All Articles
Cybersecurity tutorials, hacking guides, and security research.
Beginner Exploitation Guide: 10 Ethical Hacking Techniques Every Pentester Should Know
Learn exploitation in ethical hacking with this beginner exploitation guide. Includes penetration testing labs, attacker mindset, and Metasploit tutorial.
Dark Web Guide: Dark Web Explained and What Hackers Really Do There (2026)
Complete Dark Web Guide explaining how the Dark Web works, why hackers use it, and how cybersecurity experts track Dark…
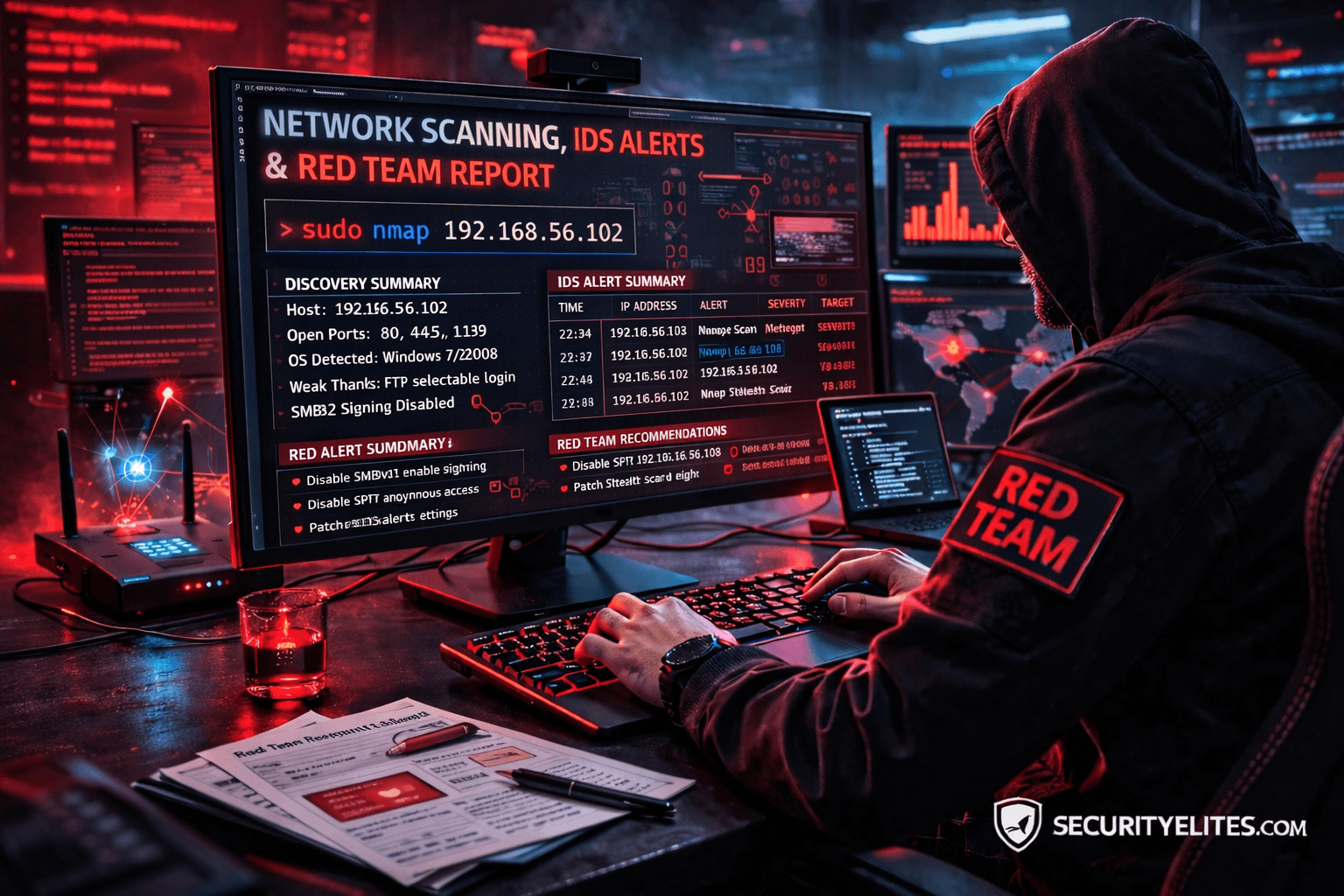
Network Scanning Tutorial Using Nmap Day 7 — Stealth Scanning, IDS Evasion & Red Team Techniques
Network Scanning Tutorial Using Nmap Day 7 - Learn stealth scanning, IDS evasion, and advanced Red Team Nmap techniques used…
DVWA to Bug Bounty Day 6: API Hacking & Business Logic Vulnerabilities
DVWA to Bug Bounty Day 6 - Learn API hacking techniques and business logic vulnerability hunting used by elite bug…
20 AI Penetration Testing Tools Ethical Hackers Use (Kali Linux Guide)
Discover 20 AI penetration testing tools ethical hackers use. Learn how AI automates reconnaissance, vulnerability discovery, and cybersecurity testing.
