Bug Bounty Hunting
Start your bug bounty hunting journey with complete beginner-to-advanced tutorials on finding and reporting vulnerabilities. Learn reconnaissance techniques, subdomain enumeration, Google dorking, automation tools, and vulnerability validation methods used by top bug bounty hunters. This section also includes real bug bounty case studies, report writing tips, and platform guides like HackerOne and Bugcrowd to help you earn rewards by ethically reporting security flaws.
89 articles
Google Bug Bounty Program — How Ethical Hackers Legally Earn $100–$31,337 Finding Gmail Vulnerabilities (2026)
Learn how ethical hackers legally earn $100 to $31,337 through Google's Vulnerability Reward Program aka Google Bug Bounty Program. Scope,…
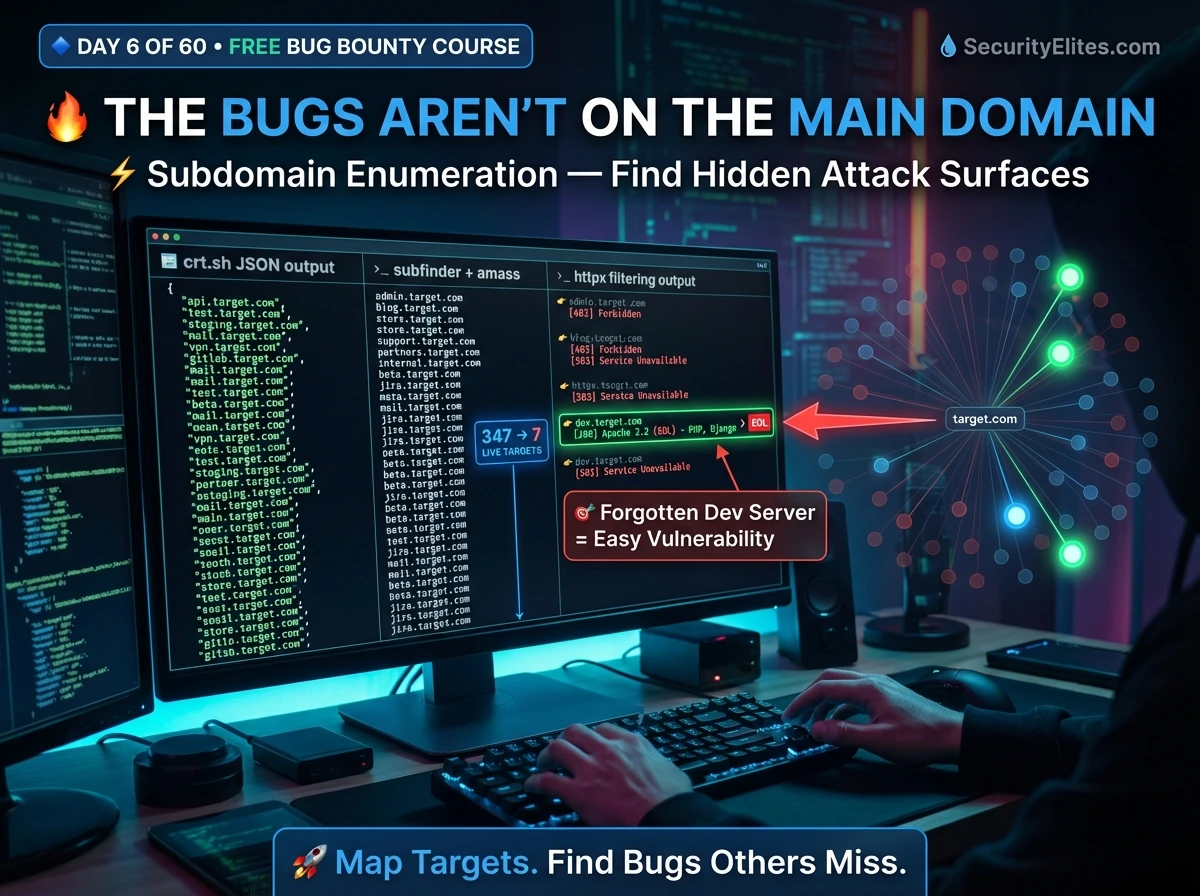
Bug Bounty Day 6: Subdomain Enumeration — Build Your Full Attack Surface Map (2026)
