Cyber Security Tools
Discover the most powerful cyber security tools and ethical hacking tools used by penetration testers and security researchers. This category features detailed tutorials, installation guides, and usage walkthroughs for reconnaissance, exploitation, OSINT, wireless testing, and password cracking tools. Explore both free and premium security tools, compare their features, and learn how to use them effectively in real penetration testing scenarios.
81 articles
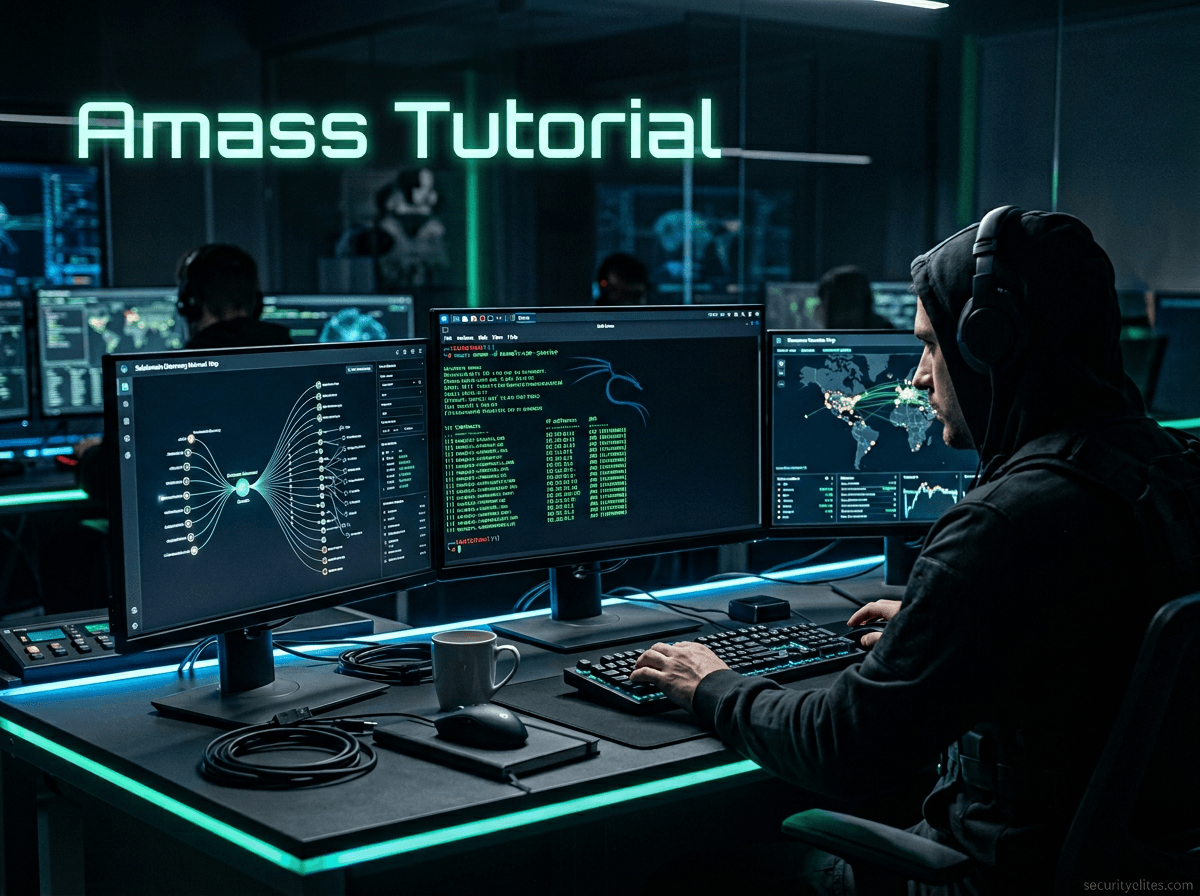
