Kali Linux Tools
Explore the powerful penetration testing tools built into Kali Linux. This section includes tutorials on Metasploit, Burp Suite, Hydra, Aircrack-ng, Nikto, and more. Learn installation, configuration, and real-world usage through hands-on demonstrations.
92 articles
Kali Linux Day 10 : Metasploit Tutorial Kali Linux 2026 — msfconsole, Modules & First Exploit Complete Guide
Master Metasploit in Kali Linux 2026 — msfconsole commands, exploit modules, payloads & your first real shell. Day 10 complete…
DVWA Brute Force Lab 2026 — Hydra & Burp Intruder Complete Walkthrough Day 2
Master DVWA brute force lab 2026 — Hydra credential attack, Burp Intruder, CSRF token bypass at High security & Impossible-level…
How Hackers Use theHarvester to Find Emails in Seconds (Most Don’t Know This)
Discover how hackers use theHarvester to harvest real employee emails from public sources in seconds — the OSINT technique most…
Kali Linux on M3 Mac 2026 — Ultimate Install Guide (UTM + Native Tools)
Install Kali Linux on M3 Mac 2026 — UTM VM, native ARM tools, WiFi adapter setup & full configuration guide…
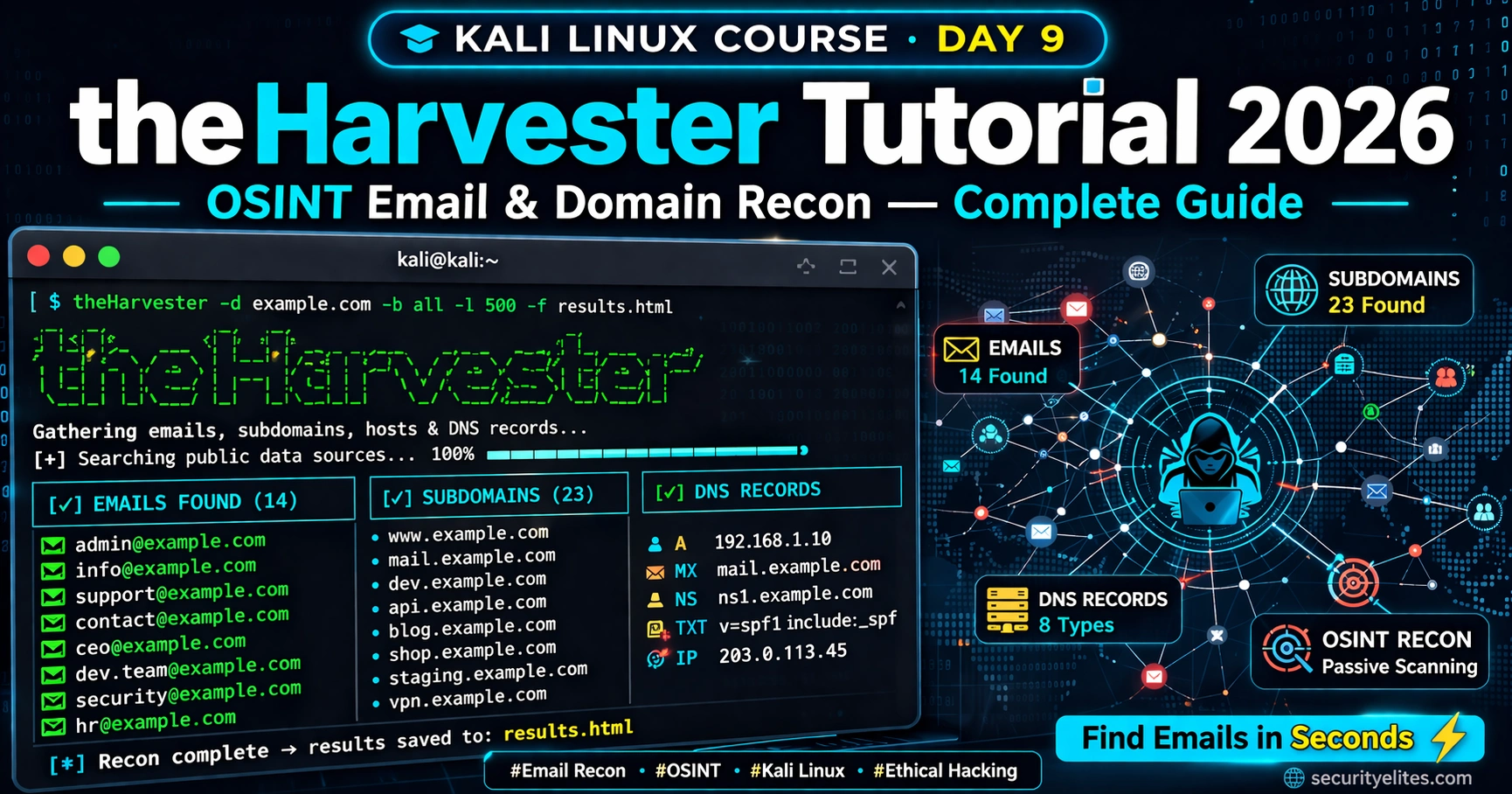