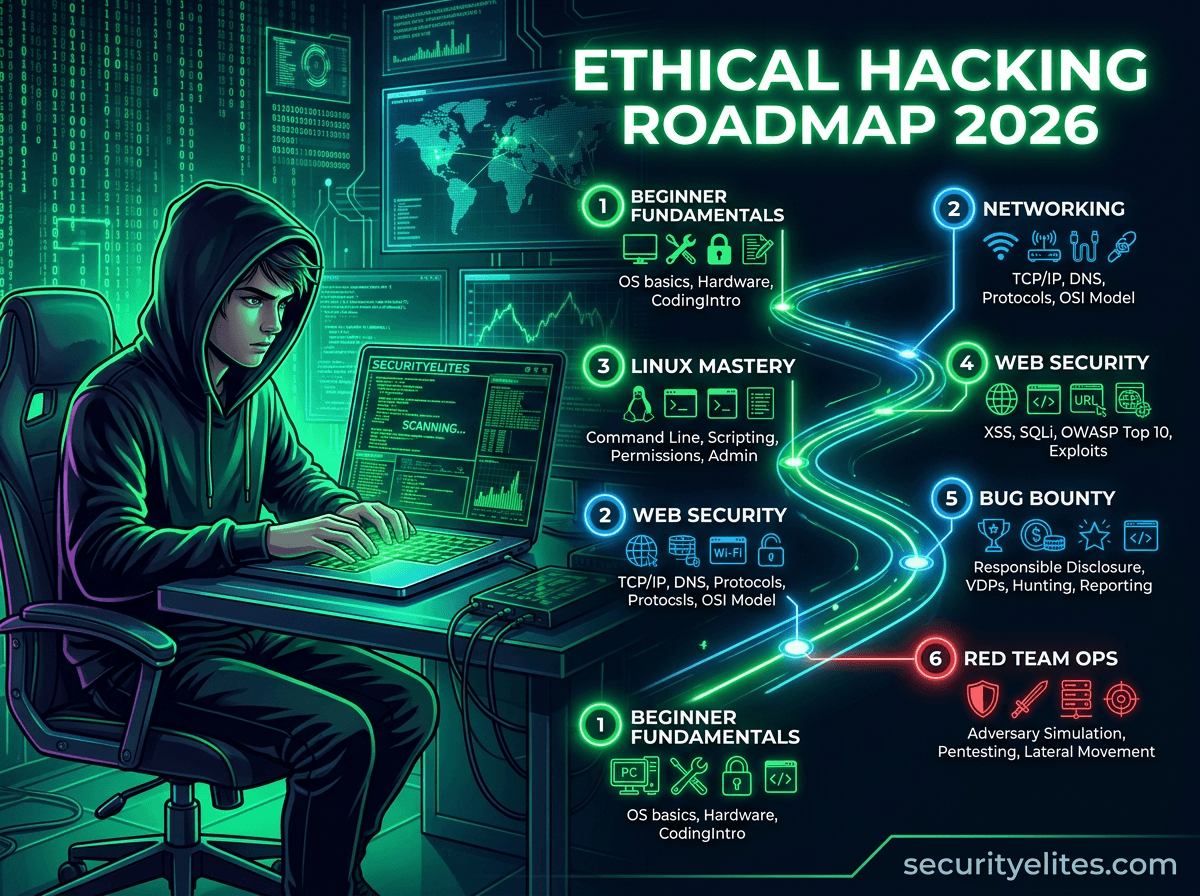
Ethical Hacking Roadmap 2026: How to Become Ethical Hacker (Beginner to Expert)
Learn the complete ethical hacking roadmap 2026 with step-by-step labs, tools, and cybersecurity skills required to become an ethical hacker…