FREE
Part of the DVWA Lab Series — 30 Labs
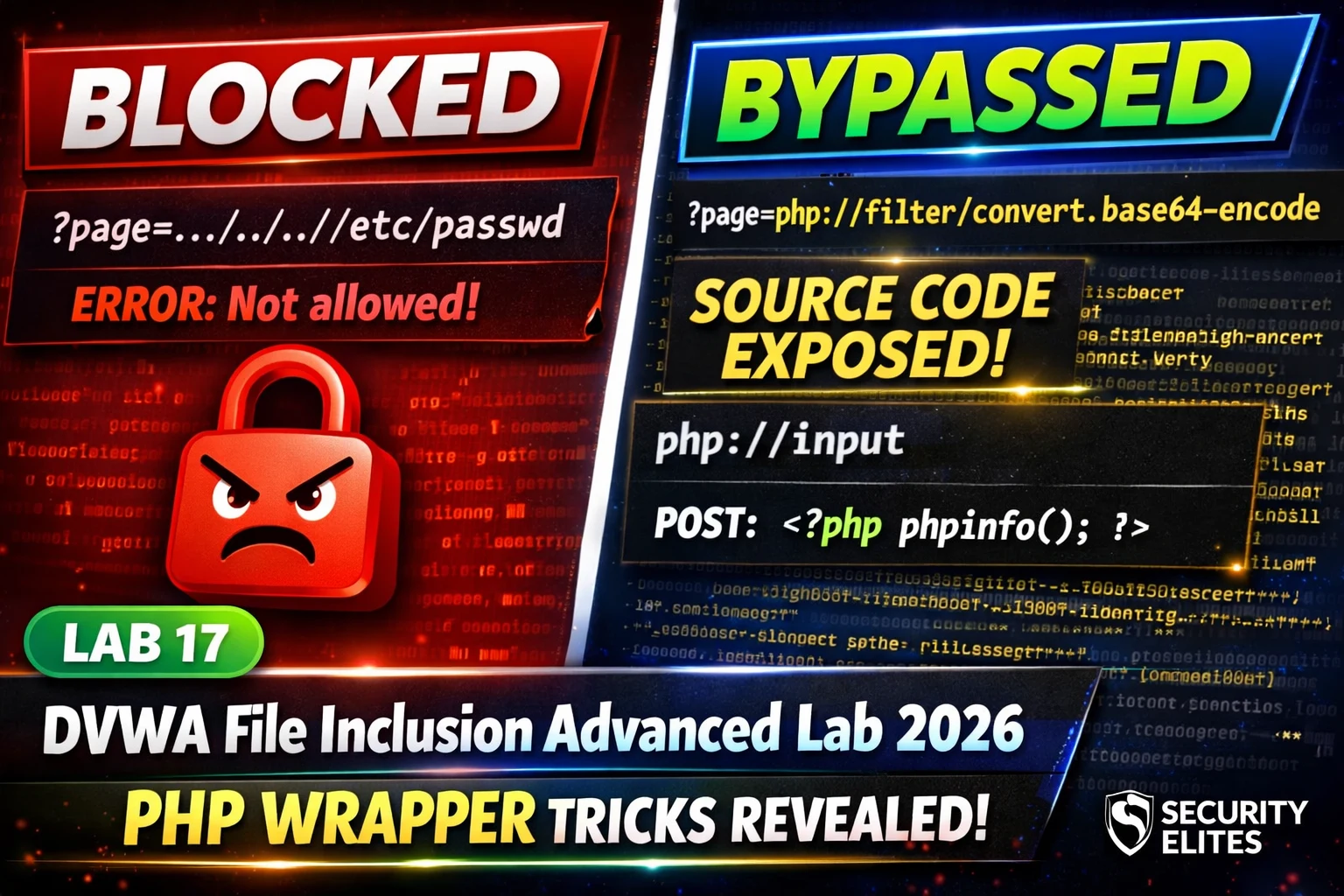
../ sequences. High security extends that filter further. Neither level blocks PHP’s built-in protocol wrappers — and those wrappers do not use path traversal at all. php://filter reads and encodes source code. php://input executes code from your POST body. data:// includes inline content. None of these need ../. The filter blocks what it knows about. These wrappers are something different entirely.🎯 What You’ll Learn in Lab 17
⏱️ 40 min · 3 DVWA exercises
✅ Prerequisites
- Lab 5: File Inclusion basics — Low security LFI understood
- Lab 14: Security Levels — comfortable reading PHP source
- DVWA running locally (Lab 1: Setup)
📋 DVWA File Inclusion Advanced Lab 17 Contents — PHP Wrapper Bypasses
In Lab 5 you read /etc/passwd using ../../../ path traversal at Low security. Lab 17 applies the same wrapper bypass philosophy as Lab 16’s command injection filter bypass — blacklists block known strings, not equivalent alternatives. The DVWA Lab Series shows this pattern across every vulnerability type.
Medium Security — What the Filter Strips
⏱️ Time: 15 minutes · DVWA Medium security
📸 Screenshot the base64-encoded output and decoded source code. Share in #dvwa-labs on Discord.
php://input — LFI to RCE
The php://input wrapper reads the raw POST request body. When used as the file parameter in an include() call, if PHP’s allow_url_include=On is set (which is DVWA’s intentional misconfiguration at Low and Medium security), the application includes the POST body as PHP code and executes it. This converts an LFI into Remote Code Execution.
⏱️ Time: 12 minutes · DVWA Medium · Burp Suite or curl
📸 Screenshot phpinfo() execution via php://input proving RCE. Share in #dvwa-labs on Discord.
High Security — Extended Blacklist and Remaining Bypasses
⏱️ Time: 12 minutes · DVWA High security
📸 Screenshot file:// bypass working at High security reading /etc/passwd. Share in #dvwa-labs on Discord. Tag #lfiwrapper2026
🧠 QUICK CHECK — Lab 17
📋 Lab 17 PHP Wrapper Reference
🏆 Mark Lab 17 as Complete
PHP protocol wrappers transform a basic LFI into source code disclosure, credential extraction, and code execution. The same blacklist-fails pattern from command injection (Lab 16) appears here in file inclusion — PHP’s wrapper ecosystem is richer than any blacklist can cover. Lab 18 applies the same principle to file upload filters.
❓ Frequently Asked Questions
What is php://filter?
What is php://input?
What is the difference between LFI and RFI?
What comes after Lab 17?
Lab 16: Command Injection Advanced
Lab 18: File Upload Advanced
📚 Further Reading
- DVWA File Inclusion Lab 2026 — Lab 5 covers basic LFI at Low security — the foundation that Lab 17 extends to advanced wrapper bypasses.
- DVWA Command Injection Advanced 2026 — Lab 16 covers the same blacklist bypass principle applied to command injection — the pattern repeats across vulnerability types.
- DVWA Labs Hub — All 30 DVWA labs — Lab 17 php wrapper techniques apply directly to the SQL injection and XSS advanced labs ahead in the series.
- PortSwigger File Path Traversal Labs — Interactive file path traversal labs including filter bypass techniques — the real-world application of the DVWA wrapper bypasses in complex web application contexts.
- PHP Official Wrapper Documentation — Complete PHP wrapper reference — all supported protocols and filters including php://, file://, data://, zip://, and more — the full attacker toolkit for LFI exploitation.