Cyber Security Courses & Training
This best cyber security courses online section helps learners choose the right training programs to build technical expertise. Tutorials include free and paid courses, certification training, lab platforms, and degree programs. You will find course comparisons, syllabus breakdowns, pricing insights, and career outcomes. Whether you prefer self-paced learning, bootcamps, or university programs, this category provides complete training guidance for cyber security learners.
51 articles
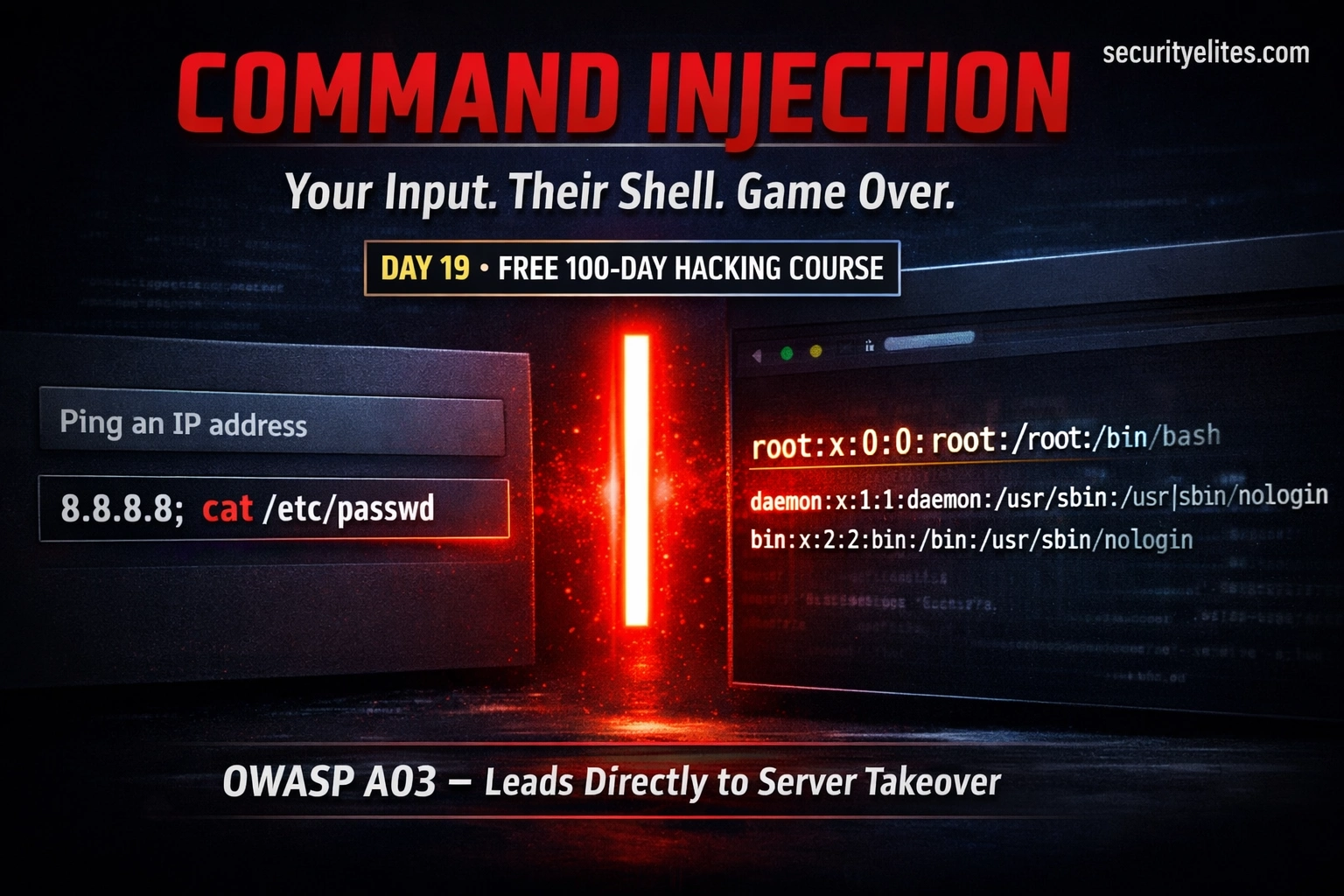
Day 19: Command Injection — When User Input Reaches the OS Shell (2026)
