Reconnaissance Tools
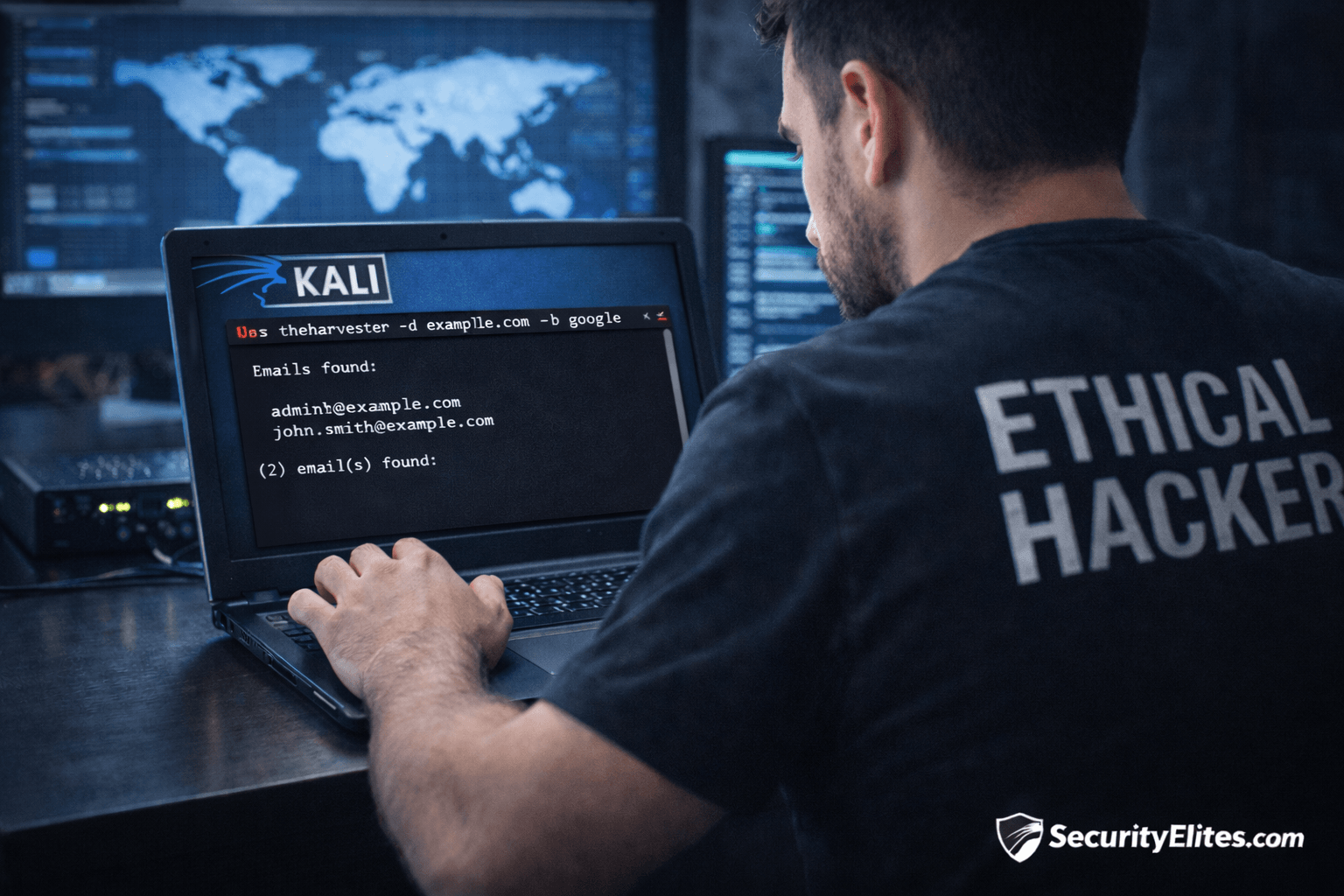
econnaissance tools for hacking are essential in the information-gathering phase of ethical hacking and penetration testing. In this section, you will explore powerful reconnaissance tools used to discover domains, subdomains, IP addresses, exposed services, and publicly available data. Tutorials cover tools like Nmap, Amass, Sublist3r, theHarvester, and Shodan with step-by-step setup and usage guides. Each article explains how security professionals map attack surfaces, automate recon workflows, and interpret scanning results safely. You will also learn how organizations defend against reconnaissance attempts and reduce information exposure. This category is ideal for bug bounty hunters, penetration testers, and cyber security students building their toolkit.
