All Articles
Cybersecurity tutorials, hacking guides, and security research.
Day 18: File Upload Vulnerabilities — From Image Upload to Web Shell (2026)
Understand file upload vulnerabilities from first principles — how validation is bypassed, how web shells work, full DVWA demos at…
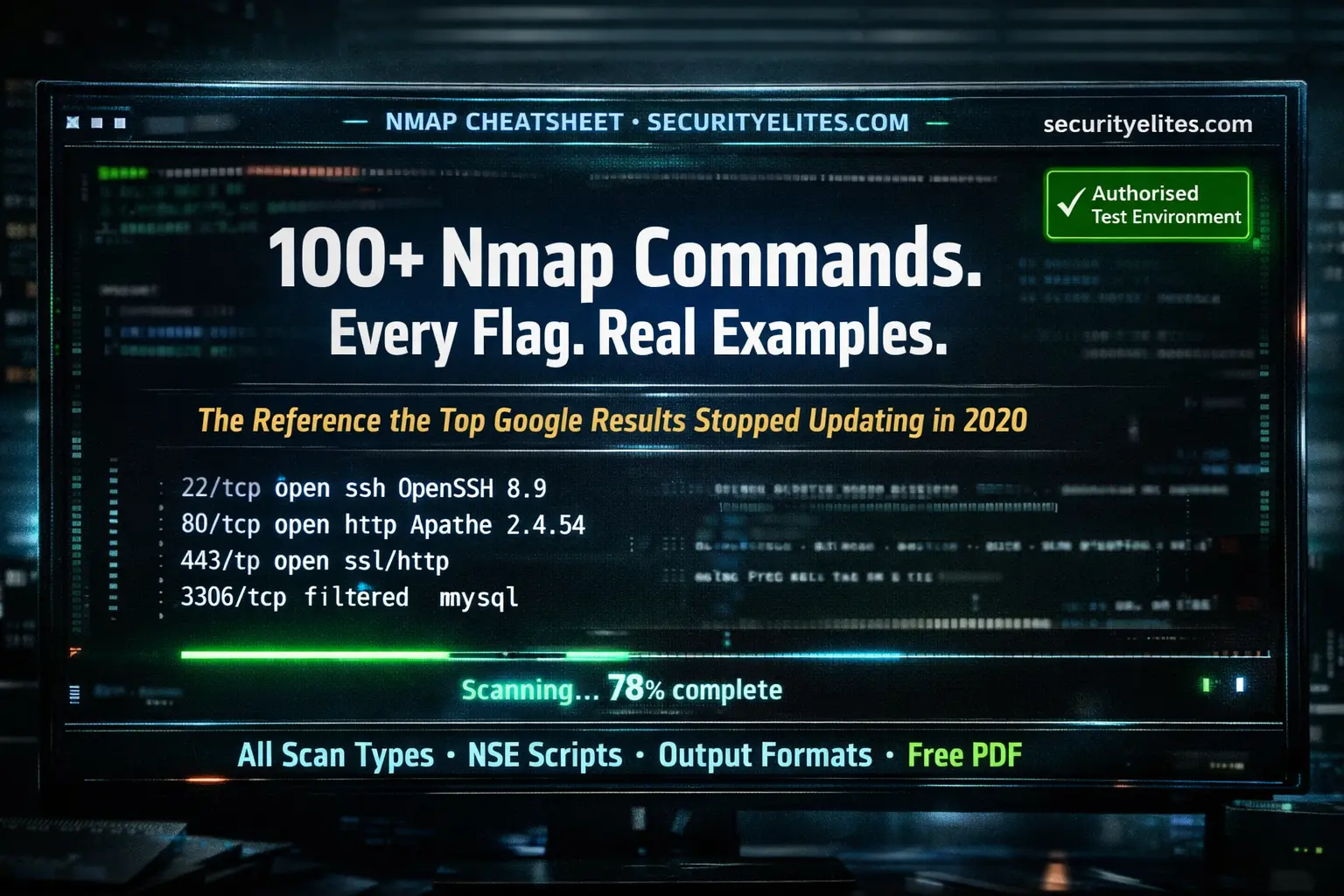
Nmap Commands with Examples 2026 — The Complete Reference (Every Flag, Every Scan Type, Free PDF Cheat Sheet)
