Information Gathering
27 articles
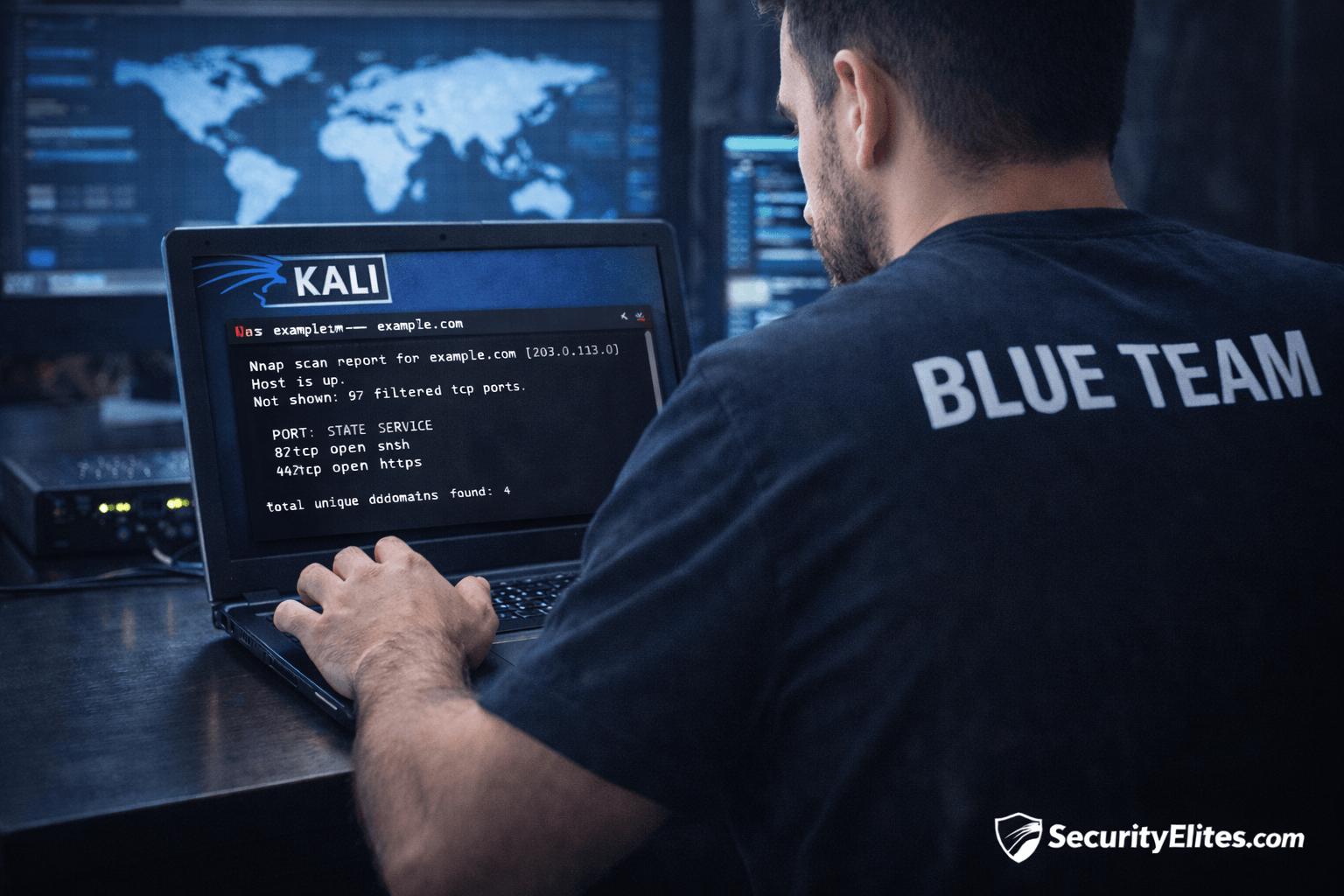
Information Gathering Using Kali Linux Day 4: Network Mapping with Nmap
Information Gathering Using Kali Linux Day 4 - Learn Information Gathering using Kali Linux with Nmap step-by-step. Discover live hosts,…
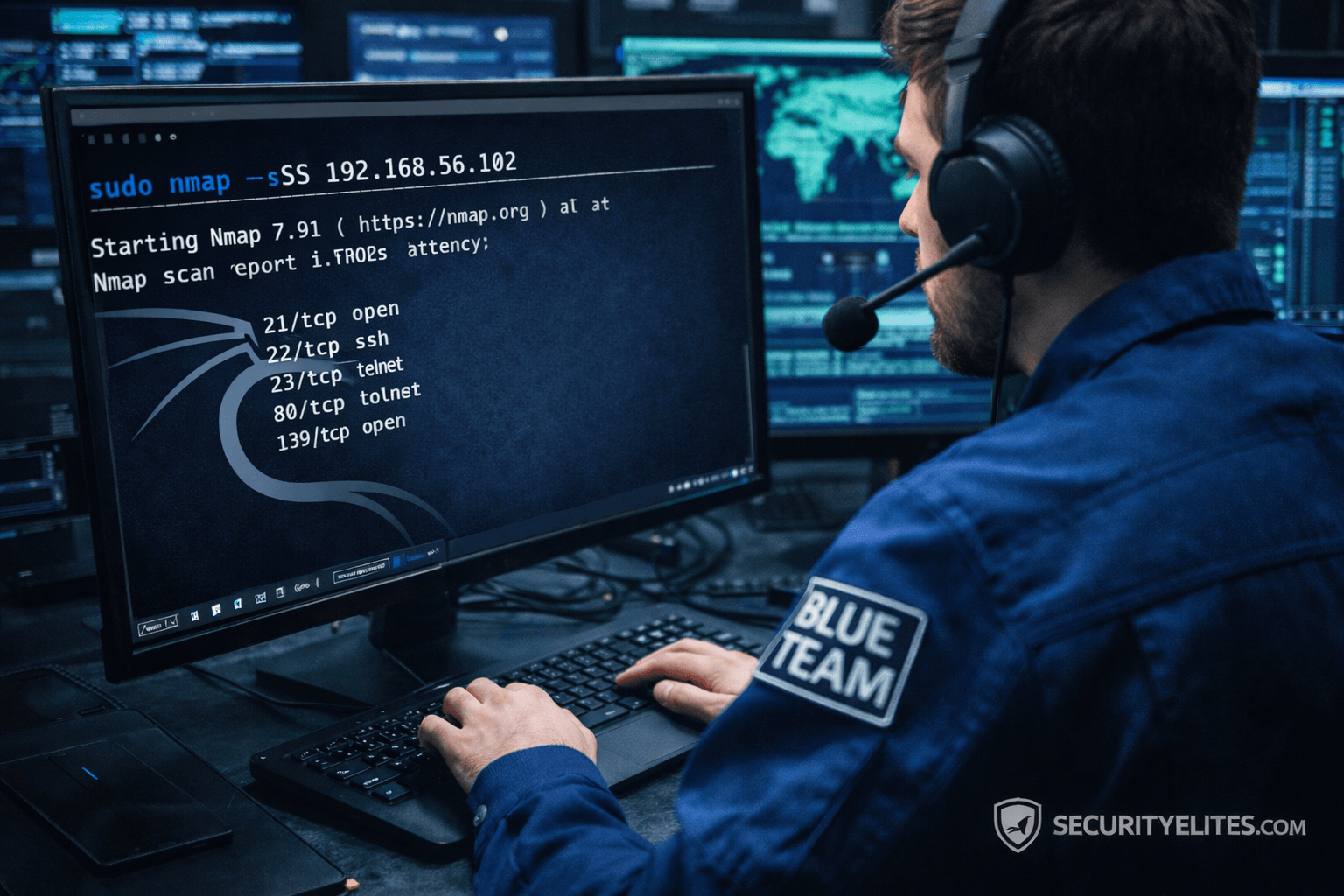
