Ethical Hacking Basics
77 articles
Dark Web Guide: Dark Web Explained and What Hackers Really Do There (2026)
Complete Dark Web Guide explaining how the Dark Web works, why hackers use it, and how cybersecurity experts track Dark…
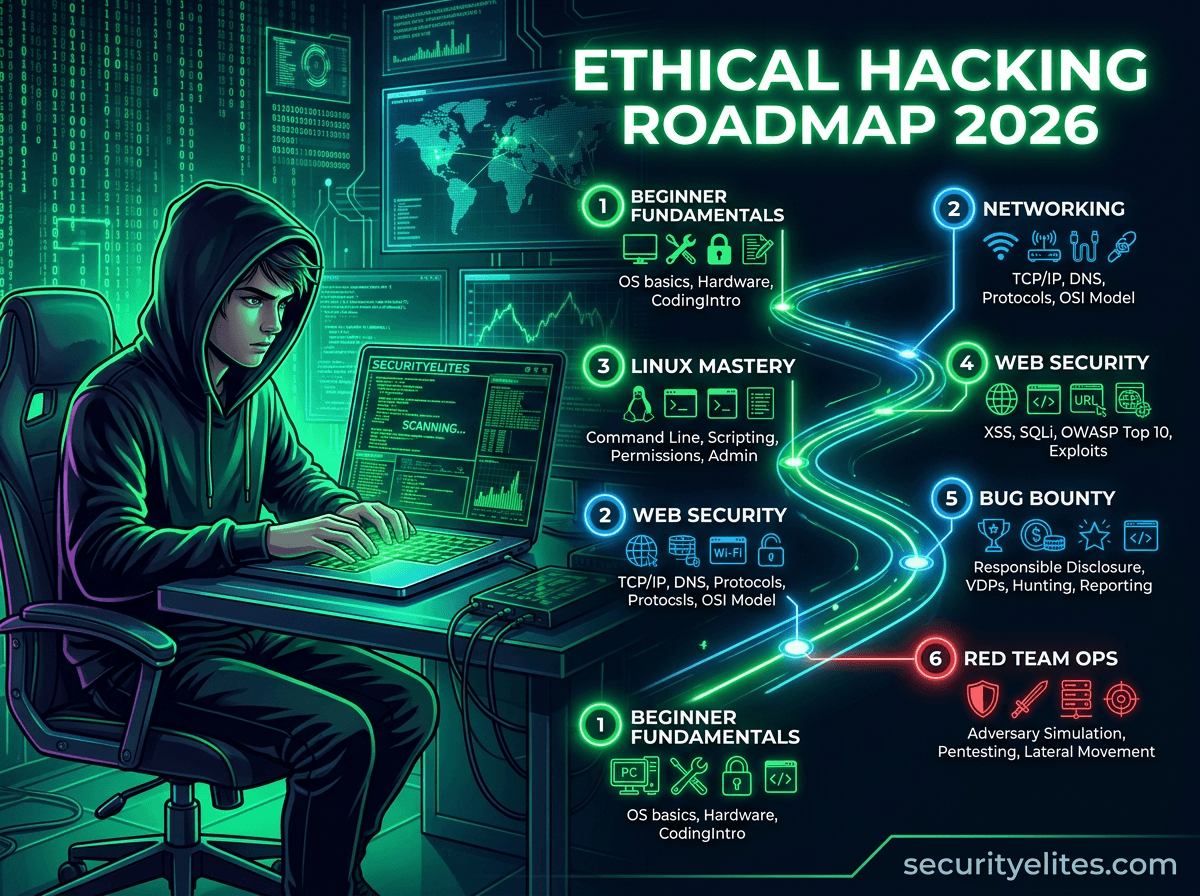
Ethical Hacking Roadmap 2026: How to Become Ethical Hacker (Beginner to Expert)
Learn the complete ethical hacking roadmap 2026 with step-by-step labs, tools, and cybersecurity skills required to become an ethical hacker…
Kali Linux Tutorial for Beginners 2026(Complete Ethical Hacking Guide)
Learn Kali Linux from scratch with this beginner-friendly Kali Linux tutorial. Step-by-step installation, tools overview, and ethical hacking training for…
Amass Tutorial (2026): Powerful Subdomain Enumeration Guide for Kali Linux
Learn Amass tutorial for subdomain enumeration and reconnaissance in Kali Linux. Step-by-step ethical hacking guide used by penetration testers and…
Bug Bounty Case Study: 8 Steps to Discover an IDOR Vulnerability
This Bug Bounty Case Study explains how ethical hackers discover IDOR vulnerabilities using real penetration testing techniques, attacker mindset, and…
Hacker Recon Checklist: 10-Step Ethical Hacking Recon Guide
Learn the hacker recon checklist used in penetration testing and bug bounty hunting. Step-by-step reconnaissance guide with tools and practical…
Authentication Bypass Basics for Beginners | Complete Ethical Hacking Guide
Learn authentication bypass basics with real penetration testing techniques, hands-on labs, attacker methodology, and enterprise defense strategies.
Burp Suite Beginner Guide: Complete Ethical Hacking & Web Testing Tutorial
Burp Suite Beginner Guide to learn Burp Suite step-by-step with this beginner ethical hacking guide covering interception, vulnerability testing, attacker…
6 Powerful Stages of the Pentesting Lifecycle: Complete Penetration Testing Guide
Learn the 6 powerful stages of the Pentesting Lifecycle used by ethical hackers. Step-by-step penetration testing process, tools, labs, and…