35 articles
Hacker Recon Checklist: 10-Step Ethical Hacking Recon Guide
Learn the hacker recon checklist used in penetration testing and bug bounty hunting. Step-by-step reconnaissance guide with tools and practical…
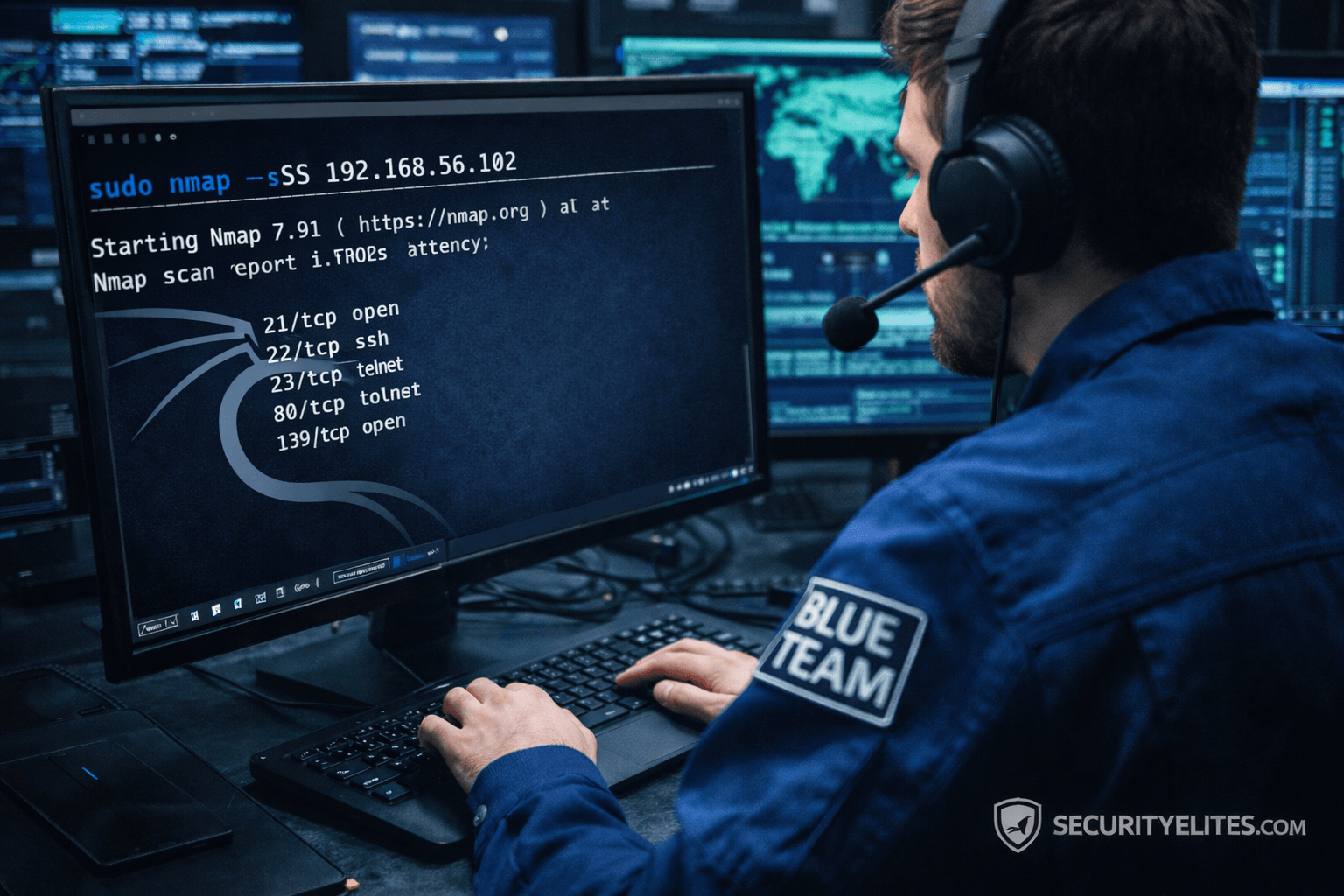
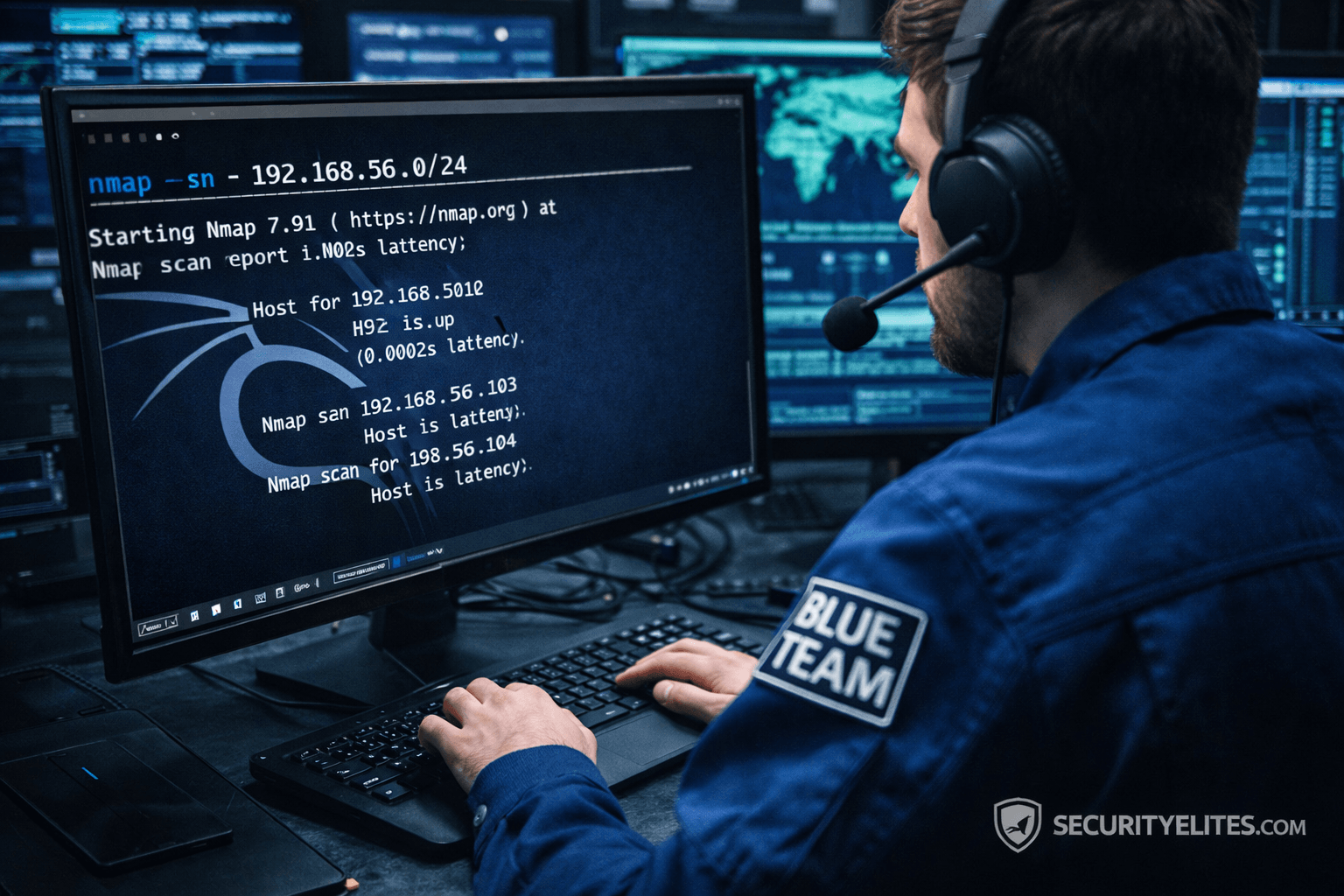
Network Scanning Tutorial Using Nmap Day 3 — Port Scanning Techniques Deep Dive