Network Scanning Tutorial Using Nmap Day 3 — Port Scanning Techniques Deep Dive
Network Scanning Tutorial Using Nmap Day 3 - Learn professional port scanning using Nmap including TCP SYN, Connect, UDP, and…
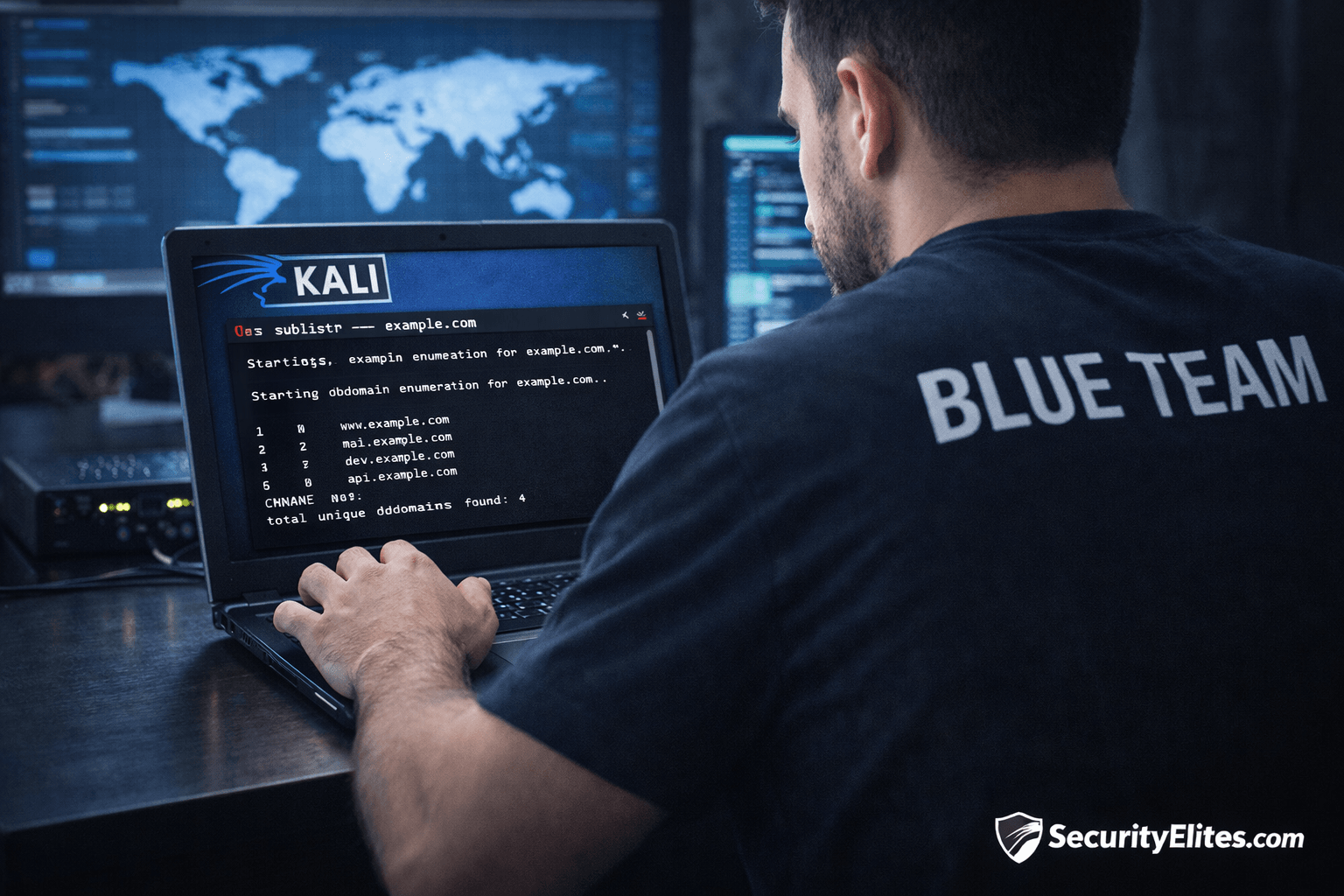
Information Gathering Using Kali Linux Day 3: Subdomain Enumeration with Sublist3r
