Kali Linux Tools
Explore the powerful penetration testing tools built into Kali Linux. This section includes tutorials on Metasploit, Burp Suite, Hydra, Aircrack-ng, Nikto, and more. Learn installation, configuration, and real-world usage through hands-on demonstrations.
84 articles
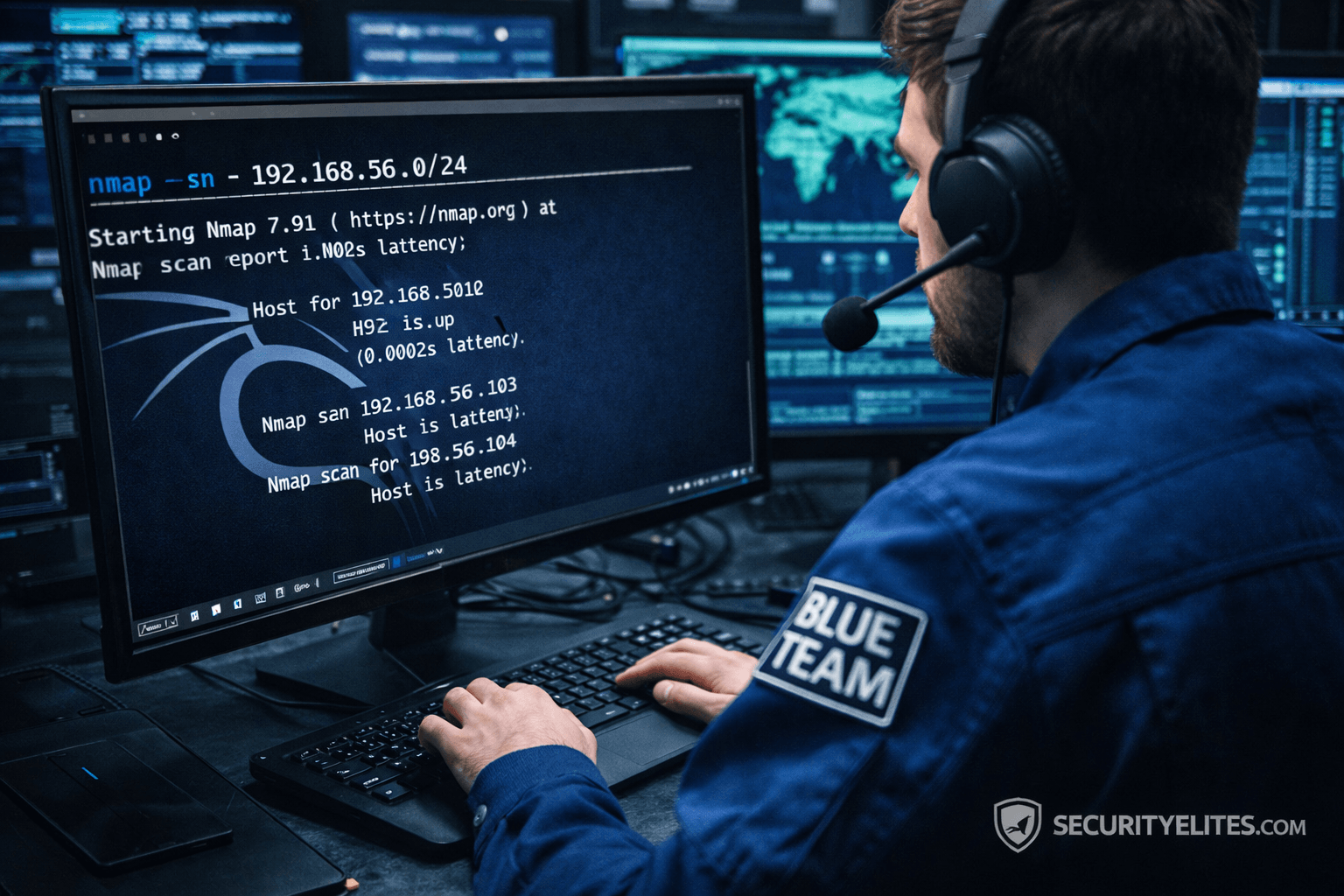
Network Scanning Tutorial Using Nmap Day 2— Host Discovery & Network Mapping
Network Scanning Tutorial Using Nmap Day 2 - Learn host discovery and network mapping using Nmap like professional ethical hackers.…
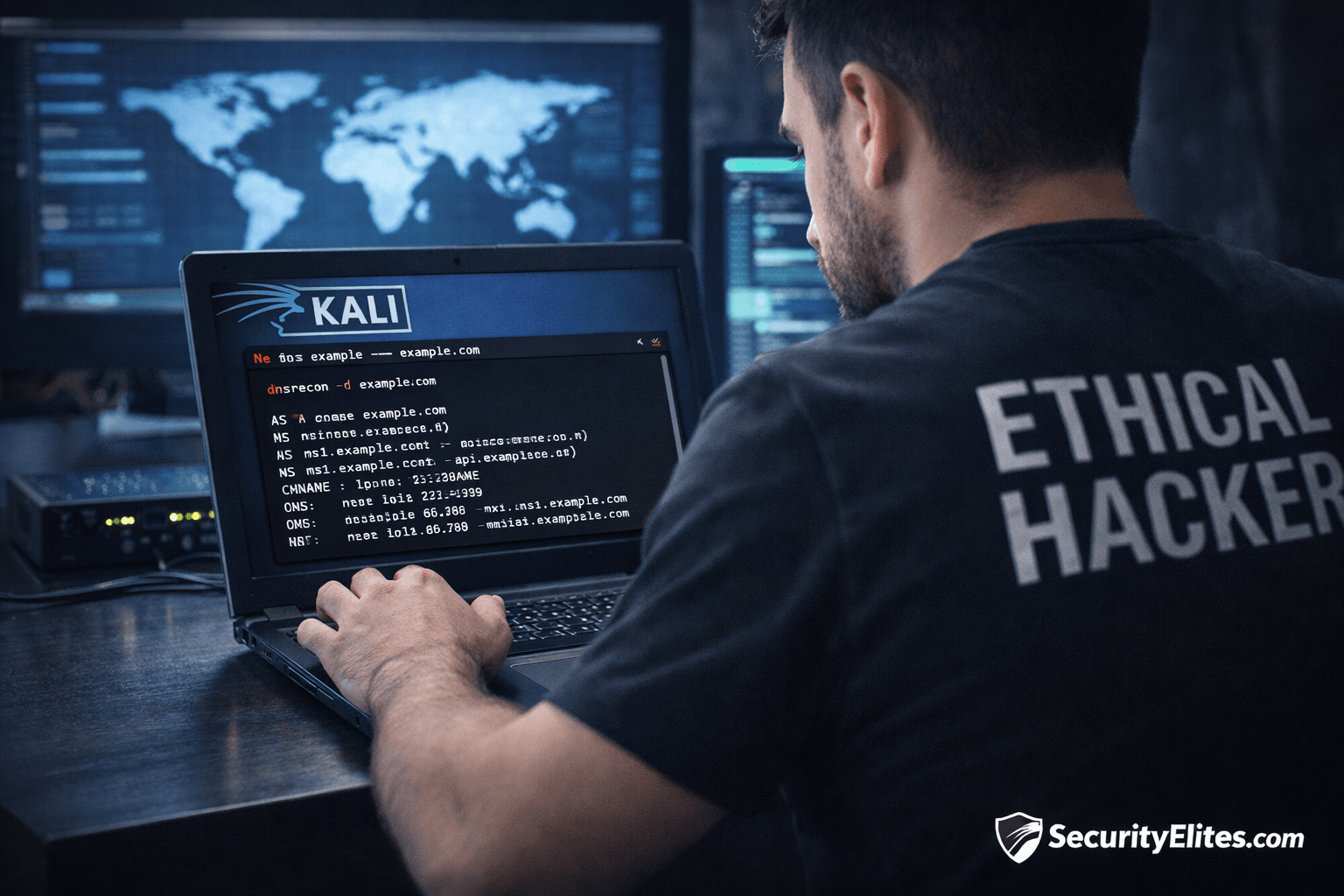