Information Gathering Using Kali Linux Day 8: Attack Surface Mapping with Amass
Information Gathering Using Kali Linux Day 8 - Learn Information Gathering using Kali Linux with Amass step-by-step. Discover hidden domains…
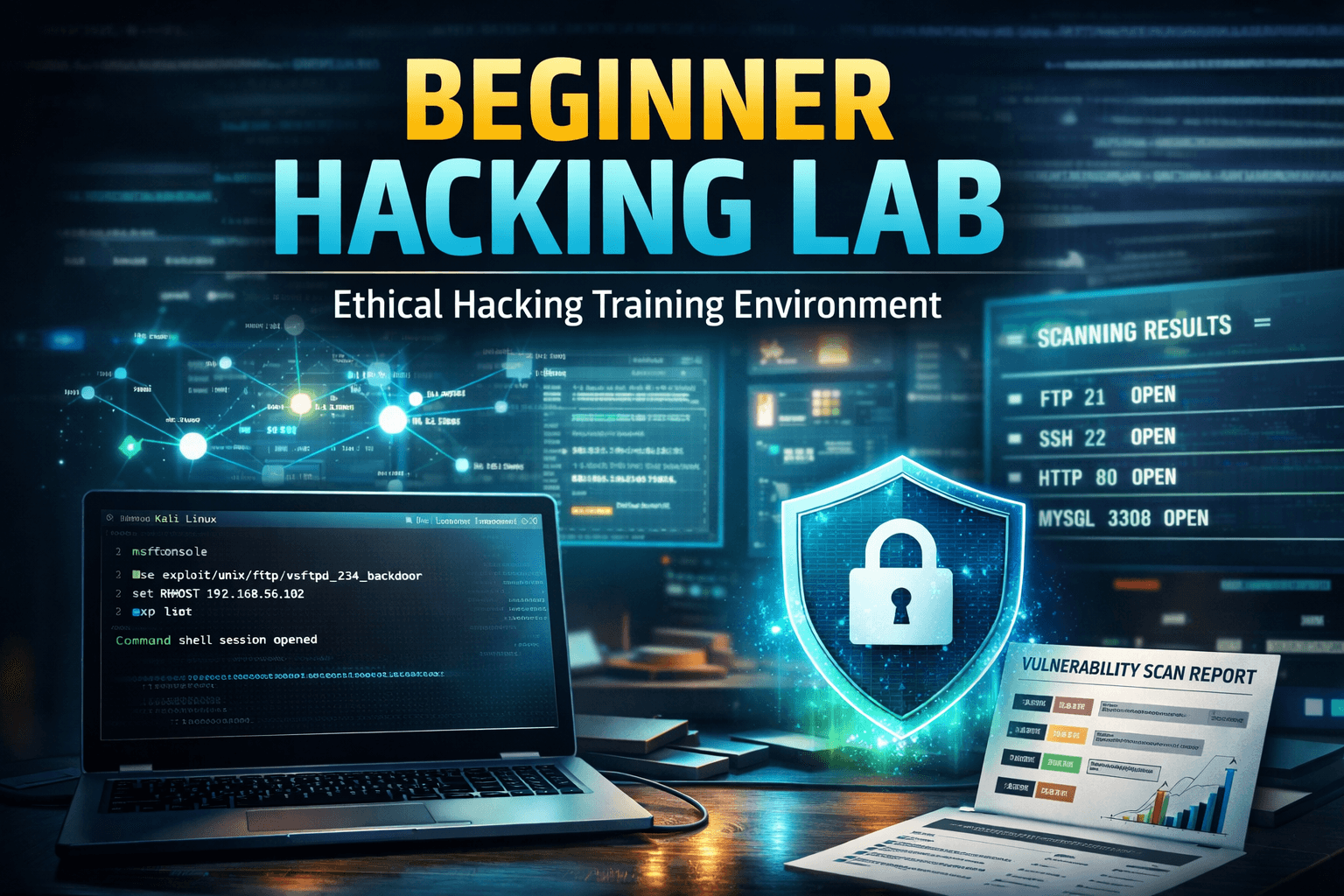
Beginner Exploitation Guide: 10 Ethical Hacking Techniques Every Pentester Should Know
Learn exploitation in ethical hacking with this beginner exploitation guide. Includes penetration testing labs, attacker mindset, and Metasploit tutorial.
