Bug Bounty Hunting
Start your bug bounty hunting journey with complete beginner-to-advanced tutorials on finding and reporting vulnerabilities. Learn reconnaissance techniques, subdomain enumeration, Google dorking, automation tools, and vulnerability validation methods used by top bug bounty hunters. This section also includes real bug bounty case studies, report writing tips, and platform guides like HackerOne and Bugcrowd to help you earn rewards by ethically reporting security flaws.
89 articles
DVWA to Bug Bounty Day 3: Hidden Endpoints & Parameter Discovery Guide
DVWA to Bug Bounty Day 3 - Learn how bug bounty hunters discover hidden endpoints, APIs, and parameters to find…
Hacker Recon Checklist: 10-Step Ethical Hacking Recon Guide
Learn the hacker recon checklist used in penetration testing and bug bounty hunting. Step-by-step reconnaissance guide with tools and practical…
DVWA to Bug Bounty Day 2: Subdomain Enumeration & Attack Surface Discovery
DVWA to Bug Bounty Day 2 - Learn professional subdomain enumeration techniques used in real bug bounty hunting. Discover hidden…
Information Gathering Using Kali Linux Day 3: Subdomain Enumeration with Sublist3r
Information Gathering Using Kali Linux Day 3 - Learn Information Gathering using Kali Linux with Sublist3r step-by-step. Discover hidden subdomains…
DVWA to Bug Bounty Day 1: Real Hacker Mindset & Scope Understanding
DVWA to Bug Bounty Day 1 - Transition from DVWA labs to real bug bounty hunting. Learn scope analysis, reconnaissance…
Google Dorks for Bug Bounty Hunters (Beginner Guide 2026)
Learn Google Dorks for bug bounty hunters with beginner-friendly red team methodology, real recon workflows, and ethical hacking fundamentals.
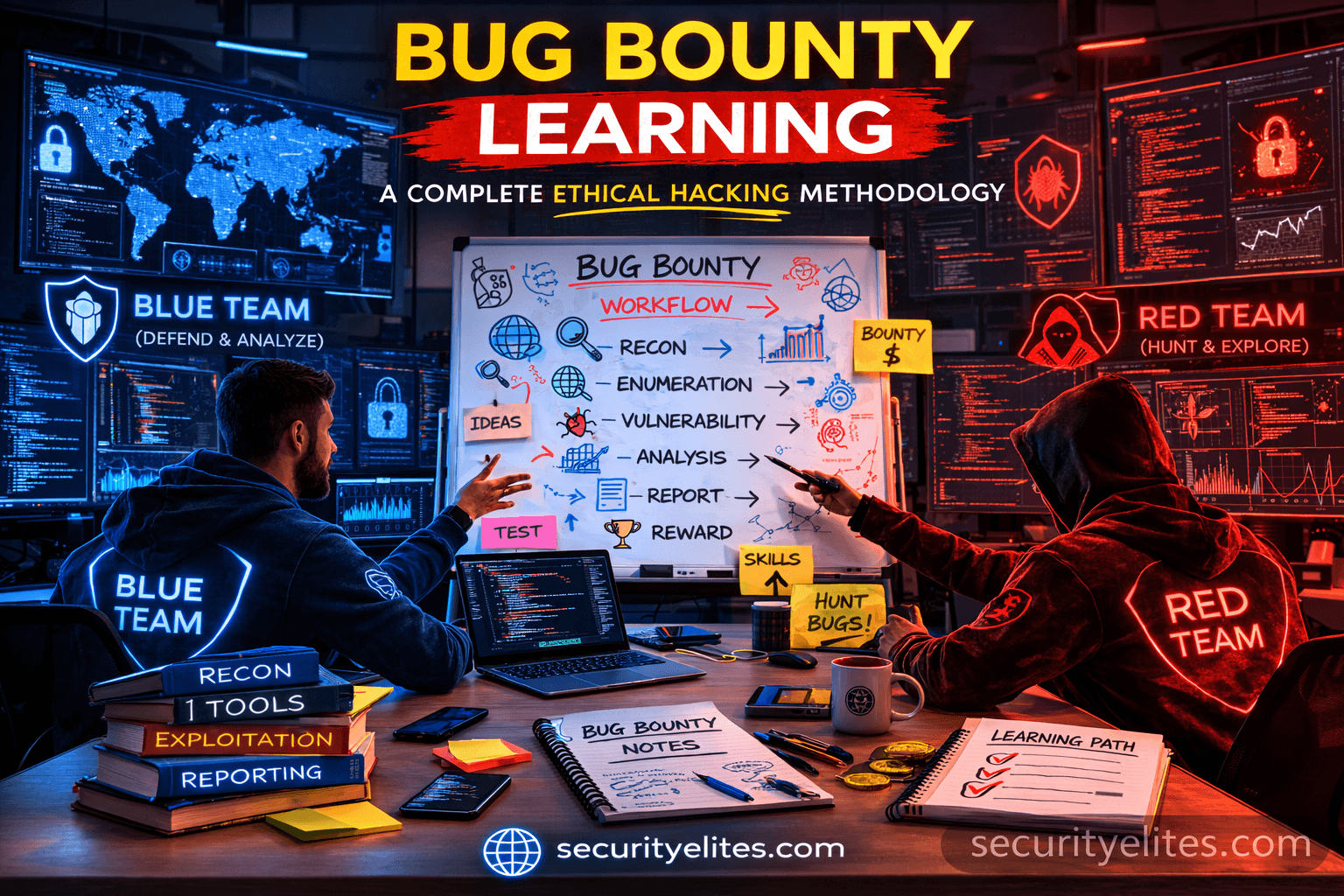
Bug Bounty Hunting Methodology: Complete Ethical Hacker Workflow Guide
Master Bug Bounty Hunting Methodology with practical recon workflow, tools, attacker mindset, and step-by-step ethical hacking tutorial.
How to Start Bug Bounty With Zero Experience – Beginner to Pro Guide
Learn how to start bug bounty with zero experience using this practical, mentor-style guide. Step-by-step process, tools, mistakes, and pro…