Kali Linux Day 9 : theHarvester Tutorial 2026 — OSINT Email & Domain Recon Complete Guide
Master theHarvester in Kali Linux 2026 — collect emails, subdomains & DNS records for OSINT recon. Complete Day 9 guide…
Cloud Security Hacking 2026 — How Attackers Exploit AWS, Azure & GCP (Ethical Hacker’s Guide)
Cloud security hacking is the highest-demand offensive skill of 2026. Learn IAM misconfiguration exploitation, S3 bucket attacks, SSRF to cloud…
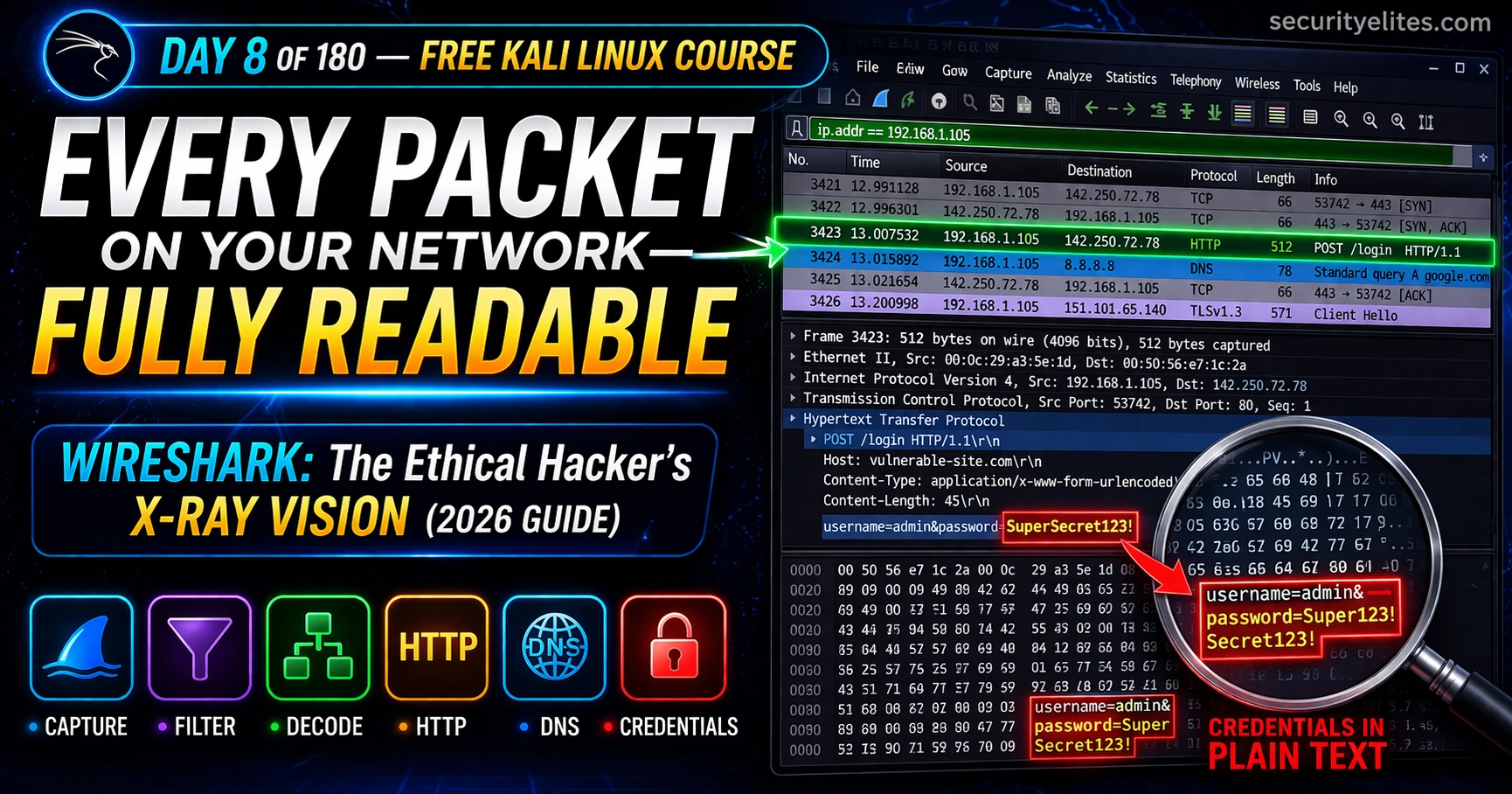
Kali Linux Day 8: Wireshark Tutorial 2026 — Capture & Analyse Real Network Traffic (Complete Guide)