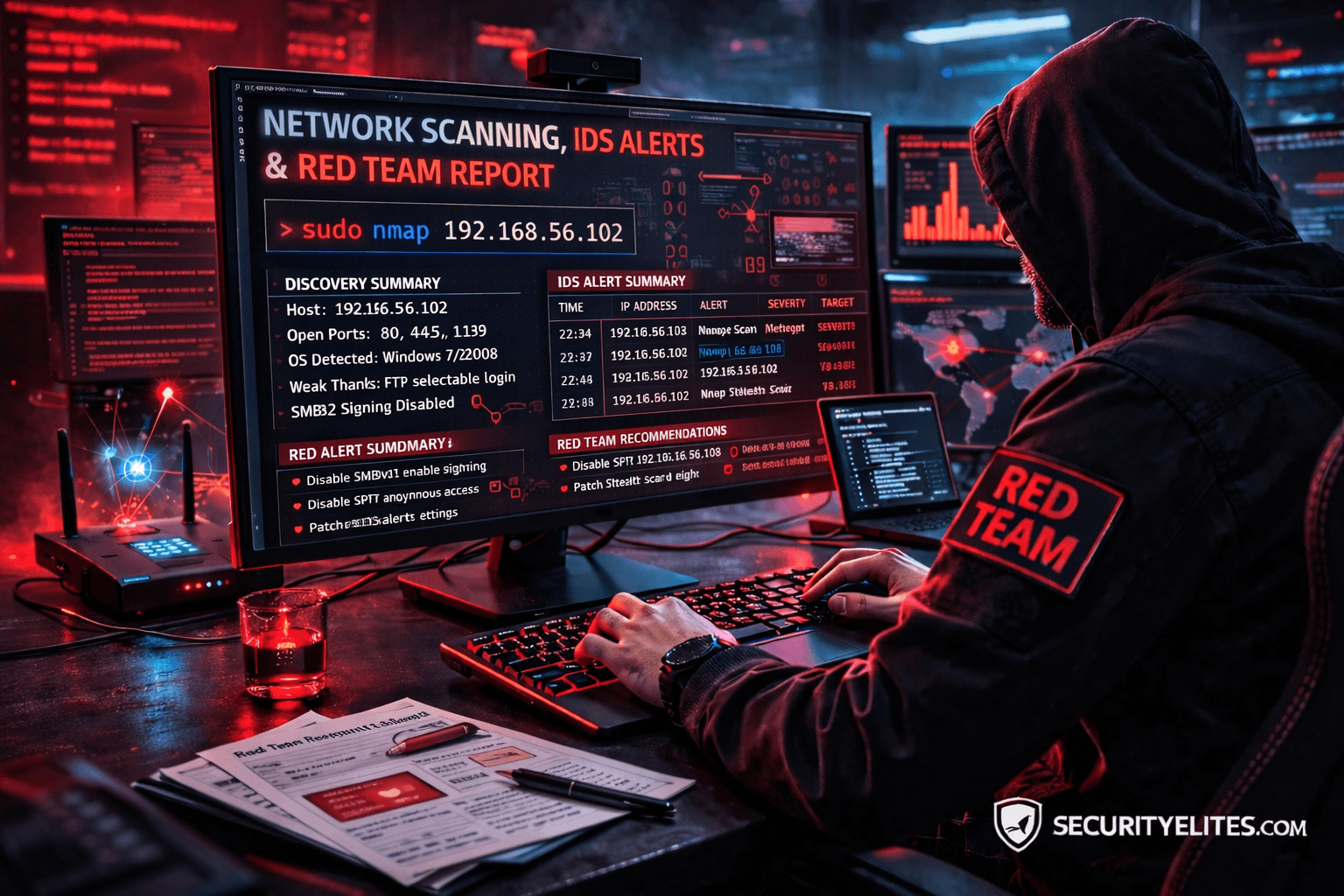
Network Scanning Tutorial Using Nmap Day 7 — Stealth Scanning, IDS Evasion & Red Team Techniques
Network Scanning Tutorial Using Nmap Day 7 - Learn stealth scanning, IDS evasion, and advanced Red Team Nmap techniques used…
20 AI Penetration Testing Tools Ethical Hackers Use (Kali Linux Guide)
Discover 20 AI penetration testing tools ethical hackers use. Learn how AI automates reconnaissance, vulnerability discovery, and cybersecurity testing.
