All Articles
Cybersecurity tutorials, hacking guides, and security research.
How to Practice Ethical Hacking Legally at Home 2026 — Build Your Own Hacking Lab (Free & Legal)
The complete guide to building a free, legal ethical hacking home lab for practice ethical hacking legally at home in…
Kali Linux Day 3: Gobuster Tutorial — Find Hidden Directories, Files & Subdomains (Complete Beginner Guide 2026)
Complete Gobuster tutorial for Kali Linux — dir mode, dns mode, vhost mode, wordlists, status code filtering, file extension discovery,…
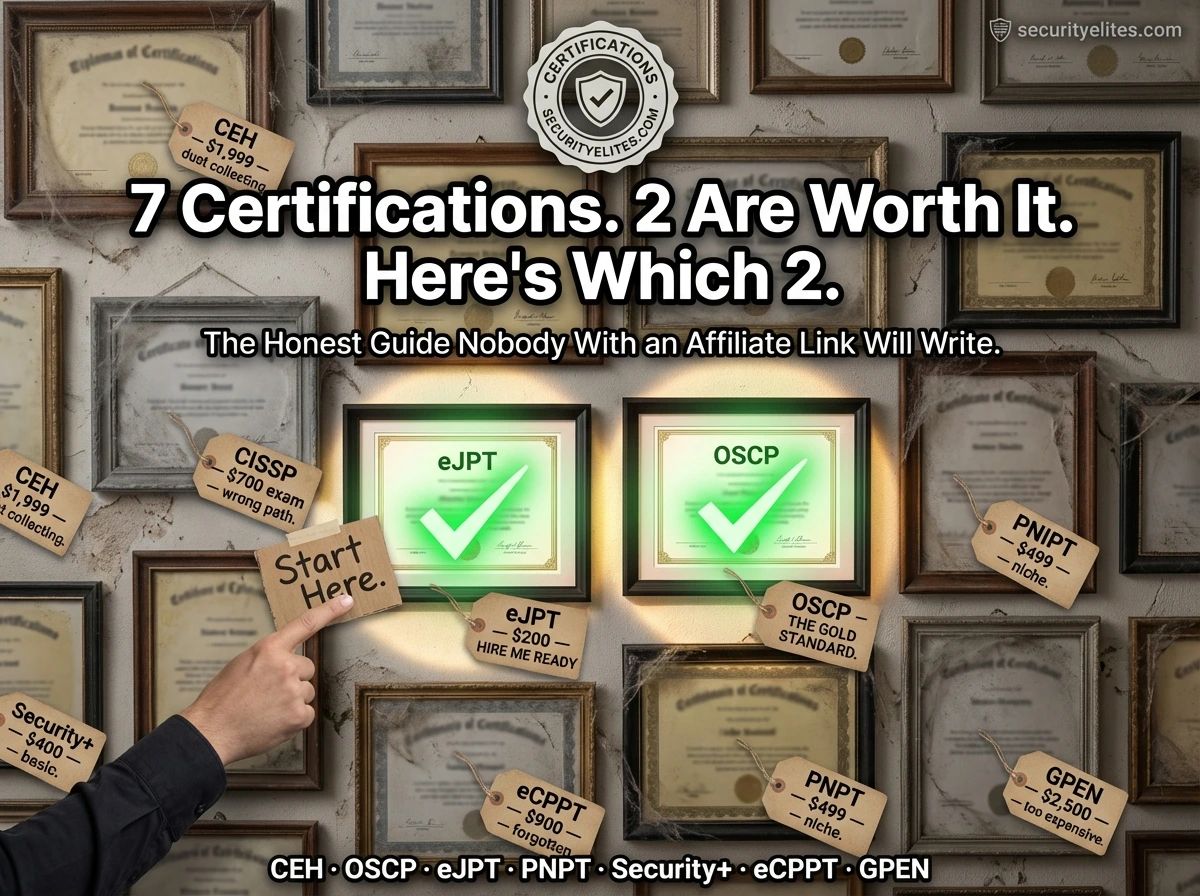
What Certifications Do Ethical Hackers Need 2026 — Honest Ranking (CEH vs OSCP vs eJPT vs Security+ Compared)
The honest, unaffiliated comparison of ethical hacking certifications in 2026 — CEH, OSCP, eJPT, CompTIA Security+, PNPT, eCPPT. Cost, difficulty,…
