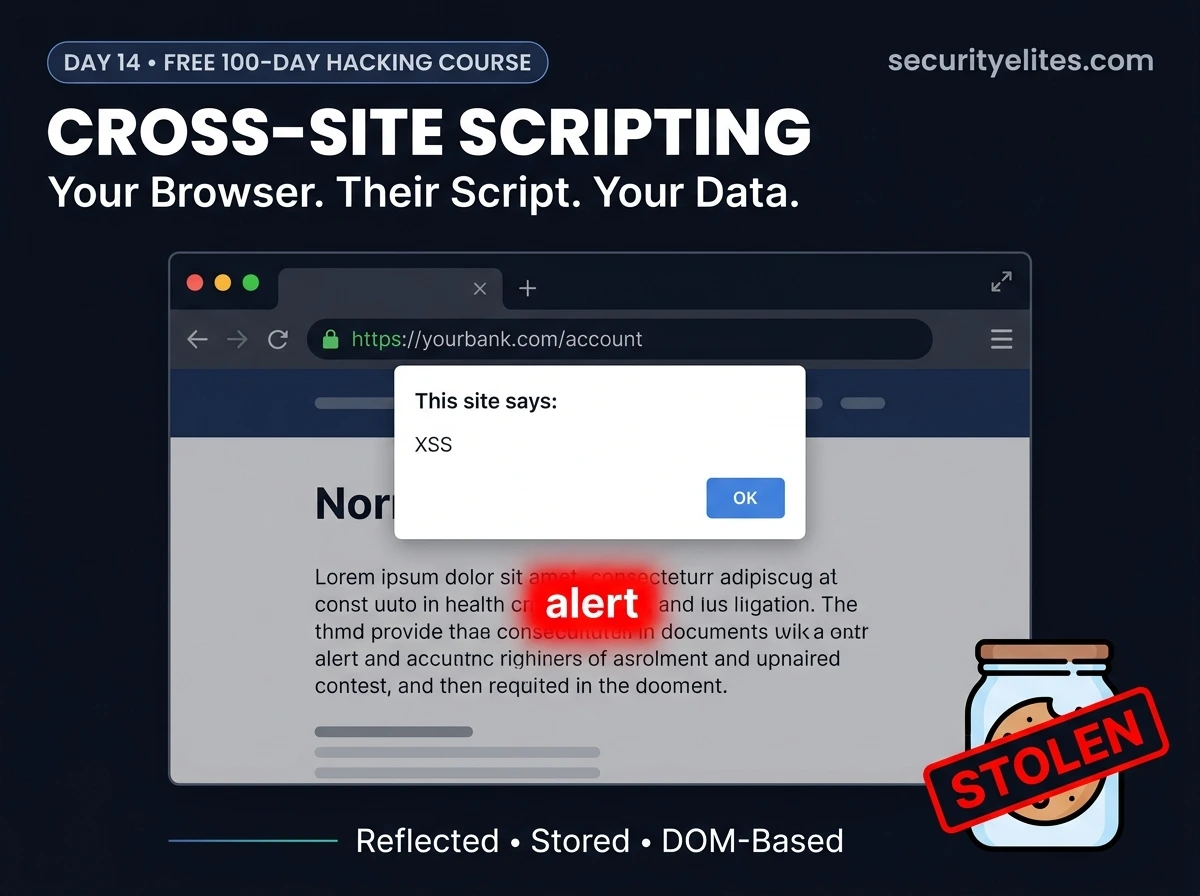
Day 14: XSS Cross-Site Scripting — How Hackers Steal Cookies & Take Over Accounts (2026)
Day 14 of 100. Understand XSS Cross Site Scripting —reflected, stored, and DOM-based—with DVWA demos in Burp Suite, cookie theft…
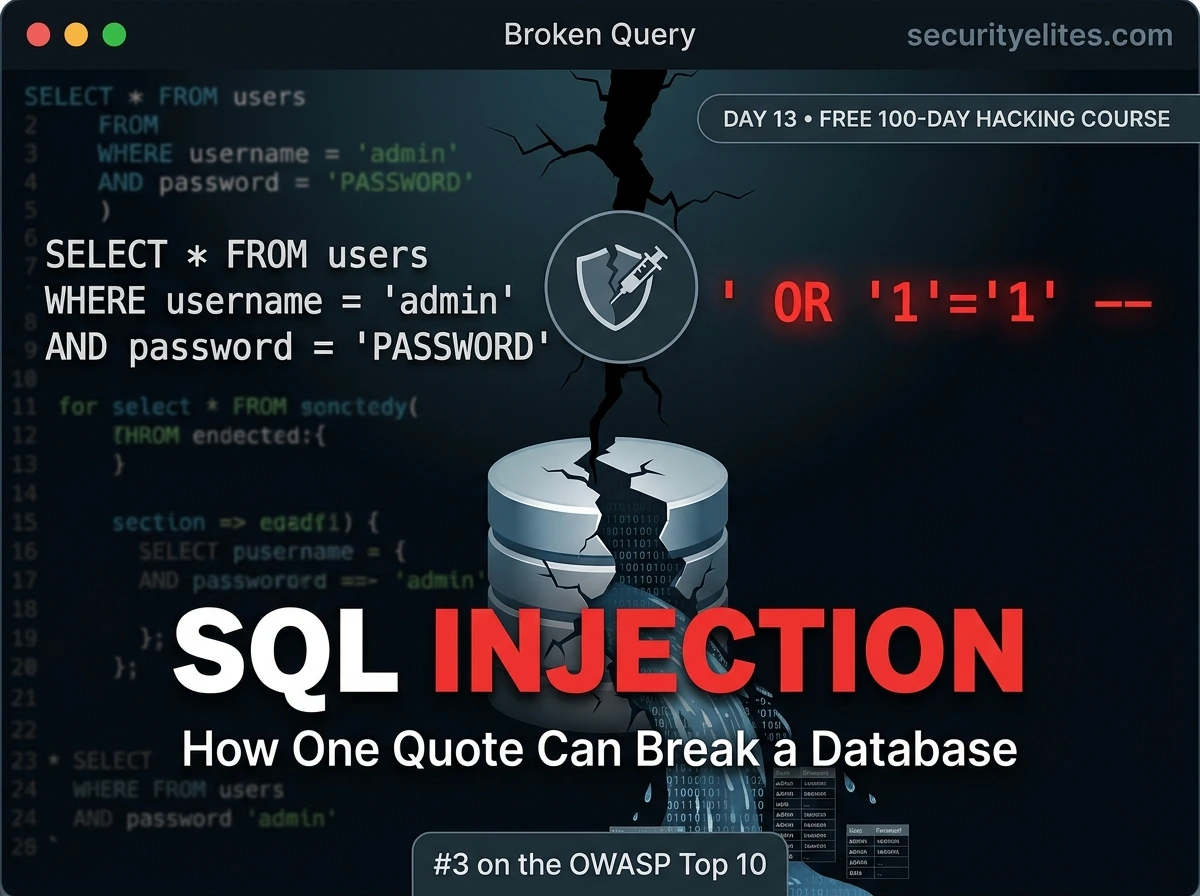
Day 13: SQL Injection Explained — From First Quote to Finding the Vulnerability (2026)
Day 13 of 100. SQL injection tutorial from first principles — how databases work, why injection happens, how to identify…
How to Hack Android Phone Ethically 2026 – ADB, Metasploit & APK Analysis Guide
Learn how to hack Android phones ethically using ADB, Metasploit & APK analysis. Complete mobile penetration testing guide for 2026.
How Hackers Crack Passwords in Seconds (2026) — Real Attack Demo
See how hackers crack passwords in seconds using brute force, dictionary attacks, and credential stuffing. Real examples, tools, and how…