Day 8 of 180. Wireshark Tutorial on Kali Linux from scratch — capture live network traffic, analyze PCAP files, apply…
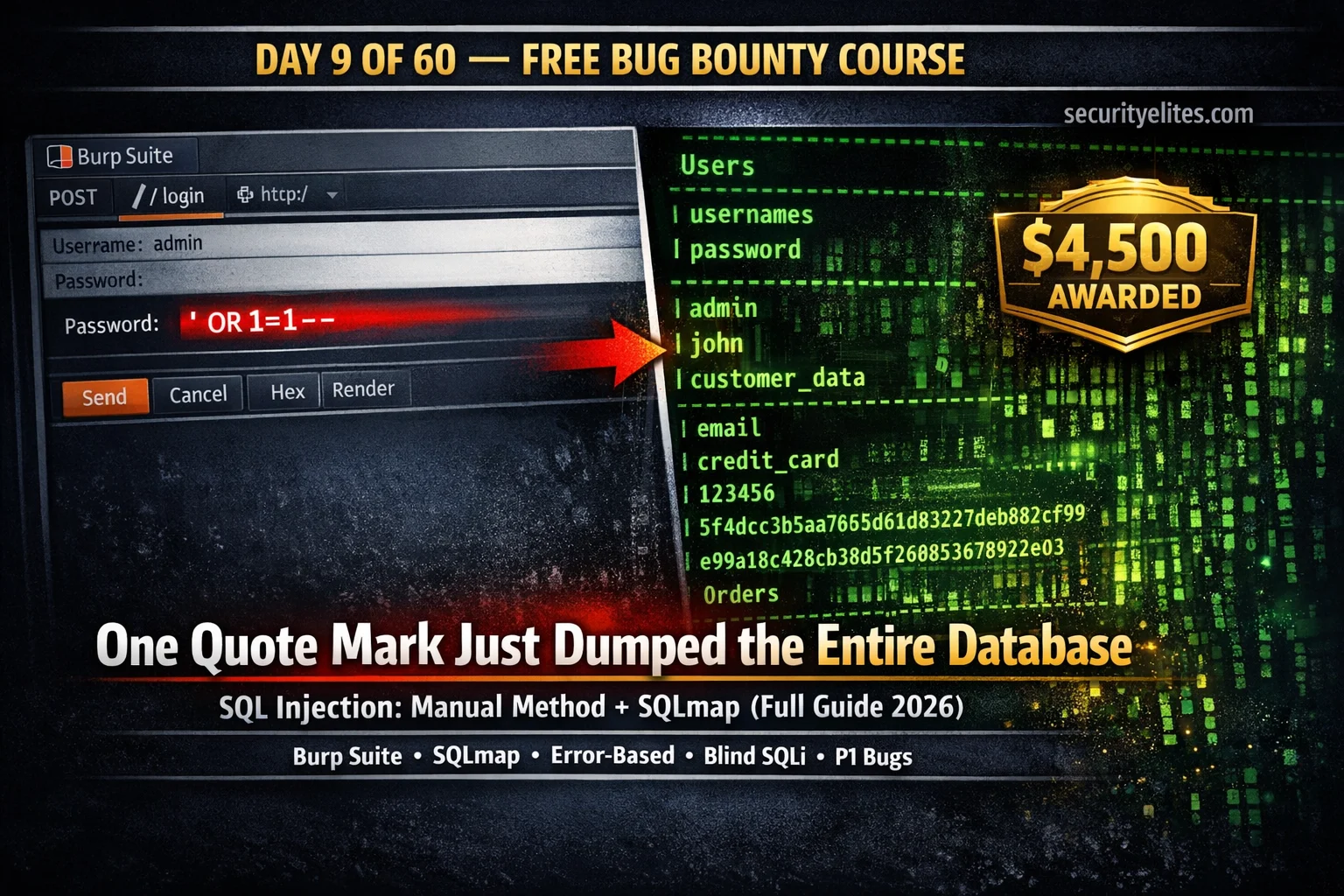
Day 9: SQL Injection for Bug Bounty 2026 — Manual Testing + SQLmap Complete Guide
Day 9 of 60. Learn SQL injection for bug bounty: manual testing with Burp Suite, error-based, UNION-based, blind SQLi, SQLmap…
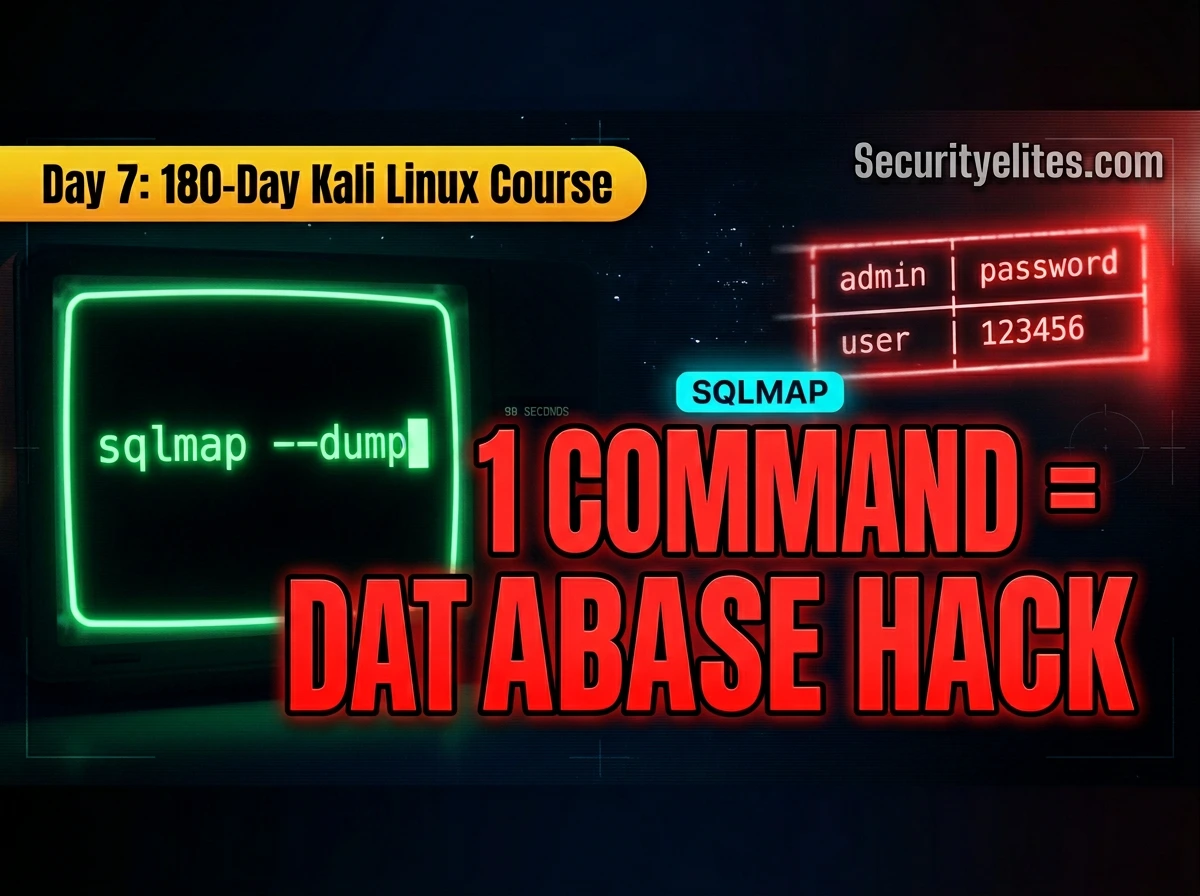
Kali Linux Day 7: SQLmap Tutorial (2026) — Automate SQL Injection Like a Pro 🔥
Complete SQLmap tutorial for Kali Linux — detect SQL injection, enumerate databases, extract tables, dump credentials, use Burp request files,…