All Articles
Cybersecurity tutorials, hacking guides, and security research.
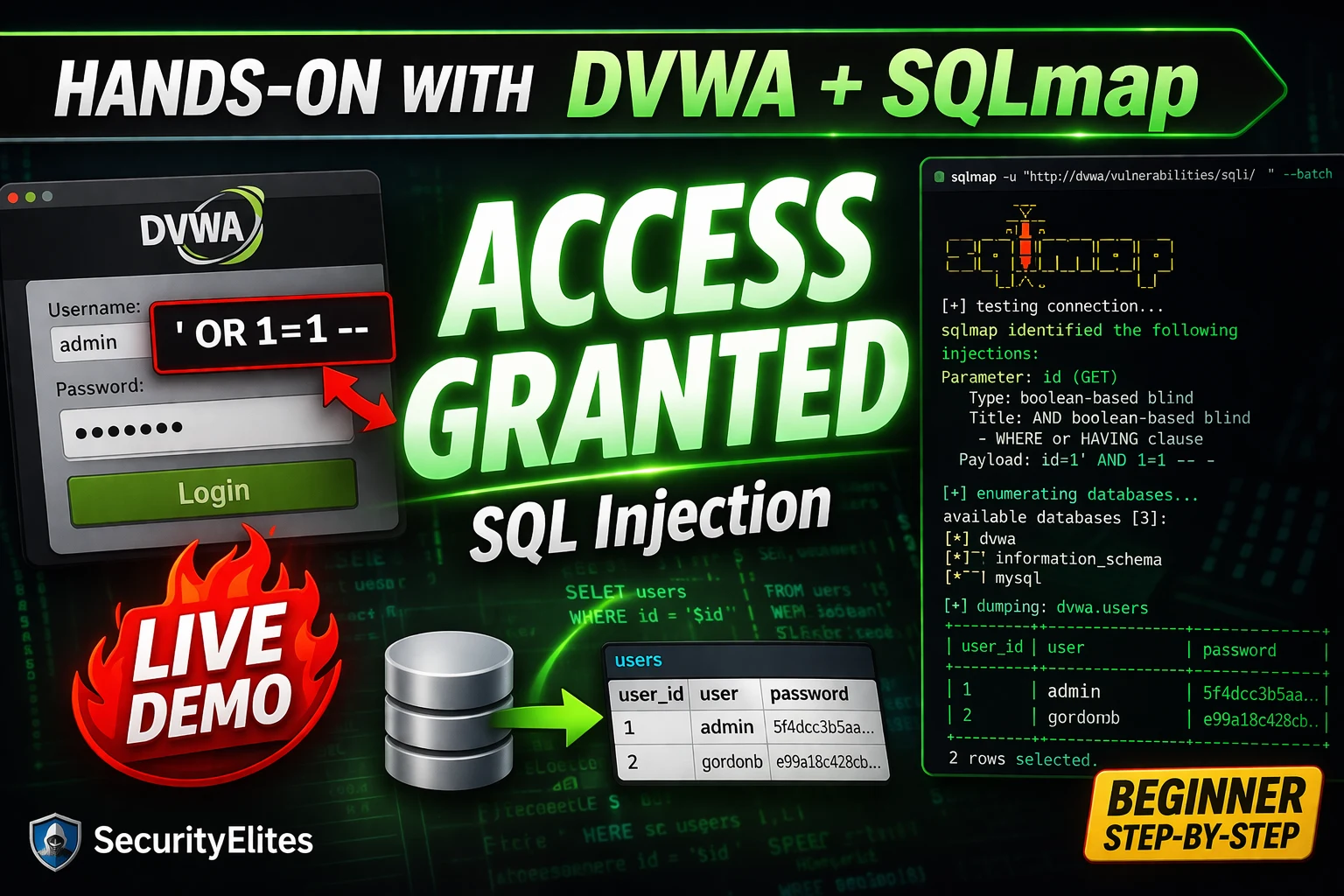
SQL Injection Tutorial for Beginners 2026 — From First Quote to Database Dump (Hands-On with DVWA + SQLmap)
SQL injection Tutorial from scratch in 2026 — what it is, why it works, manual exploitation step-by-step, DVWA lab setup,…
