Kali Linux
Master Kali Linux with step-by-step tutorials covering installation, configuration, commands, and penetration testing tools. This section includes detailed guides on wireless attacks, password cracking, reconnaissance tools, and exploitation frameworks available in Kali Linux. Learn how to set up hacking labs, use terminal commands efficiently, and perform real-world security testing using tools like Aircrack-ng, Hydra, John the Ripper, and Wireshark. Perfect for beginners and cyber security professionals looking to enhance their penetration testing skills.
110 articles
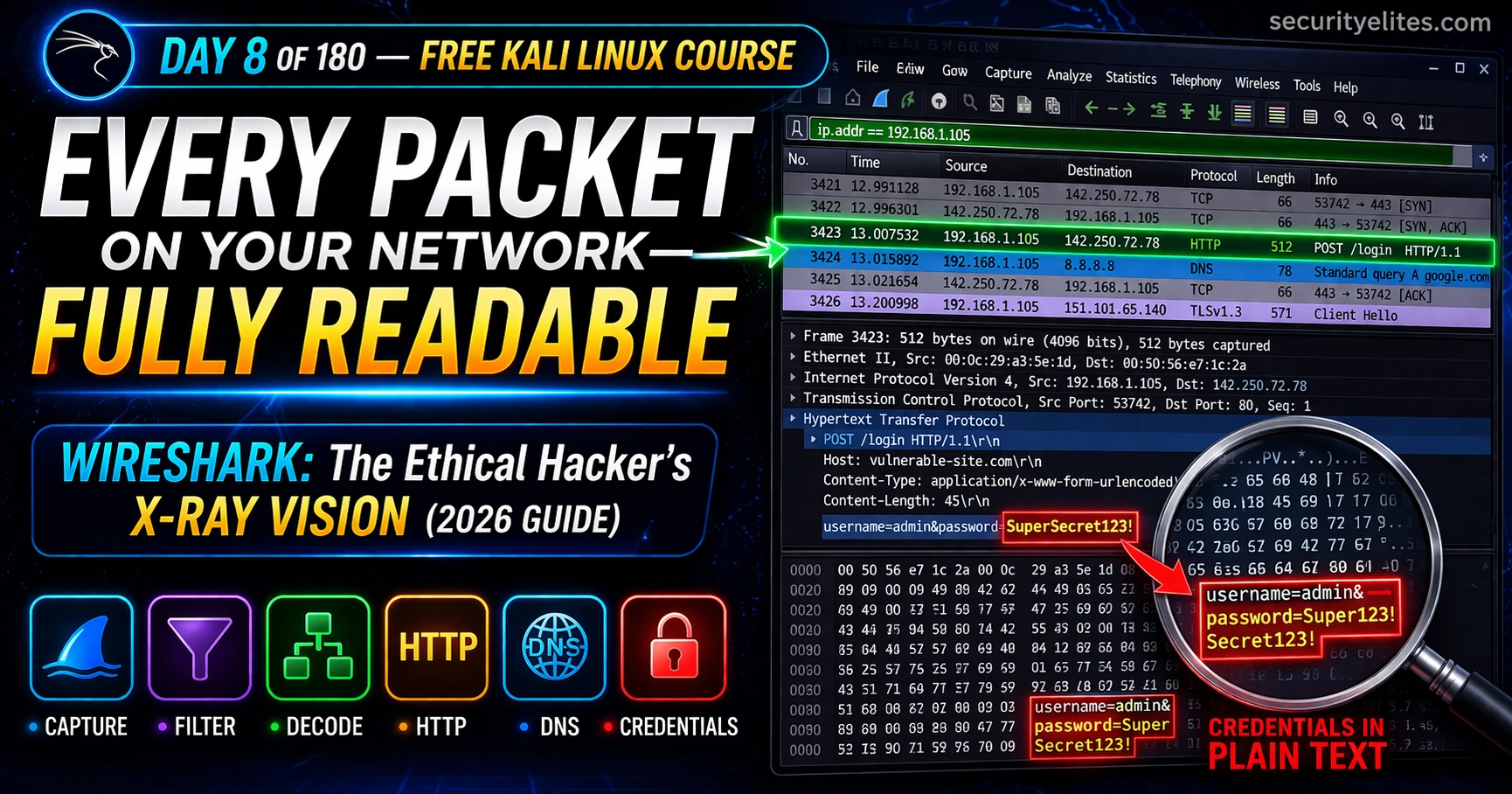
Kali Linux Day 8: Wireshark Tutorial 2026 — Capture & Analyse Real Network Traffic (Complete Guide)
Day 8 of 180. Wireshark Tutorial on Kali Linux from scratch — capture live network traffic, analyze PCAP files, apply…
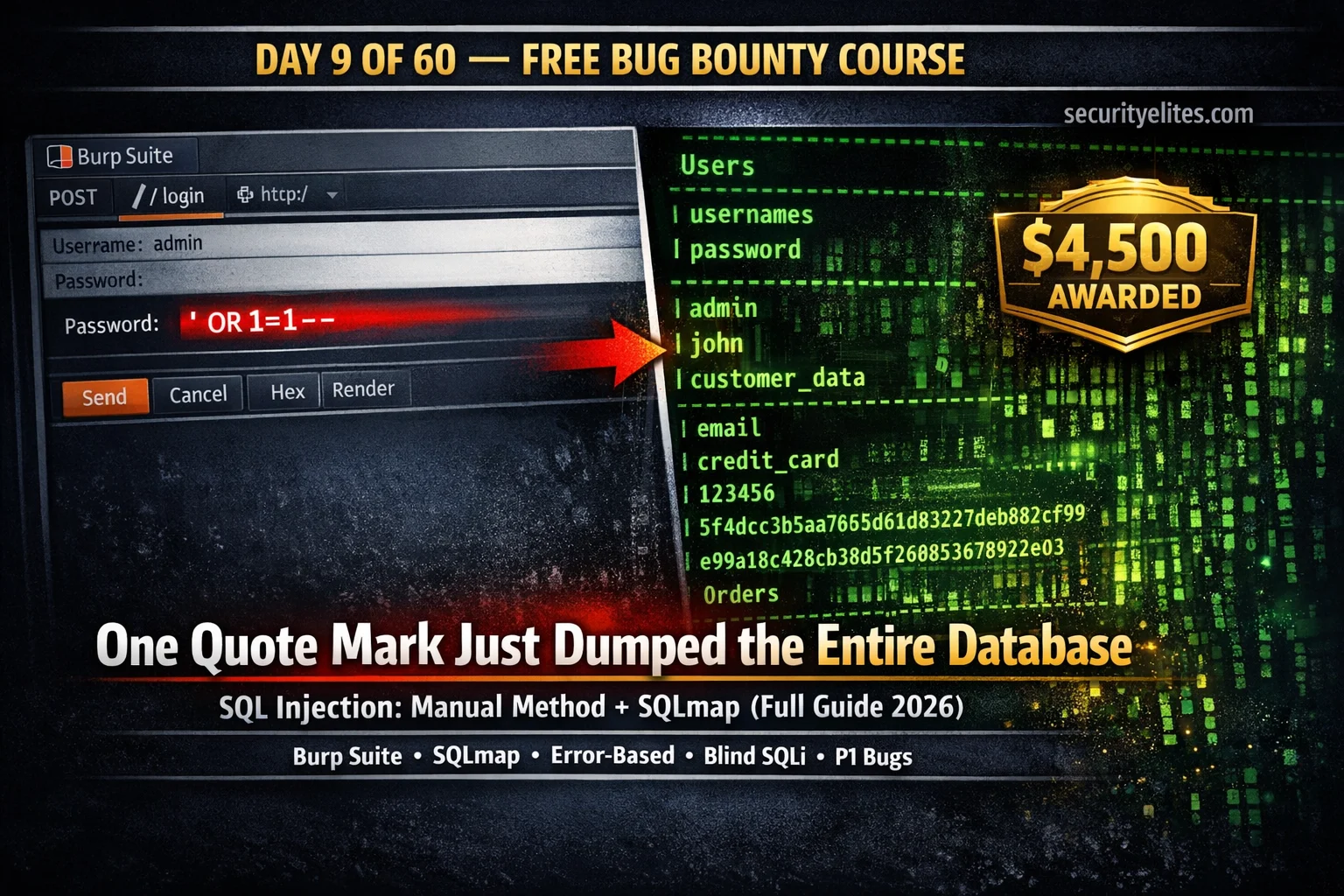
Day 9: SQL Injection for Bug Bounty 2026 — Manual Testing + SQLmap Complete Guide
Day 9 of 60. Learn SQL injection for bug bounty: manual testing with Burp Suite, error-based, UNION-based, blind SQLi, SQLmap…
Kali Linux Day 7: SQLmap Tutorial (2026) — Automate SQL Injection Like a Pro 🔥
Complete SQLmap tutorial for Kali Linux — detect SQL injection, enumerate databases, extract tables, dump credentials, use Burp request files,…
Day 21: Metasploit Framework — From Module to Shell (Complete Beginner’s Guide 2026)
