Bug Bounty Reports
Learn how to write professional vulnerability reports that get accepted and rewarded on bug bounty platforms.
30 articles
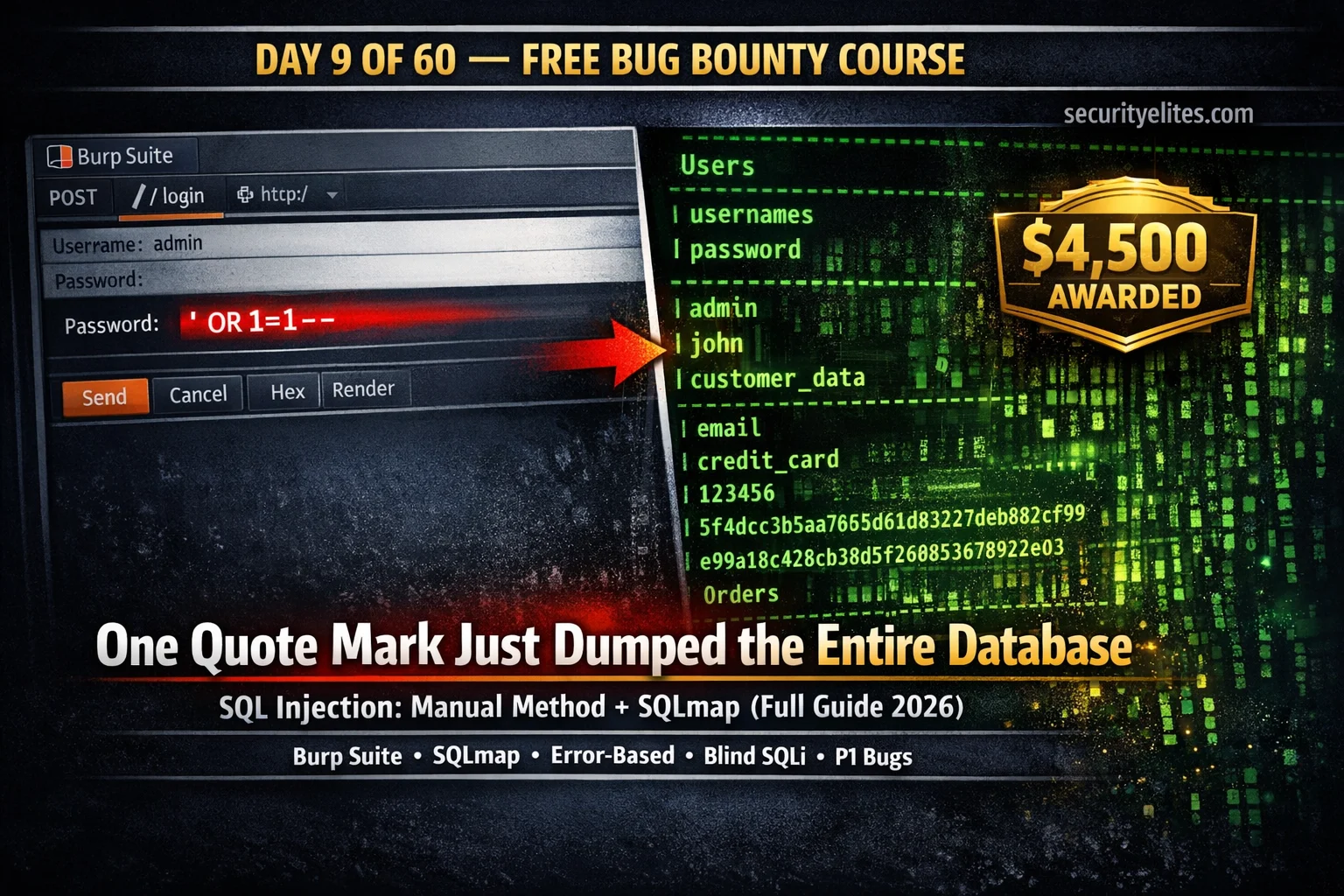
Day 9: SQL Injection for Bug Bounty 2026 — Manual Testing + SQLmap Complete Guide
Day 9 of 60. Learn SQL injection for bug bounty: manual testing with Burp Suite, error-based, UNION-based, blind SQLi, SQLmap…
Day 8: IDOR Bug Bounty Hunting — Find Insecure Direct Object Reference Vulnerabilities That Pay (2026)
Complete IDOR bug bounty hunting guide — what IDOR is, horizontal vs vertical privilege escalation, where to find IDORs, Burp…
