Kali Linux
Master Kali Linux with step-by-step tutorials covering installation, configuration, commands, and penetration testing tools. This section includes detailed guides on wireless attacks, password cracking, reconnaissance tools, and exploitation frameworks available in Kali Linux. Learn how to set up hacking labs, use terminal commands efficiently, and perform real-world security testing using tools like Aircrack-ng, Hydra, John the Ripper, and Wireshark. Perfect for beginners and cyber security professionals looking to enhance their penetration testing skills.
110 articles
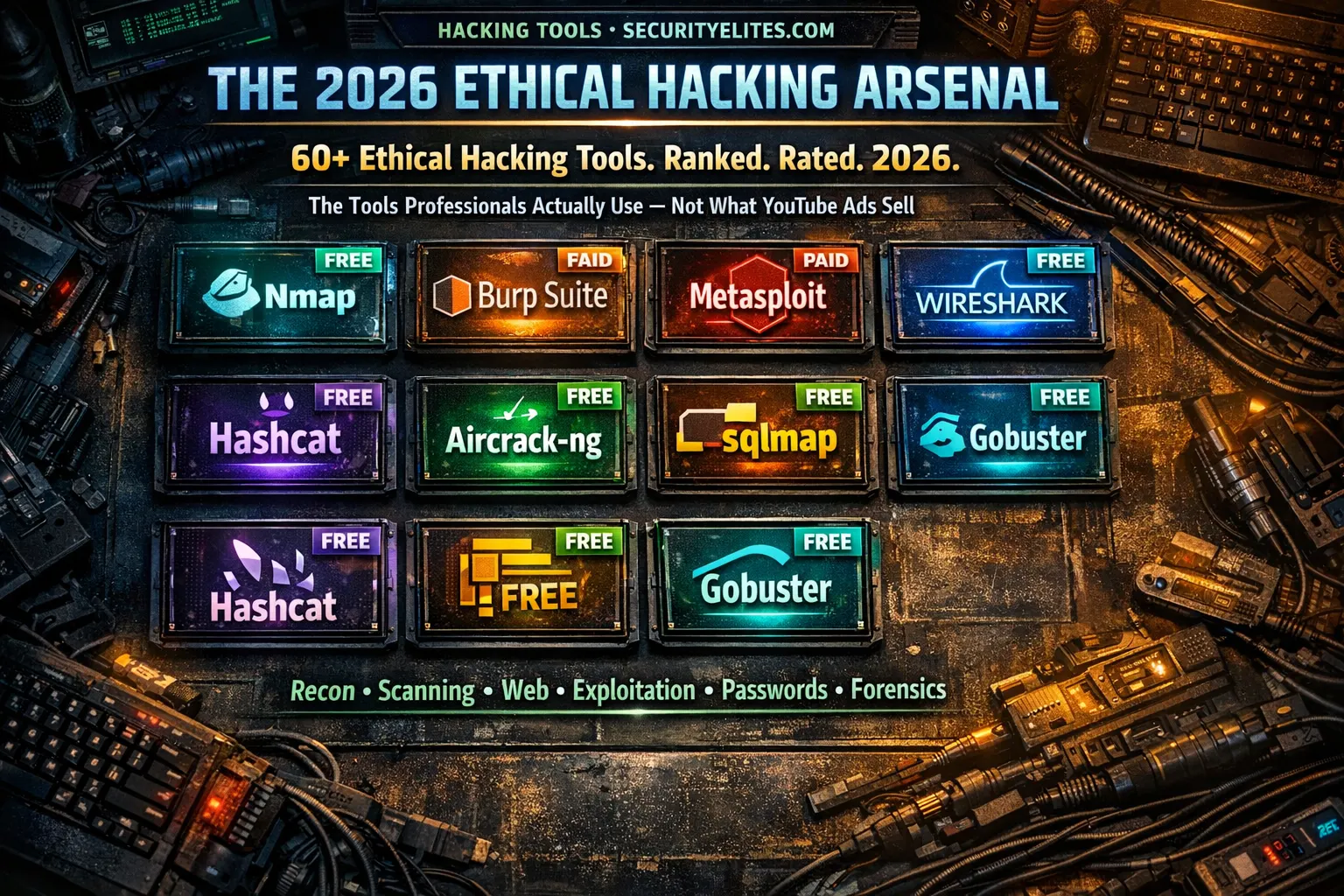
Ethical Hacking Tools List 2026 — Every Tool Professionals Actually Use (Free + Paid, Ranked by Category)
The most complete ethical hacking tools list for 2026 — 60+ tools across 10 categories with honest tier ratings, free…
