All Articles
Cybersecurity tutorials, hacking guides, and security research.
6 Powerful Stages of the Pentesting Lifecycle: Complete Penetration Testing Guide
Learn the 6 powerful stages of the Pentesting Lifecycle used by ethical hackers. Step-by-step penetration testing process, tools, labs, and…
First Pentest Walkthrough – Step-by-Step Ethical Hacking Guide
Before we start our first Pentest Walkthrough we should first understand What is Pentest or Penetration testing. Later in tutorial…
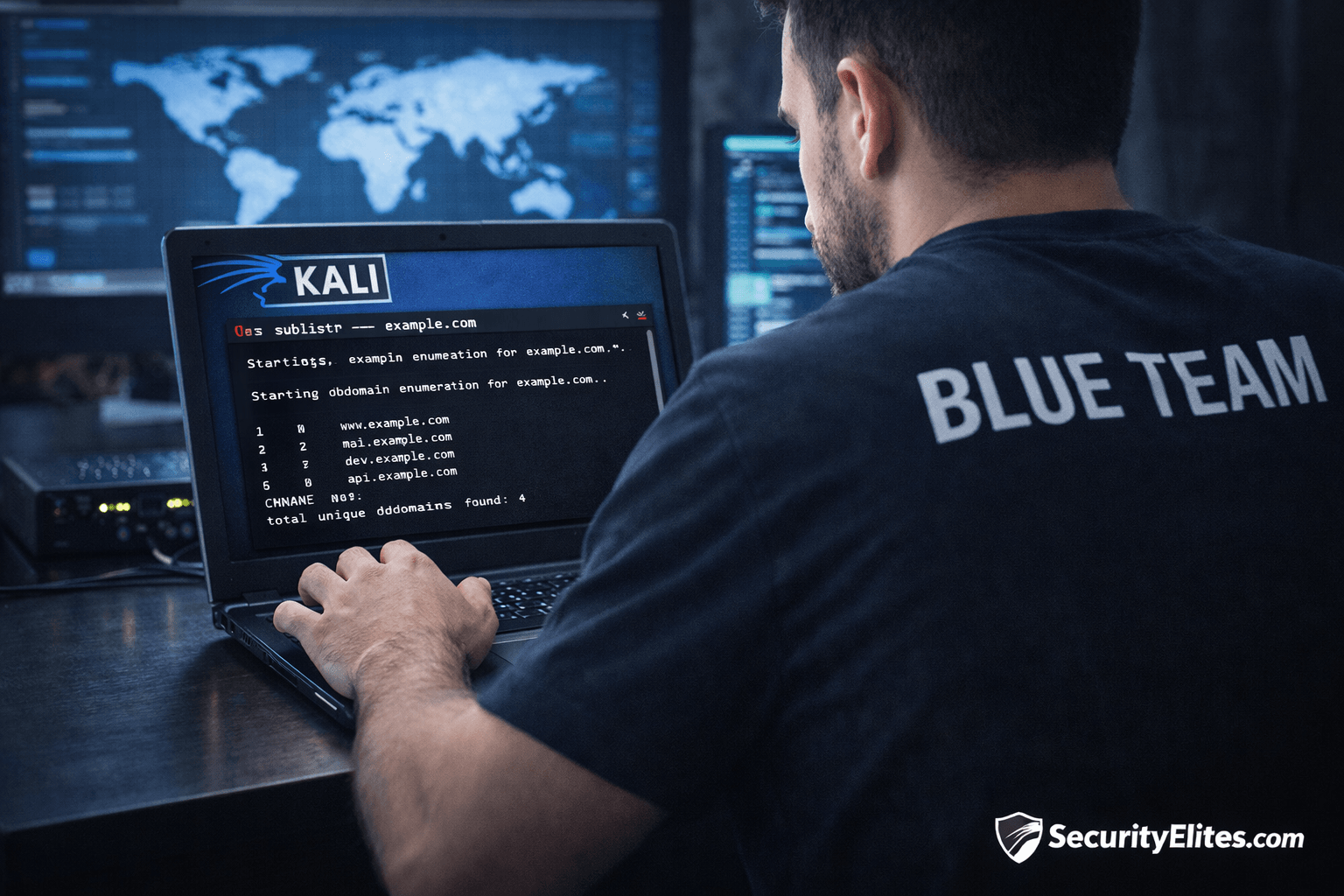
Information Gathering Using Kali Linux Day 3: Subdomain Enumeration with Sublist3r
Information Gathering Using Kali Linux Day 3 - Learn Information Gathering using Kali Linux with Sublist3r step-by-step. Discover hidden subdomains…
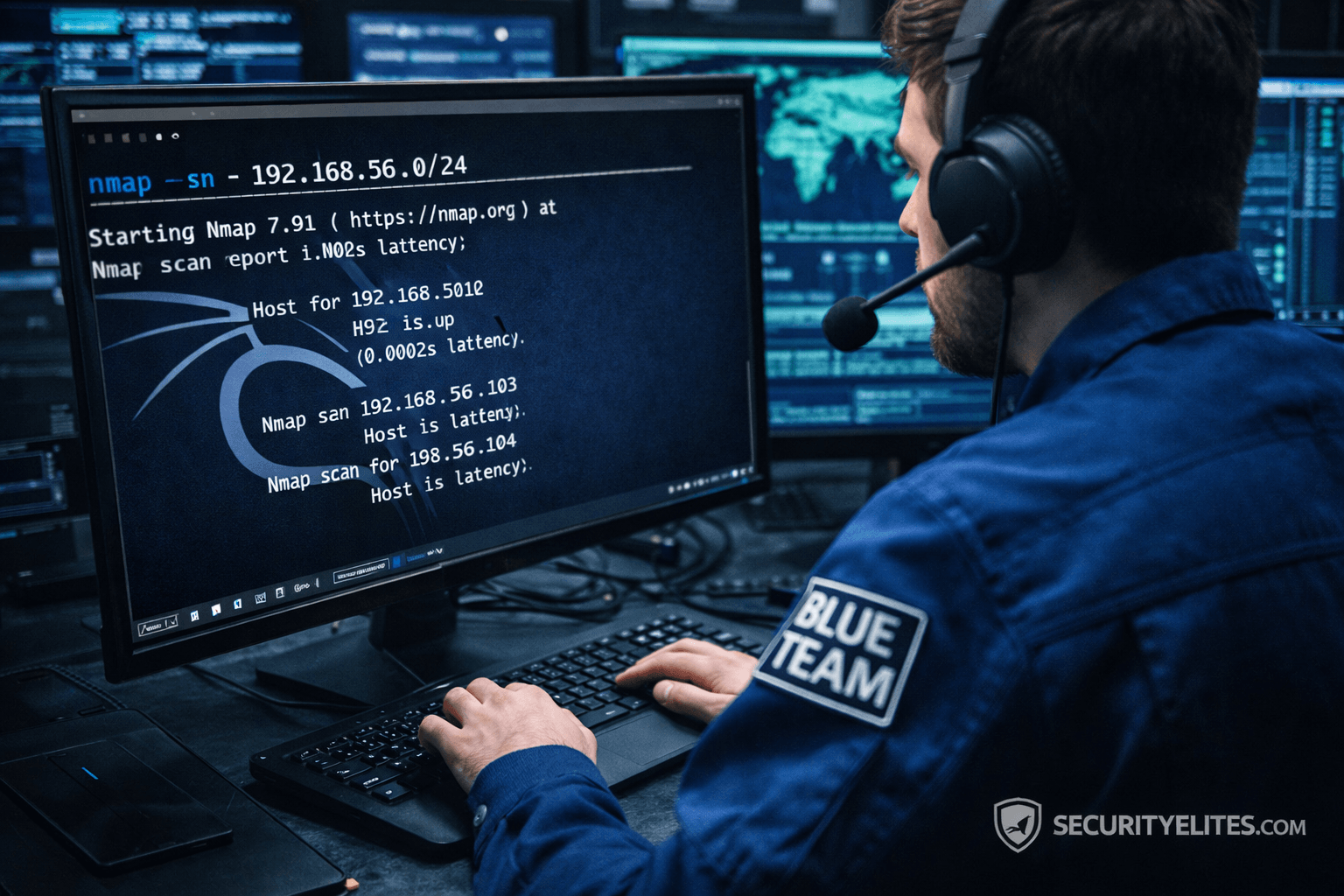
Network Scanning Tutorial Using Nmap Day 2— Host Discovery & Network Mapping
Network Scanning Tutorial Using Nmap Day 2 - Learn host discovery and network mapping using Nmap like professional ethical hackers.…
