Footprinting & Reconnaissance
Footprinting and reconnaissance are the first and most critical phases of ethical hacking, where security professionals gather intelligence about a target before launching any attack simulation. This section covers passive and active reconnaissance techniques including domain analysis, WHOIS lookup, DNS enumeration, social media intelligence, and public data mining. You’ll learn how ethical hackers use reconnaissance tools to map attack surfaces, identify entry points, and collect valuable system information. Step-by-step tutorials, tool guides, and lab demonstrations will help you master information gathering legally and effectively.
37 articles
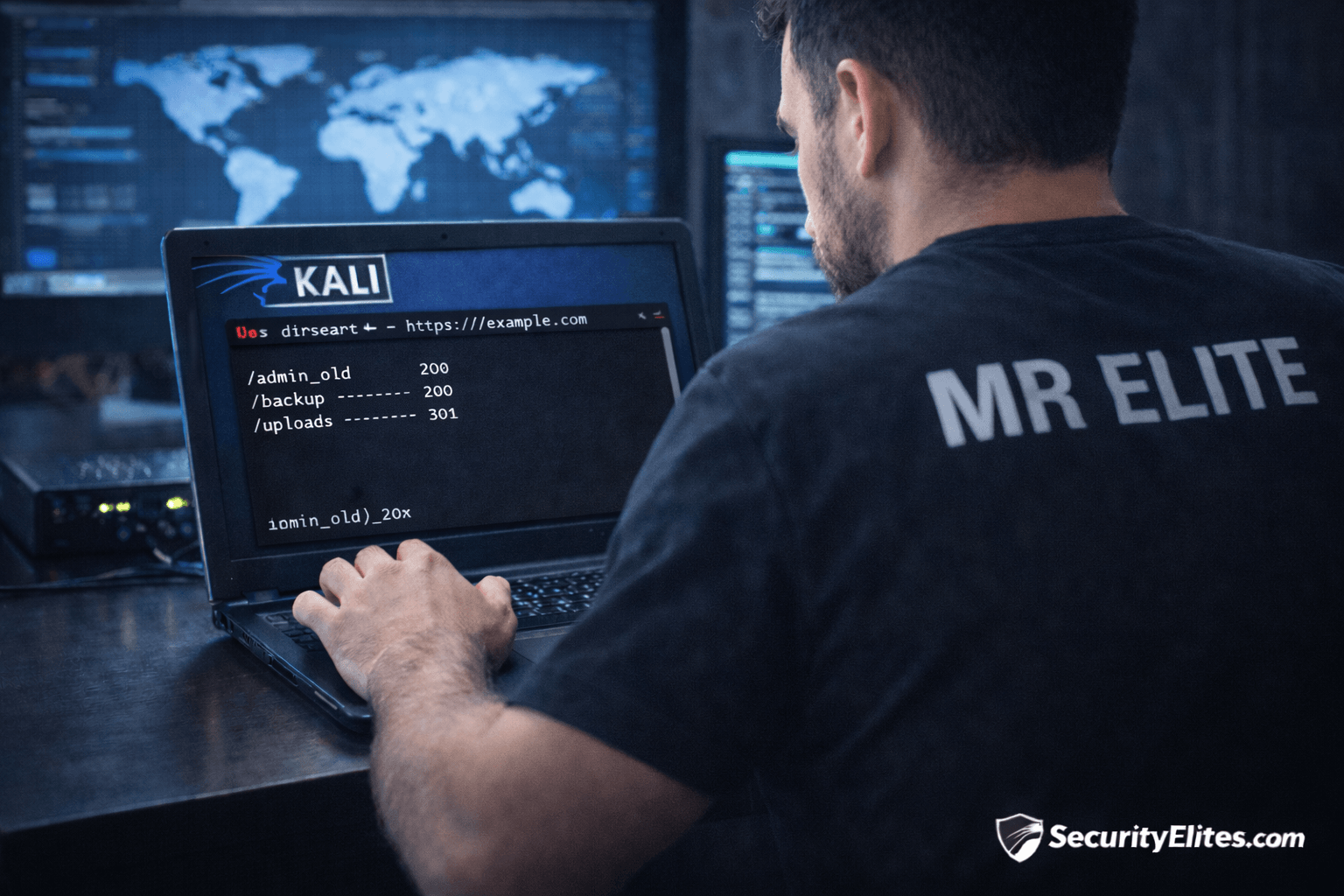
