Kali Linux
Master Kali Linux with step-by-step tutorials covering installation, configuration, commands, and penetration testing tools. This section includes detailed guides on wireless attacks, password cracking, reconnaissance tools, and exploitation frameworks available in Kali Linux. Learn how to set up hacking labs, use terminal commands efficiently, and perform real-world security testing using tools like Aircrack-ng, Hydra, John the Ripper, and Wireshark. Perfect for beginners and cyber security professionals looking to enhance their penetration testing skills.
110 articles
10 Best Hacking Tools in 2026 — What Every Ethical Hacker Actually Uses
The 10 best hacking tools in 2026 ranked by real-world usage — Kali Linux, Burp Suite, Metasploit, Nmap, and more.…
Kali Linux WSL2 Setup 2026 — Install, Configure & Run Tools on Windows in 10 Minutes
Complete Kali Linux WSL2 setup guide 2026 — install on Windows 11, enable WSL2, configure kex GUI, fix common errors…
Kali Linux Day 11: Aircrack-ng Tutorial 2026 — Crack WiFi Passwords & Audit WPA2 Security
Aircrack-ng tutorial in Kali Linux 2026 — capture WPA2 handshakes, run dictionary attacks, audit wireless security. Day 11 complete guide…
Kali Linux Day 10 : Metasploit Tutorial Kali Linux 2026 — msfconsole, Modules & First Exploit Complete Guide
Master Metasploit in Kali Linux 2026 — msfconsole commands, exploit modules, payloads & your first real shell. Day 10 complete…
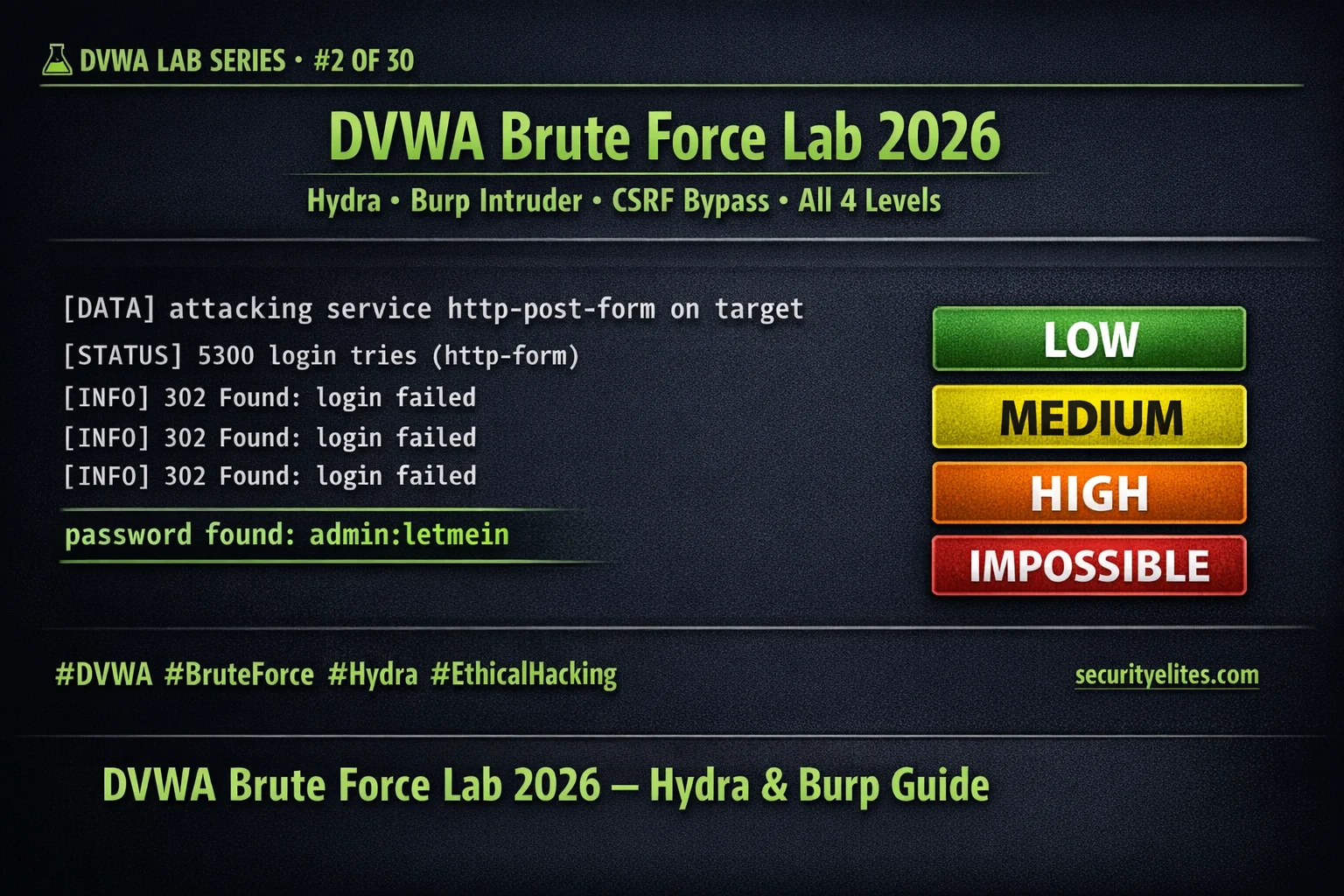
DVWA Brute Force Lab 2026 — Hydra & Burp Intruder Complete Walkthrough Day 2
Master DVWA brute force lab 2026 — Hydra credential attack, Burp Intruder, CSRF token bypass at High security & Impossible-level…
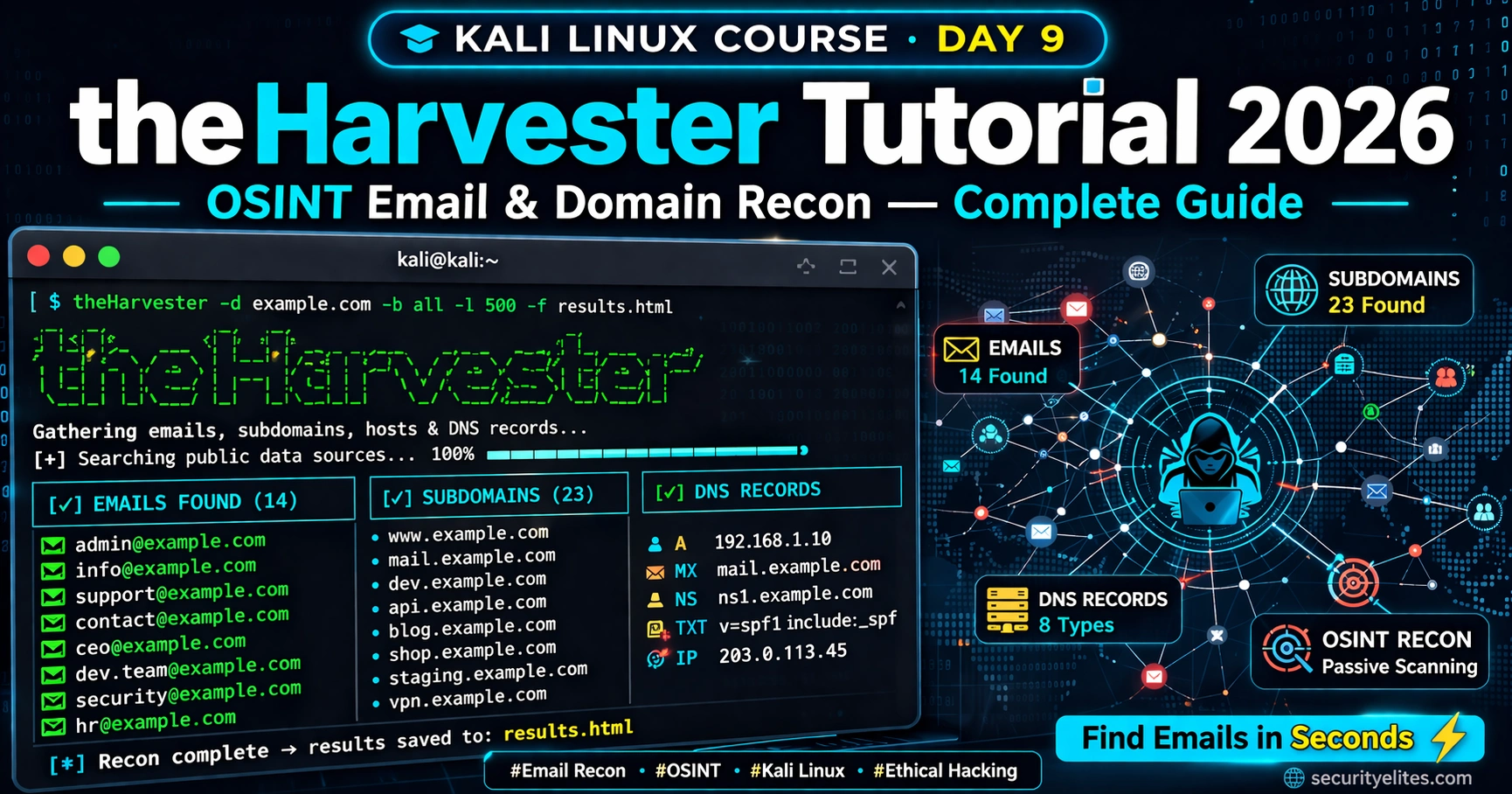
