Kali Linux Tools
Explore the powerful penetration testing tools built into Kali Linux. This section includes tutorials on Metasploit, Burp Suite, Hydra, Aircrack-ng, Nikto, and more. Learn installation, configuration, and real-world usage through hands-on demonstrations.
92 articles
Network Scanning Tutorial Using Nmap Day 4 — Service & Version Enumeration
Network Scanning Tutorial Using Nmap Day 4 - Learn service and version enumeration using Nmap like professional penetration testers. Day…
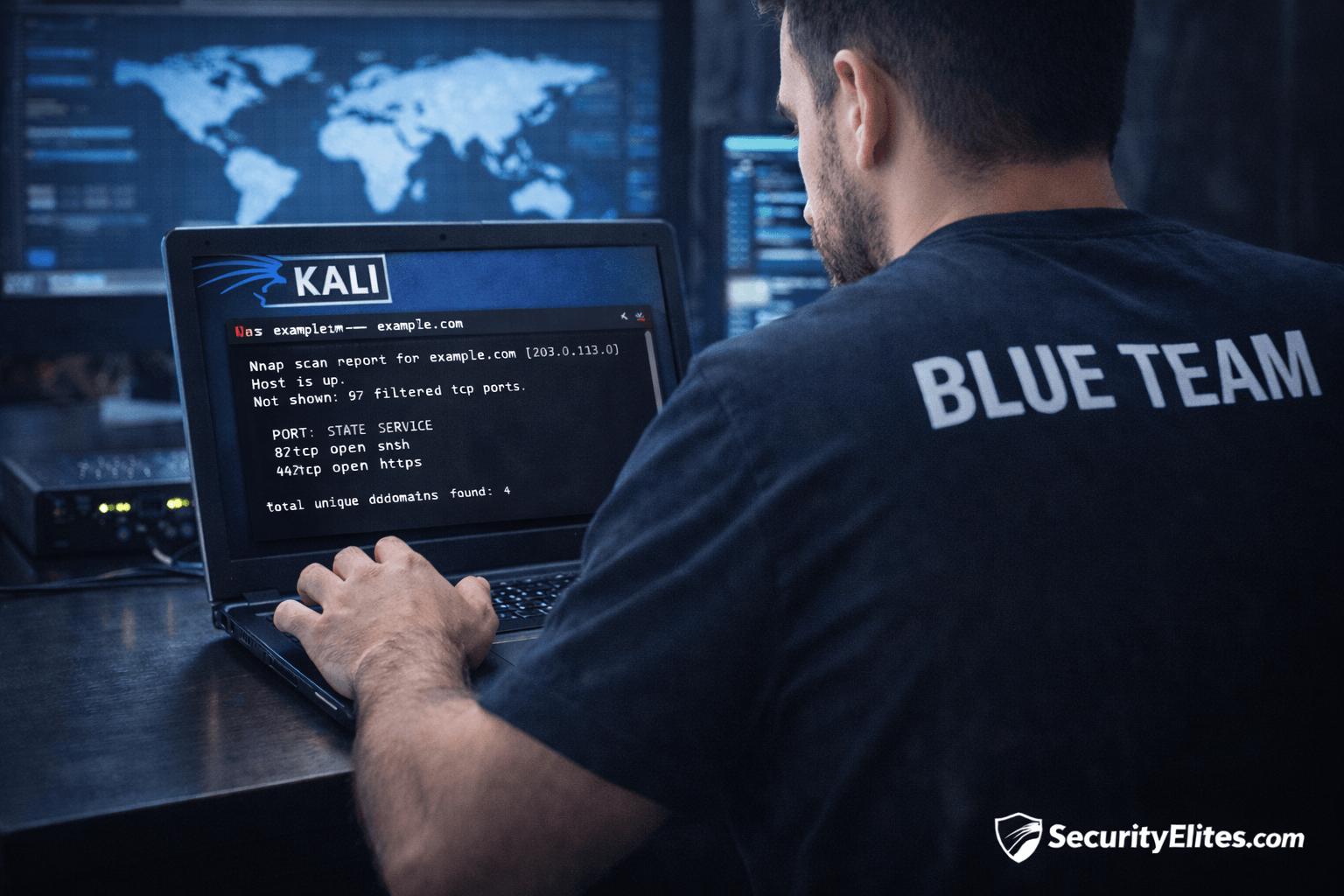
Information Gathering Using Kali Linux Day 4: Network Mapping with Nmap
Information Gathering Using Kali Linux Day 4 - Learn Information Gathering using Kali Linux with Nmap step-by-step. Discover live hosts,…
Authentication Bypass Basics for Beginners | Complete Ethical Hacking Guide
Learn authentication bypass basics with real penetration testing techniques, hands-on labs, attacker methodology, and enterprise defense strategies.