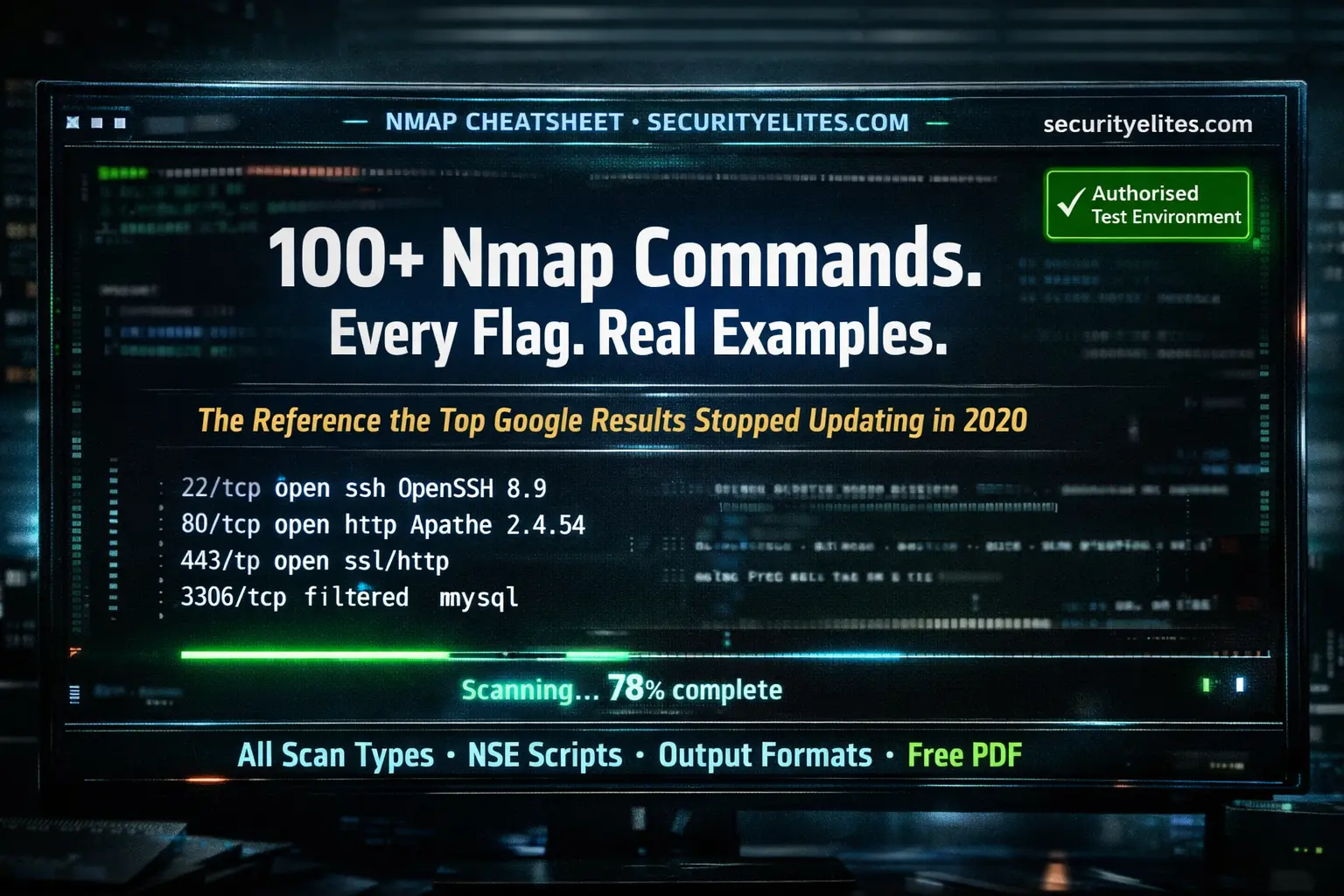
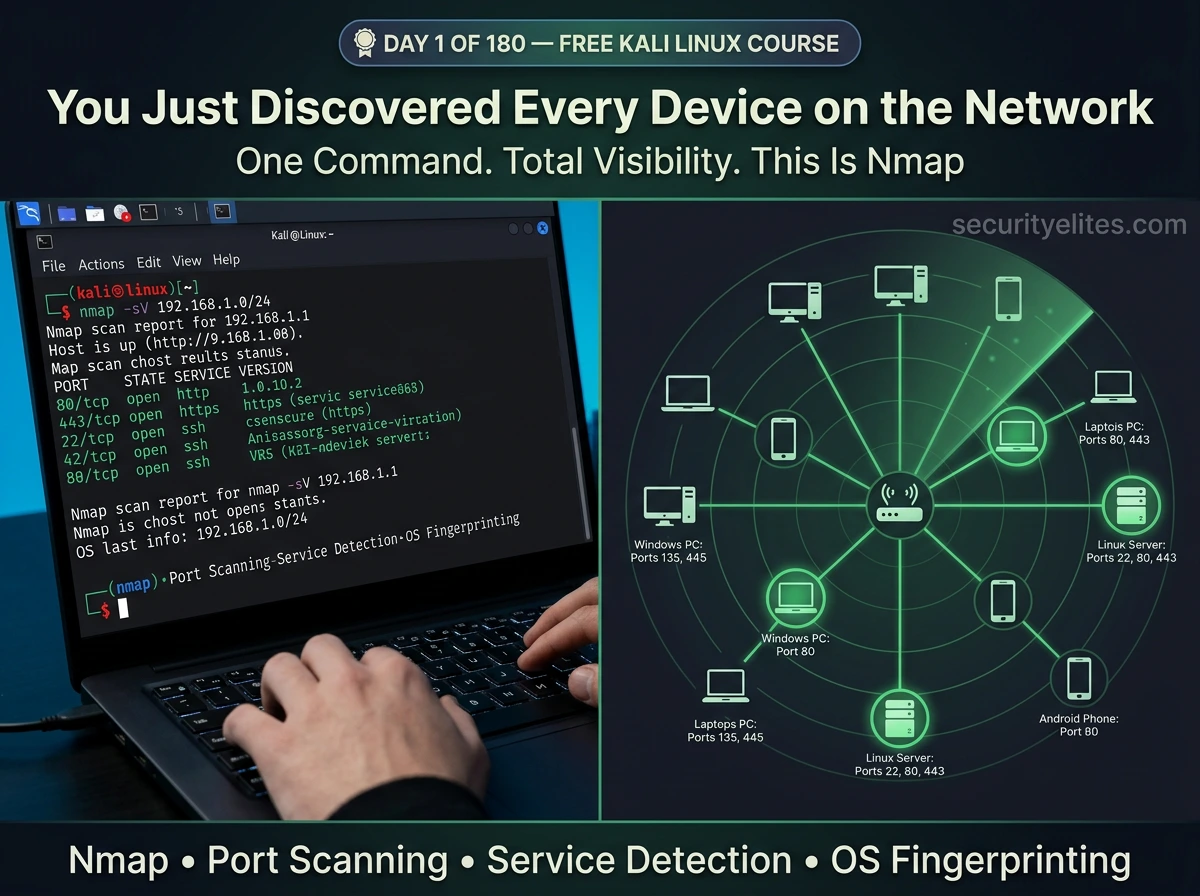
Nmap Commands with Examples 2026 — The Complete Reference (Every Flag, Every Scan Type, Free PDF Cheat Sheet)
Every Nmap commands with examples — covering all scan types, timing options, output formats, NSE scripts, firewall evasion techniques, and…
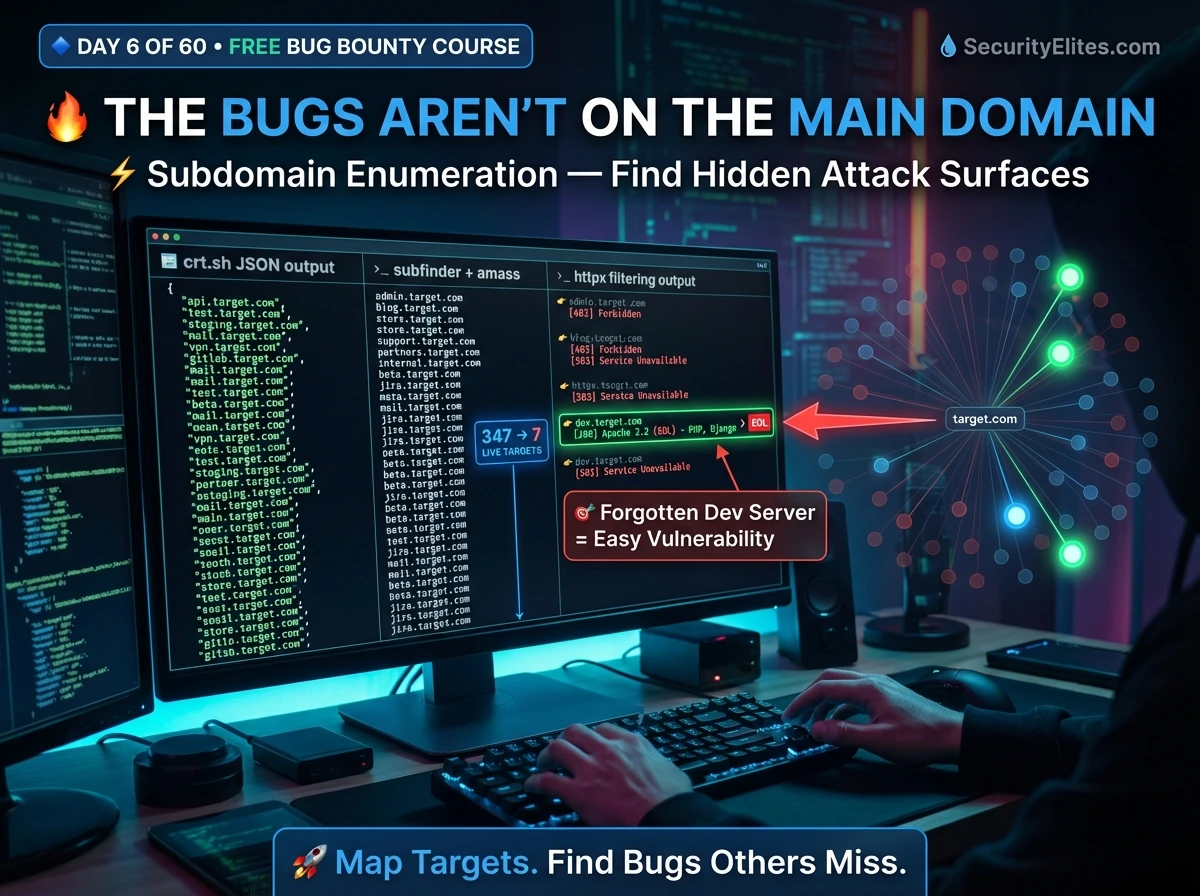
Bug Bounty Day 6: Subdomain Enumeration — Build Your Full Attack Surface Map (2026)