Master subdomain enumeration for bug bounty — Subfinder, Amass, crt.sh, httpx live filtering, ffuf directory fuzzing, and building a professional…
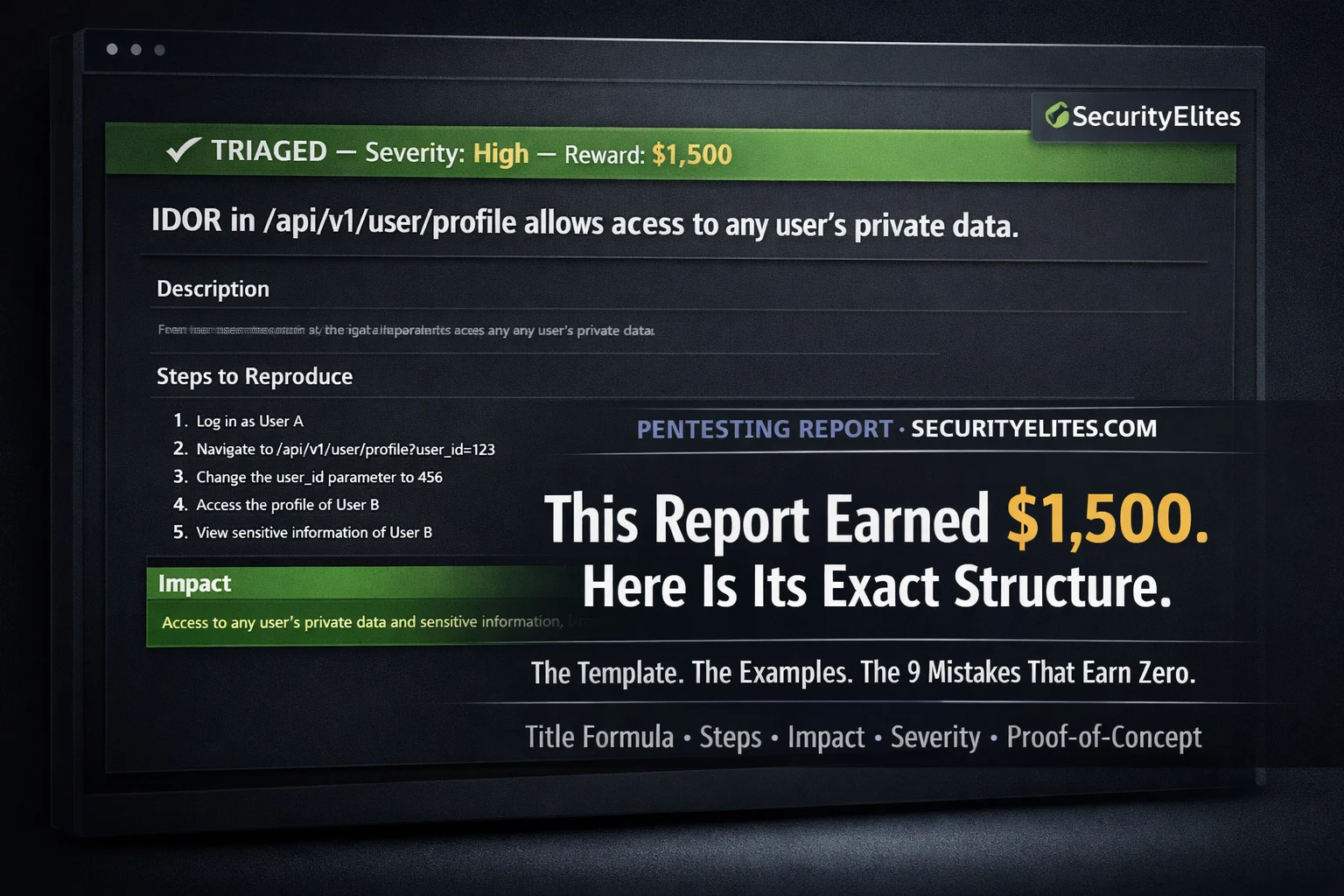
Bug Bounty Hunting for Beginners — The Complete Step-by-Step Guide From Zero to First Paid Finding (2026)
The most completeguide on bug bounty hunting for beginners 2026 — platform setup, reconnaissance, vulnerability testing, professional report writing, and…
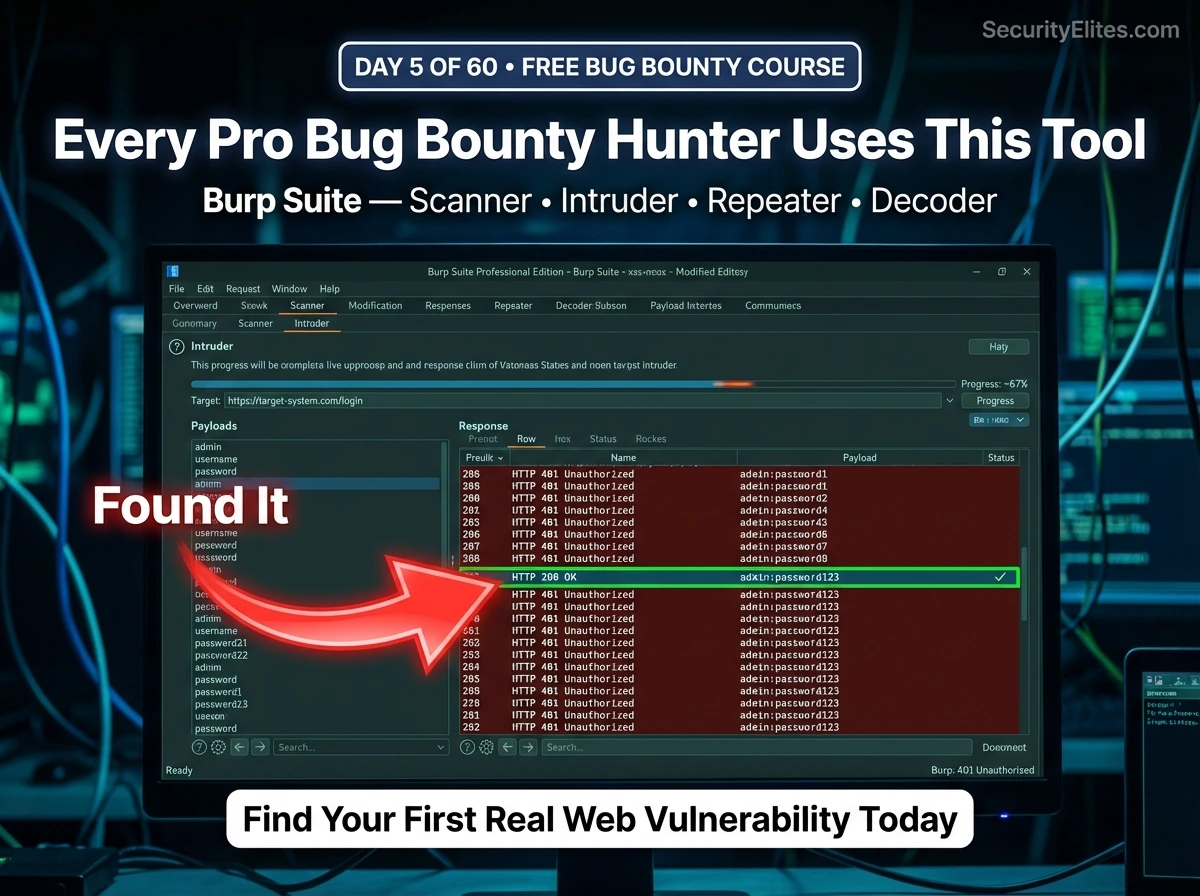