Information Gathering Using Kali Linux Day 7: Directory Discovery with Dirsearch
Information Gathering Using Kali Linux Day 7 - Learn Information Gathering using Kali Linux with Dirsearch step-by-step. Discover hidden directories…
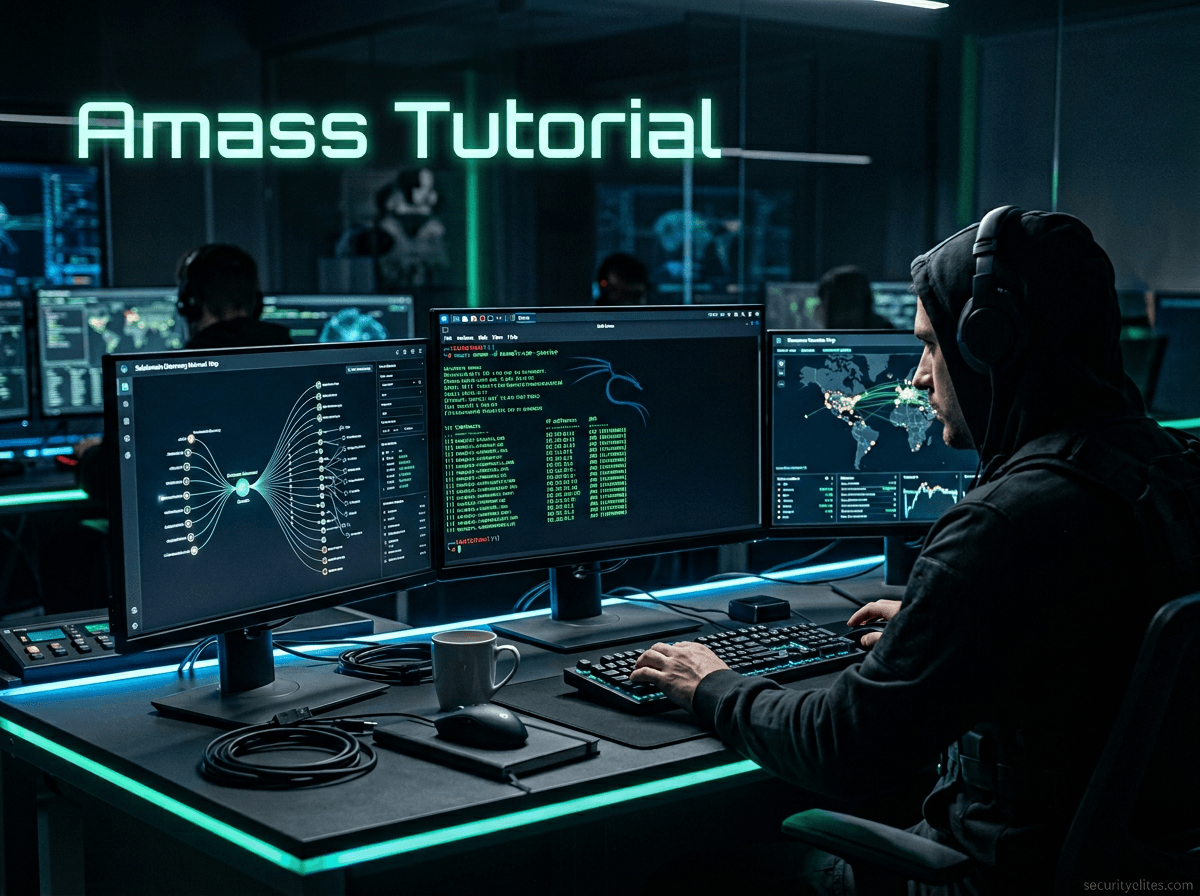
Amass Tutorial (2026): Powerful Subdomain Enumeration Guide for Kali Linux
Learn Amass tutorial for subdomain enumeration and reconnaissance in