Day 19 of 100. Learn OS command injection, shell metacharacters, blind injection, DVWA lab walkthrough, and secure coding practices. One…
How to Become a Cybersecurity Analyst in 2026 — Complete Step-by-Step Career Guide (No Degree Required)
The complete guide on how to become a cybersecurity analyst in 2026 — SOC analyst roles explained, required skills, the…
Day 7: XSS Bug Bounty Hunting — Find, Exploit & Report Cross-Site Scripting Bugs That Pay (2026)
Complete XSS bug bounty hunting guide — where to find reflected, stored, and DOM XSS, Burp Suite Repeater workflow, filter…
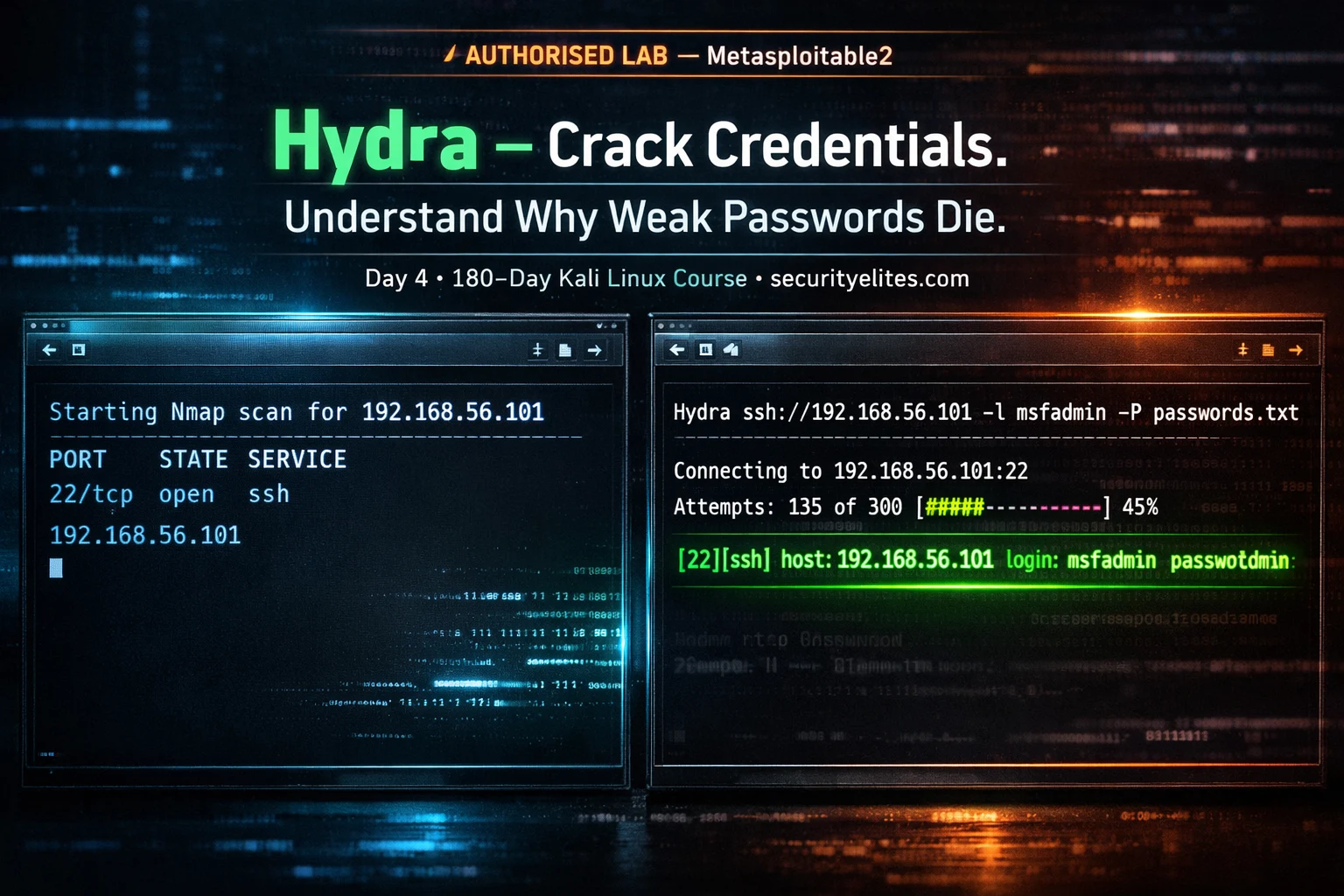
Kali Linux Day 4: Hydra Tutorial — Brute Force SSH, FTP, HTTP & 50+ Protocols (Complete Beginner Guide 2026)
