Part of the 60-Day Bug Bounty Mastery Course
Host header injection sits at the intersection of authentication, infrastructure, and caching vulnerabilities. The core issue is straightforward — the application trusts the Host header to construct URLs without validating it — but the attack surface is broader than most testers initially realise. Password reset poisoning is the headline variant, but the same root cause enables web cache poisoning, SSRF, and virtual host routing attacks. Day 25 covers all of them.
🎯 What You’ll Master in Day 25
⏱️ 20 min read · Burp Suite for Exercises 2 & 3
📋 Host Header Injection Attacks – Contents
How Host Header Injection Works
The HTTP Host header tells the server which virtual host is being addressed — in a shared hosting environment, dozens of domains may point to the same IP, and the Host header determines which application handles the request. In theory, the server knows its own domain and should validate the Host header against it. In practice, many applications use the Host header value directly in their business logic: constructing password reset URLs, building canonical links, routing to backend services, or setting cache keys.
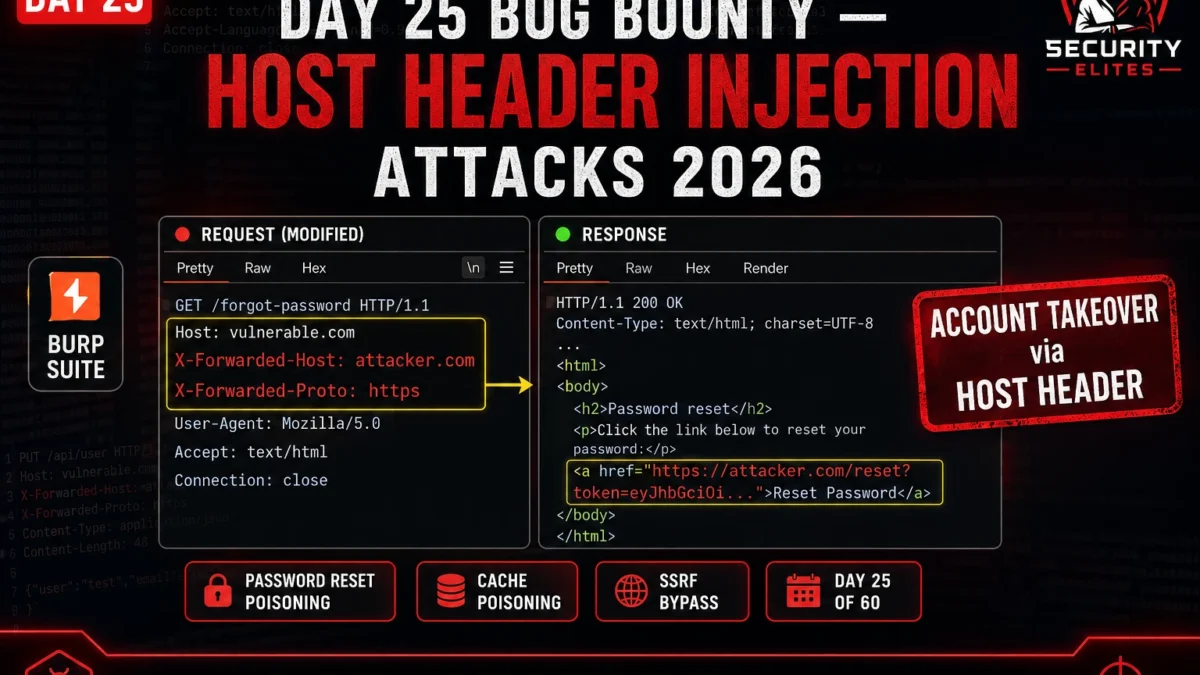
The attacker’s leverage is control over this header. In normal browser traffic, the browser sets the Host header to the domain in the URL and you can’t change it. In Burp Suite’s intercept proxy, you can modify any header before it reaches the server. An application that uses Host to construct a password reset link without validation will happily include your attacker-controlled domain in that link, send it to the victim’s email, and not know anything went wrong.
⏱️ 10 minutes · Browser only
Before touching the labs, I always read the PortSwigger research article on the vulnerability class. Their write-ups are the clearest, most technically precise explanations of web vulnerabilities available anywhere — and they’re free. Understanding the mechanism deeply makes the lab exercises click immediately rather than being trial-and-error.
Go to: portswigger.net/web-security/host-header
Read the full article.
Step 2: Answer these questions after reading:
a) What header besides Host can be used to inject a domain?
b) How does the “flawed validation” bypass work?
(What format makes the application think it’s the real domain?)
c) What is a “dangling markup” injection and how does Host enable it?
Step 3: Find the list of all Host injection variants
The PortSwigger article lists multiple techniques.
Write down every bypass variant they mention.
Which bypass works when the Host value is validated as an exact match?
Step 4: Understand the password reset attack flow
PortSwigger shows the exact HTTP request modification.
What specific line changes between the legitimate and malicious request?
What happens next when the victim clicks the poisoned reset link?
📸 Write down every bypass variant and share in #bug-bounty.
Password Reset Poisoning — Full Attack Chain
Password reset poisoning is the cleanest, most directly reportable variant of Host header injection. The attack chain is: attacker initiates password reset for victim account → modifies Host header to attacker-controlled domain → application generates reset token and sends reset email to victim with attacker’s domain in the link → victim clicks what appears to be a legitimate reset email → attacker’s server receives the reset token → attacker uses token to set new password and owns the account.
The beauty of this attack from a bug bounty perspective is the clear, demonstrable impact. You don’t need to guess whether it’s exploitable — you can demonstrate the full chain using test accounts and Burp Collaborator without touching any real user. The severity is unambiguously Critical when the chain results in complete account takeover.
