Footprinting & Reconnaissance
Footprinting and reconnaissance are the first and most critical phases of ethical hacking, where security professionals gather intelligence about a target before launching any attack simulation. This section covers passive and active reconnaissance techniques including domain analysis, WHOIS lookup, DNS enumeration, social media intelligence, and public data mining. You’ll learn how ethical hackers use reconnaissance tools to map attack surfaces, identify entry points, and collect valuable system information. Step-by-step tutorials, tool guides, and lab demonstrations will help you master information gathering legally and effectively.
37 articles
25 Google Dorks Hackers Use to Find Vulnerable Websites (2026 Guide)
Discover 25 powerful Google Dorks hackers use to find vulnerable websites, exposed databases, admin panels, and hidden files. Complete Google…
Information Gathering Using Kali Linux Day 11: Recon Automation with Recon-ng
Information Gathering Using Kali Linux Day 11 - Master Information Gathering using Kali Linux with Recon-ng. Learn full reconnaissance automation…
Amass Cheat Sheet (70+ Commands & Examples) – Ultimate 2026 Guide for Recon & Bug Bounty
Master the Amass Cheat Sheet with 60+ commands, real examples, and hands-on labs. Learn domain enumeration for bug bounty and…
NMAP Cheat Sheet (60+ Commands, Examples & Hands-on Lab) – Ultimate 2026 Guide
Complete NMAP Cheat Sheet with 60+ commands, real examples, Kali Linux installation, and hands-on labs. Learn NMAP penetration testing fast.