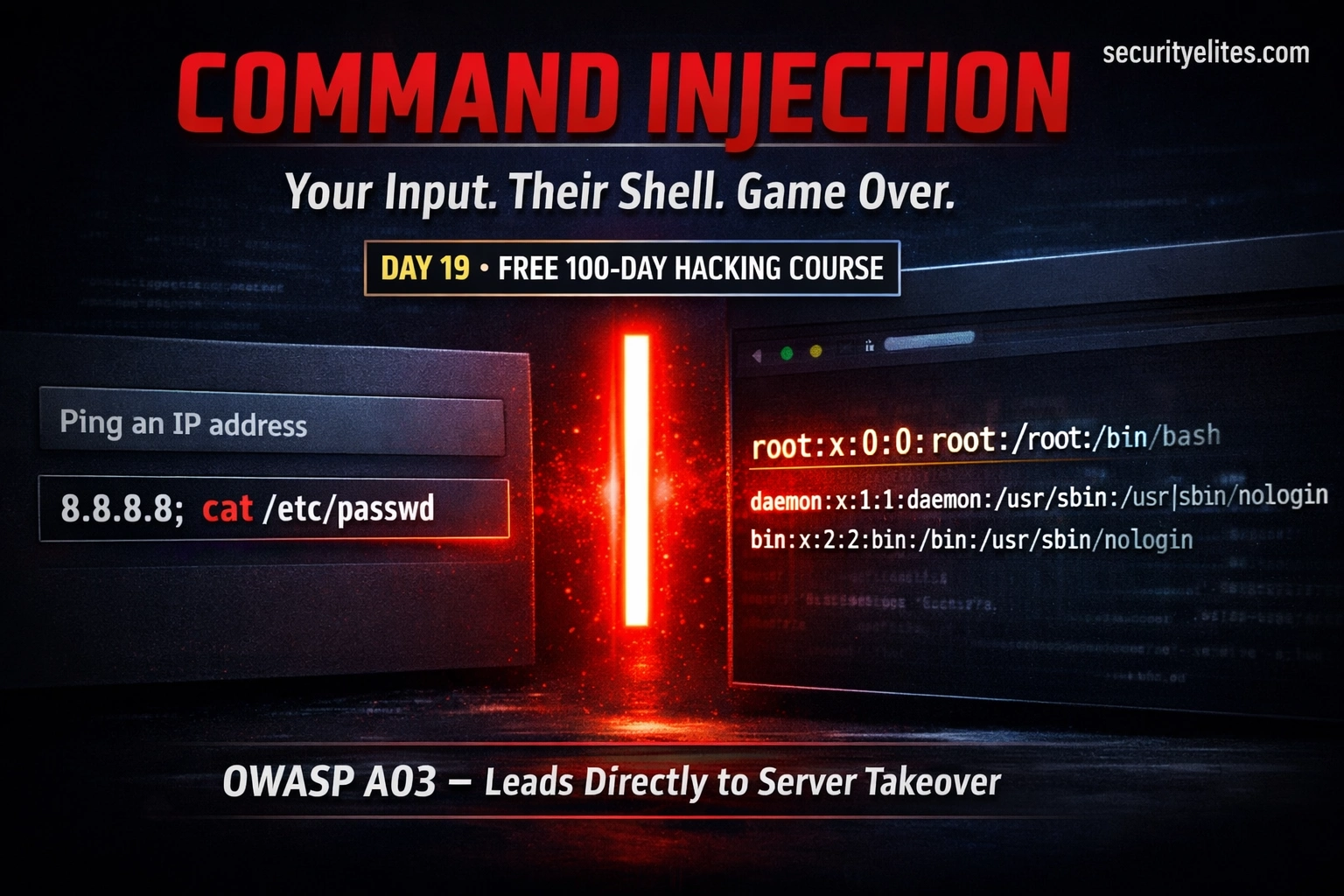
Day 19: Command Injection — When User Input Reaches the OS Shell (2026)
Day 19 of 100. Learn OS command injection, shell metacharacters, blind injection, DVWA lab walkthrough, and secure coding practices. One…
