All Articles
Cybersecurity tutorials, hacking guides, and security research.
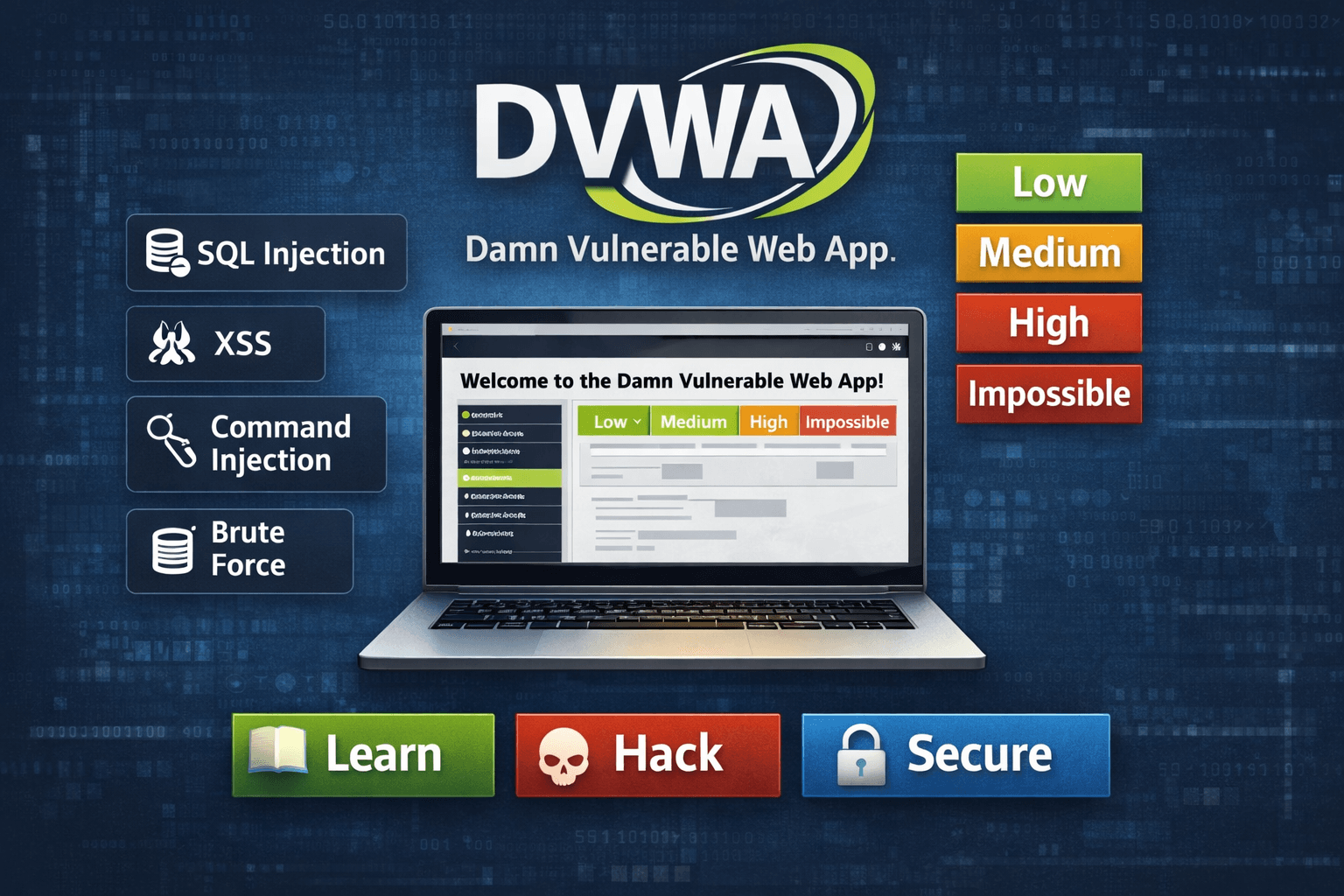
DVWA Web Hacking Tutorial Day 3: Brute Force & Authentication Exploitation
DVWA Web Hacking Tutorial DAY 3, Learn authentication hacking using DVWA. Perform brute force attacks with Burp Suite and understand…
DVWA Web Hacking Tutorial Day 2: Reconnaissance & Attack Surface Mapping
DVWA Web Hacking Tutorial Day 2, Learn real reconnaissance techniques in DVWA. Discover attack surface mapping, Burp Suite interception, and…
AI vs Hackers: Future of Cyber Warfare Explained (2026 Cybersecurity Guide)
AI vs Hackers Future of Cyber Warfare - Learn how AI is transforming cyber warfare with practical ethical hacking labs,…