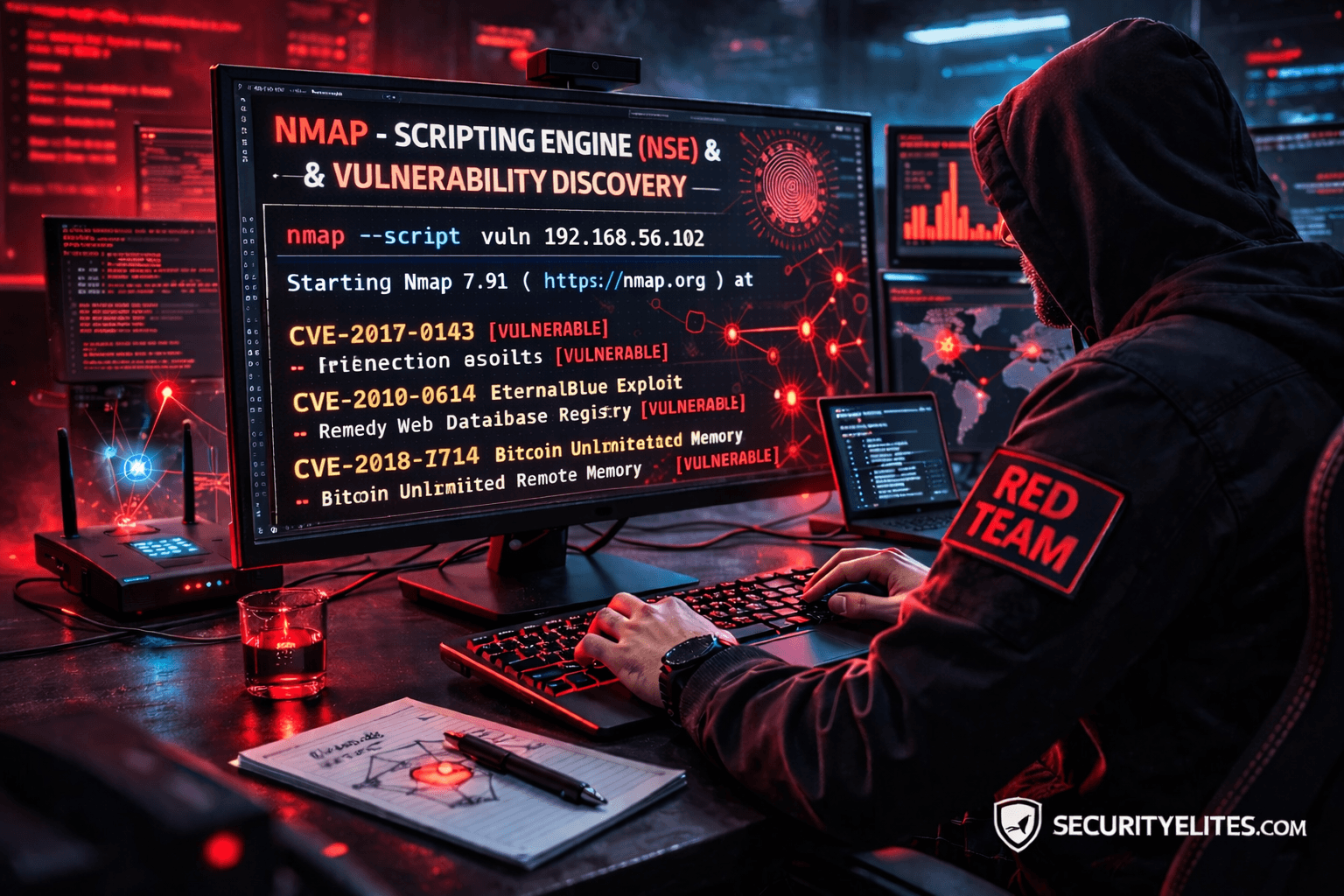
Network Scanning Tutorial Using Nmap Day 6— Nmap Scripting Engine (NSE) & Vulnerability Discovery
Network Scanning Tutorial Using Nmap Day 6 - Learn Nmap Scripting Engine (NSE) for vulnerability discovery and automated reconnaissance. Day…
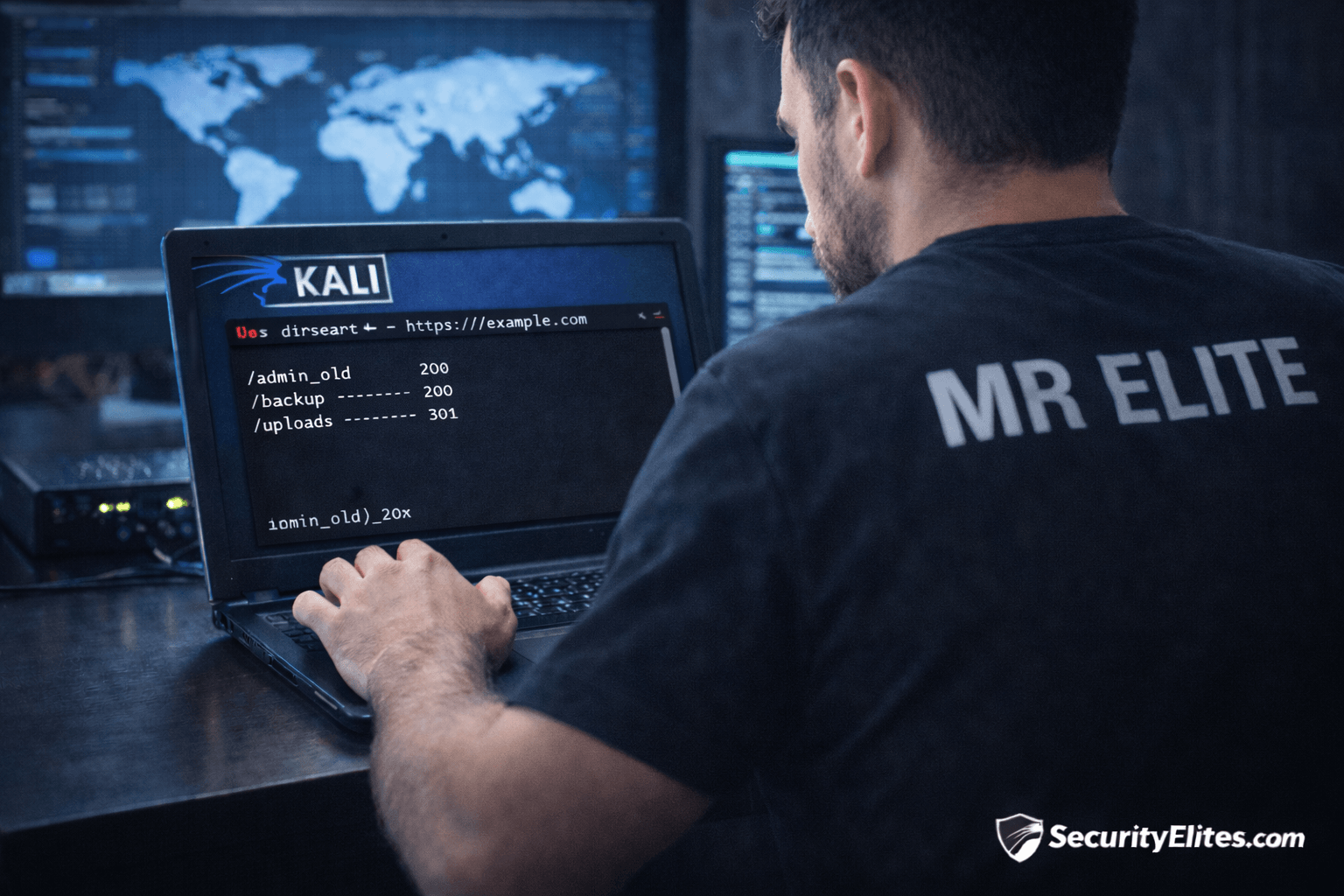
