Exploitation Tools
Exploitation tools for penetration testing help security professionals validate vulnerabilities in controlled environments. This category includes tutorials on frameworks like Metasploit, SQLmap, Hydra, and other exploitation utilities used to test system weaknesses. Learn how to configure payloads, execute exploits, establish reverse shells, and perform post-exploitation activities responsibly. Each guide emphasizes ethical usage and defensive measures to protect against exploit-based attacks. Real-world lab demonstrations help readers understand how vulnerabilities are exploited and how security teams mitigate risks.
12 articles
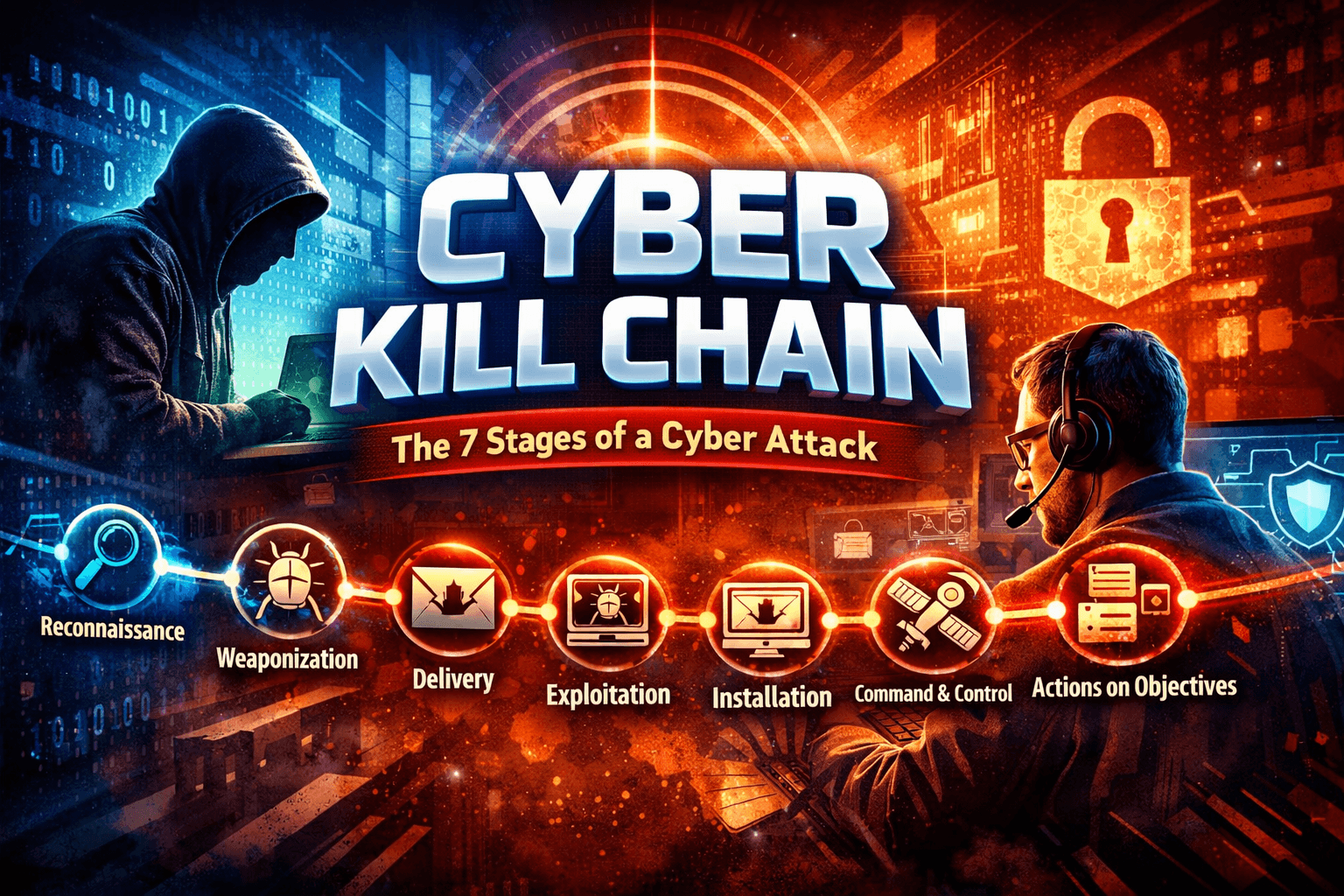
Cyber Kill Chain Explained: 7 Stages of a Cyber Attack
Learn the Cyber Kill Chain explained with ethical hacking examples, attacker mindset, hands-on labs, and defense strategies.