Day 5: Burp Suite Deep Dive for Beginners — Scanner, Intruder, Decoder & Your First Real Vulnerability Test (2026)
Day 5 of 60. Burp Suite Deep Dive from scratch — Scanner, Intruder, Repeater, Decoder, and Comparer. Learn how to…
How to Become an Ethical Hacker With No Experience in 2026 — The Honest Roadmap Nobody Else Will Give You
No degree. No IT background. No budget. Here is the exact month-by-month roadmap of how to become an ethical hacker…
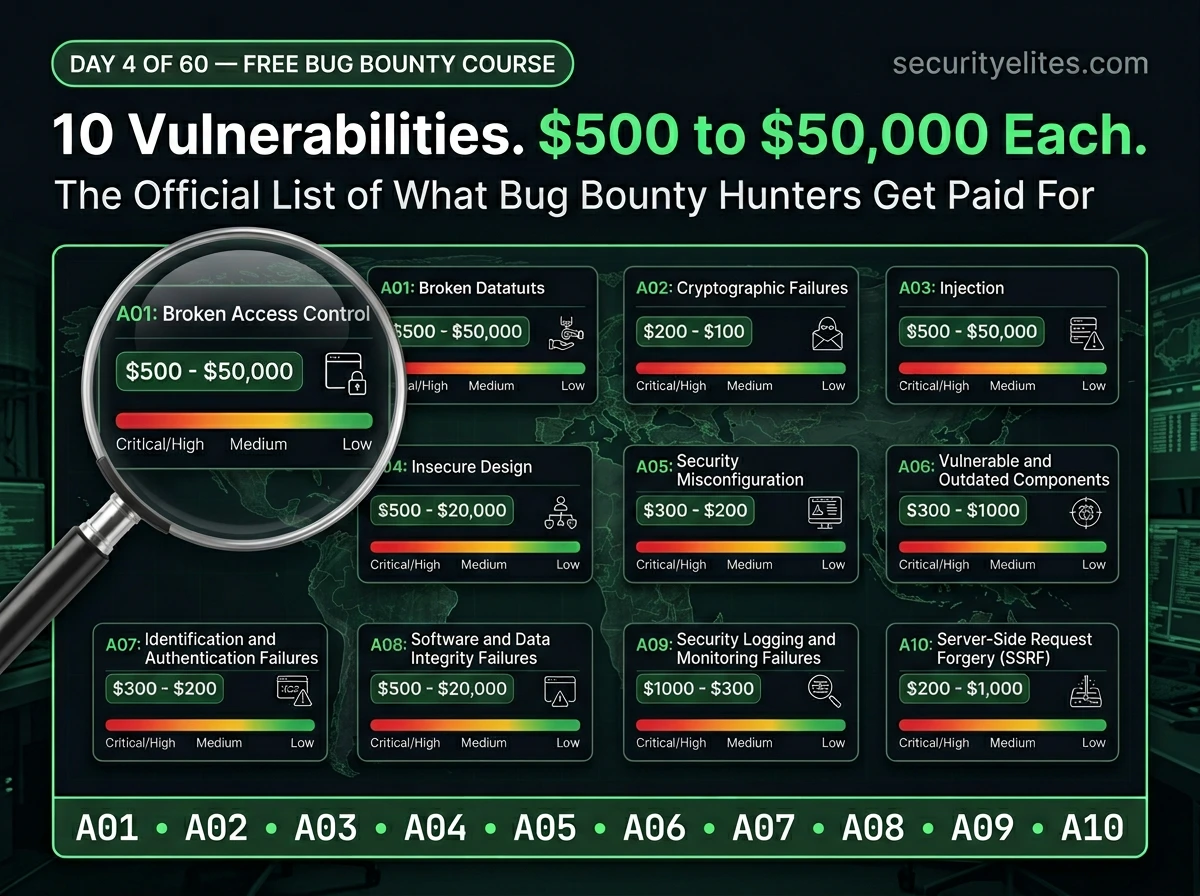
