Bug Bounty Hunting
Start your bug bounty hunting journey with complete beginner-to-advanced tutorials on finding and reporting vulnerabilities. Learn reconnaissance techniques, subdomain enumeration, Google dorking, automation tools, and vulnerability validation methods used by top bug bounty hunters. This section also includes real bug bounty case studies, report writing tips, and platform guides like HackerOne and Bugcrowd to help you earn rewards by ethically reporting security flaws.
89 articles
DVWA to Bug Bounty Day 7: Professional Reporting & Earning Strategy
DVWA to Bug Bounty Day 7 - Learn professional bug bounty workflow, vulnerability reporting techniques, and strategies to earn rewards…
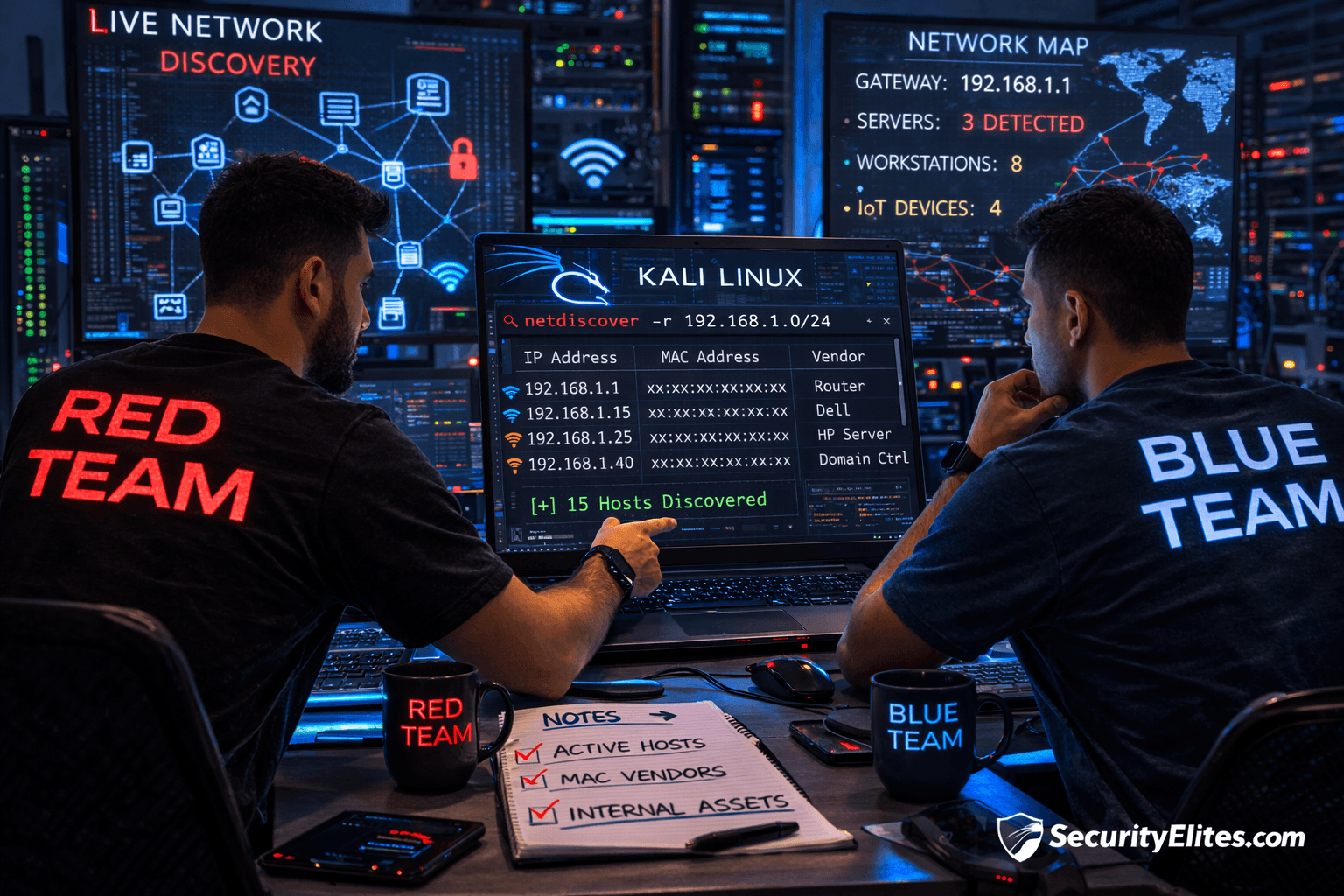
Information Gathering Using Kali Linux Day 9: Internal Network Discovery with Netdiscover
Information Gathering Using Kali Linux Day 9 - Learn Information Gathering using Kali Linux with Netdiscover step-by-step. Discover live internal…
DVWA to Bug Bounty Day 6: API Hacking & Business Logic Vulnerabilities
DVWA to Bug Bounty Day 6 - Learn API hacking techniques and business logic vulnerability hunting used by elite bug…
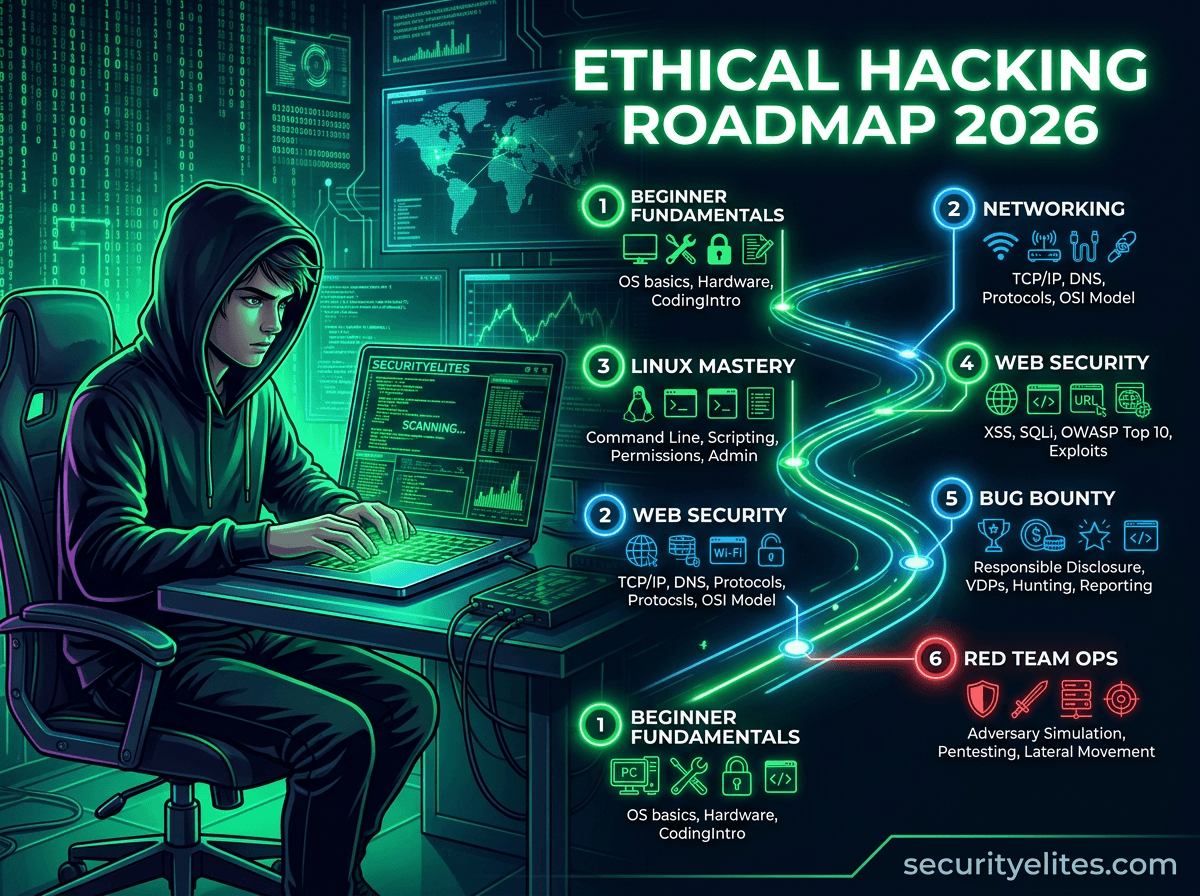
Ethical Hacking Roadmap 2026: How to Become Ethical Hacker (Beginner to Expert)
