Ethical Hacking Courses
71 articles
DVWA to Bug Bounty Day 4: Authentication & Authorization Logic Bugs
DVWA to Bug Bounty Day 4 - Learn how bug bounty hunters find IDOR and authorization vulnerabilities using real-world testing…
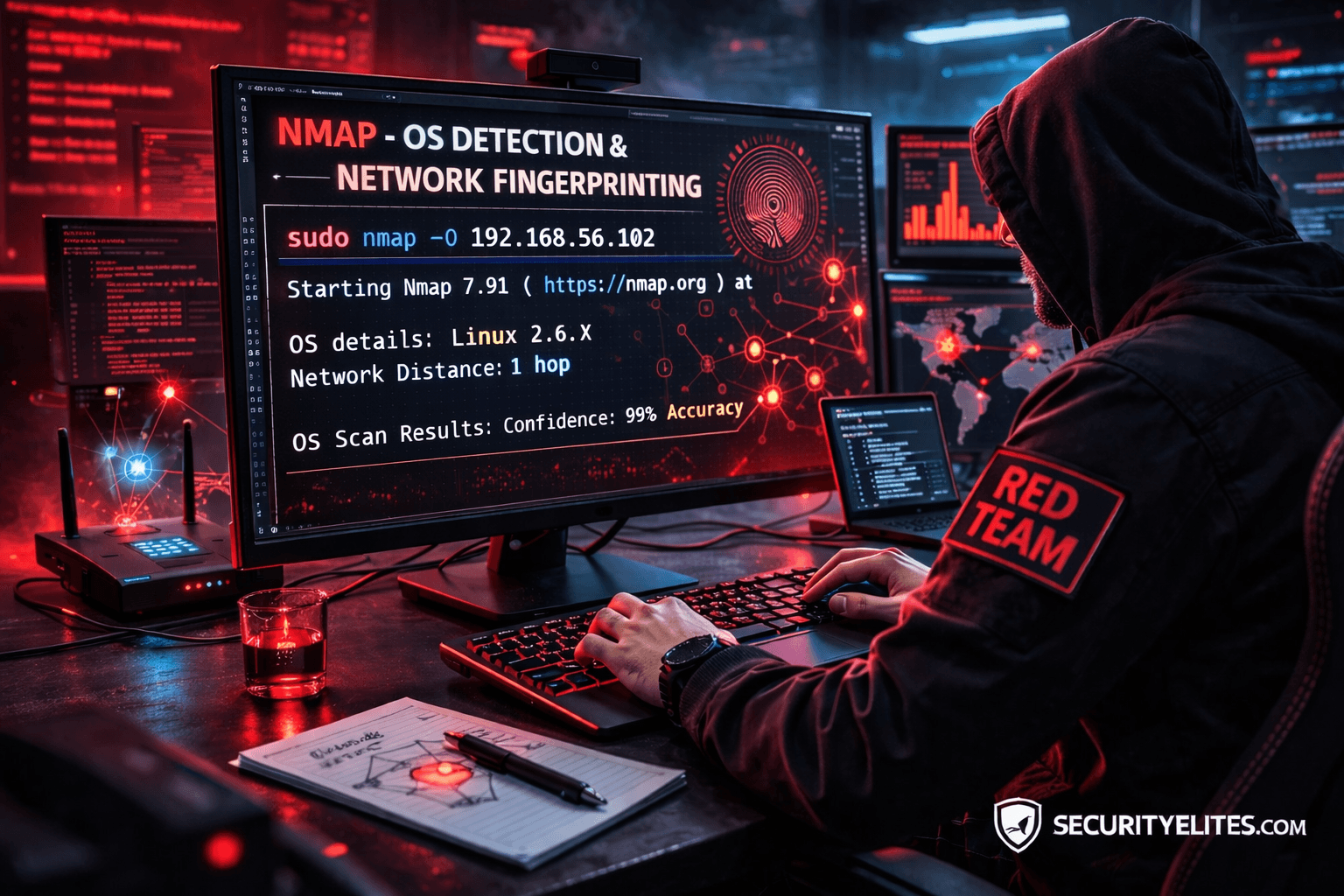
Network Scanning Tutorial Using Nmap Day 5— OS Detection & Network Fingerprinting (Professional Level)
Network Scanning Tutorial Using Nmap Day 5 - Learn operating system detection and network fingerprinting using Nmap like professional penetration…
DVWA to Bug Bounty Day 3: Hidden Endpoints & Parameter Discovery Guide
DVWA to Bug Bounty Day 3 - Learn how bug bounty hunters discover hidden endpoints, APIs, and parameters to find…
