FREE
Part of the DVWA Lab Series — 30 Labs
🎯 What You’ll Learn in Lab 18
⏱️ 40 min · 3 exercises
✅ Prerequisites
- Lab 6: File Upload basics — Low security webshell upload understood
- Lab 14: Security Levels — comfortable reading PHP source
- Burp Suite configured with browser proxy
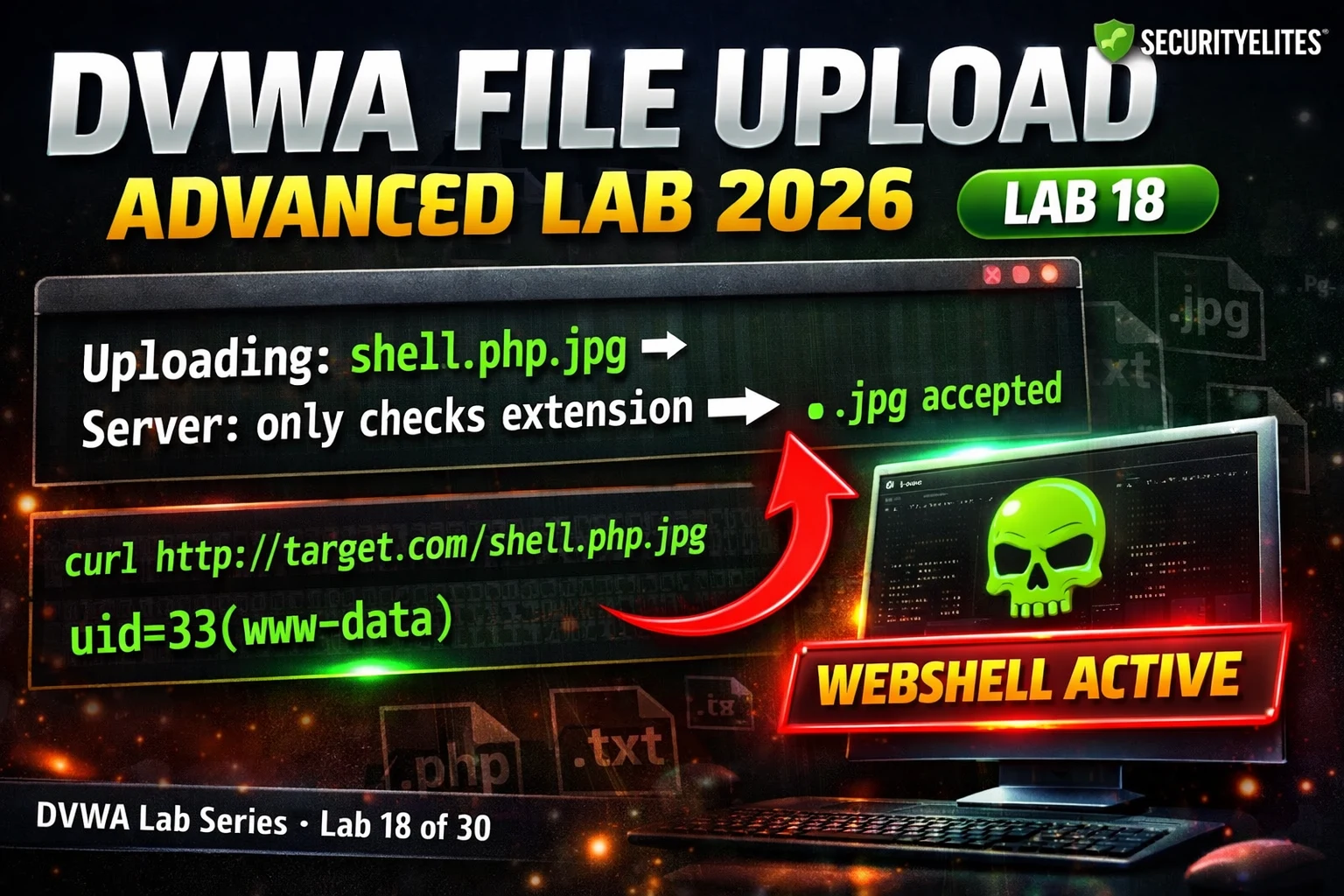
📋 DVWA File Upload Advanced Lab 18 Contents — Upload Filter Bypass
In Lab 6 you uploaded a PHP webshell at Low security. Lab 18 builds directly on that — same goal (PHP execution), different obstacles. The same source code reading methodology from Lab 14 applies: check the filter logic first, identify the gap, apply the specific bypass. The DVWA Lab Series teaches technique recognition, not just exploit execution.
Medium Security — MIME Spoofing Bypass
⏱️ Time: 12 minutes · DVWA Medium · Burp Suite active
📸 Screenshot the Burp Content-Type modification and the webshell RCE output. Share in #dvwa-labs on Discord.
High Security — .htaccess Upload and Magic Bytes
High security adds two additional checks: getimagesize() which validates that the file has valid image dimensions (checking magic bytes), and an extension whitelist that only accepts .jpg, .jpeg, and .png. The getimagesize() check can be bypassed by prepending valid image magic bytes to the PHP webshell. The extension check can be bypassed by uploading an .htaccess file (if the server accepts it) that redefines how certain extensions are executed.
⏱️ Time: 15 minutes · DVWA High security · Burp Suite
📸 Screenshot the .htaccess upload success and webshell execution with magic bytes. Share in #dvwa-labs on Discord.
Executing the Webshell After Upload
⏱️ Time: 10 minutes · DVWA · all three security levels
📸 Screenshot RCE from all three security levels and share in #dvwa-labs on Discord. Tag #fileupload2026
🧠 QUICK CHECK — Lab 18
📋 Lab 18 Upload Bypass Reference
🏆 Mark Lab 18 as Complete
Lab 18 completes the file upload bypass series — Low through High all bypassed, each using a technique matched to the specific filter gap. The pattern is consistent: read the source, find the unchecked dimension, use the bypass that targets that specific gap. Lab 19 moves to XSS cookie theft — advanced cross-site scripting for session hijacking.
❓ Frequently Asked Questions
What does Medium security check?
What does High security check?
What is a double extension bypass?
What is magic byte injection?
What comes after Lab 18?
Lab 17: File Inclusion Advanced
Lab 19: XSS Cookie Theft Advanced
📚 Further Reading
- DVWA File Upload Lab 2026 — Lab 6 covers basic webshell upload at Low security — the foundation Lab 18 extends to Medium and High bypass techniques.
- File Upload Vulnerabilities Hub — SecurityElites complete file upload security category — real-world bypass techniques, CVE examples, and secure implementation patterns for production applications.
- DVWA Labs Hub — All 30 DVWA labs — Lab 18 at 60% completion marks the beginning of the advanced techniques phase of the series.
- PortSwigger File Upload Labs — Interactive file upload bypass labs including remote code execution via extension manipulation, .htaccess upload, and polyglot file attacks — real-world complexity beyond DVWA.
- OWASP Unrestricted File Upload — OWASP’s complete file upload vulnerability reference — all bypass categories, real CVE examples, and the definitive secure file upload implementation guidance.