Every Nmap commands with examples — covering all scan types, timing options, output formats, NSE scripts, firewall evasion techniques, and…
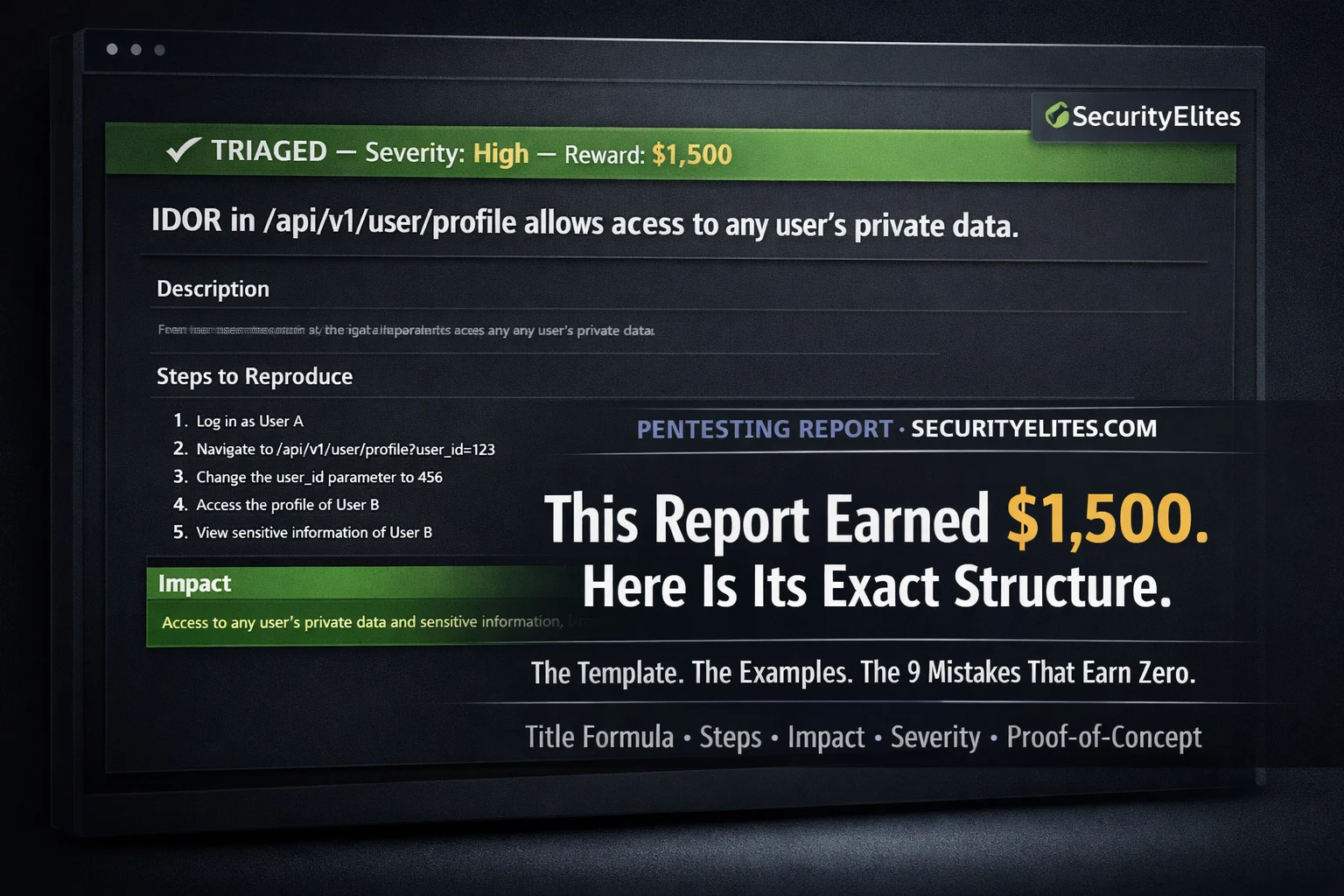
Google Bug Bounty Program — How Ethical Hackers Legally Earn $100–$31,337 Finding Gmail Vulnerabilities (2026)
Learn how ethical hackers legally earn $100 to $31,337 through Google's Vulnerability Reward Program aka Google Bug Bounty Program. Scope,…