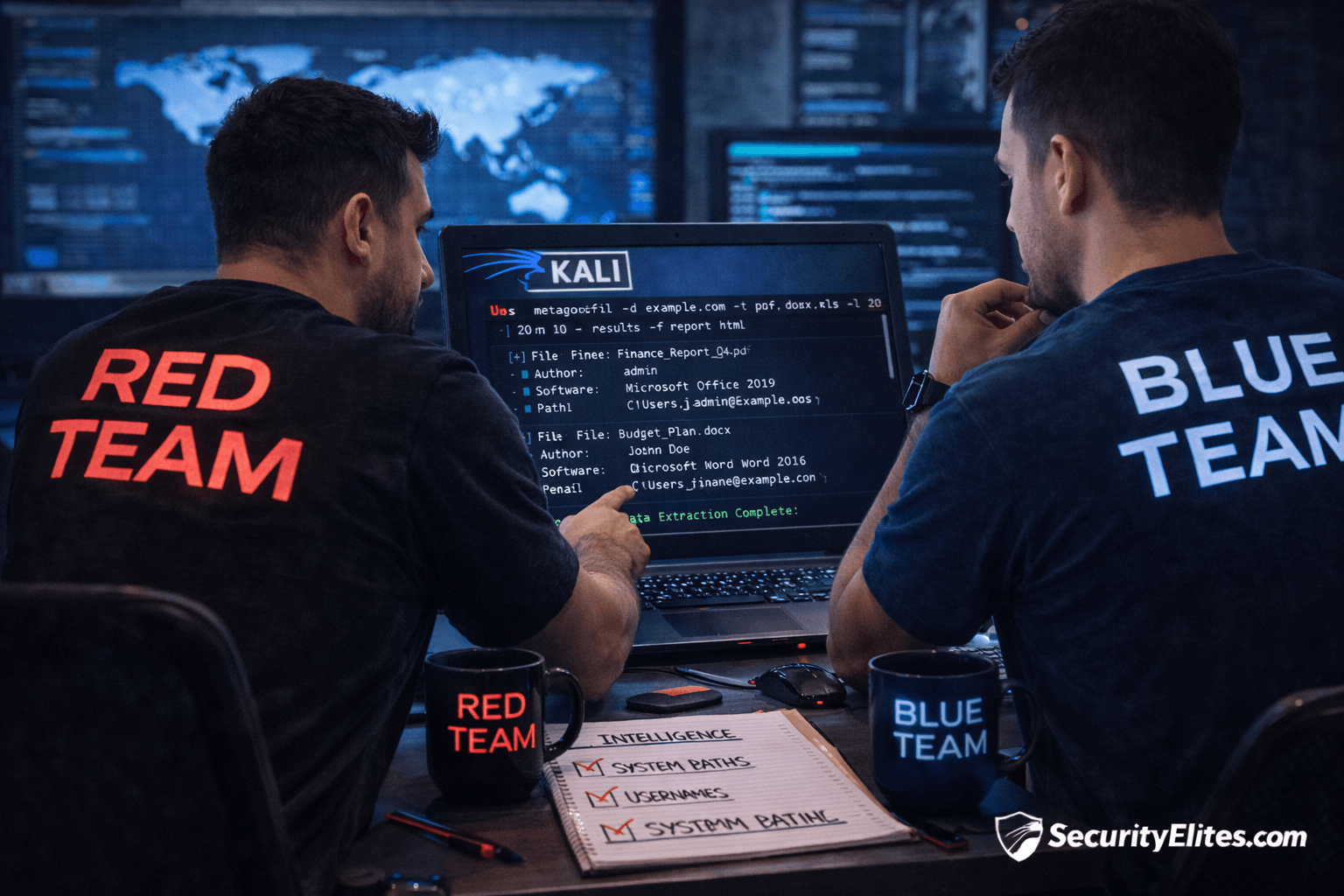
Information Gathering Using Kali Linux Day 10: Metadata Intelligence with Metagoofil
Information Gathering Using Kali Linux Day 10 - Learn Information Gathering using Kali Linux with Metagoofil step-by-step. Extract hidden metadata…
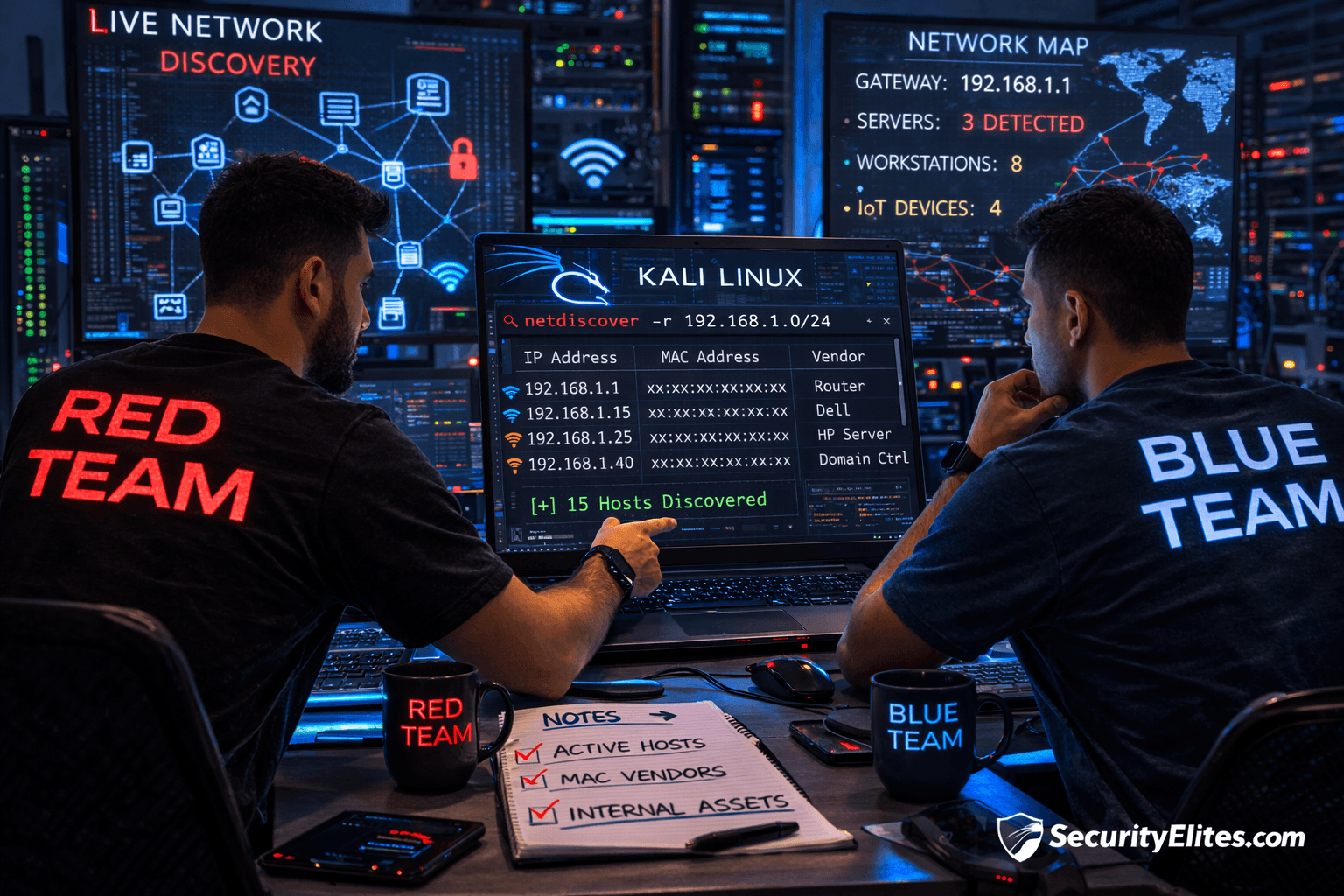
Information Gathering Using Kali Linux Day 9: Internal Network Discovery with Netdiscover
Information Gathering Using Kali Linux Day 9 - Learn Information Gathering using Kali Linux with Netdiscover step-by-step. Discover live internal…
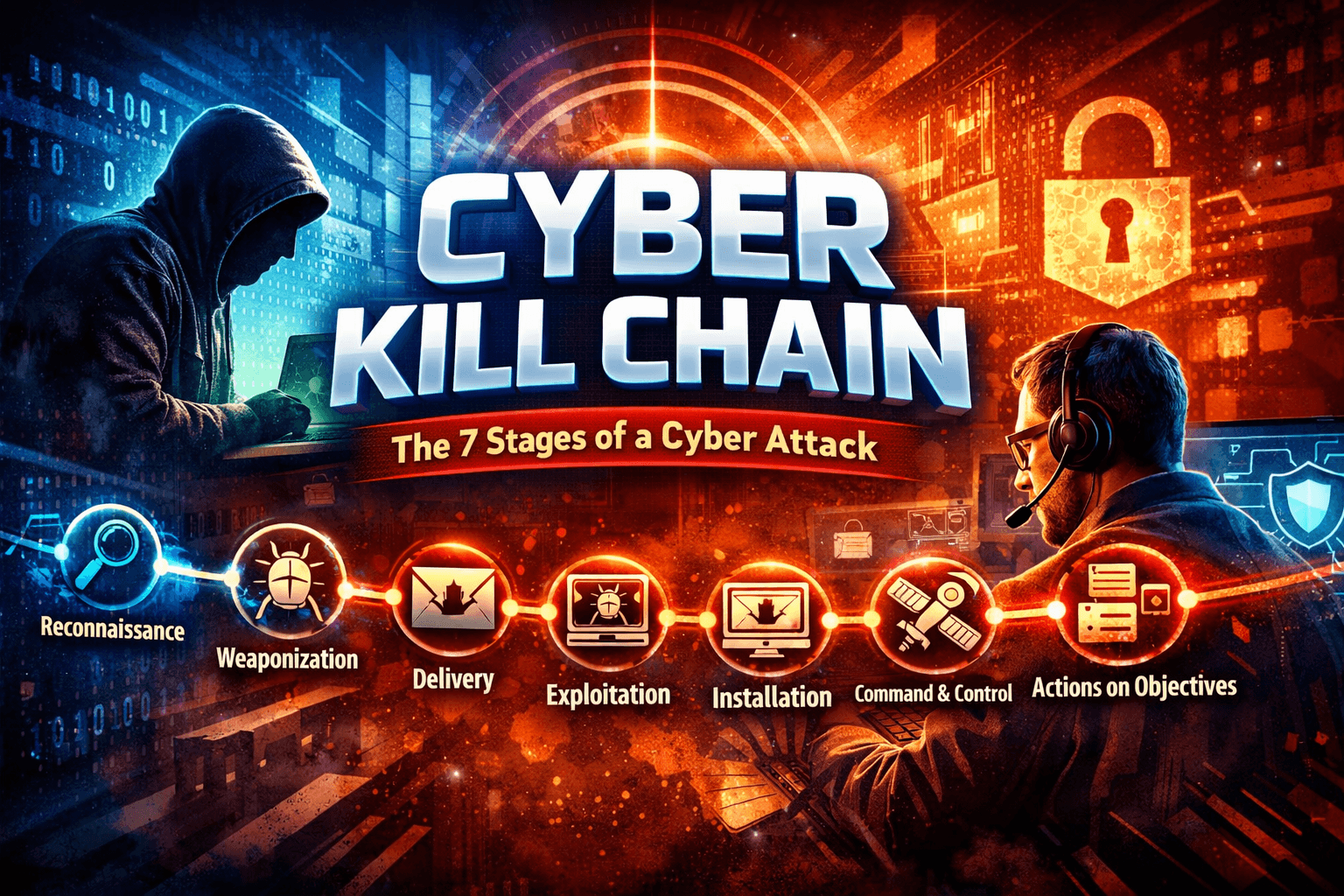
Cyber Kill Chain Explained: 7 Stages of a Cyber Attack
Learn the Cyber Kill Chain explained with ethical hacking examples, attacker mindset, hands-on labs, and defense strategies.