Master subdomain enumeration for bug bounty — Subfinder, Amass, crt.sh, httpx live filtering, ffuf directory fuzzing, and building a professional…
How to Practice Ethical Hacking Legally at Home 2026 — Build Your Own Hacking Lab (Free & Legal)
The complete guide to building a free, legal ethical hacking home lab for practice ethical hacking legally at home in…
Kali Linux Day 3: Gobuster Tutorial — Find Hidden Directories, Files & Subdomains (Complete Beginner Guide 2026)
Complete Gobuster tutorial for Kali Linux — dir mode, dns mode, vhost mode, wordlists, status code filtering, file extension discovery,…
Kali Linux Commands Cheat Sheet 2026 — 200+ Commands with Examples (The Only Reference You’ll Ever Need)
The most comprehensive Kali Linux commands cheat sheet 2026 — 200+ commands across 10 categories with real examples. Networking, scanning,…
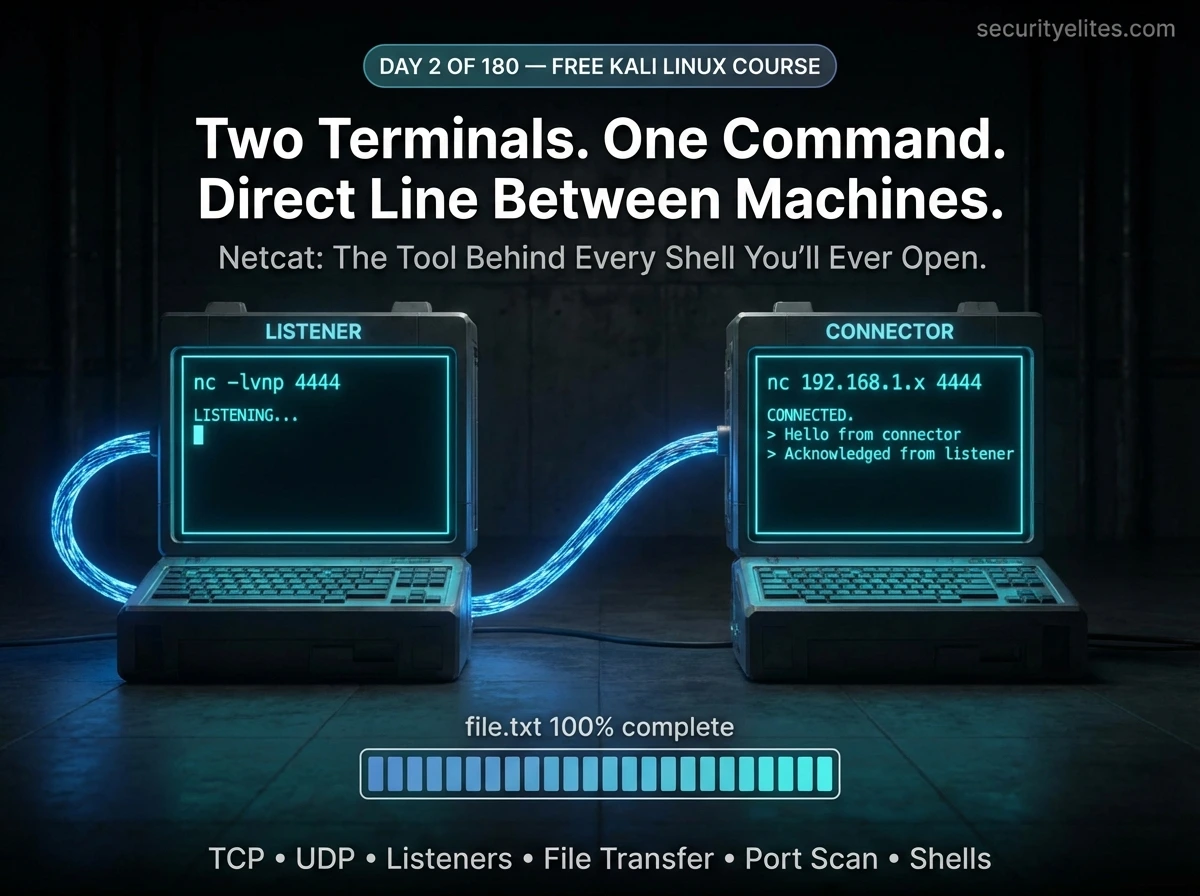
Day 2: Netcat Tutorial for Beginners — Master the Swiss Army Knife of Networking in Kali Linux (2026)
Day 2 of 180. Netcat tutorial from scratch — make TCP/UDP connections, transfer files, set up listeners, perform port scanning,…
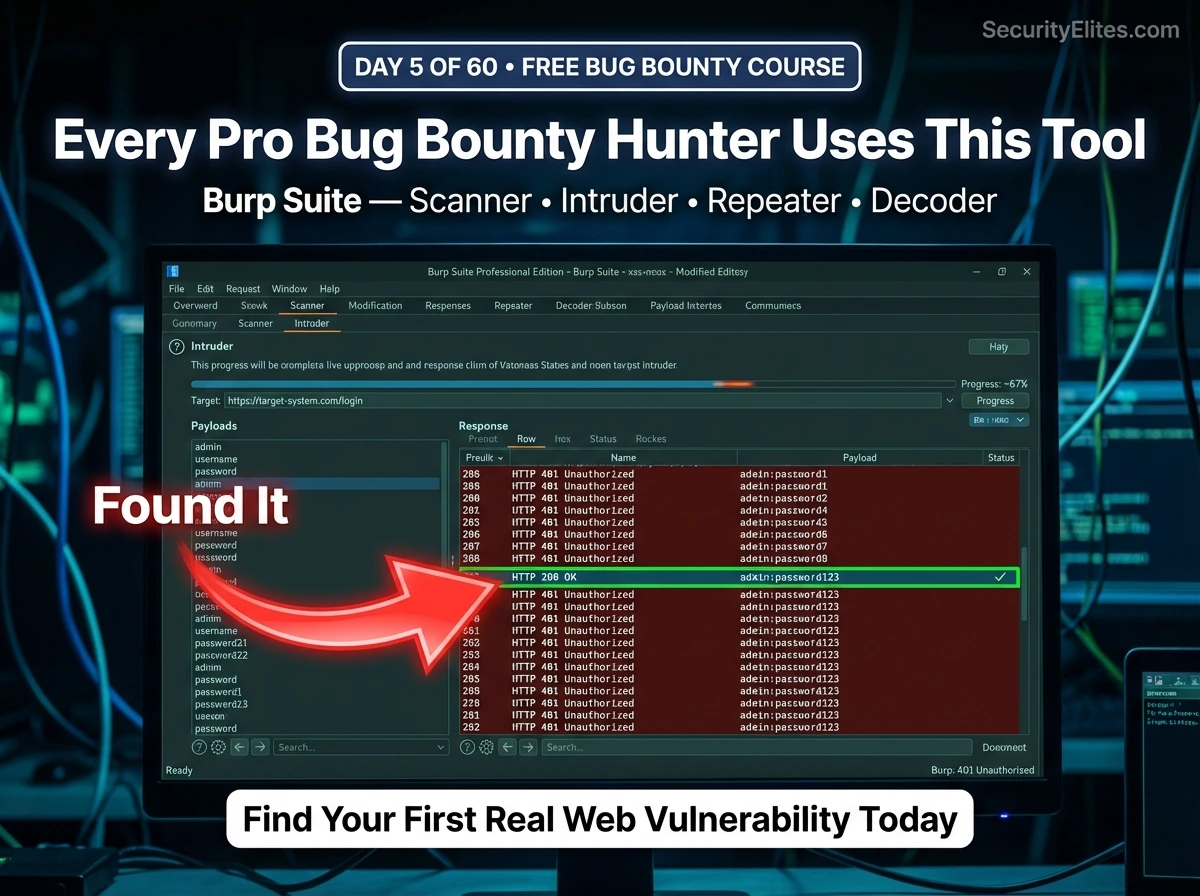
Day 5: Burp Suite Deep Dive for Beginners — Scanner, Intruder, Decoder & Your First Real Vulnerability Test (2026)