Cybersecurity for Beginners: Where to Start in 2026 — The Only Guide You Need (4 Career Paths, Real Salaries)
Where should you start cybersecurity in 2026? Cybersecurity for beginners guide maps 4 career paths (ethical hacking, blue team), the…
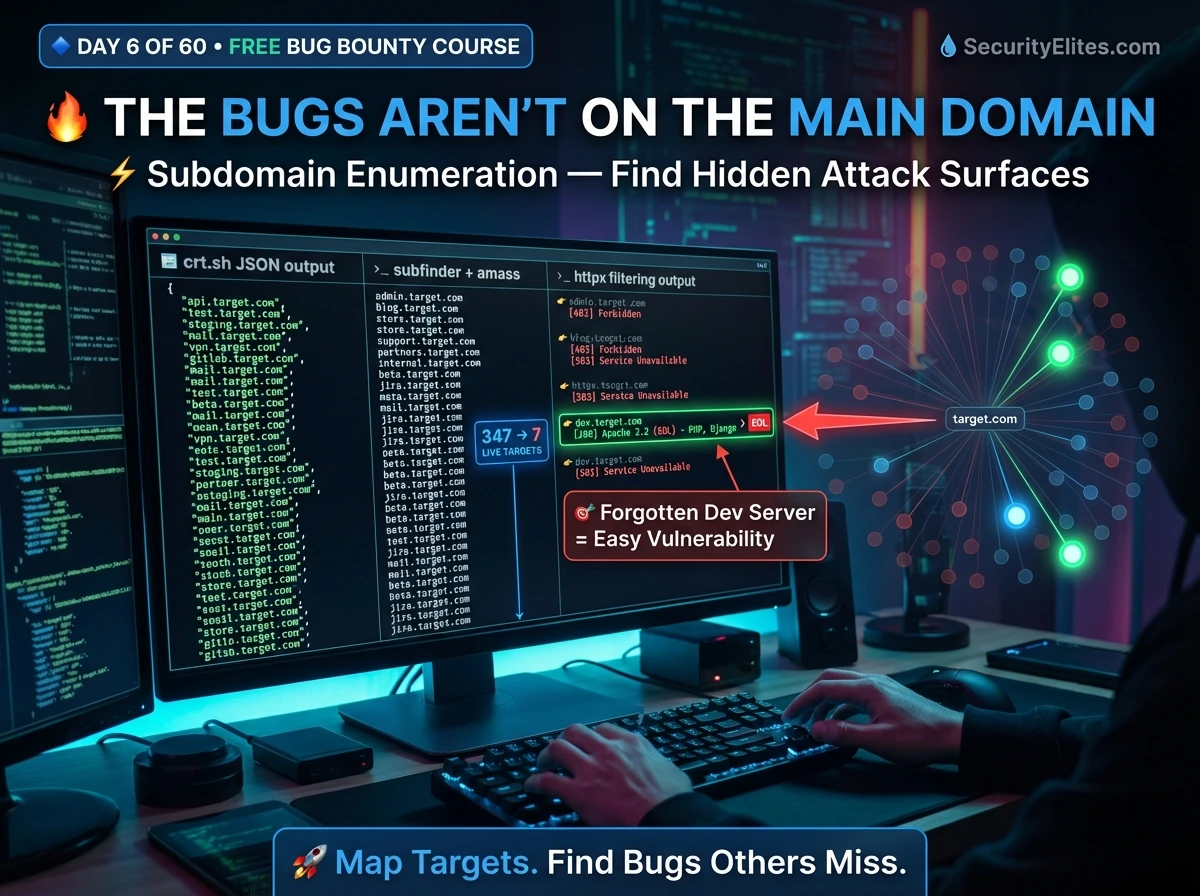
Bug Bounty Day 6: Subdomain Enumeration — Build Your Full Attack Surface Map (2026)