Information Gathering Using Kali Linux Day 7: Directory Discovery with Dirsearch
Information Gathering Using Kali Linux Day 7 - Learn Information Gathering using Kali Linux with Dirsearch step-by-step. Discover hidden directories…
Amass Tutorial (2026): Powerful Subdomain Enumeration Guide for Kali Linux
Learn Amass tutorial for subdomain enumeration and reconnaissance in Kali Linux. Step-by-step ethical hacking guide used by penetration testers and…
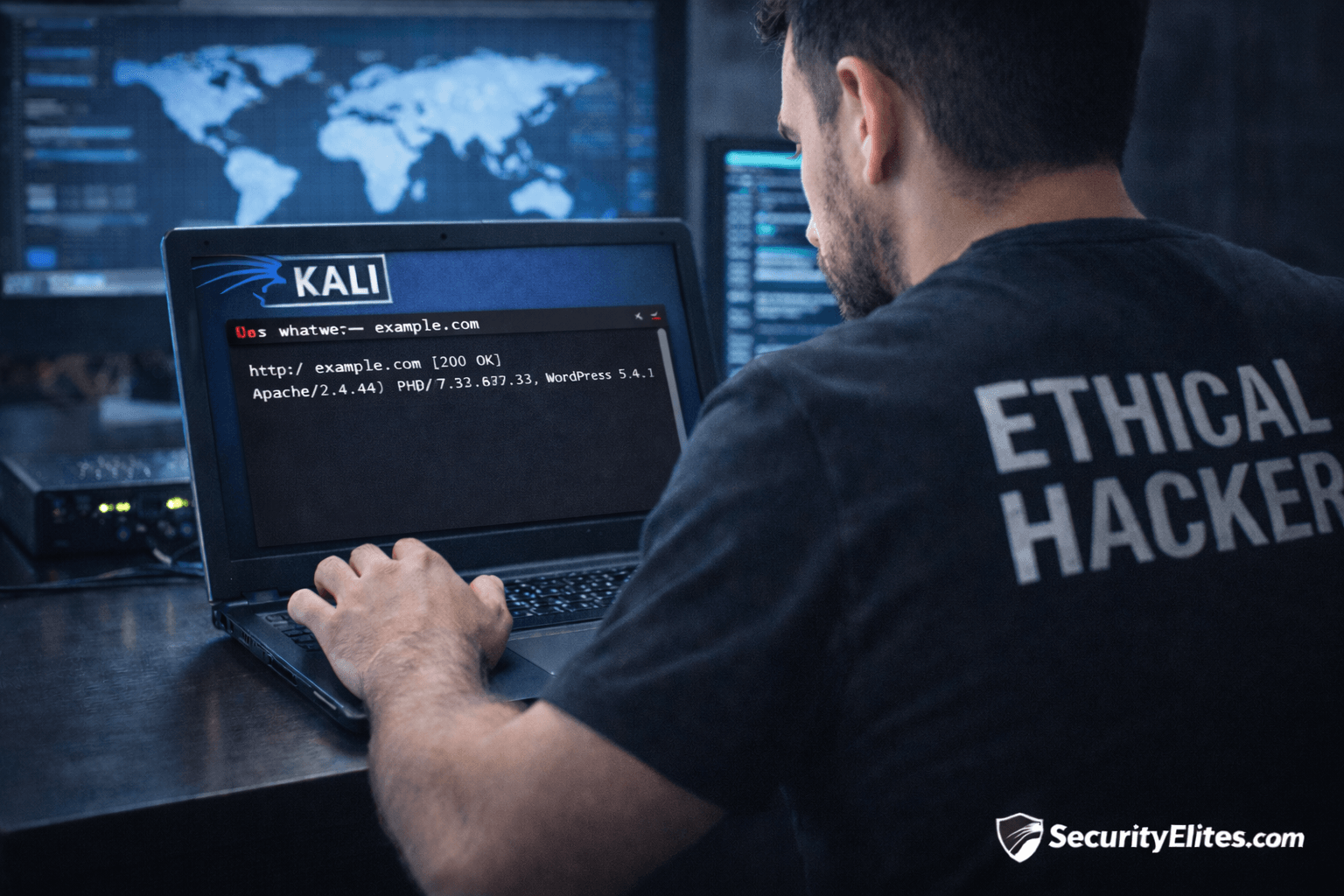
Information Gathering Using Kali Linux Day 6: Technology Fingerprinting with WhatWeb
Information Gathering Using Kali Linux Day 6 - Learn Information Gathering using Kali Linux with WhatWeb step-by-step. Detect website technologies,…