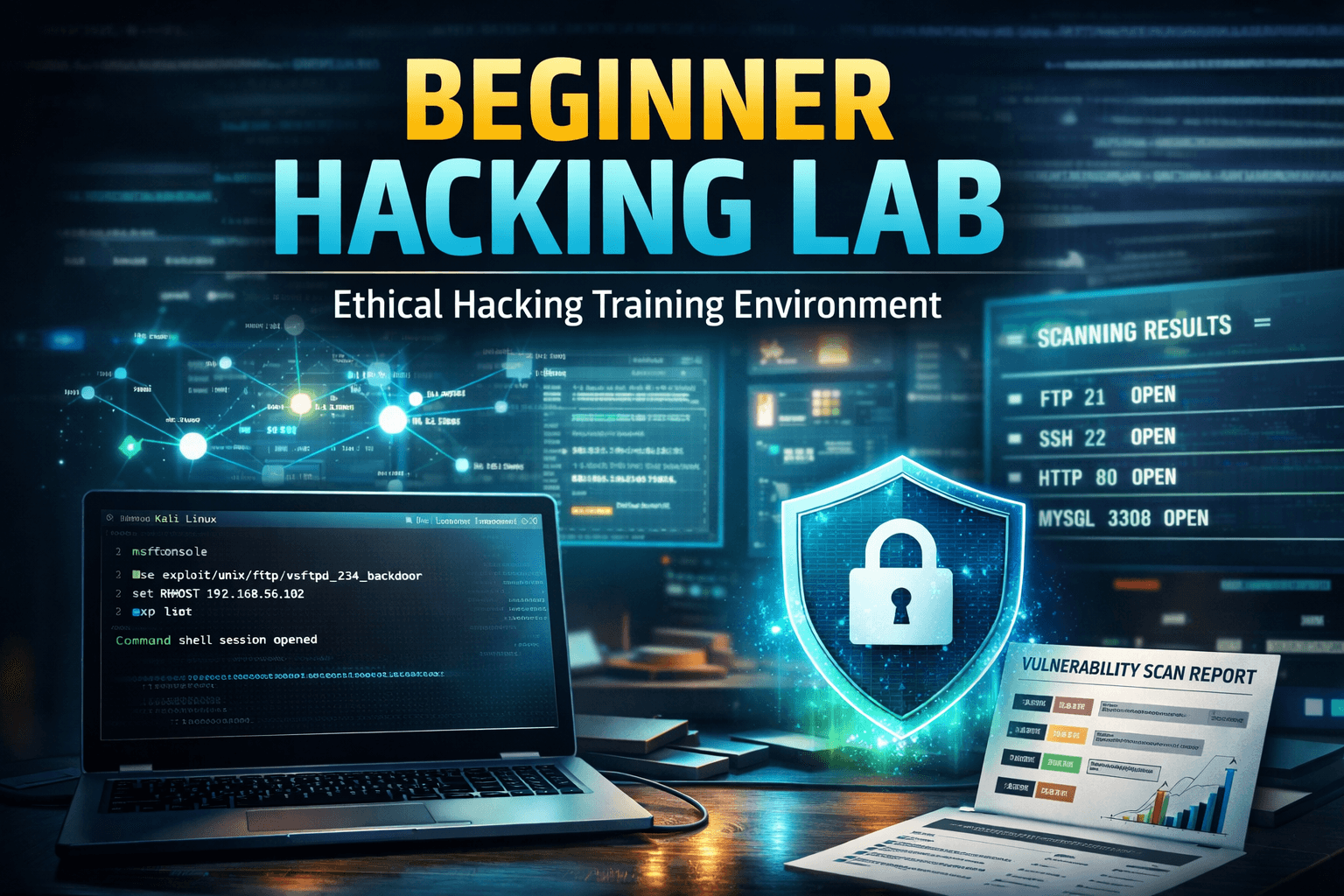
Beginner Exploitation Guide: 10 Ethical Hacking Techniques Every Pentester Should Know
Learn exploitation in ethical hacking with this beginner exploitation guide. Includes penetration testing labs, attacker mindset, and Metasploit tutorial.
300 Ethical Hacking Tools – Ultimate Collection for Security Professionals
Discover 300 ethical hacking tools used by cybersecurity professionals for penetration testing, vulnerability scanning, reconnaissance and security research.
Burp Suite Beginner Guide: Complete Ethical Hacking & Web Testing Tutorial
Burp Suite Beginner Guide to learn Burp Suite step-by-step with this beginner ethical hacking guide covering interception, vulnerability testing, attacker…