Day 4: OWASP Top 10 Explained — The Official Bug Bounty Vulnerability Map Every Hunter Needs (2026)
Day 4 of 60. Learn the OWASP Top 10 in plain English — what each vulnerability is, how it’s exploited,…
Instagram Bug Bounty — How Ethical Hackers Legally Earn $500–$30,000 Finding Instagram Vulnerabilities (2026)
Learn how ethical hackers legally earn $500 to $30,000 through Meta's Instagram bug bounty program on Bugcrowd. Explore scope, payouts,…
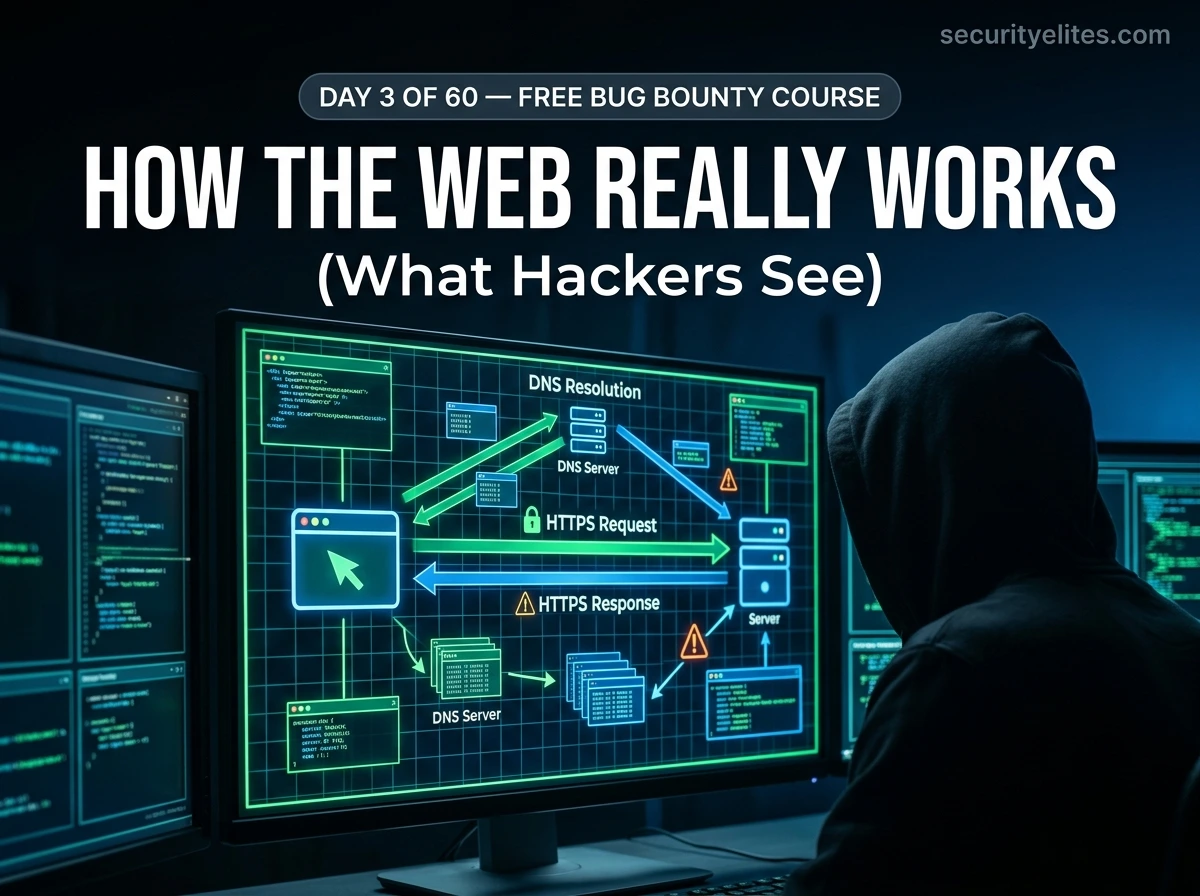
