All Articles
Cybersecurity tutorials, hacking guides, and security research.
Bug Bounty Case Study: 8 Steps to Discover an IDOR Vulnerability
This Bug Bounty Case Study explains how ethical hackers discover IDOR vulnerabilities using real penetration testing techniques, attacker mindset, and…
300 Ethical Hacking Tools – Ultimate Collection for Security Professionals
Discover 300 ethical hacking tools used by cybersecurity professionals for penetration testing, vulnerability scanning, reconnaissance and security research.
DVWA to Bug Bounty Day 3: Hidden Endpoints & Parameter Discovery Guide
DVWA to Bug Bounty Day 3 - Learn how bug bounty hunters discover hidden endpoints, APIs, and parameters to find…
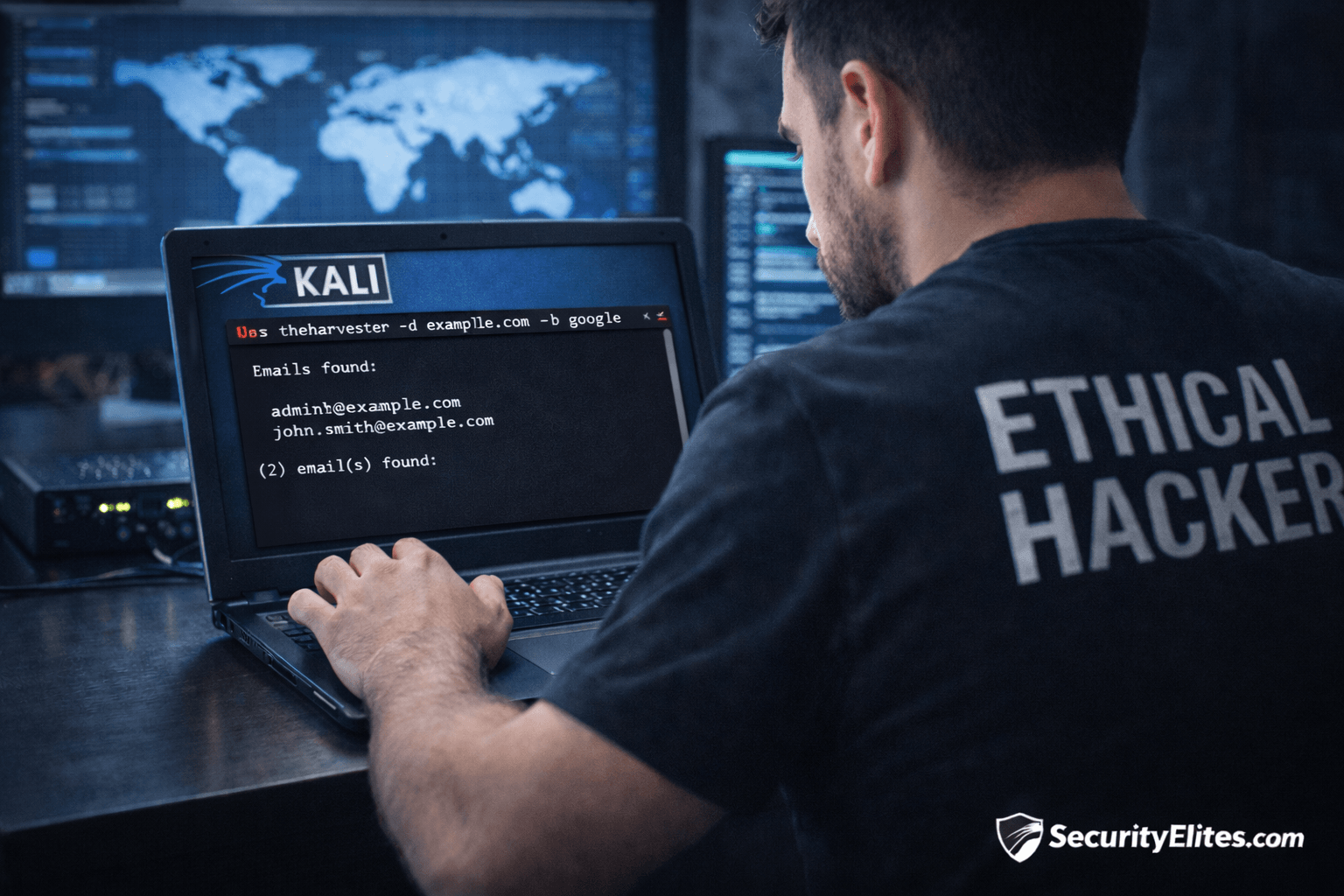
Information Gathering Using Kali Linux Day 5: OSINT Recon with theHarvester
Information Gathering Using Kali Linux Day 5 - Learn Information Gathering using Kali Linux with theHarvester step-by-step. Discover emails, hosts,…
Network Scanning Tutorial Using Nmap Day 4 — Service & Version Enumeration
Network Scanning Tutorial Using Nmap Day 4 - Learn service and version enumeration using Nmap like professional penetration testers. Day…
Hacker Recon Checklist: 10-Step Ethical Hacking Recon Guide
Learn the hacker recon checklist used in penetration testing and bug bounty hunting. Step-by-step reconnaissance guide with tools and practical…