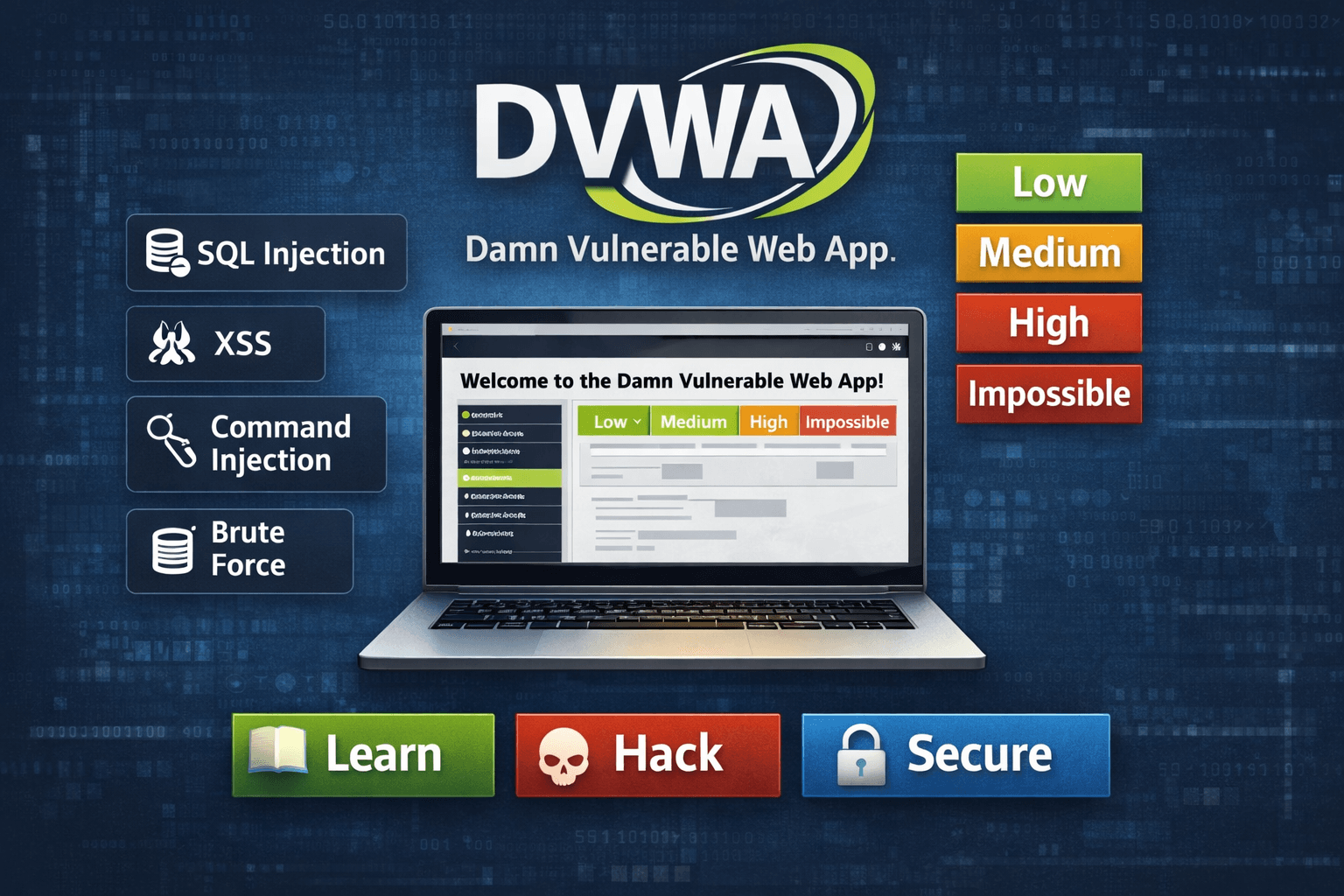
DVWA to Bug Bounty Day 1: Real Hacker Mindset & Scope Understanding
DVWA to Bug Bounty Day 1 - Transition from DVWA labs to real bug bounty hunting. Learn scope analysis, reconnaissance…
DVWA Web Hacking Tutorial Day 7: Full Penetration Testing Simulation Guide
DVWA Web Hacking Tutorial Day 7 - Complete DVWA web hacking course with full penetration testing workflow, exploitation chaining, and…