How to Become a Cybersecurity Analyst in 2026 — Complete Step-by-Step Career Guide (No Degree Required)
The complete guide on how to become a cybersecurity analyst in 2026 — SOC analyst roles explained, required skills, the…
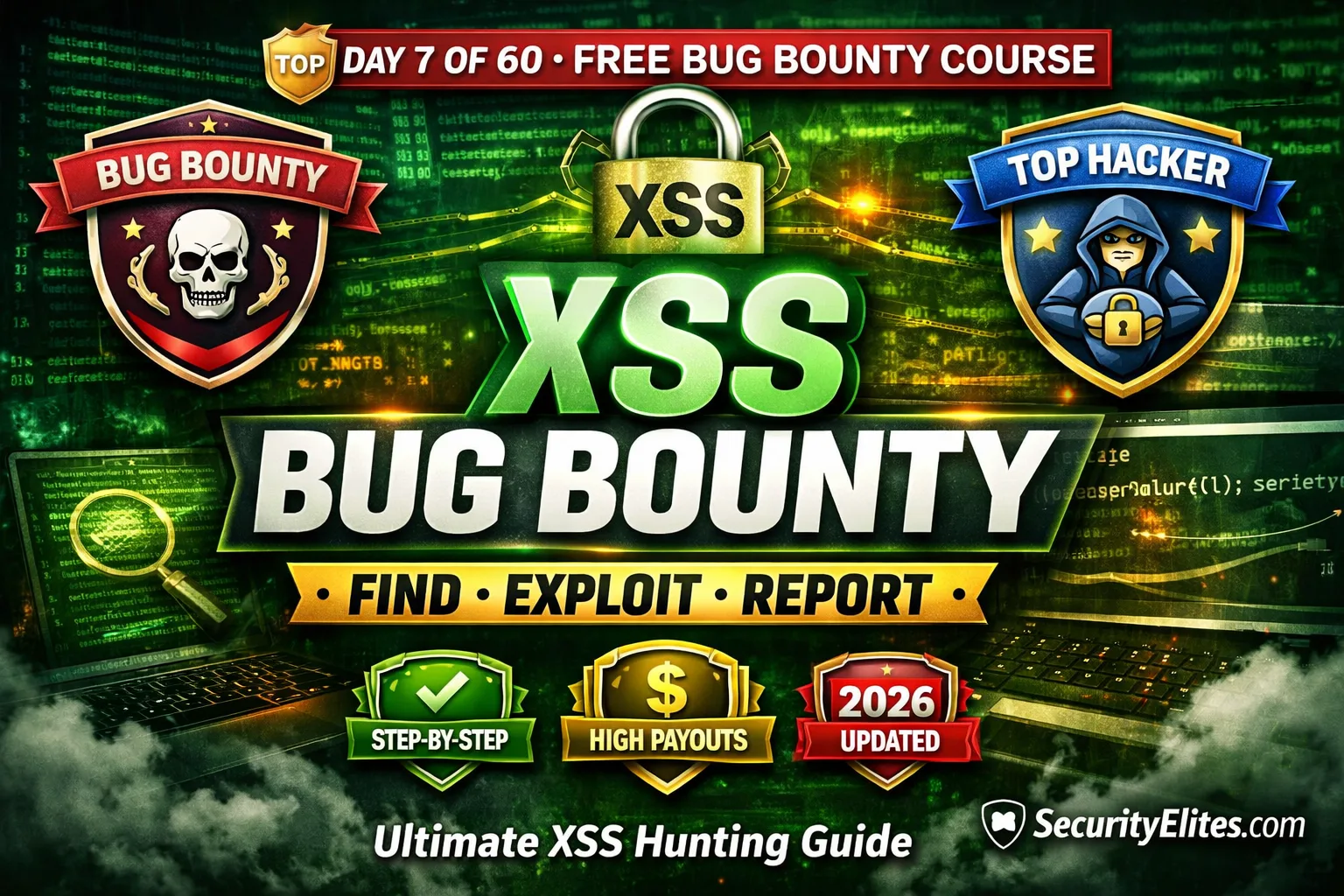
Day 7: XSS Bug Bounty Hunting — Find, Exploit & Report Cross-Site Scripting Bugs That Pay (2026)