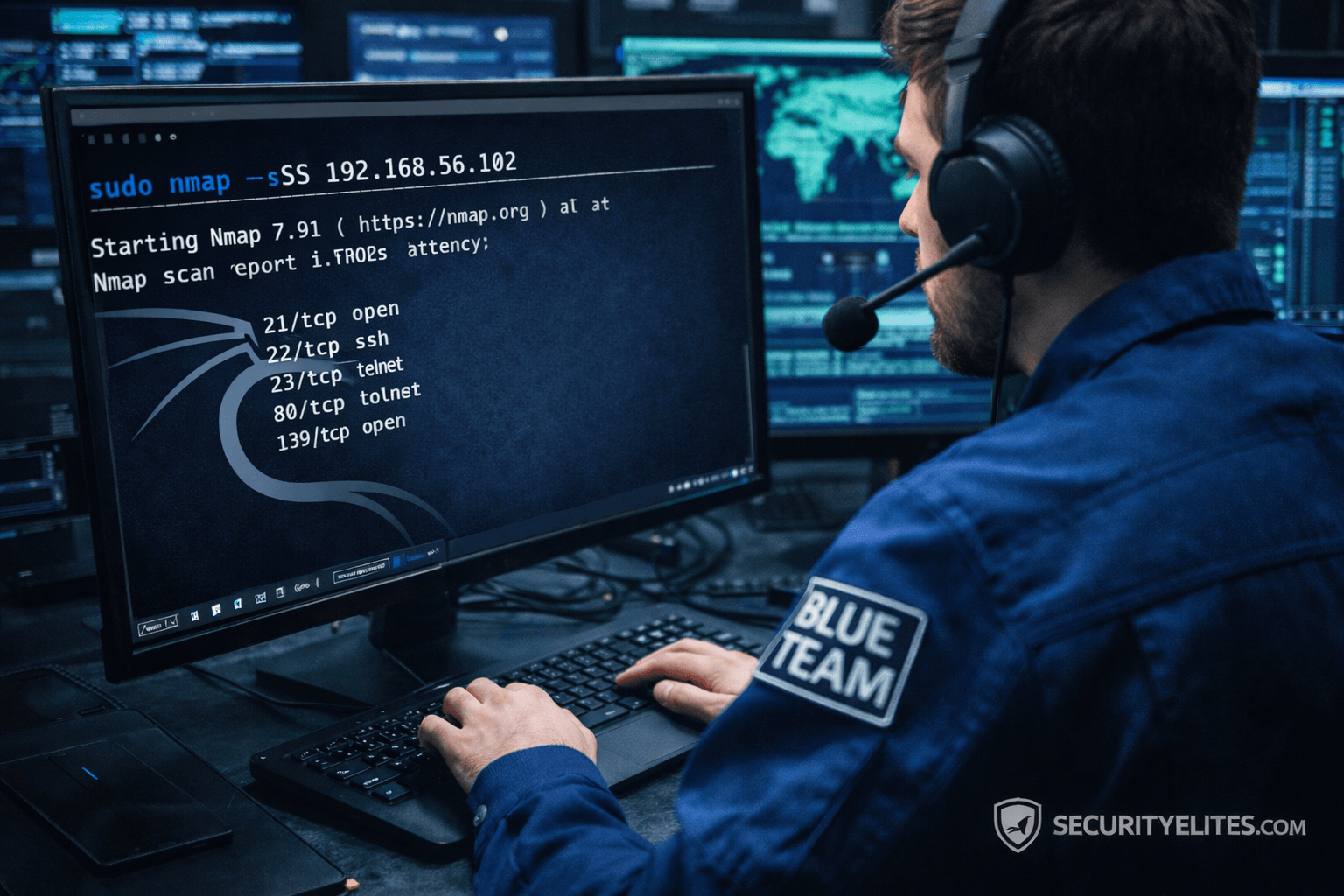
Network Scanning Tutorial Using Nmap Day 3 — Port Scanning Techniques Deep Dive
Network Scanning Tutorial Using Nmap Day 3 - Learn professional port scanning using Nmap including TCP SYN, Connect, UDP, and…
Burp Suite Beginner Guide: Complete Ethical Hacking & Web Testing Tutorial
Burp Suite Beginner Guide to learn Burp Suite step-by-step with this beginner ethical hacking guide covering interception, vulnerability testing, attacker…
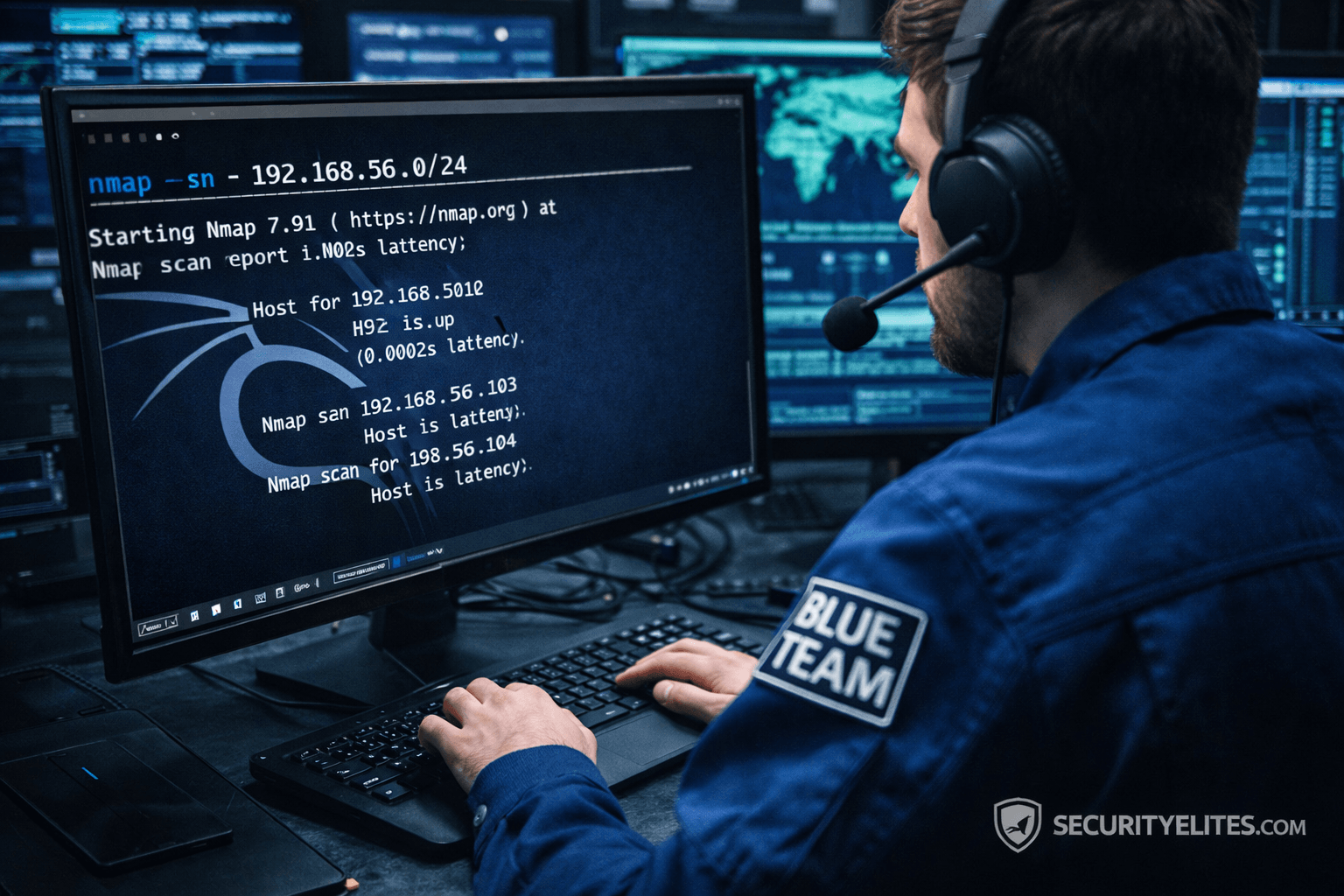
Network Scanning Tutorial Using Nmap Day 2— Host Discovery & Network Mapping
Network Scanning Tutorial Using Nmap Day 2 - Learn host discovery and network mapping using Nmap like professional ethical hackers.…
Information Gathering Using Kali Linux Day 2: DNS Reconnaissance with dnsrecon
Information Gathering Using Kali Linux Day 2 - Learn Information Gathering using Kali Linux with dnsrecon step-by-step. Discover DNS records,…
Email Harvesting Tutorial for Ethical Hackers – Beginner to Pro Guide
Email Harvesting Tutorial step-by-step with practical ethical hacking lab, OSINT reconnaissance workflow, tools, attacker mindset, and enterprise defense strategies.
Information Gathering Tools in Kali Linux – Complete Beginner to Expert Guide
Learn Information Gathering Tools in Kali Linux with real-world cybersecurity methodology, professional workflows, beginner guidance, and ethical hacking insights.