Network Scanning Tutorial Using Nmap Day 3 - Learn professional port scanning using Nmap including TCP SYN, Connect, UDP, and…
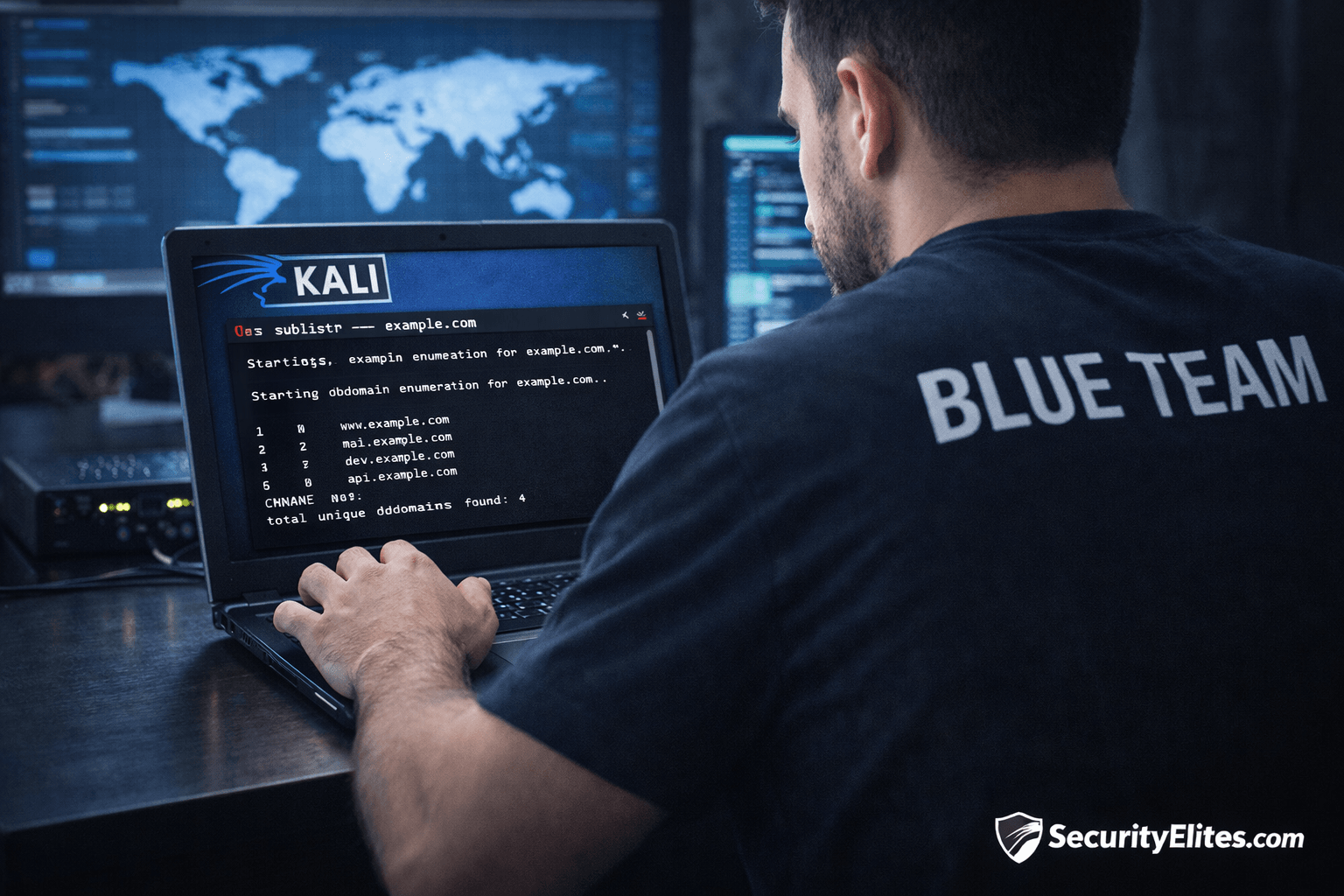
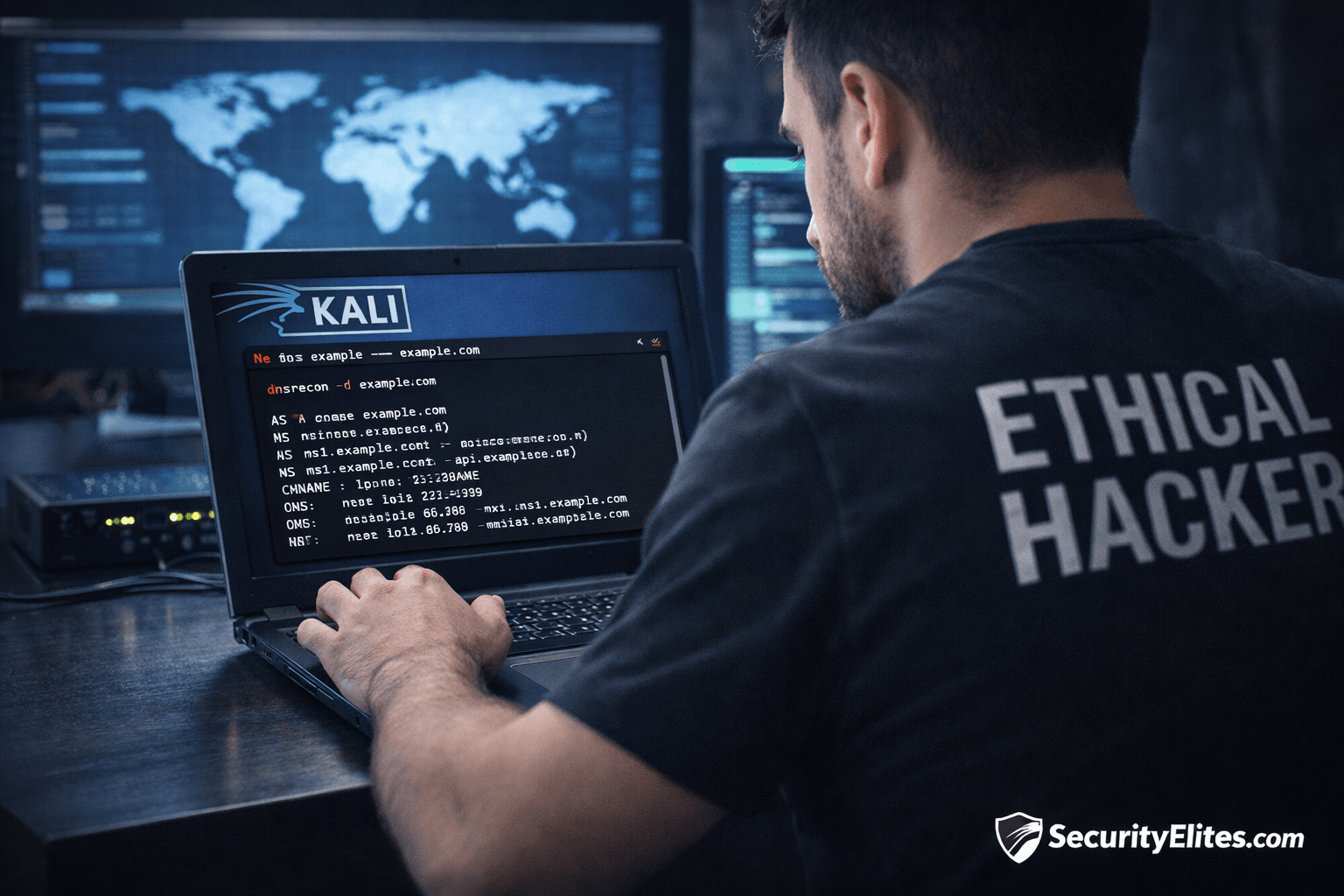
Information Gathering Using Kali Linux Day 3: Subdomain Enumeration with Sublist3r
Information Gathering Using Kali Linux Day 3 - Learn Information Gathering using Kali Linux with Sublist3r step-by-step. Discover hidden subdomains…
Network Scanning Tutorial Using Nmap Day 2— Host Discovery & Network Mapping
Network Scanning Tutorial Using Nmap Day 2 - Learn host discovery and network mapping using Nmap like professional ethical hackers.…
Information Gathering Using Kali Linux Day 2: DNS Reconnaissance with dnsrecon
Information Gathering Using Kali Linux Day 2 - Learn Information Gathering using Kali Linux with dnsrecon step-by-step. Discover DNS records,…
Network Scanning Tutorial Using Nmap for Beginners | Day 1 Ethical Hacking Course
Learn Network Scanning using Nmap from scratch. Day 1 of a complete 7-day ethical hacking course covering real penetration testing…