Cyber Security
32 articles
How Hackers Are Using ChatGPT for Phishing, Recon & Exploitation in 2026 — Complete Guide
How hackers use ChatGPT for cyberattacks in 2026 — phishing email generation, OSINT recon automation, exploit research, social engineering scripts…
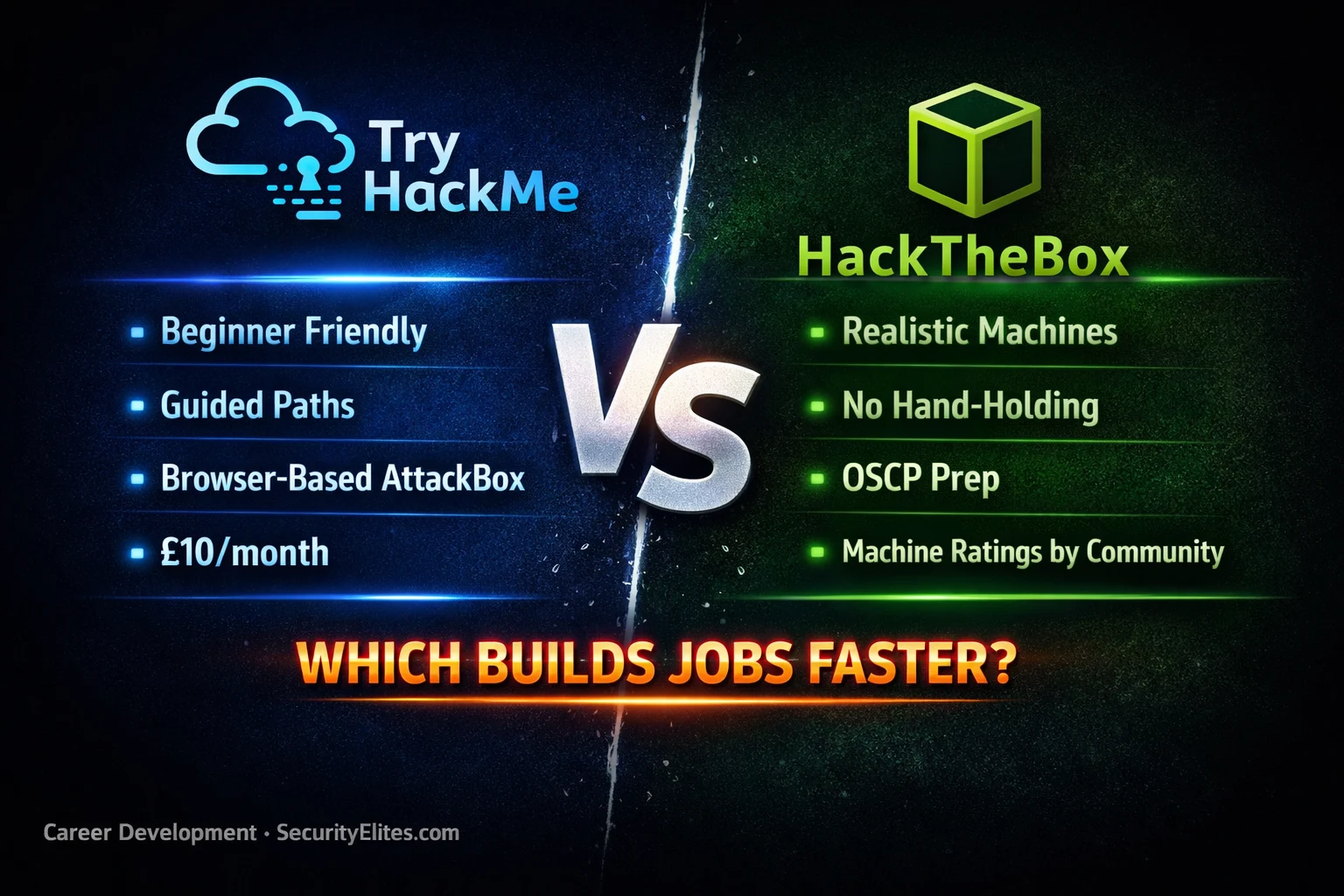
TryHackMe vs HackTheBox 2026 — Which Platform Builds Employable Skills Faster?
TryHackMe vs HackTheBox 2026 — honest comparison of both platforms for beginners and advanced learners. Which builds real employable skills…
ChatGPT Plugins Are a Security Nightmare — Here’s How Hackers Exploit Them
ChatGPT plugin security vulnerabilities 2026 — how attackers exploit insecure plugins to exfiltrate data, bypass restrictions, and hijack AI tool…
How Hackers Bypass 2FA in 2026 — 7 Methods That Still Work (Ethical Analysis)
How hackers bypass 2fa 2026 — 7 real methods used to circumvent two-factor authentication including SIM swapping, SS7 attacks, AiTM…
North Korea Just Poisoned the Axios npm Package — Here’s Exactly How a Supply Chain Attack Works (2026)
Google attributed the Axios npm supply chain attack to North Korean group UNC1069. Millions of developers affected. Here's exactly how…
ShinyHunters Stole 3 Million Cisco Records — Here’s Exactly How (2026)
Cisco Data Breach 2026 by ShinyHunters via Salesforce and AWS, exposing 3M+ records. Full attack breakdown, exploited vectors, and key…