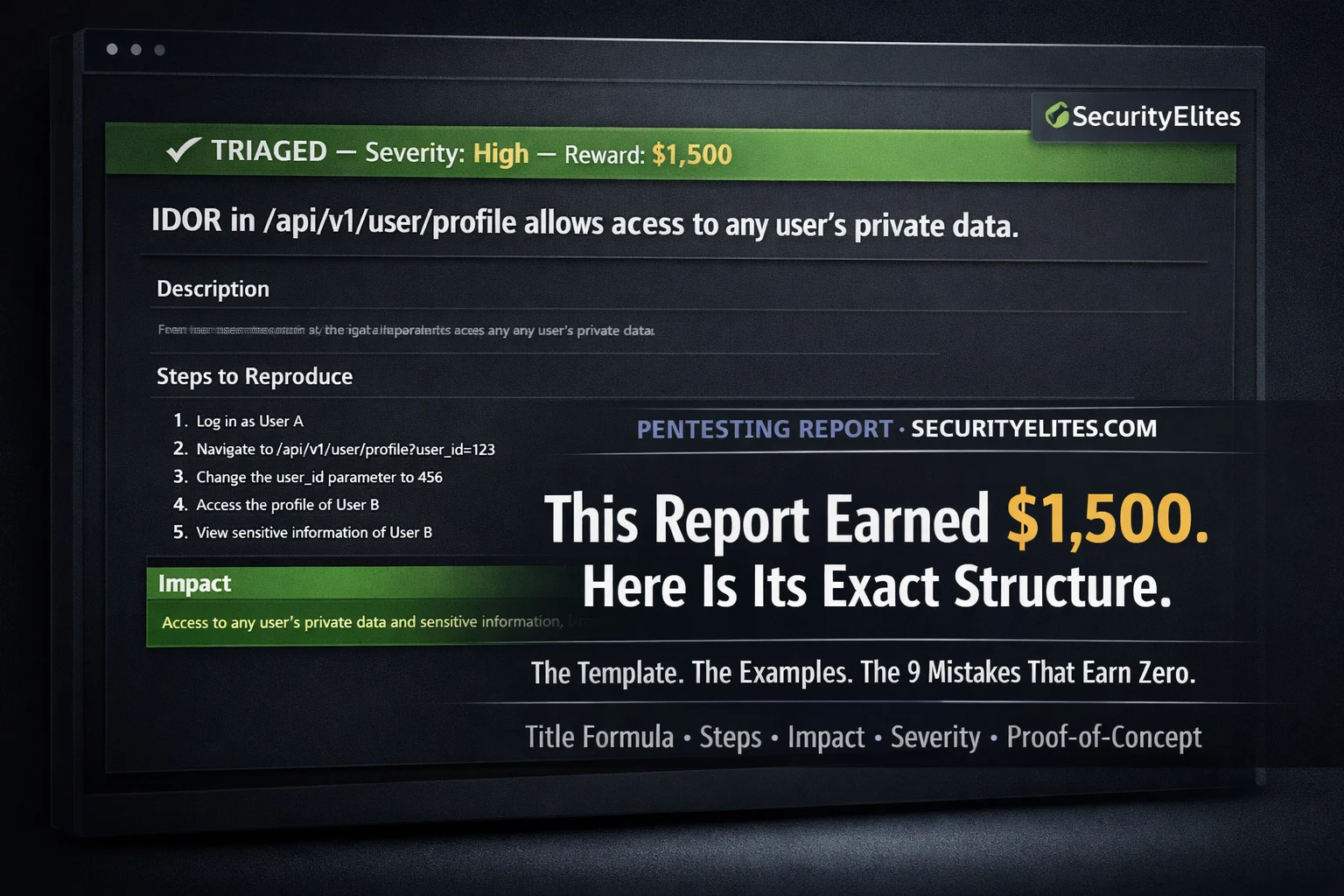
How to Write a Bug Bounty Report That Gets Paid — Templates, Examples, and the 9 Reasons Reports Get Rejected (2026)
The complete guide on how to Report bug bounty Vulnerability that get paid — including the exact report template, severity…
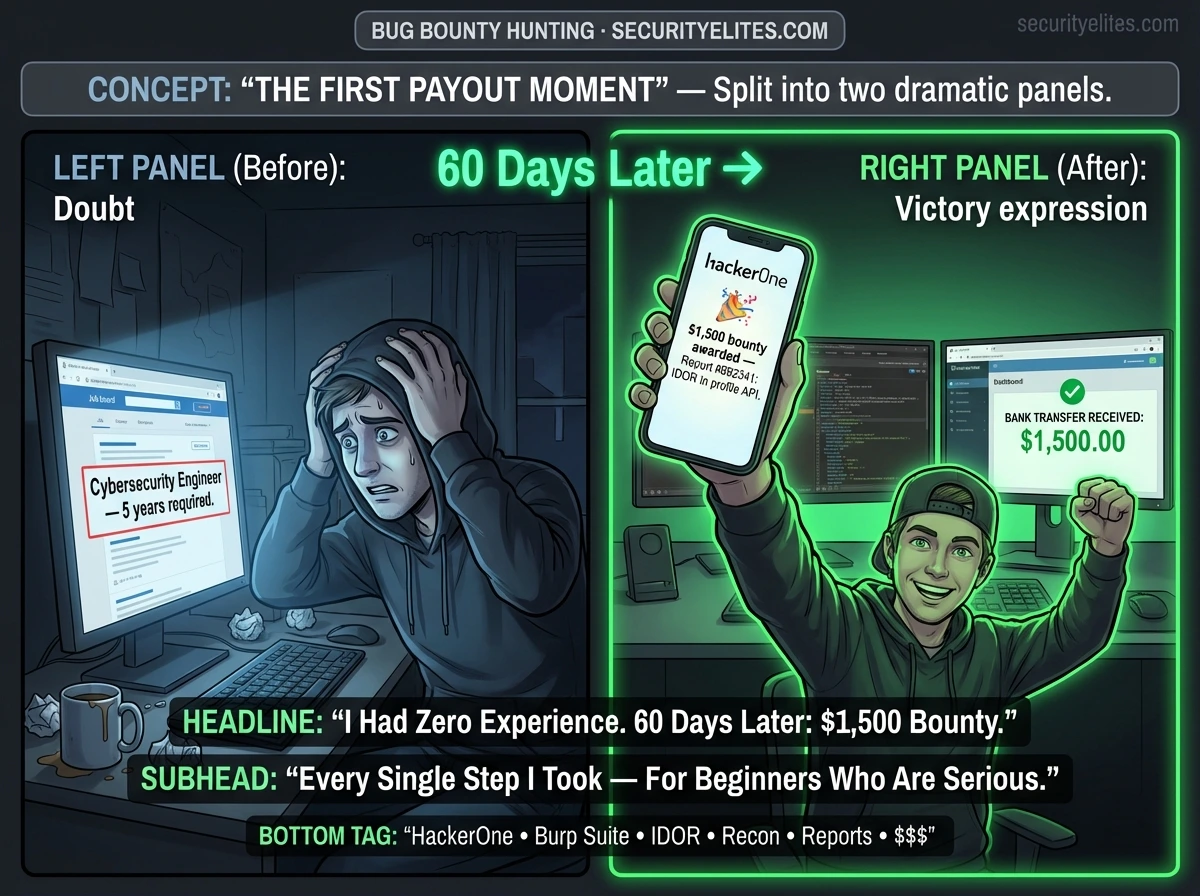
Bug Bounty Hunting for Beginners — The Complete Step-by-Step Guide From Zero to First Paid Finding (2026)
The most completeguide on bug bounty hunting for beginners 2026 — platform setup, reconnaissance, vulnerability testing, professional report writing, and…