Day 5 of 60. Burp Suite Deep Dive from scratch — Scanner, Intruder, Repeater, Decoder, and Comparer. Learn how to…
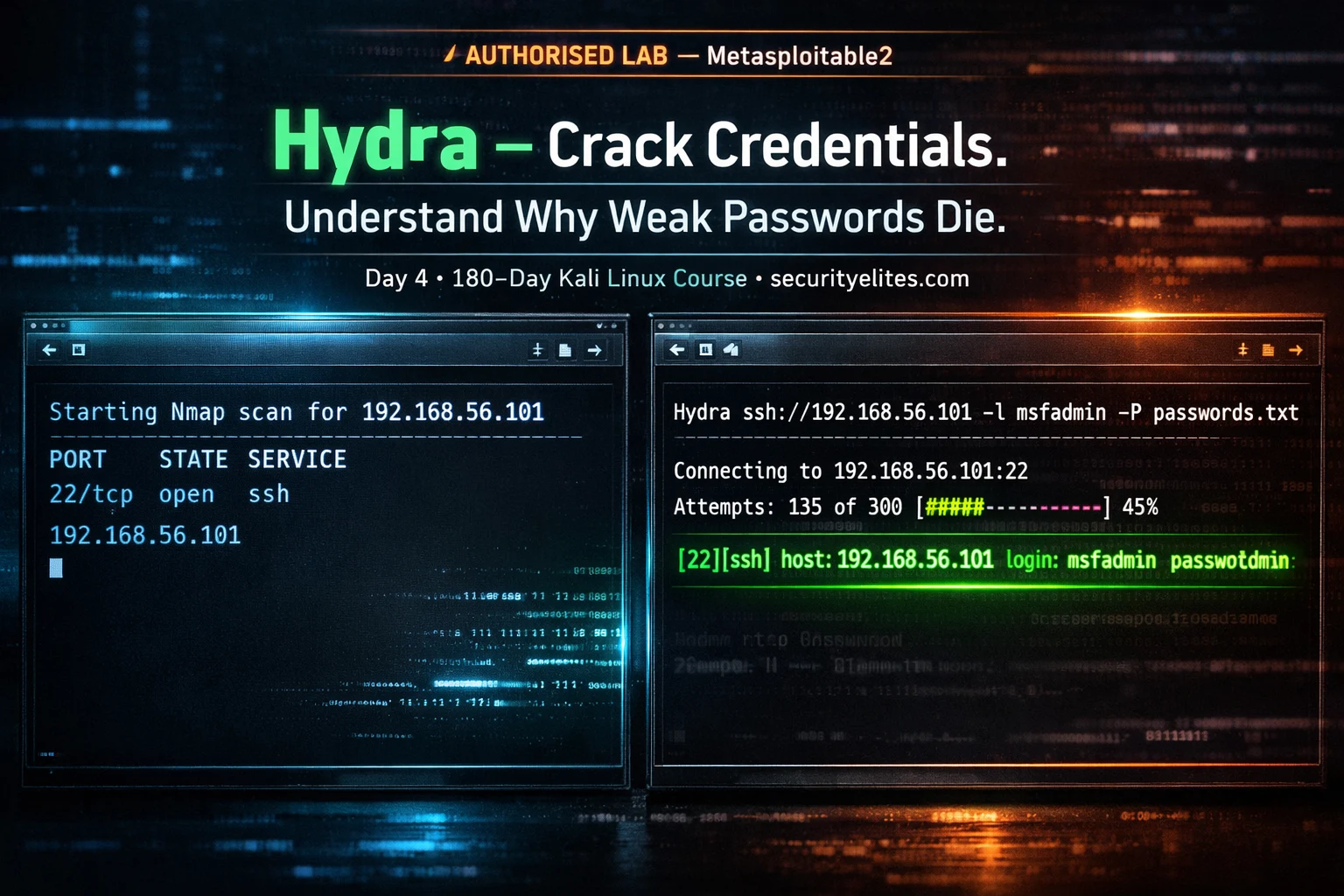
Day 1: Nmap Tutorial for Beginners — How to Scan Any Network Like a Pro in Kali Linux (2026)
Day 1 of 180. Nmap tutorial from absolute zero—install, run your first scan, understand every flag, read results like a…