Information Gathering Using Kali Linux Day 3 - Learn Information Gathering using Kali Linux with Sublist3r step-by-step. Discover hidden subdomains…
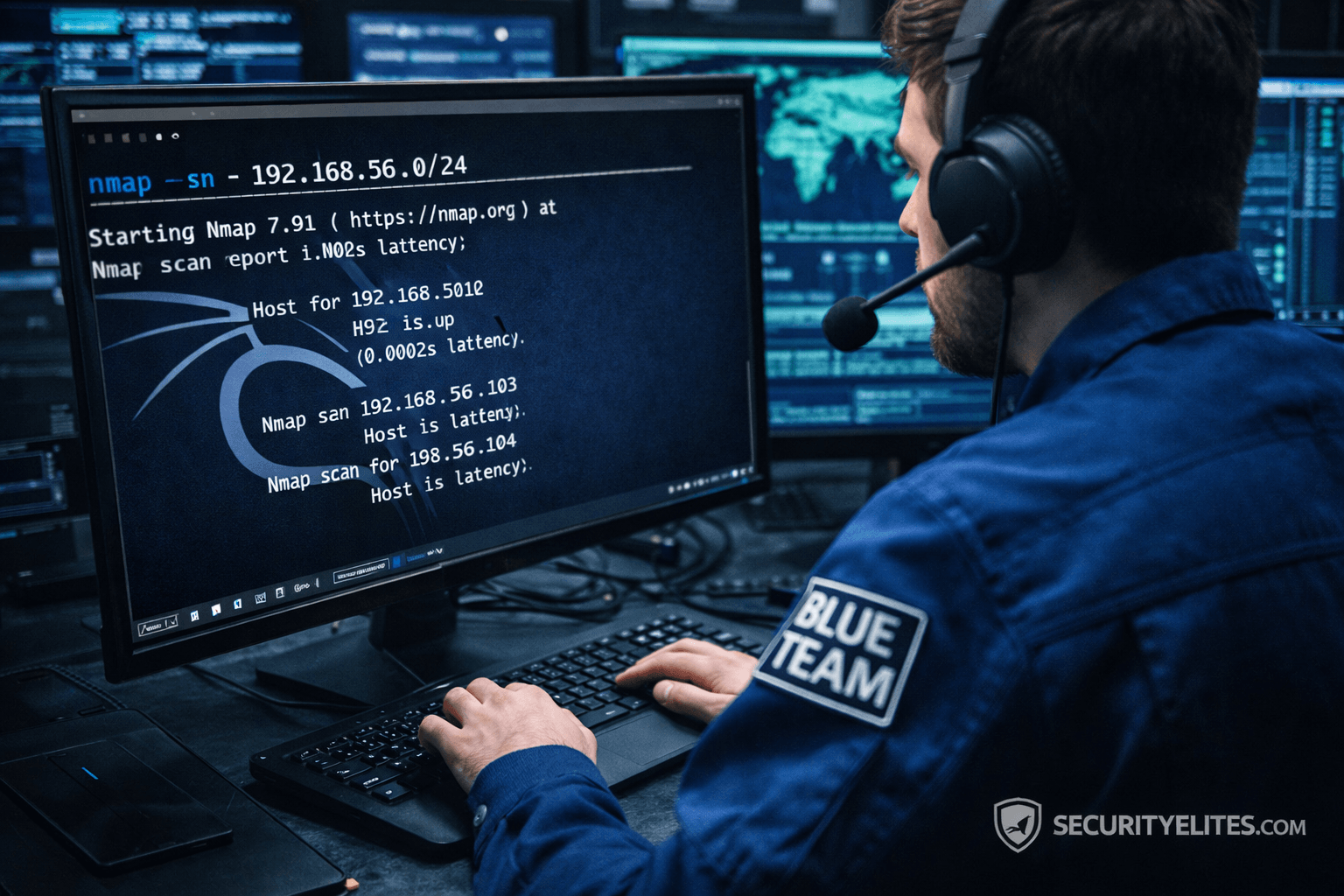
Network Scanning Tutorial Using Nmap Day 2— Host Discovery & Network Mapping