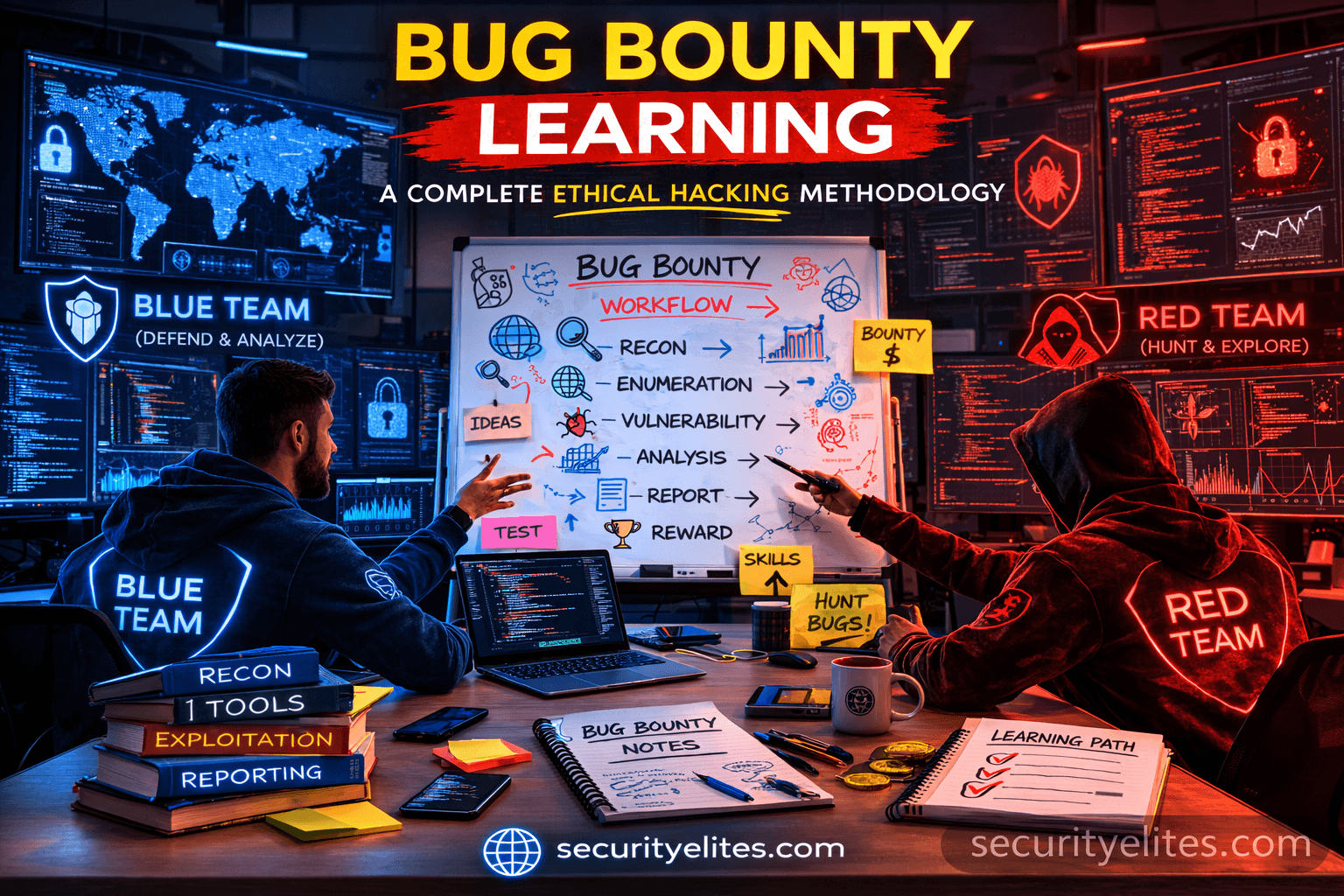
Bug Bounty Hunting Methodology: Complete Ethical Hacker Workflow Guide
Master Bug Bounty Hunting Methodology with practical recon workflow, tools, attacker mindset, and step-by-step ethical hacking tutorial.
Information Gathering Using Kali Linux Day 1: WHOIS Tutorial for Beginners
Information Gathering Using Kali Linux Day 1 - Learn Information Gathering using Kali Linux with WHOIS step-by-step. Beginner-friendly ethical hacking…
Learn IP Addressing Basics for Cybersecurity Beginners (Complete Guide)
Learn IP addressing basics for ethical hacking and cybersecurity. Beginner-friendly explanation with real-world professional insights and practical workflows.