Day 3: How the Web Works — HTTP, DNS & the Request-Response Cycle Every Bug Bounty Hunter Must Understand (2026)
Day 3 of 60. Learn how http works for beginners in bug bounty — HTTP methods, DNS, status codes, cookies…
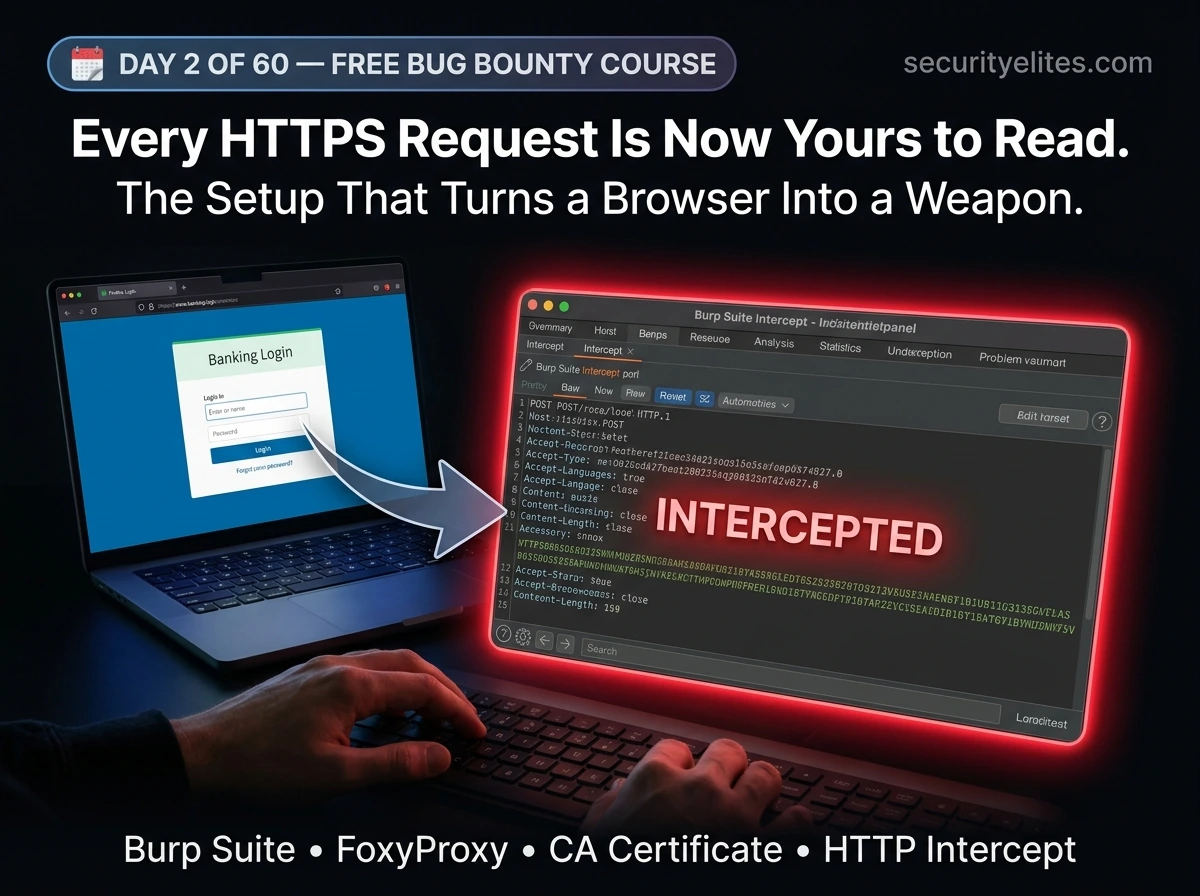
Day 2: Setting Up Your Bug Bounty Hacking Lab — Burp Suite, Firefox & Your First Intercepted HTTP Request (2026)
Day 2 of 60. Set up your complete bug bounty hacking lab — Burp Suite setup for Bug Bounty for…