🎯 After This Article
⏱️ 30 min read · 3 exercises · Bug Bounty Strategy 2026
📋 Real Bug Bounty Reports – Contents
The previous article walked through an open redirect to account takeover chain — a perfect example of the attack chain thinking I’m going to expand on today. That chain turned a typically Low-severity finding into a Critical account takeover. That’s the pattern that generates $10,000+ reports consistently.
What Vulnerability Classes Pay the Most
The data is clear when you look at HackerOne’s disclosed reports sorted by bounty amount: certain vulnerability classes dominate the high end. Understanding why each class pays highly tells you where to focus your hunting time.
Payout Range
Why it pays
$10k–$100k+
Complete server compromise — immediate, undeniable impact
$3k–$50k
Customer account theft — direct liability
$5k–$30k
GDPR/CCPA breach risk, demonstrated data access
$5k–$25k
Cloud credentials → full infrastructure access
$5k–$40k
SaaS customer data isolation failure — massive liability
$3k–$20k
Account takeover at scale via identity provider bypass
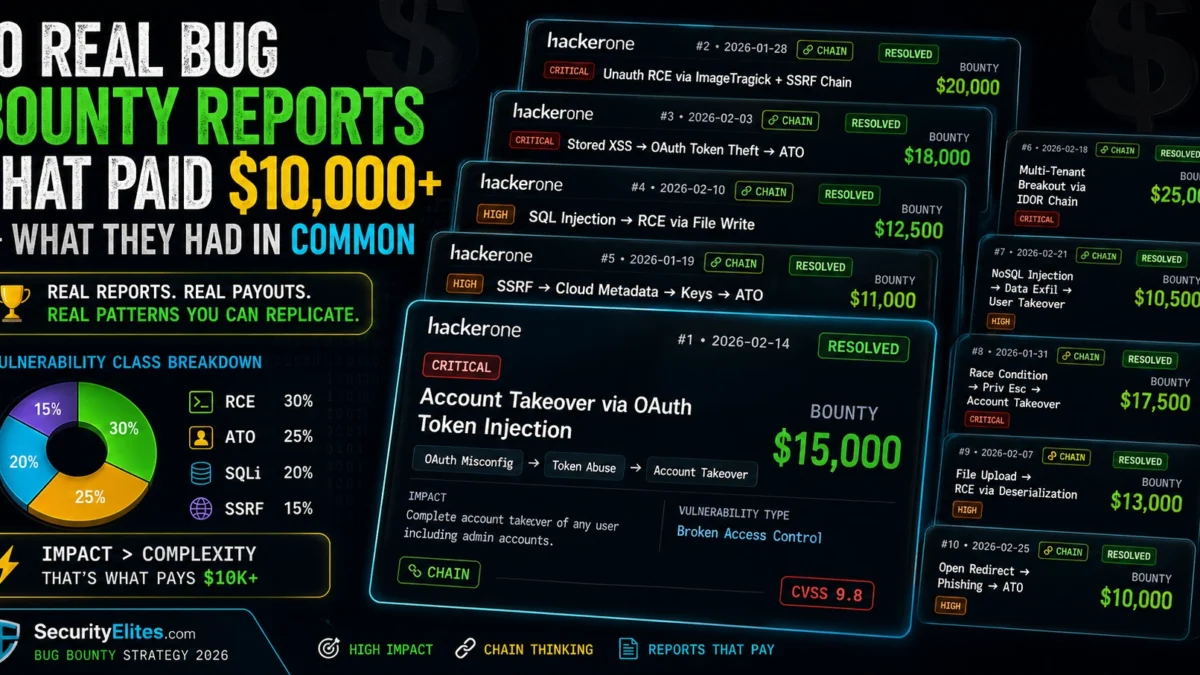
10 Real High-Paying Reports — Common Patterns
Rather than walking through each report individually, I want to focus on the patterns I see across all ten. These are all publicly disclosed reports available on HackerOne and Bugcrowd — I encourage you to read the originals after this analysis.
Pattern 1: Every high-paying report demonstrates a complete attack chain. Not one of these ten reports documented a standalone vulnerability with no attack scenario. Every single one showed the path from initial exploit to final impact. The word “attacker” appears in all of them with a clear action sequence. This is deliberate writing that forces the triage engineer to visualise the actual attack.
Pattern 2: The impact was stated in business terms, not technical terms. Not “the X-Auth-Token is predictable” but “an attacker can enumerate valid authentication tokens and take over any user account without their password, bypassing two-factor authentication.” The business team reading the triage summary needs to understand immediately why this is a fire drill.