Bypass Headers — When Direct Injection Fails
Many applications validate the Host header — checking that it contains their domain or matches a whitelist. When direct Host modification fails, I move to bypass headers. The most effective is X-Forwarded-Host — a proxy header that many applications accept as an override for the actual Host value, often without the same validation applied to the Host header itself. Some applications strip X-Forwarded-Host but accept X-Host, Forwarded, or X-Original-Host.
The validation bypass techniques are equally important. Applications that check whether the Host header contains their domain can be bypassed with Host: target.com@attacker.com or Host: attacker.com#target.com. The application’s string matching finds “target.com” in the header, but the URL construction uses the full value — routing the generated link to the attacker’s domain.
⏱️ 20 minutes · PortSwigger Web Security Academy (free account)
PortSwigger’s Host header labs are the best structured practice for this vulnerability class. The password reset poisoning lab walks you through the complete attack chain with the exact Burp modifications needed — this is the closest to a real-world exploitation you’ll get in a legal environment.
Create a free account if you don’t have one.
Launch the lab: “Basic password reset poisoning”
Step 2: Find the password reset functionality
Navigate to /forgot-password
Capture the request in Burp Suite
Step 3: Modify the Host header
In Burp Repeater:
Change: Host: vulnerable-website.com
To: Host: [your exploit server URL from lab]
Step 4: Trigger the reset for the victim account
Submit with email=carlos@carlos-montoya.net
(Carlos is the target user in this lab)
Step 5: Check the exploit server access log
The reset email will contain your exploit server URL
Get the token from the server log
Step 6: Use the token to log in as Carlos
Navigate to: /forgot-password?temp-forgot-password-token=[stolen_token]
Reset Carlos’s password to anything
Log in as Carlos to solve the lab
Note the exact request modification that made it work.
What would happen if the Host header was validated?
Try X-Forwarded-Host if the basic lab succeeds quickly.
📸 Screenshot the stolen token in your exploit server log and share in #bug-bounty.
Web Cache Poisoning via Host Header
Web cache poisoning via Host header is the variant with the highest potential scale. Instead of affecting one user’s password reset, a successful cache poisoning attack delivers a poisoned response to every user who requests the cached endpoint. If the Host header is included in the response (as an absolute URL, a script source, or a canonical tag) but not in the cache key, an attacker can send a poisoned request that gets cached and served to all subsequent visitors.
Testing cache poisoning safely requires cache busters — unique parameter values appended to the URL that prevent your poisoned response from being served to real users during testing. Always test cache poisoning with a cache buster parameter first to confirm the vulnerability without polluting real cached responses.
Writing the Bug Bounty Report
Host header injection reports follow a clear structure: the specific vulnerable endpoint, the exact header modification, the impact chain demonstrated, and the suggested remediation. For password reset poisoning, the impact chain is explicit — demonstrate that a victim’s reset token can be captured and used for account takeover, using your own test accounts only. Never attempt to capture another user’s real reset token.
⏱️ 20 minutes · PortSwigger Web Security Academy
The advanced variant is where real-world skill pays off. When the direct Host header modification fails (which it will on hardened applications), the X-Forwarded-Host bypass is your next move. This lab forces you to think beyond the obvious test and use the bypass technique.
portswigger.net/web-security/host-header/exploiting/password-reset-poisoning
Select the X-Forwarded-Host / middleware variant lab
Step 2: Attempt direct Host modification first
Modify Host header to your exploit server
Confirm it fails (host is validated)
Step 3: Add X-Forwarded-Host header
Keep original Host: vulnerable-website.com
Add: X-Forwarded-Host: [your exploit server URL]
Note: application is running behind a proxy that trusts this header
Step 4: Follow the same token capture → account takeover chain
Same target email, same exploit server log check
Same token → password reset → login as victim
Step 5: Test additional bypass headers
After solving: try adding each of these (one at a time):
X-Host: [your server]
Forwarded: host=[your server]
X-Original-Host: [your server]
Which ones does this app also accept?
Step 6: Write a three-paragraph report section
Section 1: Vulnerability description
Section 2: Steps to reproduce (exact request)
Section 3: Impact + remediation recommendation
📸 Share your three-paragraph report section in #bug-bounty. Real skill at writing reports.
✅ Day 25 Complete — Host Header Injection
Password reset poisoning, X-Forwarded-Host bypass, web cache poisoning, and report writing. Day 26 moves to SSTI — Server-Side Template Injection to Remote Code Execution across five template engines.
🧠 Quick Check
❓ Frequently Asked Questions
What is Host Header Injection?
What is password reset poisoning?
What headers should I test for Host header injection?
What is the severity of Host Header Injection?
How does web cache poisoning via Host header work?
What is the best lab for practicing Host Header Injection?
CRLF Injection — Header Injection & Response Splitting
SSTI Bug Bounty — Template Injection to RCE
📚 Further Reading
- Bug Bounty Mastery Course — Full Programme — Complete bug bounty hunting course covering recon through advanced exploitation, with real labs and report templates.
- Day 19 — CSRF Bug Bounty — CSRF is in the same vulnerability neighbourhood as Host injection — both exploit trust assumptions in request handling. Understanding CSRF deepens your Host injection analysis.
- Day 10 — SSRF Bug Bounty — Server-side request forgery is the SSRF variant that Host header injection can enable. SSRF methodology that applies directly when Host injection triggers server-side requests.
- PortSwigger — Host Header Attacks — The authoritative technical reference for Host header attacks — complete technique taxonomy, bypass methods, and free interactive labs.
- PortSwigger — Web Cache Poisoning Research — James Kettle’s original web cache poisoning research — the foundational paper covering Host-header-based cache poisoning in depth.