Master subdomain enumeration for bug bounty — Subfinder, Amass, crt.sh, httpx live filtering, ffuf directory fuzzing, and building a professional…
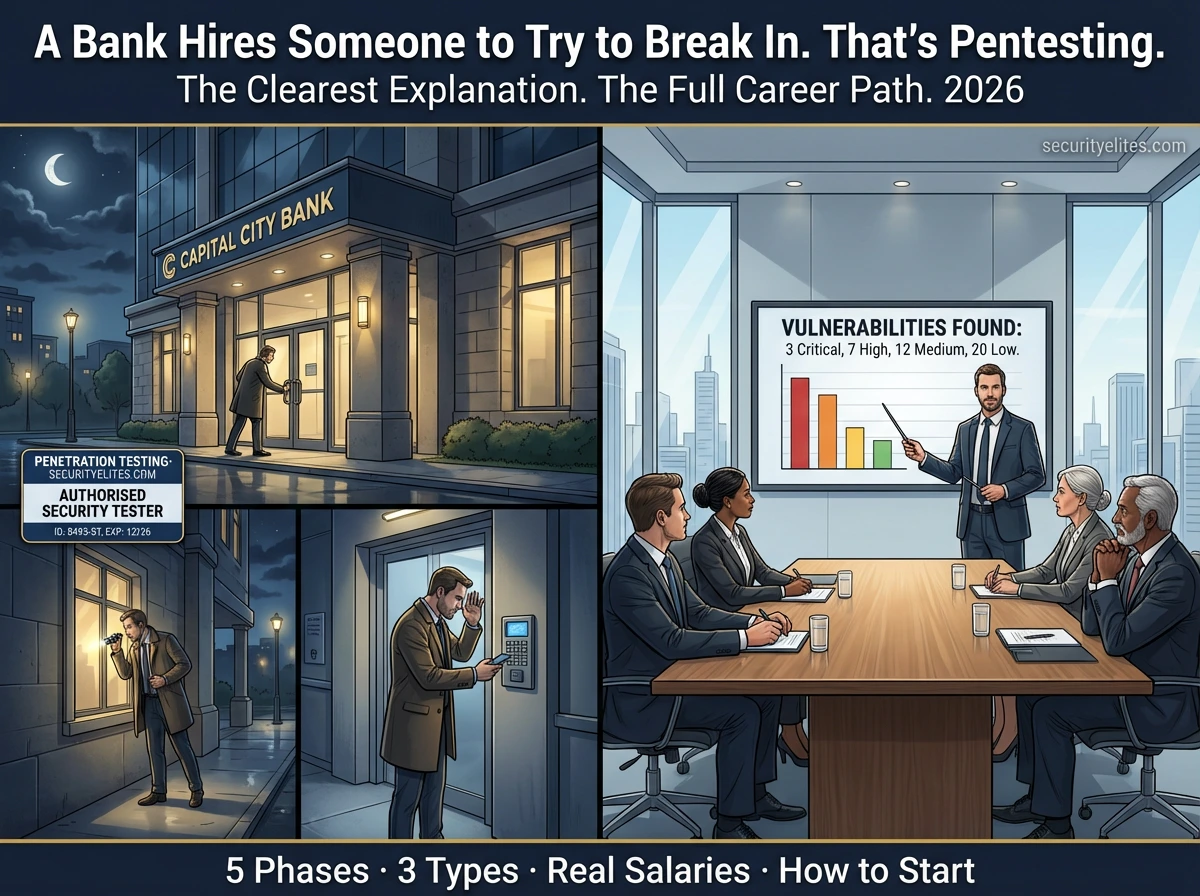
What Is Penetration Testing? The Simplest Explanation You Will Ever Read — With Real-World Examples (2026)
What is Penetration testing explained simply — how it works, the 5 phases professionals follow, types of pentest, who hires…