Complete XSS bug bounty hunting guide — where to find reflected, stored, and DOM XSS, Burp Suite Repeater workflow, filter…
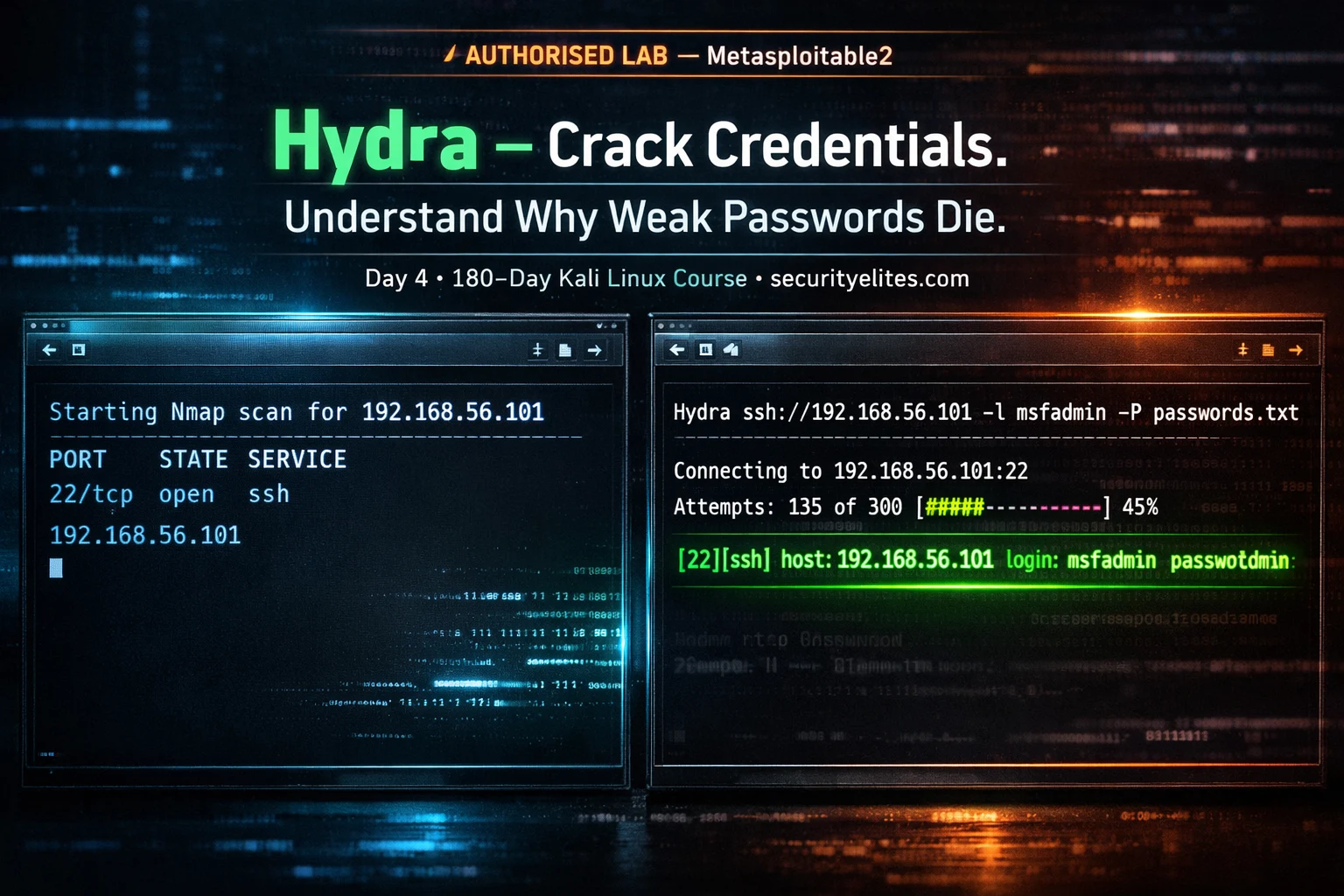
Kali Linux Day 4: Hydra Tutorial — Brute Force SSH, FTP, HTTP & 50+ Protocols (Complete Beginner Guide 2026)
Complete Hydra tutorial for Kali Linux — brute force