Network Scanning Tutorial Using Nmap Day 2 - Learn host discovery and network mapping using Nmap like professional ethical hackers.…
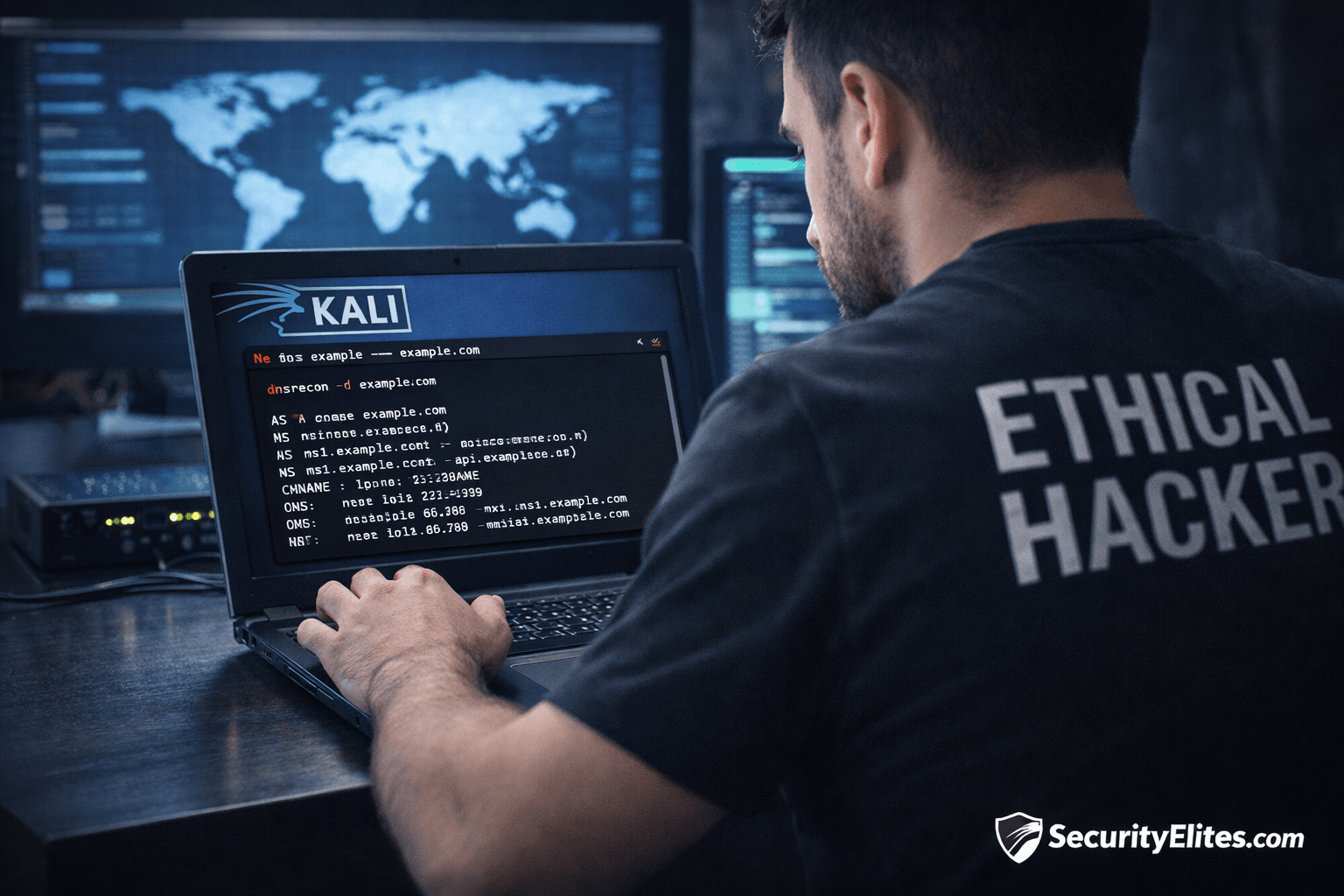
Information Gathering Using Kali Linux Day 2: DNS Reconnaissance with dnsrecon
Information Gathering Using Kali Linux Day 2 - Learn Information Gathering using Kali Linux with dnsrecon step-by-step. Discover DNS records,…
Information Gathering Using Kali Linux Day 1: WHOIS Tutorial for Beginners
Information Gathering Using Kali Linux Day 1 - Learn Information Gathering using Kali Linux with WHOIS step-by-step. Beginner-friendly ethical hacking…