Learn the complete ethical hacking roadmap 2026 with step-by-step labs, tools, and cybersecurity skills required to become an ethical hacker…
DVWA to Bug Bounty Day 5: Advanced XSS Hunting & Filter Bypass Guide
DVWA to Bug Bounty Day 5 - Learn advanced Cross-Site Scripting hunting techniques, filter bypass methods, and real bug bounty…
Amass Tutorial (2026): Powerful Subdomain Enumeration Guide for Kali Linux
Learn Amass tutorial for subdomain enumeration and reconnaissance in Kali Linux. Step-by-step ethical hacking guide used by penetration testers and…
ChatGPT Bug Bounty Automation: How Hackers Find Vulnerabilities Faster (5 AI Techniques)
Learn ChatGPT bug bounty automation techniques ethical hackers use to discover vulnerabilities faster. Includes reconnaissance prompts, AI vulnerability analysis, and…
DVWA to Bug Bounty Day 4: Authentication & Authorization Logic Bugs
DVWA to Bug Bounty Day 4 - Learn how bug bounty hunters find IDOR and authorization vulnerabilities using real-world testing…
ChatGPT Penetration Testing Automation: 7 Powerful Techniques Ethical Hackers Use
Learn how ethical hackers use ChatGPT penetration testing automation with Kali Linux labs, vulnerability discovery, and AI-assisted exploitation workflows.