Complete Hydra tutorial for Kali Linux — brute force SSH, FTP, HTTP login forms, RDP, MySQL, and 50+ protocols. Every…
Day 18: File Upload Vulnerabilities — From Image Upload to Web Shell (2026)
Understand file upload vulnerabilities from first principles — how validation is bypassed, how web shells work, full DVWA demos at…
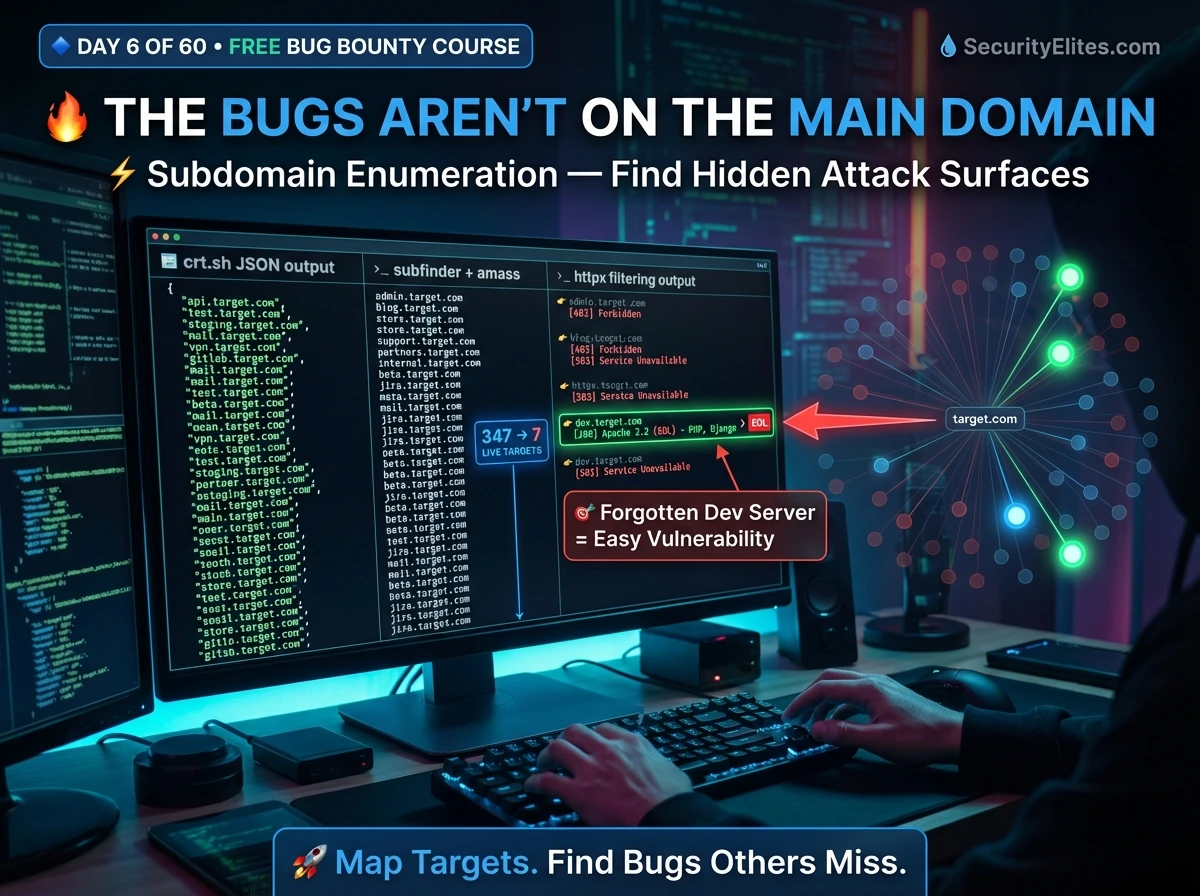
Bug Bounty Day 6: Subdomain Enumeration — Build Your Full Attack Surface Map (2026)
Master subdomain enumeration for bug bounty — Subfinder, Amass, crt.sh, httpx live filtering, ffuf directory fuzzing, and building a professional…
Day 17: Security Misconfiguration — The Easiest Vulnerabilities to Find (2026)