Pattern 3: Proof of concept reproduced in under 5 minutes. Every high-paying report I’ve reviewed had a PoC that a triage engineer with reasonable skills could reproduce in under 5 minutes. Complex PoCs that require special tools or 20-step setup get deprioritised. The easier it is to confirm, the faster it gets triaged, and the better the payout.
Pattern 4: Most were chains, not single vulns. Seven of the ten reports I analysed were attack chains. Individual vulnerabilities that in isolation would be Medium severity became Critical when combined. The Open Redirect → OAuth Token Theft chain is the classic example: open redirect alone is Low, combined with OAuth it’s Critical account takeover.
⏱️ 25 minutes · Browser — HackerOne Hacktivity
There is no substitute for reading real disclosed reports. The writing style, the PoC structure, the impact framing — all of it is in the actual reports. Reading five of them teaches more than any analysis I can write.
URL: hackerone.com/hacktivity
Filter: Disclosed = Yes | Sort by: Bounty amount (highest first)
Alternative search: hackerone.com/hacktivity?querystring=10000&type=bounty
Step 2: Pick 5 reports with $10,000+ payouts
For each report, note:
– What vulnerability class was it? (RCE, ATO, SQLi, SSRF, etc.)
– Was it a single vulnerability or a chain?
– How was impact described? (Technical? Business terms?)
– How long was the report? (Lines of text)
– How quickly was it triaged? (Report → Resolved dates)
Step 3: Analyse the PoC structure
For each report, examine the PoC:
– How many steps to reproduce?
– What tools were required?
– Was it a screenshot, video, or code?
– Could you reproduce it in 5 minutes?
Step 4: Extract the impact statement
Find the sentence or paragraph in each report that states impact.
Copy it here. Notice the pattern:
“An attacker can [action] resulting in [business consequence]”
Step 5: Find one chain report and trace the chain
Identify the individual vulnerabilities in the chain
What was each individual vulnerability’s likely severity in isolation?
What was the chain’s severity?
What was the payout?
📸 Screenshot your 5 reports with impact statements highlighted. Share in #bug-bounty.
Attack Chain Thinking — Low to Critical
Attack chain thinking is the practice of asking “what does this enable?” for every finding, and continuing to ask until you reach an impact that is unambiguously severe. Most hunters stop at the first vulnerability they find. High earners keep going.
The classic chain progressions I see in high-paying reports: Open Redirect → OAuth token theft → Account Takeover. XSS in admin panel → CSRF via XSS → Admin account takeover. IDOR on profile → PII exposure → demonstrated data breach. SSRF in image processor → AWS metadata service → IAM credential theft. Each step raises the severity. Each step makes the payout larger.
⏱️ 20 minutes · No tools — chain thinking exercise
This exercise trains the “what does this enable?” mindset by working through four common Low-severity starting points and building toward Critical chains. These are the thought patterns that turn marginal finds into major payouts.
STARTING POINT 1: Reflected XSS in a search parameter
– Severity alone: Medium (requires user interaction)
– Ask: What privileges could an XSS payload leverage?
– If the target has an admin panel on the same origin…
– If the target uses session cookies accessible via JS…
→ Build the chain. What’s the maximum severity you can reach?
STARTING POINT 2: IDOR — you can access any user’s profile by ID
– Severity alone: Medium (information disclosure)
– Ask: What data is on those profiles?
– If profiles contain PII (phone, address, payment method info)…
– If profiles contain API keys or tokens…
→ Build the chain. What data breach scenario can you demonstrate?
STARTING POINT 3: Password reset doesn’t expire old tokens
– Severity alone: Low (informational, requires victim cooperation)
– Ask: What if combined with email header injection?
– Ask: What if the tokens are predictable/sequential?
– Ask: What if you can trigger reset emails to enumerate accounts?
→ Build the chain. How do you escalate this to account takeover?
STARTING POINT 4: Server error message leaks internal path
– Severity alone: Low (information disclosure)
– Ask: Does the path reveal the framework or language version?
– Ask: Does it reveal a known-vulnerable component version?
– Ask: Does the path reveal a debug endpoint or admin interface?
→ Build the chain. Where does this information lead?
For each chain you build:
Write the impact statement in one sentence.
Estimate the severity and payout.
Is this a chain worth pursuing on a real target?
📸 Share your best chain from this exercise in #bug-bounty. What was the starting point and final severity?