Kali Linux. Step-by-step ethical hacking guide used by penetration testers and…
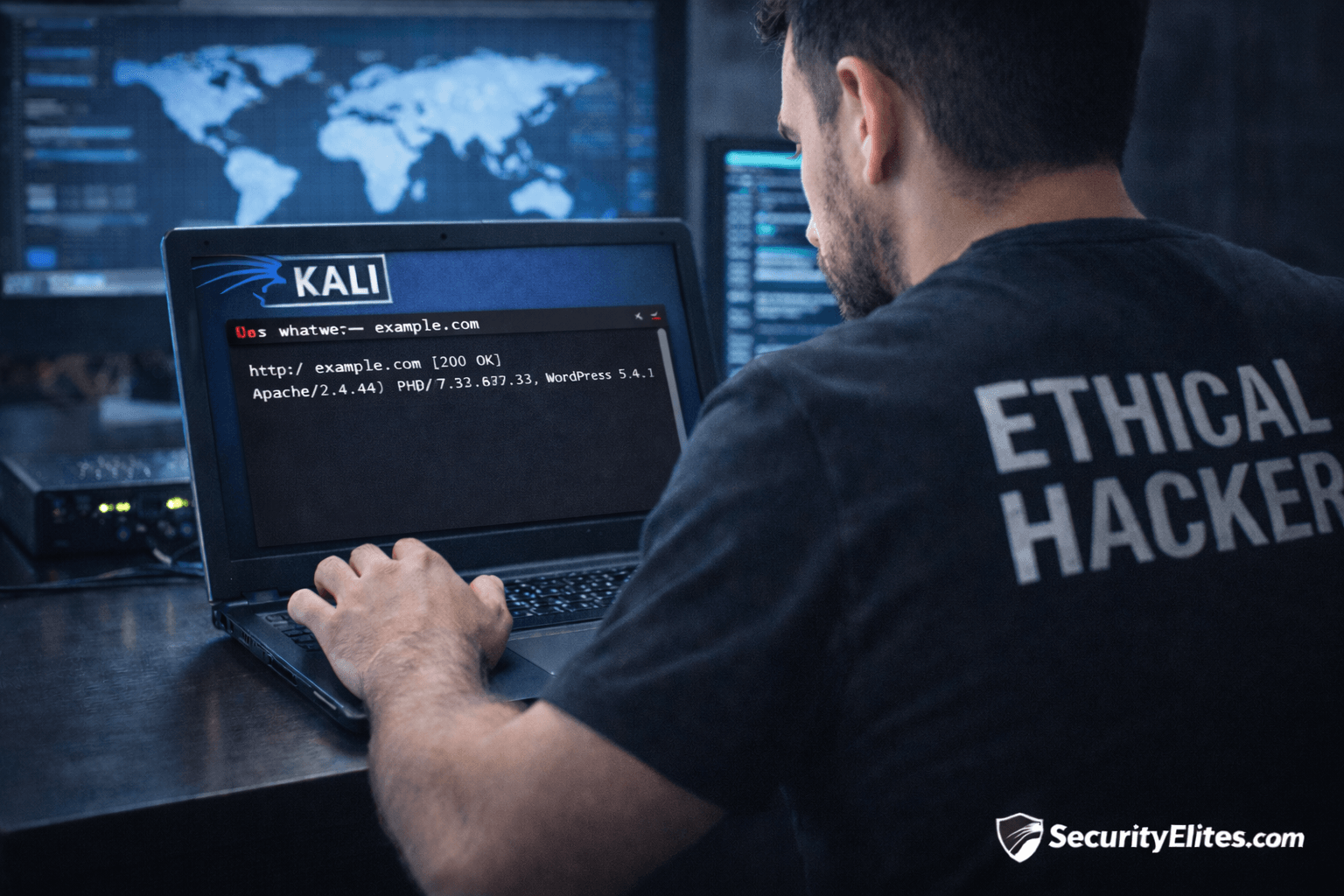
Information Gathering Using Kali Linux Day 6: Technology Fingerprinting with WhatWeb
Information Gathering Using Kali Linux Day 6 - Learn Information Gathering using Kali Linux with WhatWeb step-by-step. Detect website technologies,…
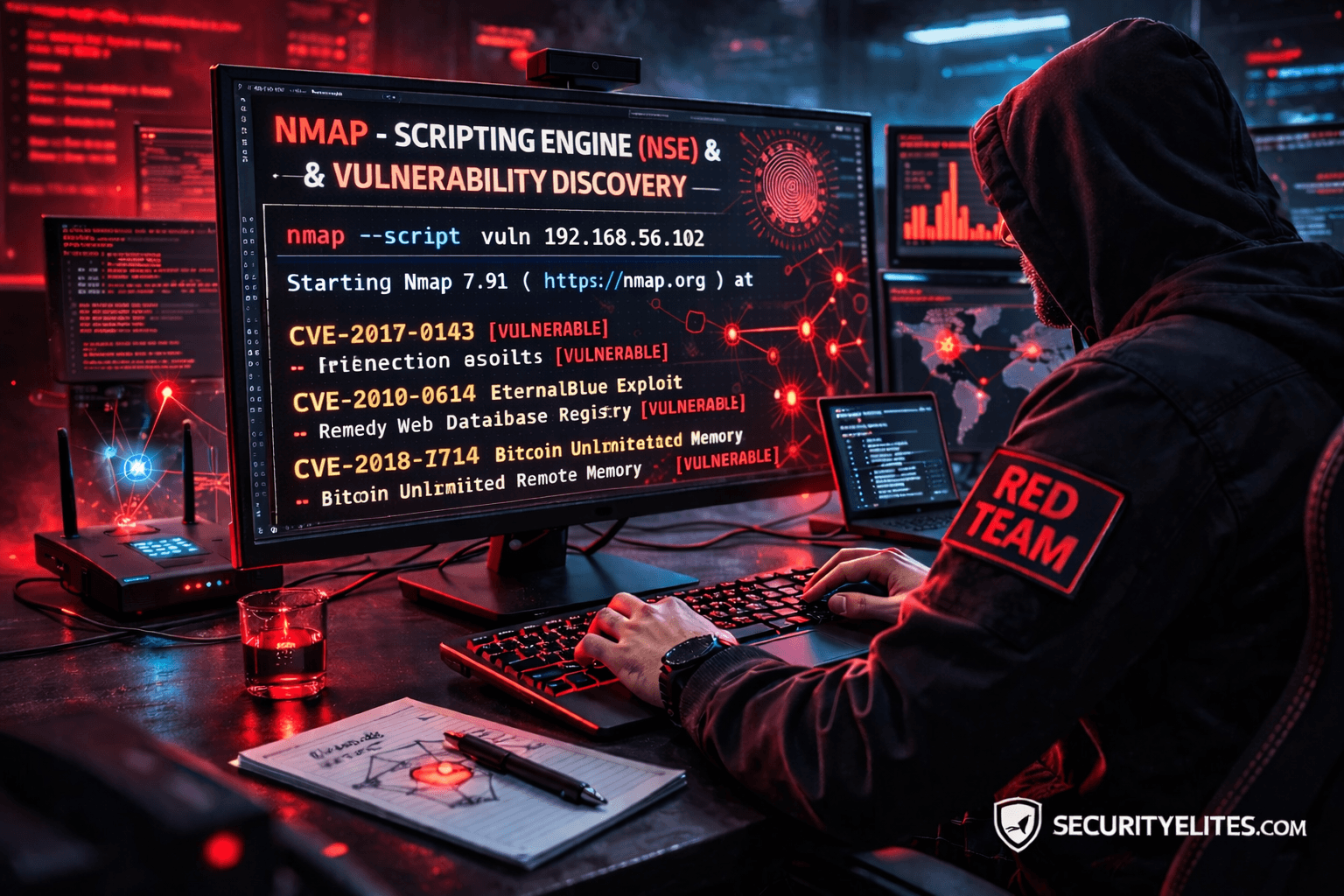