Day 17 of 100. Learn security misconfiguration — default credentials, verbose errors, exposed admin panels, open cloud buckets, directory listing,…
Kali Linux Day 3: Gobuster Tutorial — Find Hidden Directories, Files & Subdomains (Complete Beginner Guide 2026)
Complete Gobuster tutorial for Kali Linux — dir mode, dns mode, vhost mode, wordlists, status code filtering, file extension discovery,…
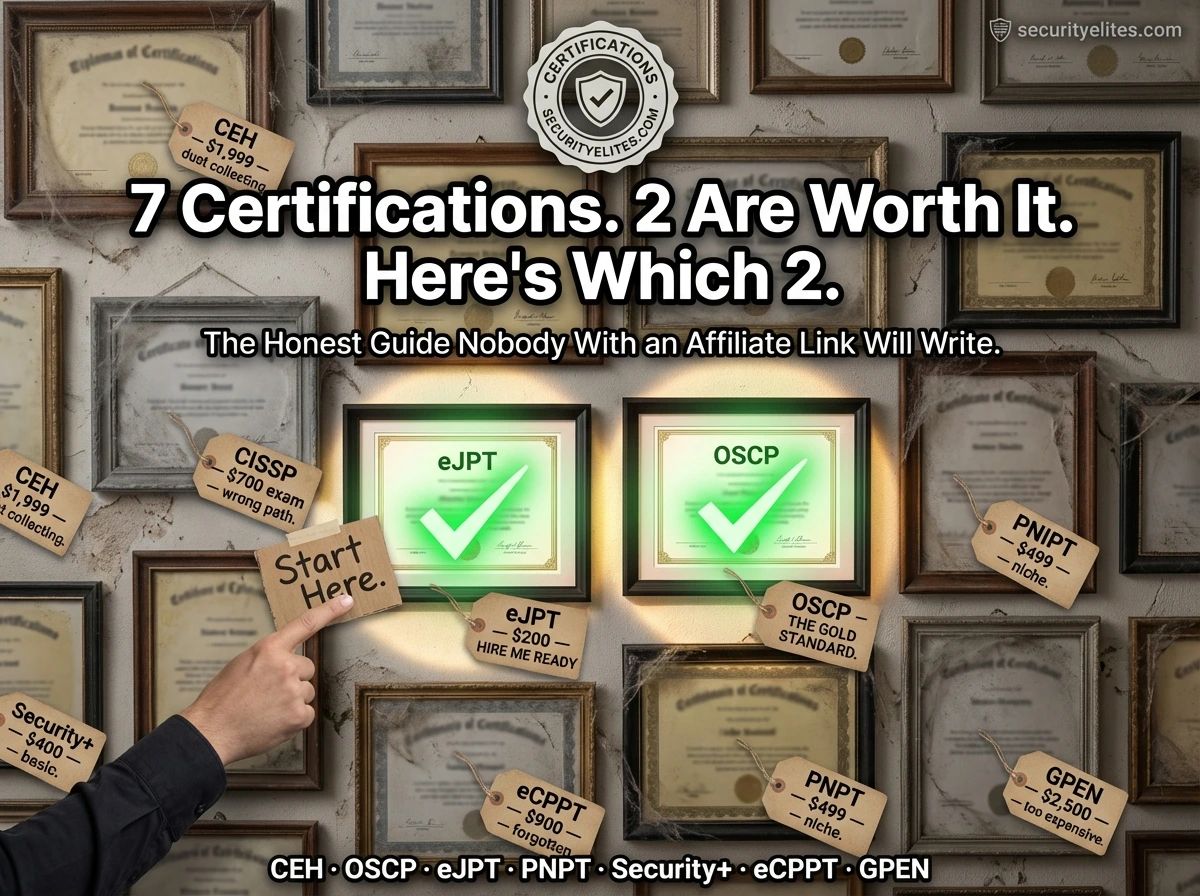
What Certifications Do Ethical Hackers Need 2026 — Honest Ranking (CEH vs OSCP vs eJPT vs Security+ Compared)
The honest, unaffiliated comparison of ethical hacking certifications in 2026 — CEH, OSCP, eJPT, CompTIA Security+, PNPT, eCPPT. Cost, difficulty,…