Information Gathering Using Kali Linux Day 8: Attack Surface Mapping with Amass
Information Gathering Using Kali Linux Day 8 - Learn Information Gathering using Kali Linux with Amass step-by-step. Discover hidden domains…
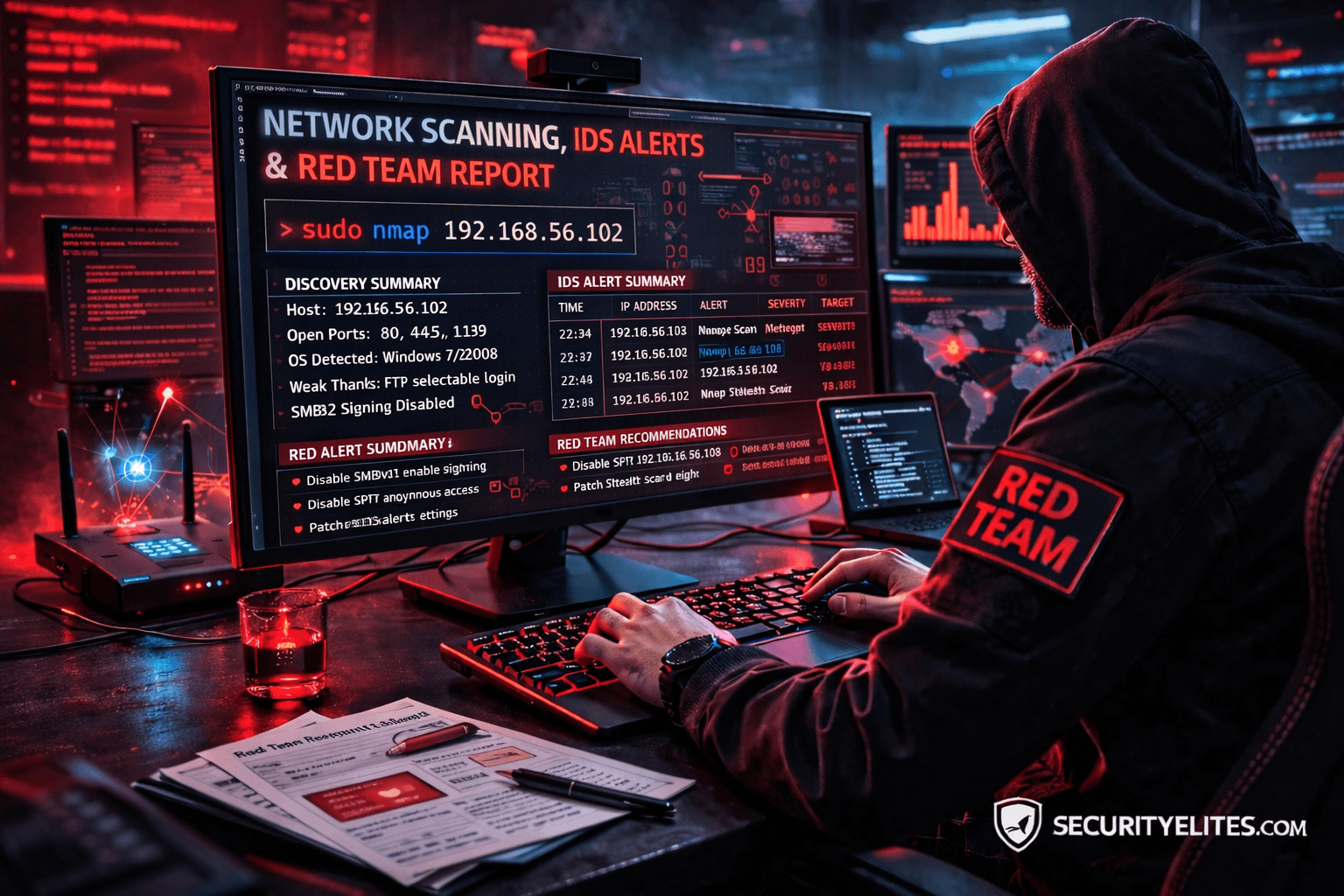
Network Scanning Tutorial Using Nmap Day 7 — Stealth Scanning, IDS Evasion & Red Team Techniques
Network Scanning Tutorial Using Nmap Day 7 - Learn stealth scanning, IDS evasion, and advanced Red Team Nmap techniques used…