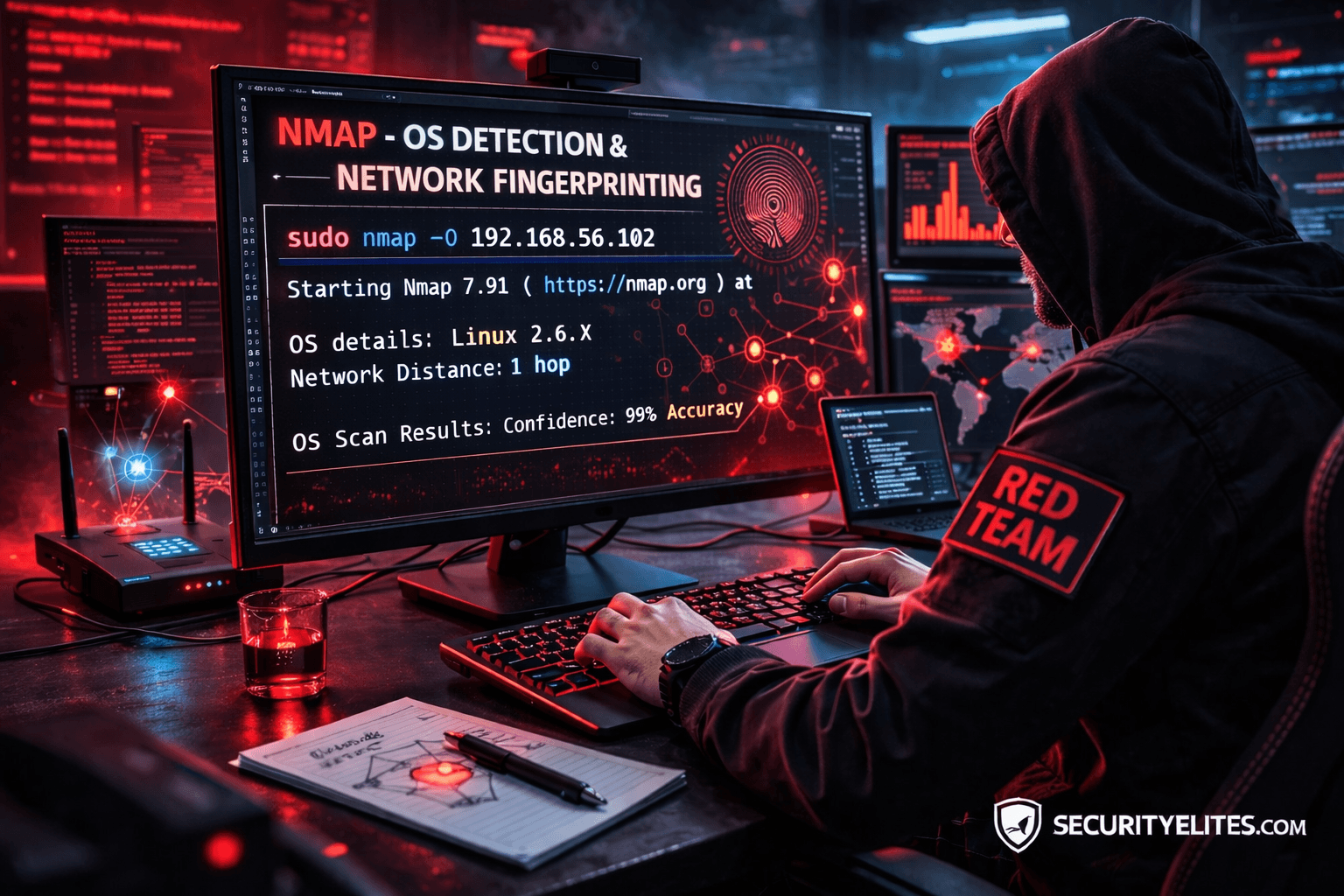
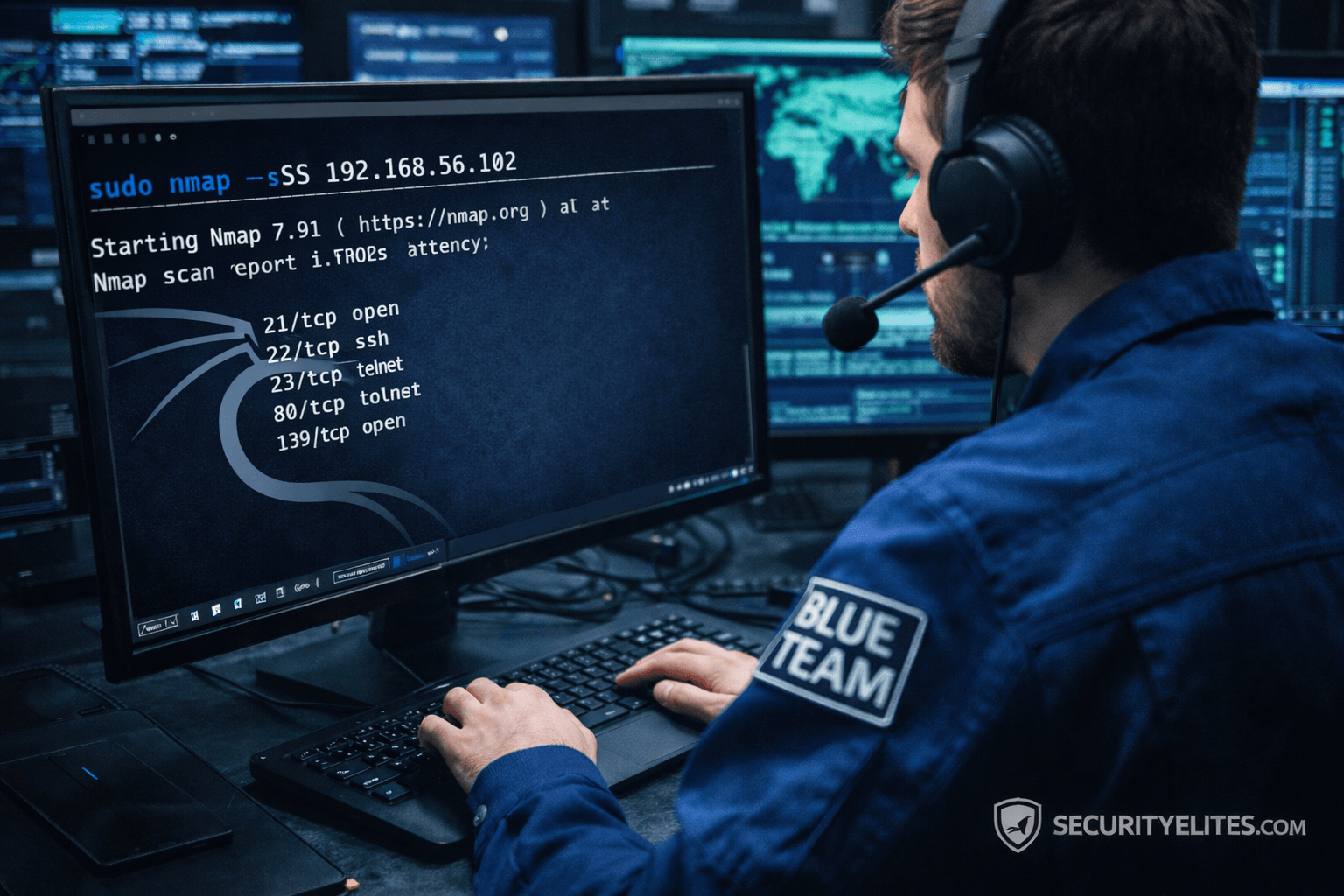
Network Scanning Tutorial Using Nmap Day 5— OS Detection & Network Fingerprinting (Professional Level)
Network Scanning Tutorial Using Nmap Day 5 - Learn operating system detection and network fingerprinting using Nmap like professional penetration…
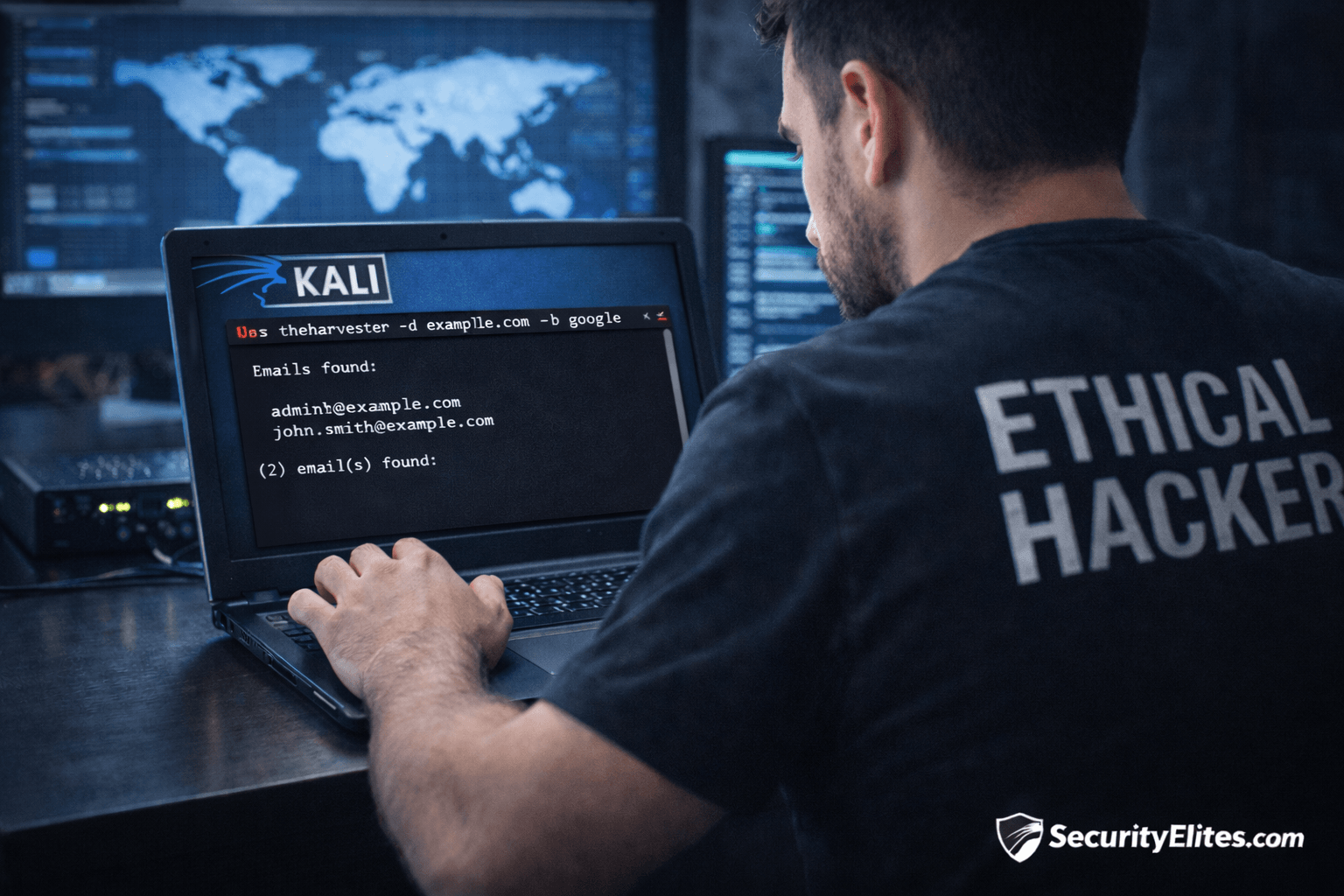