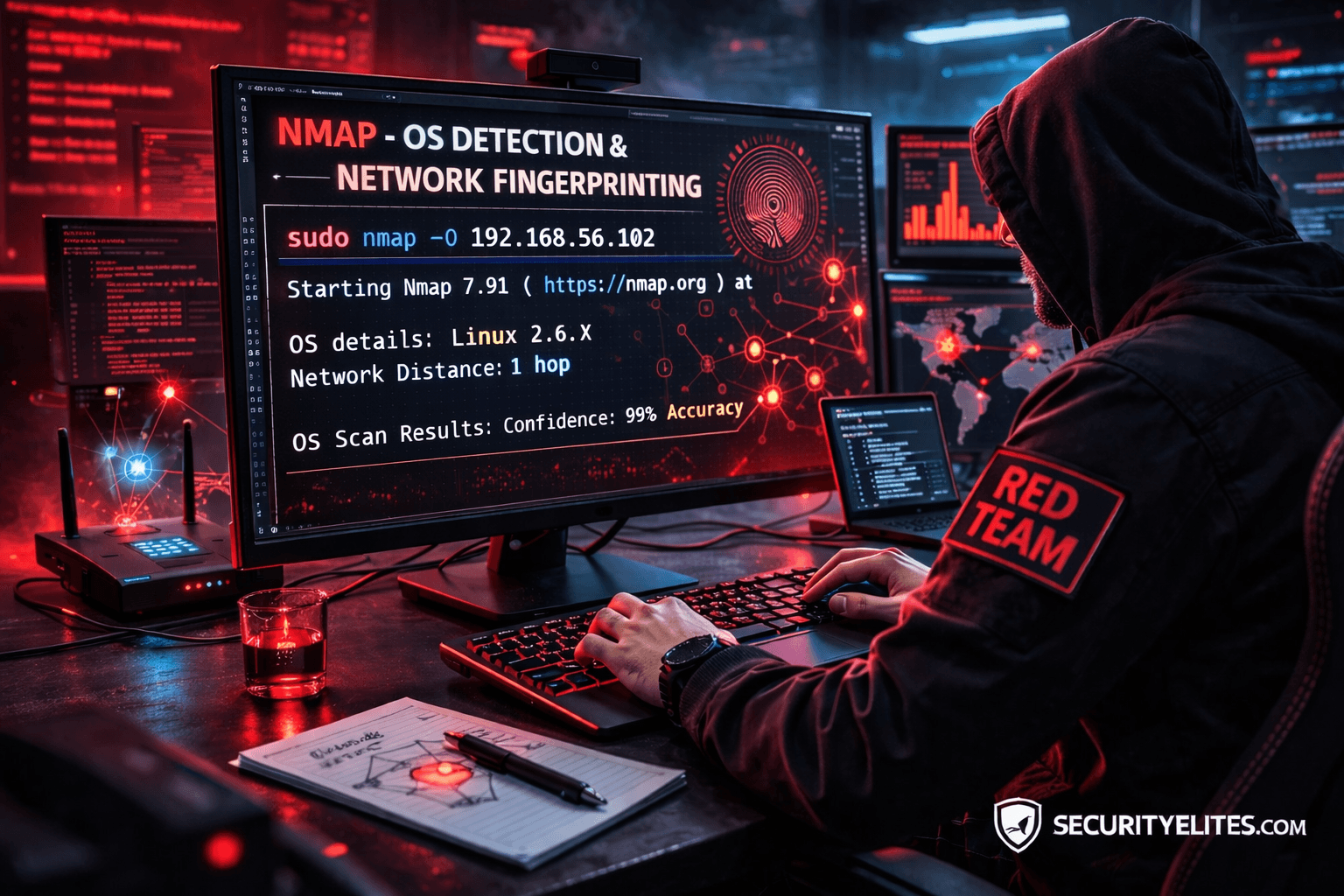
Network Scanning Tutorial Using Nmap Day 5— OS Detection & Network Fingerprinting (Professional Level)
Network Scanning Tutorial Using Nmap Day 5 - Learn operating system detection and network fingerprinting using Nmap like professional penetration…