Information Gathering Using Kali Linux Day 2: DNS Reconnaissance with dnsrecon
Information Gathering Using Kali Linux Day 2 - Learn Information Gathering using Kali Linux with dnsrecon step-by-step. Discover DNS records,…
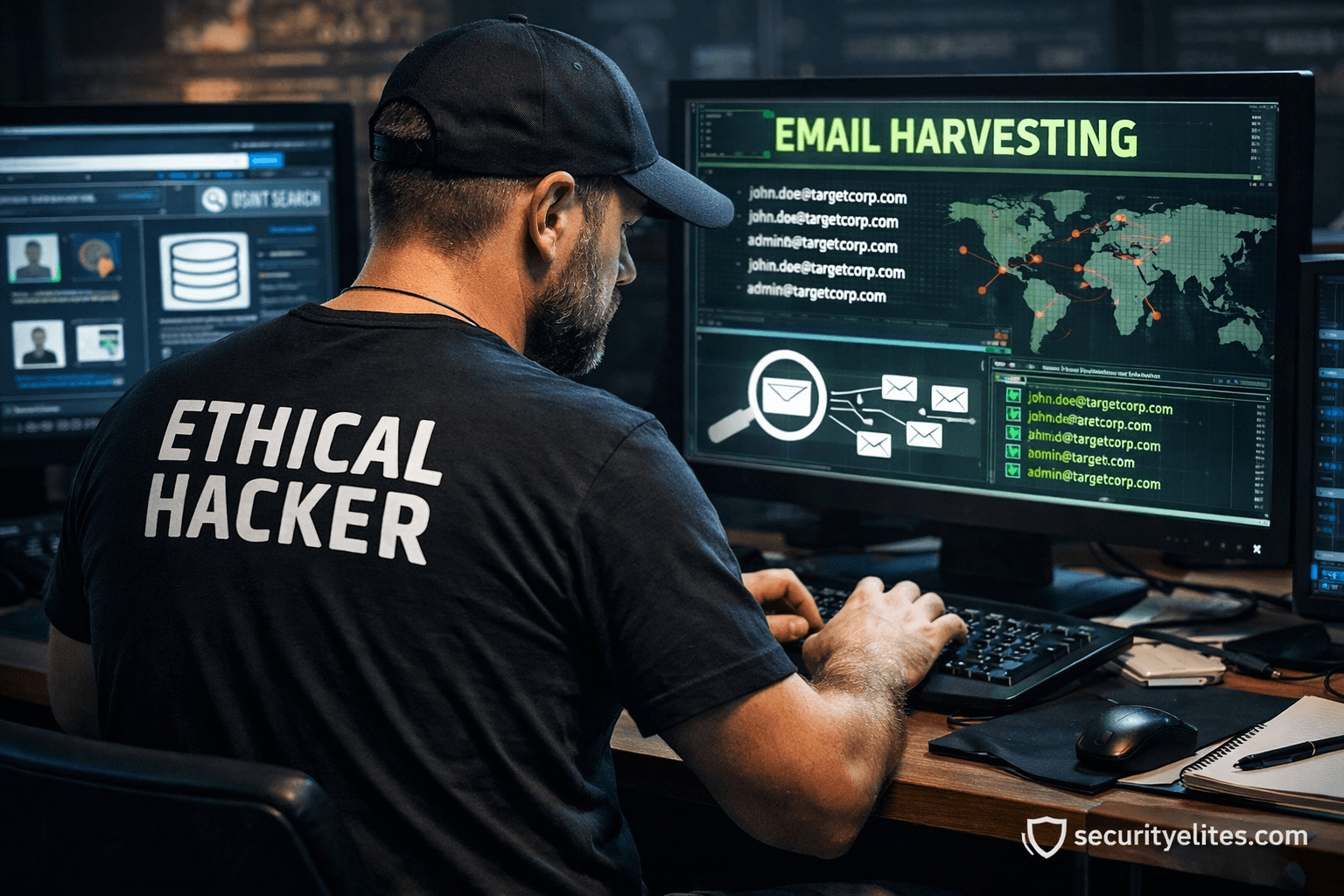
Email Harvesting Tutorial for Ethical Hackers – Beginner to Pro Guide
Email Harvesting Tutorial step-by-step with practical ethical hacking lab, OSINT reconnaissance workflow, tools, attacker mindset, and enterprise defense strategies.
Information Gathering Tools in Kali Linux – Complete Beginner to Expert Guide
Learn Information Gathering Tools in Kali Linux with real-world cybersecurity methodology, professional workflows, beginner guidance, and ethical hacking insights.
Best Kali Linux Tools for Beginners (2026 Ethical Hacking Guide)
Learn the best Kali Linux tools for beginners with real ethical hacking workflows, expert tips, and practical cybersecurity guidance from…
Top 20 Kali Tools Explained Practically — Real Ethical Hacker Workflow Guide
Learn the top 20 Kali Linux tools explained practically with real-world penetration testing examples, expert tips, workflows, and beginner guidance.