Cyber Security Tools
Discover the most powerful cyber security tools and ethical hacking tools used by penetration testers and security researchers. This category features detailed tutorials, installation guides, and usage walkthroughs for reconnaissance, exploitation, OSINT, wireless testing, and password cracking tools. Explore both free and premium security tools, compare their features, and learn how to use them effectively in real penetration testing scenarios.
81 articles
Kali Linux Day 5: John the Ripper Tutorial — Crack Hashes, /etc/shadow, ZIP & PDF Passwords (Complete Guide 2026)
Complete John the Ripper tutorial for Kali Linux — identify hashes, crack /etc/shadow with unshadow, use wordlist mode, rule-based cracking,…
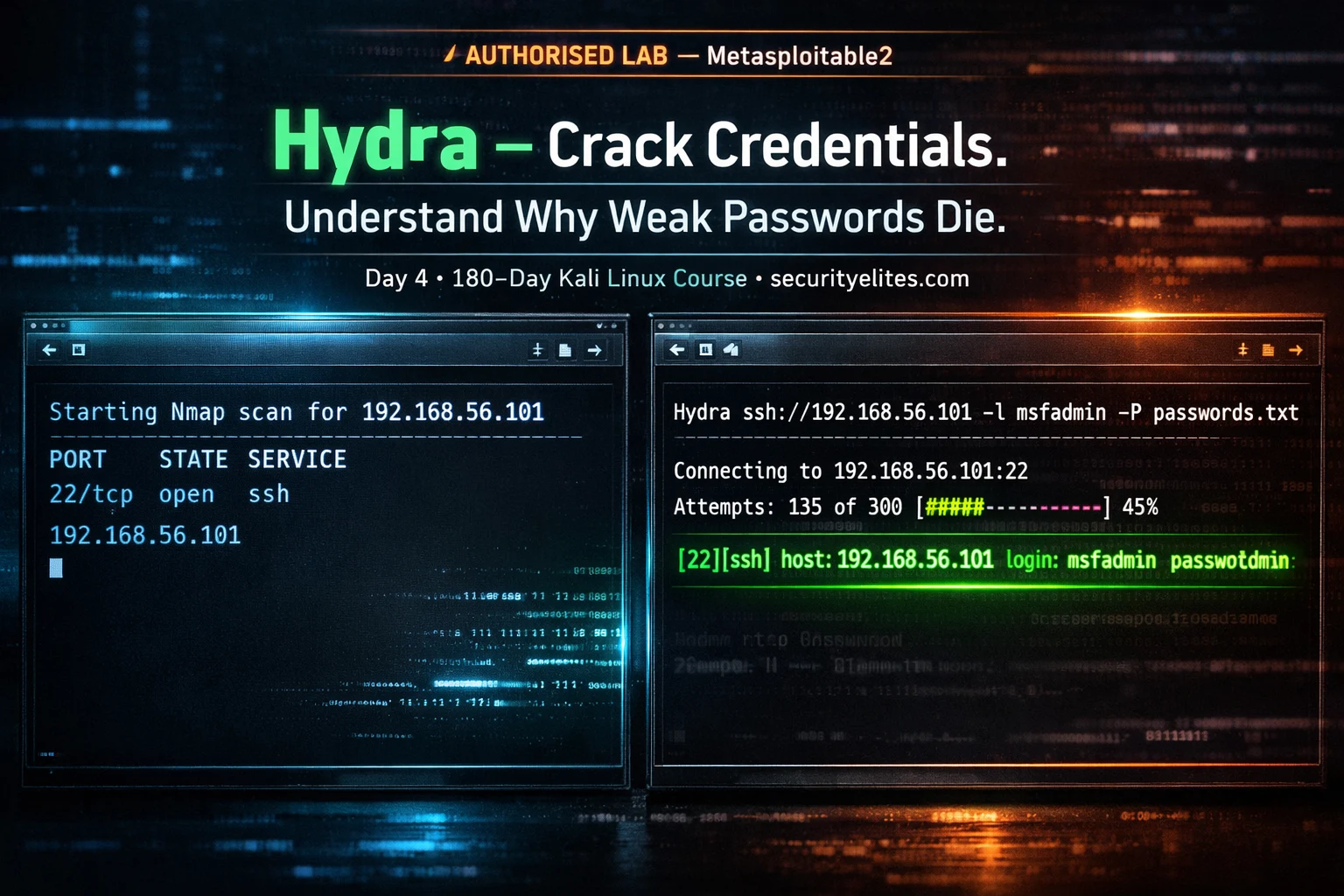
Kali Linux Day 4: Hydra Tutorial — Brute Force SSH, FTP, HTTP & 50+ Protocols (Complete Beginner Guide 2026)