How Hackers Use theHarvester to Find Emails in Seconds (Most Don’t Know This)
Discover how hackers use theHarvester to harvest real employee emails from public sources in seconds — the OSINT technique most…
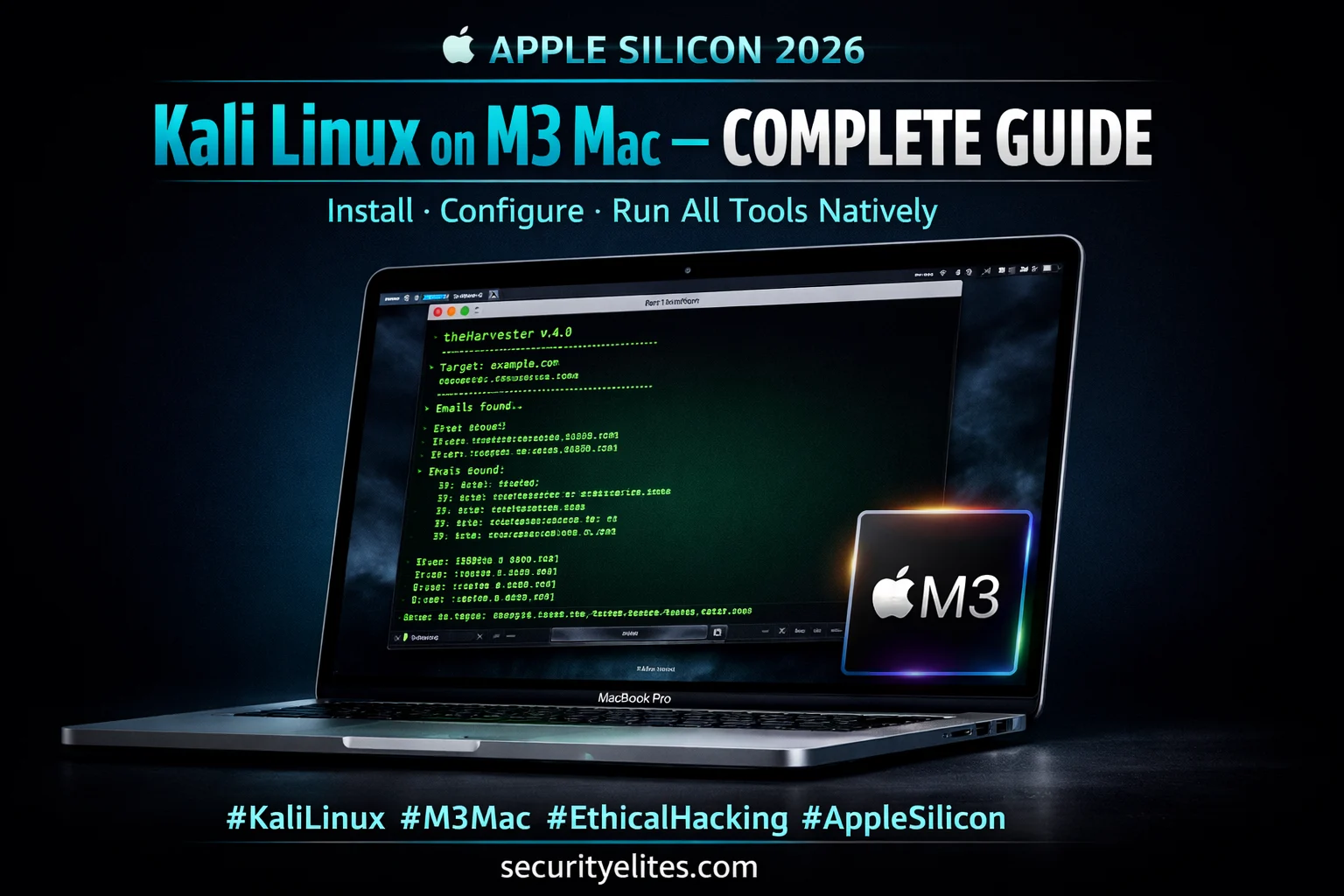
Kali Linux on M3 Mac 2026 — Ultimate Install Guide (UTM + Native Tools)
Install Kali Linux on M3 Mac 2026 — UTM VM, native ARM tools, WiFi adapter setup & full configuration guide…
Kali Linux Day 9 : theHarvester Tutorial 2026 — OSINT Email & Domain Recon Complete Guide
Master theHarvester in Kali Linux 2026 — collect emails, subdomains & DNS records for OSINT recon. Complete Day 9 guide…
Cloud Security Hacking 2026 — How Attackers Exploit AWS, Azure & GCP (Ethical Hacker’s Guide)
Cloud security hacking is the highest-demand offensive skill of 2026. Learn IAM misconfiguration exploitation, S3 bucket attacks, SSRF to cloud…