SSH, FTP, HTTP login forms, RDP, MySQL, and 50+ protocols. Every…
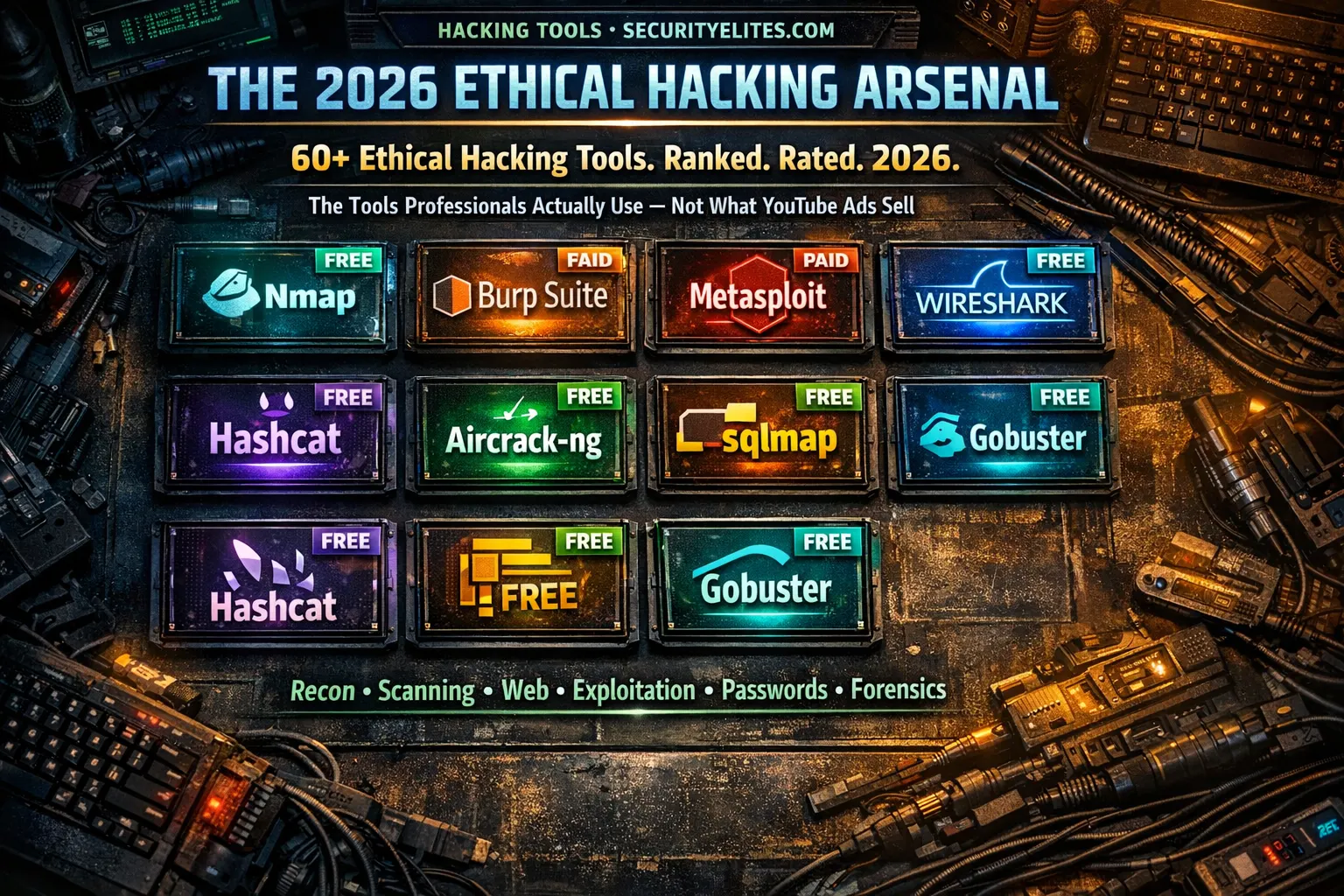
Ethical Hacking Tools List 2026 — Every Tool Professionals Actually Use (Free + Paid, Ranked by Category)
The most complete ethical hacking tools list for 2026 — 60+ tools across 10 categories with honest tier ratings, free…