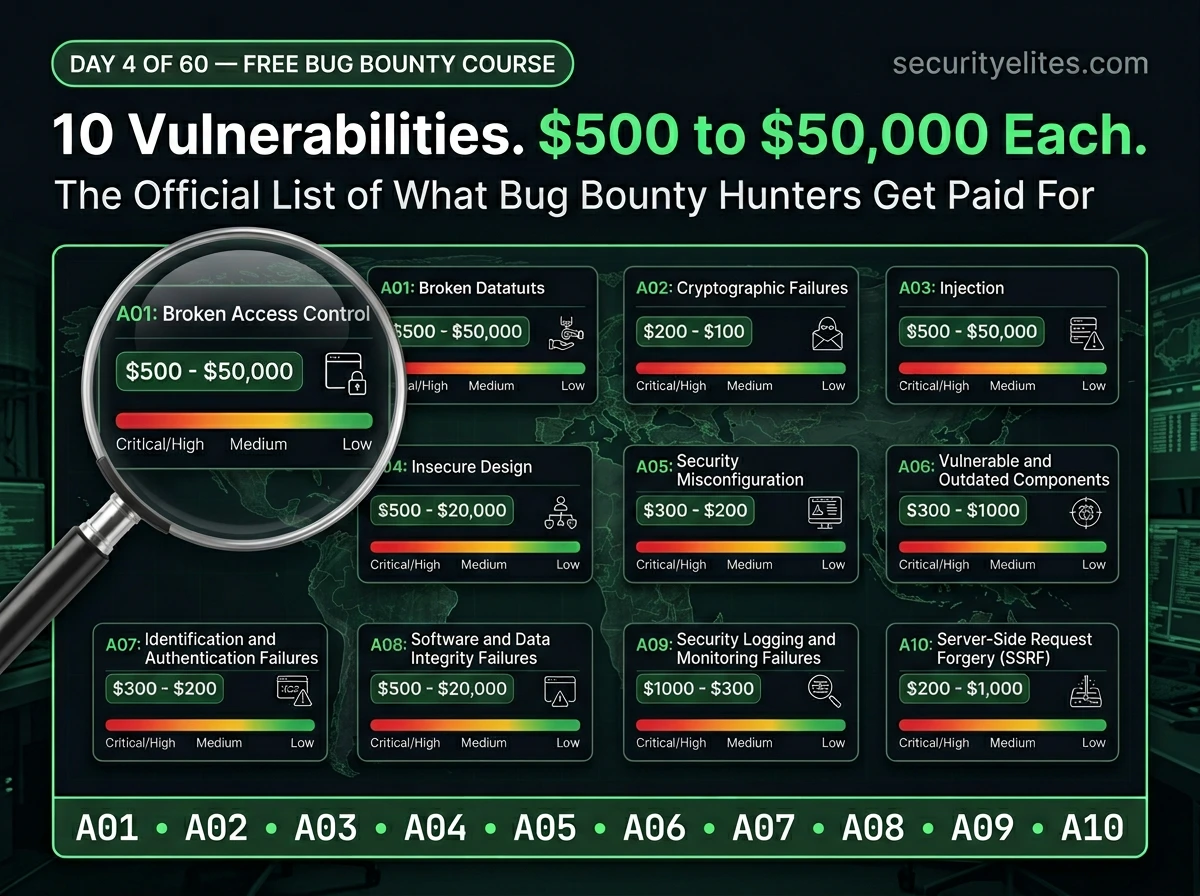
Day 4: OWASP Top 10 Explained — The Official Bug Bounty Vulnerability Map Every Hunter Needs (2026)
Day 4 of 60. Learn the OWASP Top 10 in plain English — what each vulnerability is, how it’s exploited,…
Instagram Bug Bounty — How Ethical Hackers Legally Earn $500–$30,000 Finding Instagram Vulnerabilities (2026)
Learn how ethical hackers legally earn $500 to $30,000 through Meta's Instagram bug bounty program on Bugcrowd. Explore scope, payouts,…
DVWA to Bug Bounty Day 7: Professional Reporting & Earning Strategy
DVWA to Bug Bounty Day 7 - Learn professional bug bounty workflow, vulnerability reporting techniques, and strategies to earn rewards…
Bug Bounty Case Study: 8 Steps to Discover an IDOR Vulnerability
This Bug Bounty Case Study explains how ethical hackers discover IDOR vulnerabilities using real penetration testing techniques, attacker mindset, and…
Bug Bounty Hunting Methodology: Complete Ethical Hacker Workflow Guide
Master Bug Bounty Hunting Methodology with practical recon workflow, tools, attacker mindset, and step-by-step ethical hacking tutorial.