Information Gathering Using Kali Linux Day 5: OSINT Recon with theHarvester
Information Gathering Using Kali Linux Day 5 - Learn Information Gathering using Kali Linux with theHarvester step-by-step. Discover emails, hosts,…
Network Scanning Tutorial Using Nmap Day 4 — Service & Version Enumeration
Network Scanning Tutorial Using Nmap Day 4 - Learn service and version enumeration using Nmap like professional penetration testers. Day…
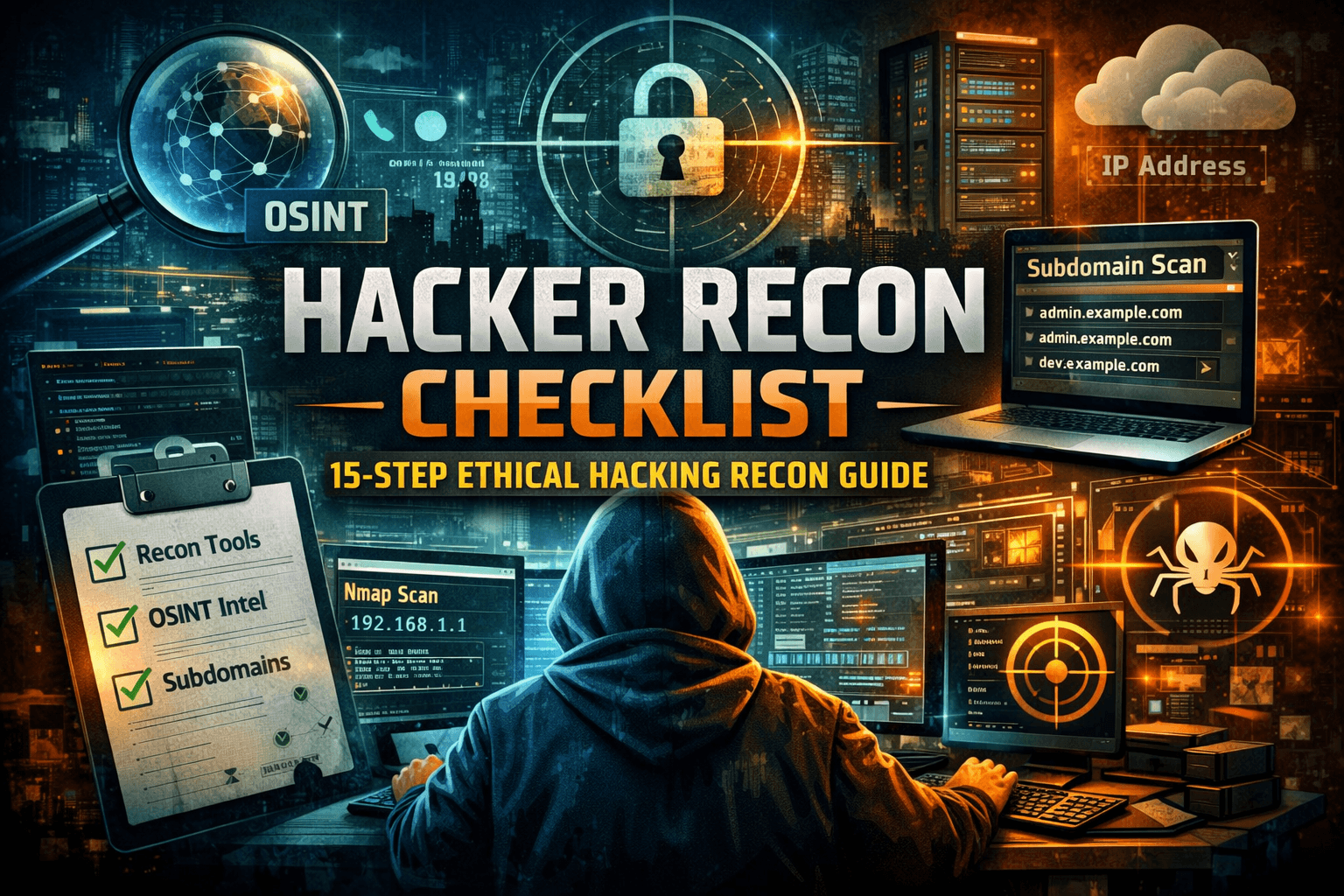
Hacker Recon Checklist: 10-Step Ethical Hacking Recon Guide
Learn the hacker recon checklist used in penetration testing and bug bounty hunting. Step-by-step reconnaissance guide with tools and practical…
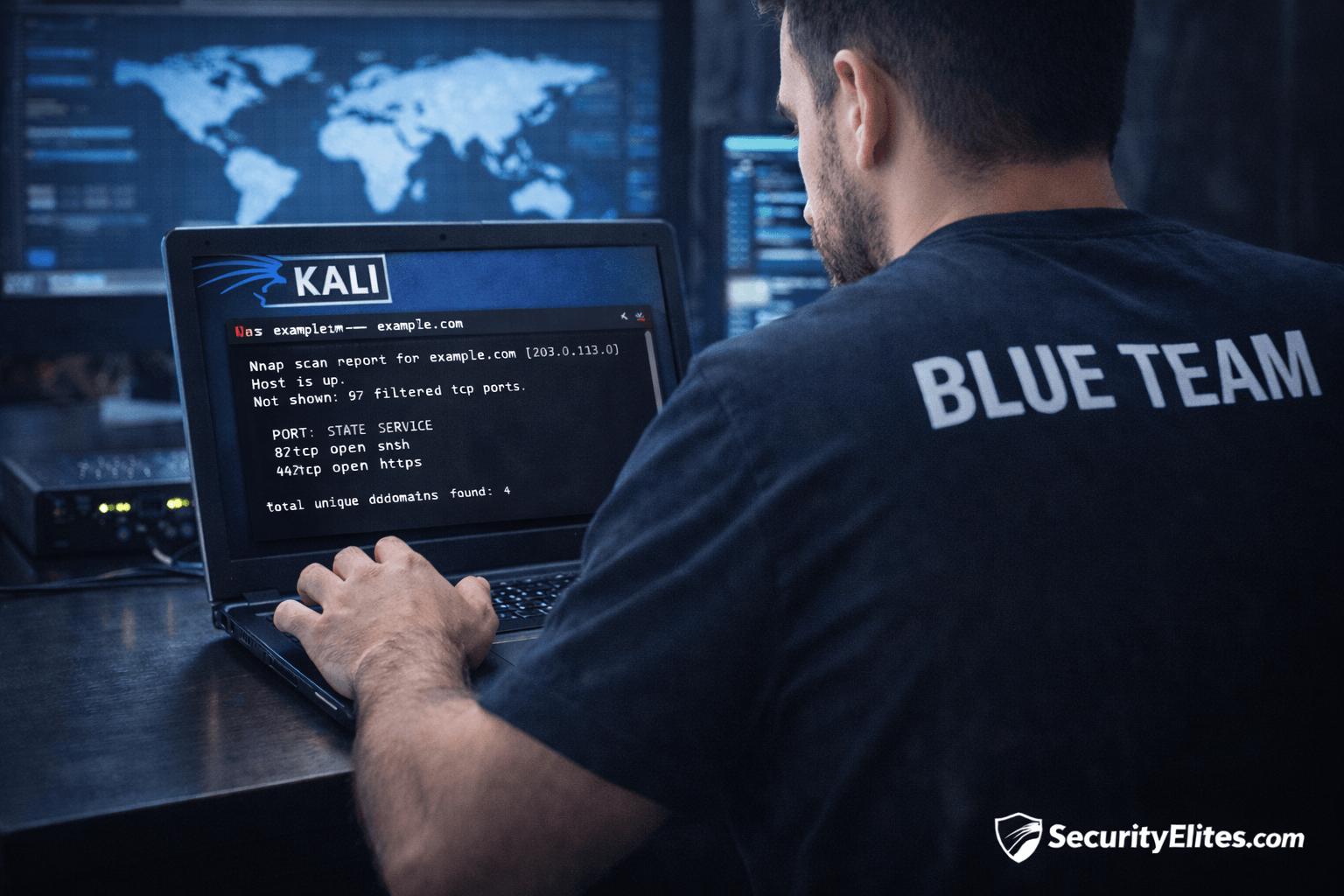
Information Gathering Using Kali Linux Day 4: Network Mapping with Nmap
Information Gathering Using Kali Linux Day 4 - Learn Information Gathering using Kali Linux with Nmap step-by-step. Discover live hosts,…
Network Scanning Tutorial Using Nmap Day 3 — Port Scanning Techniques Deep Dive
Network Scanning Tutorial Using Nmap Day 3 - Learn professional port scanning using Nmap including TCP SYN, Connect, UDP, and…