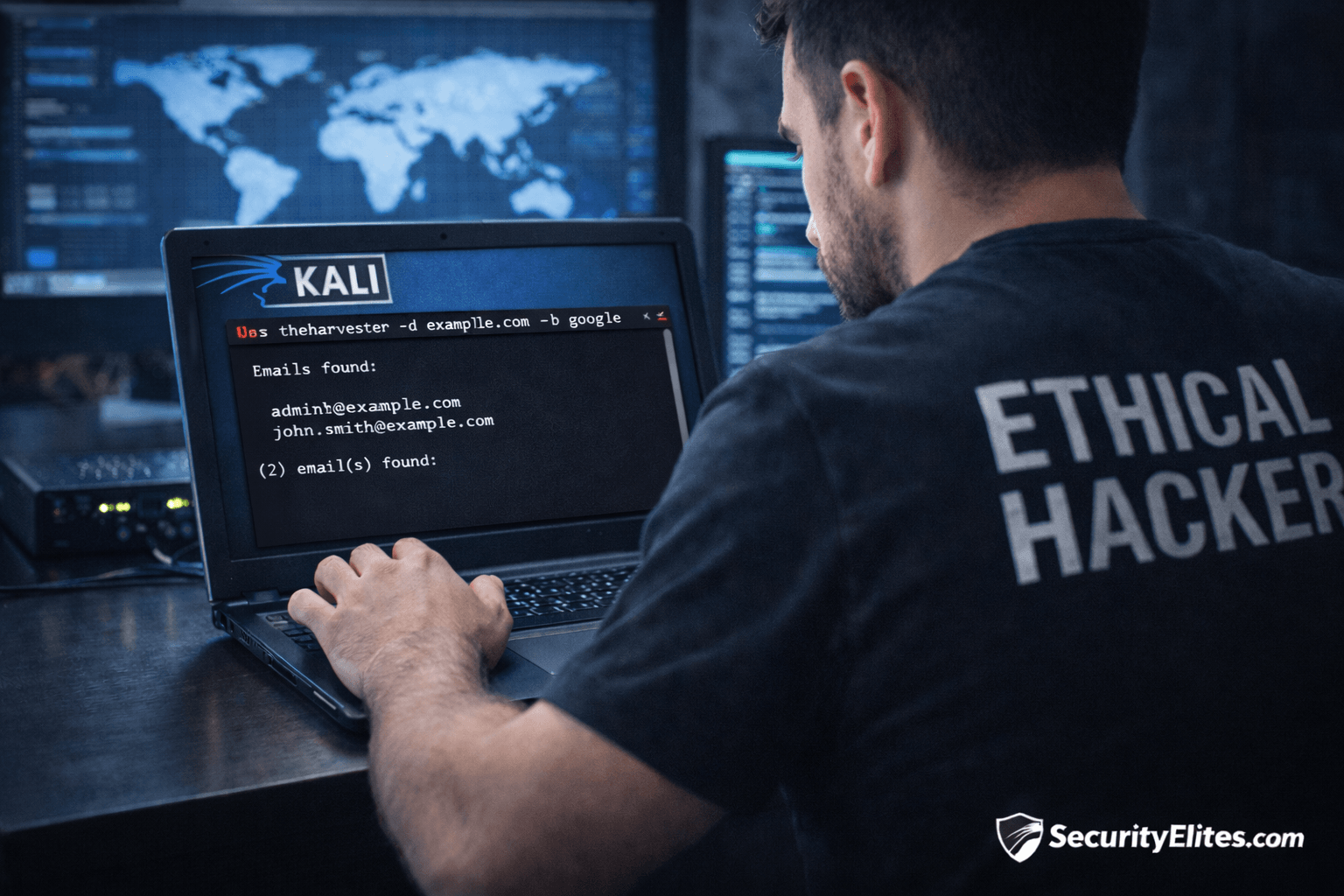
Information Gathering Using Kali Linux Day 5: OSINT Recon with theHarvester
Information Gathering Using Kali Linux Day 5 - Learn Information Gathering using Kali Linux with theHarvester step-by-step. Discover emails, hosts,…
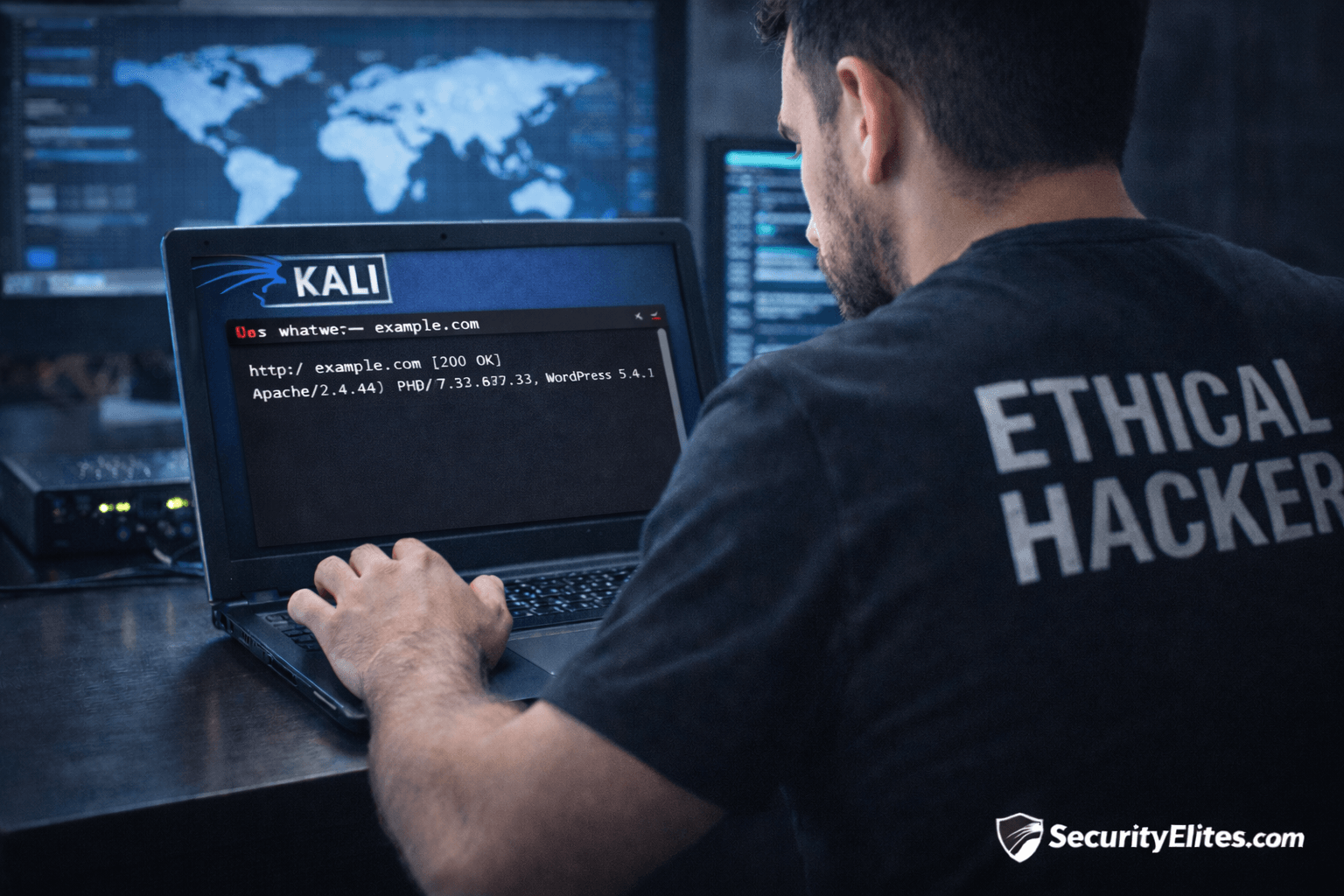
Network Scanning Tutorial Using Nmap Day 4 — Service & Version Enumeration
Network Scanning Tutorial Using Nmap Day 4 - Learn service and version enumeration using Nmap like professional penetration testers. Day…
Information Gathering Using Kali Linux Day 4: Network Mapping with Nmap
Information Gathering Using Kali Linux Day 4 - Learn Information Gathering using Kali Linux with Nmap step-by-step. Discover live hosts,…
DVWA to Bug Bounty Day 2: Subdomain Enumeration & Attack Surface Discovery
DVWA to Bug Bounty Day 2 - Learn professional subdomain enumeration techniques used in real bug bounty hunting. Discover hidden…
Information Gathering Using Kali Linux Day 3: Subdomain Enumeration with Sublist3r
Information Gathering Using Kali Linux Day 3 - Learn Information Gathering using Kali Linux with Sublist3r step-by-step. Discover hidden subdomains…
Network Scanning Tutorial Using Nmap Day 2— Host Discovery & Network Mapping
Network Scanning Tutorial Using Nmap Day 2 - Learn host discovery and network mapping using Nmap like professional ethical hackers.…