Day 21 of 100. Master the Metasploit Framework — msfconsole commands, auxiliary and exploit modules, Meterpreter, and a full Metasploitable…
Kali Linux Day 6: Nikto Tutorial (Kali Linux 2026): Find CRITICAL Web Server Vulnerabilities in Minutes
Complete Nikto tutorial for Kali Linux: learn basic scans, HTTPS testing, output formats, tuning categories, evasion techniques, authentication, and a…
Passive vs Active Reconnaissance — 90% of Beginners Do This Wrong (2026 Hacker Guide)
Master Passive vs Active Reconnaissance for ethical hacking and bug bounty. Learn passive recon (OSINT, WHOIS, certificate transparency) vs active…
How to Use Burp Suite for Beginners (2026) — Intercept Your First Request in 15 Minutes or Less
The most practical guide on How to use Burp Suite for beginners in 2026 — learn setup, FoxyProxy configuration, certificate…
Kali Linux Day 5: John the Ripper Tutorial — Crack Hashes, /etc/shadow, ZIP & PDF Passwords (Complete Guide 2026)
Complete John the Ripper tutorial for Kali Linux — identify hashes, crack /etc/shadow with unshadow, use wordlist mode, rule-based cracking,…
Metasploit Tutorial for Beginners 2026 — First Exploit to Root Shell in Your Home Lab (Step-by-Step)
The complete Metasploit tutorial for beginners 2026 — covering msfconsole basics, finding exploits, setting payloads, Meterpreter commands, post-exploitation, and a…