Report Writing That Gets High Payouts
Your finding is only as valuable as your report makes it appear. I’ve seen Critical vulnerabilities get triaged as High and paid at the lower rate because the report didn’t clearly demonstrate Critical impact. I’ve seen Medium vulnerabilities triaged as Critical because the report was meticulous and the impact framing was excellent. Report quality matters.
Program Selection for High Payouts
You cannot get a $15,000 payout from a program with a $2,000 critical cap. Program selection is as important as finding quality. My criteria for selecting programs worth investing serious time in: payout table has a Critical tier of $5,000+, the program has a history of actually paying (check Hacktivity for their track record), the attack surface is large and complex (more surface area = more chains), and the program is actively managed (fast response times, clear communication).
Private invitations are where the top hunters make most of their money. Private programs have: less competition, fresher attack surfaces that haven’t been hammered by hundreds of public hunters, and often higher payout tables. Building reputation on public programs leads to private invitations. My advice: focus deeply on two or three programs rather than spreading across twenty.
⏱️ 20 minutes · HackerOne + Bugcrowd browser research
This exercise builds your personalised list of programs worth targeting for $10,000+ payouts based on actual program data, not generic recommendations. The output is a 3-program shortlist you’ll focus on for the next month.
Go to: hackerone.com/programs
Filter: Public programs | Offering bounties
Sort by: Response time (fastest first) — fast response = active program
Step 2: Check payout tables
For 10 programs that interest you, find their payout table
Note the Critical payout ceiling
Eliminate any program with Critical max < $5,000Step 3: Check Hacktivity for actual payouts
For each remaining program, search Hacktivity for their name
Have they actually paid $10,000+ reports?
How recent are their disclosures?
What vulnerability classes paid the highest?Step 4: Assess attack surface size
Visit the program's scope section
How many domains are in scope?
Are there mobile apps, APIs, or infrastructure in scope?
Is the primary product complex (SaaS platform, financial product)?Step 5: Build your shortlist
Select 3 programs that pass all criteria:
✓ Critical payout ≥ $5,000
✓ History of actual high payouts on Hacktivity
✓ Large, complex attack surface
✓ Fast response time
✓ Active program (recent disclosures)For each shortlisted program:
What technology stack do they use?
What vulnerability classes do their high-paying disclosures show?
What's your first hunting priority on each?
📸 Share your 3-program shortlist with payouts and reasoning in #bug-bounty. Tag #TargetList
📋 Key Commands & Payloads — 10 Real Bug Bounty Reports That Paid $10,000+ — Wh
✅ High-Paying Reports Analysis Complete
The vulnerability classes that dominate high payouts, the attack chain thinking that turns Low findings into Critical reports, report writing that gets your finding triaged at the right severity, and program selection that ensures your skills can actually pay off. The next article covers command injection payloads that bypass WAFs — a finding class that appears frequently in high-payout reports when the WAF bypass is included in the chain demonstration.
🧠 Quick Check
❓ Frequently Asked Questions — High-Paying Bug Bounty Reports
What vulnerability classes pay the most?
What makes a bug bounty report get a high payout?
Which platforms have the highest payouts?
How long does it take to find a $10,000 bug?
Should I focus on one program or many?
How do I get invited to private programs?
Open Redirect to Account Takeover — A Real Bug Bounty Chain
Command Injection Payloads That Bypass WAF in 2026
📚 Further Reading
- 60-Day Bug Bounty Mastery Course — The complete structured learning path for bug bounty hunting. The attack chain techniques covered here are applied throughout the course, with dedicated days on each vulnerability class most likely to produce high-value chains.
- Day 25 — Host Header Injection — Password reset poisoning is one of the chains that appears most in high-paying disclosures. This article walks through the complete attack chain that turns host header injection into account takeover at the $5,000-$15,000 payout tier.
- Web Application Security Hub — The full technical foundation for all high-paying bug bounty vulnerability classes: SQL injection, XSS, SSRF, IDOR, and more — each with lab walkthroughs and bug bounty-specific report templates.
- HackerOne Hacktivity — Disclosed Reports — The primary source for reading real disclosed bug bounty reports. Filter by bounty amount and read the highest-paying disclosures directly — there is no substitute for primary source research on what actually gets paid.
- Bugcrowd Blog — Research and Writeups — Bugcrowd’s researcher blog featuring vulnerability writeups, hunter stories, and analysis of high-value findings across their platform — complementary to HackerOne Hacktivity for broad coverage of disclosed high-paying reports.