Day 100 — Professional Pentester
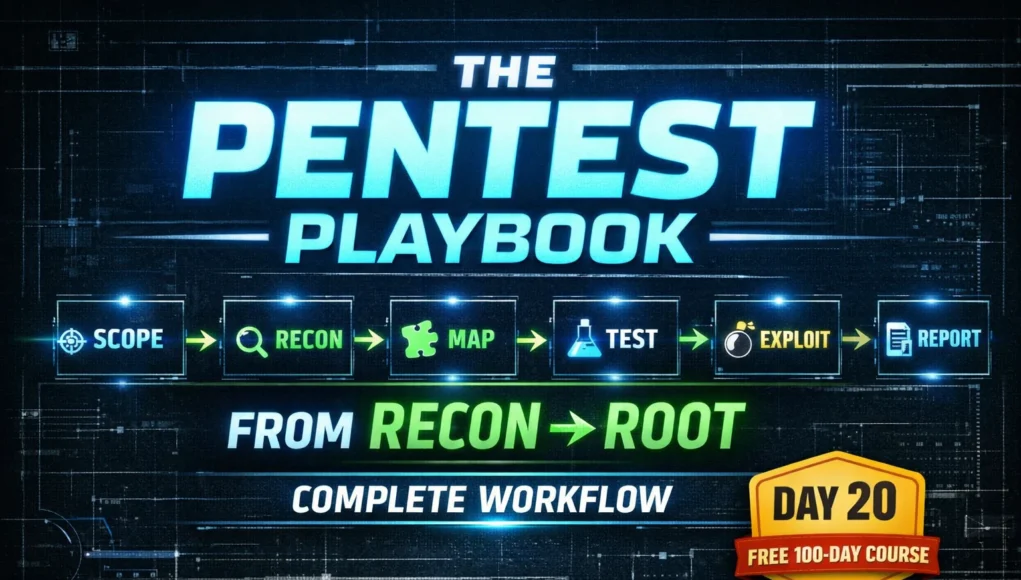
You’ve spent 10 days learning individual web vulnerabilities. Today you learn how a professional brings all of them together into a single, structured engagement that produces reliable, comprehensive results.
HTTP fundamentals → Burp Suite → SQL injection → XSS → CSRF → Broken access control → Security misconfiguration → File upload → Command injection. The methodology is what turns these separate skills into a professional workflow.
- The Six-Phase Methodology Overview
- Phase 1 — Scoping & Authorisation
- Phase 2 — Passive Reconnaissance
- Phase 3 — Application Mapping
- Phase 4 — Systematic Vulnerability Testing
- Phase 5 — Exploitation & Impact Proof
- Phase 6 — Documentation & Reporting
- Finding Report Template
- Master Testing Checklist
- Day 20 Practical Task
The Six-Phase Web Application Penetration Testing Methodology
Professional web application security testing follows a repeatable, documented methodology. Using a methodology rather than ad-hoc testing ensures coverage (you don’t miss vulnerability categories), defensibility (you can explain what you did and why), and consistency (every engagement meets the same quality standard). The methodology below aligns with the OWASP Testing Guide v4.2.
PHASE 1
Scoping & Authorisation
No testing happens before this phase is complete. Every professional engagement begins with written authorisation that clearly defines what is in scope, what is out of scope, testing windows, rules of engagement, and emergency contact procedures. This document protects both the tester and the client.
PHASE 2
Passive Reconnaissance
Before touching the target’s servers, gather as much intelligence as possible from public sources. This shapes your entire testing approach — the tech stack tells you which vulnerabilities are relevant, subdomain enumeration reveals additional attack surface, and leaked credentials from public breach databases might grant immediate access.
PHASE 3
Application Mapping — Building the Attack Surface Inventory
Before testing any individual vulnerability, you need a complete picture of the application. Walk through every page, form, function, and API endpoint — with Burp Suite running and Intercept off so HTTP History captures everything. This map is what you systematically test in Phase 4.
PHASE 4
Systematic Vulnerability Testing — The OWASP Coverage Map
With your attack surface inventory in hand, test each category systematically — working through the OWASP Top 10 against every relevant endpoint. The key word is systematic: don’t jump between techniques randomly. Finish one category before moving to the next, and document as you go.
| Test Category | OWASP | Key Tests | Course Day |
|---|---|---|---|
| Authentication | A07 | Default creds, brute force, password reset, lockout | Day 15 |
| Access Control | A01 | IDOR, horizontal/vertical escalation, forced browsing | Day 16 |
| Injection | A03 | SQLi, command injection, LDAP, NoSQL injection | Days 13, 19 |
| XSS | A03 | Reflected, stored, DOM-based in all output contexts | Day 14 |
| CSRF | A04 | Token absent/bypassable, SameSite misconfigured | Day 15 |
| Misconfiguration | A05 | Default creds, debug mode, headers, Nikto | Day 17 |
| File Upload | A03/A05 | Extension bypass, MIME bypass, web shell upload | Day 18 |
| Crypto Failures | A02 | HTTP in use, weak TLS, cleartext secrets, MD5 passwords | Days 5, 10 |
| Session Mgmt | A07 | Token entropy, HttpOnly/Secure flags, fixation | Days 11, 12 |
PHASE 5
Exploitation & Impact Proof
Finding a vulnerability is not the end — you need to confirm exploitability and demonstrate actual impact. A client needs to understand not just that a vulnerability exists, but what an attacker could concretely do with it. This is what turns a finding from a theoretical concern into an urgent remediation priority.
id output. Each finding needs a concrete “here’s what an attacker can actually obtain” statement.
PHASE 6
Documentation & Reporting
The report is the product of a penetration test. It is what the client receives, what the development team reads, what the remediation effort is based on, and what demonstrates the value of the engagement. A technically brilliant test produces zero value if the findings can’t be communicated clearly and acted upon.
Finding Report Template — Every Vulnerability, Same Structure
Every finding in a professional report follows the same structure. This consistency means developers always know where to find the information they need — what the vulnerability is, where it is, how serious it is, and exactly what to do about it.
📋 Master Web Application Testing Checklist
Use this checklist on every engagement. It ensures complete coverage and gives you a documented record of what was tested — valuable for both quality assurance and dispute resolution if a finding is later questioned.
🎯 Day 20 Practical Task — Full Methodology Run on DVWA
~/Day20/scope.txt defining in-scope URLs, out-of-scope elements, testing window, and two test account details. Even for a lab this exercise builds the professional habit of documenting before testing.~/Day20/dvwa_report.md — one finding entry per vulnerability, severity-rated, with your evidence notes. This becomes your Phase 2 portfolio piece. Share your finding count with #Day20Done 📄You can now approach a web application as a professional — with a methodology, a systematic testing process, and the ability to produce findings that development teams can actually act on. Phase 3 begins with Metasploit — where we move beyond web application testing into network exploitation, post-exploitation, and pivoting.
Frequently Asked Questions — Day 20 Web App Pentesting Methodology
SecurityElites — Complete Web Application Security Guide
SecurityElites — Burp Suite Tutorial (Core Testing Tool)
OWASP Testing Guide v4.2 — Complete Reference →
PortSwigger Web Security Academy — Free Practice Labs →
OWASP Top 10 — Official Reference →
Phase 2 is where most students start this course — jumping straight to SQL injection without foundations. You’ve done it the right way: built the networking and Linux foundation first, then systematically worked through every major web vulnerability category. You know how each attack works at the protocol level. The methodology today is what turns that knowledge into professional capability. Phase 3 takes it further — into the infrastructure exploitation layer where web vulnerabilities meet network access.