Kali Linux Commands Cheat Sheet 2026 — 200+ Commands with Examples (The Only Reference You’ll Ever Need)
The most comprehensive Kali Linux commands cheat sheet 2026 — 200+ commands across 10 categories with real examples. Networking, scanning,…
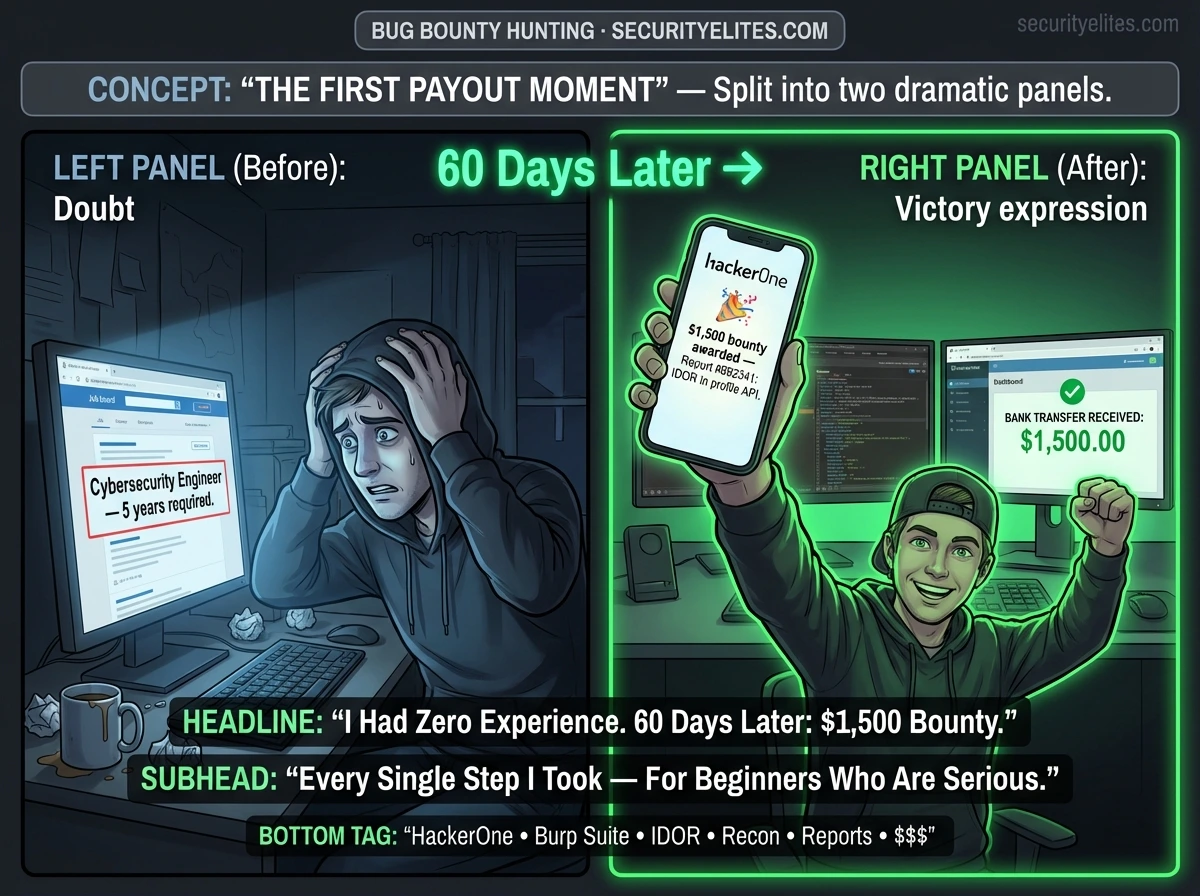
Bug Bounty Hunting for Beginners — The Complete Step-by-Step Guide From Zero to First Paid Finding (2026)
The most completeguide on bug bounty hunting for beginners 2026 — platform setup, reconnaissance, vulnerability testing, professional report writing, and…
How to Secure Gmail Account From Hackers — The Ultimate 2026 Protection Guide (Block Every Attack)
Complete step-by-step guide on how to secure Gmail account — enabling 2-Step Verification with an authenticator app, reviewing account activity,…