Complete Hydra tutorial for Kali Linux — brute force SSH, FTP, HTTP login forms, RDP, MySQL, and 50+ protocols. Every…
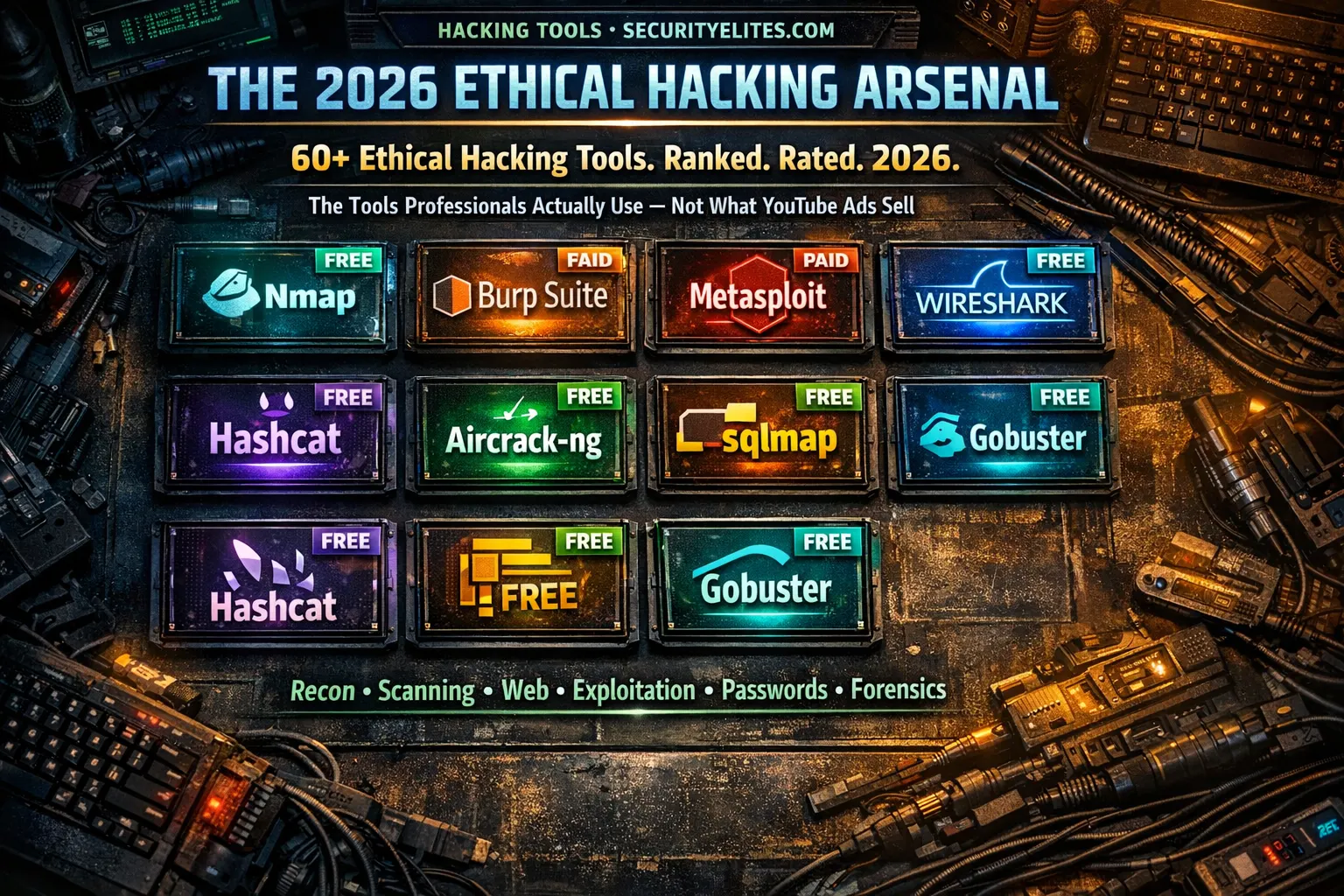
Ethical Hacking Tools List 2026 — Every Tool Professionals Actually Use (Free + Paid, Ranked by Category)
The most complete ethical hacking tools list for 2026 — 60+ tools across 10 categories with honest tier ratings, free…
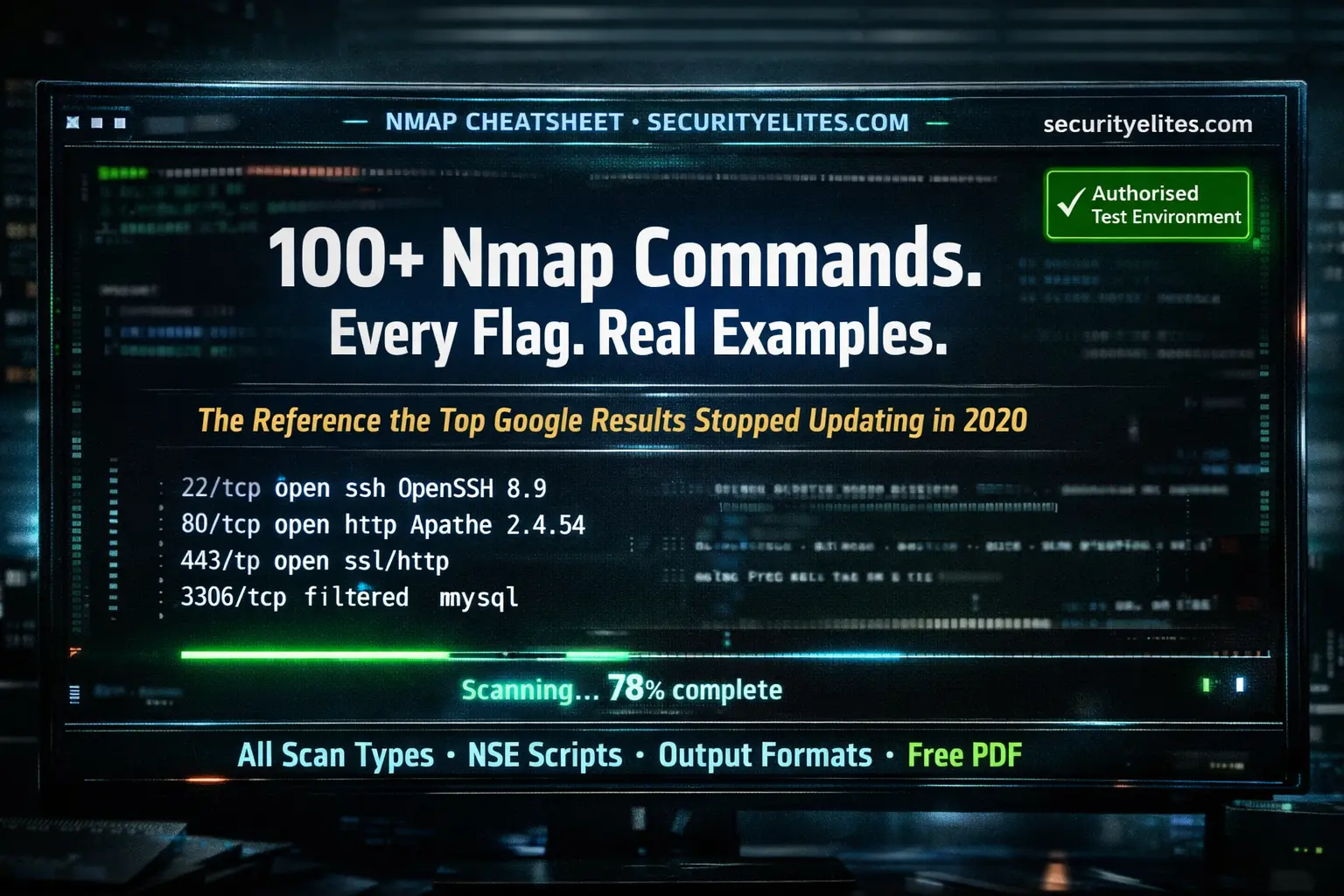
Nmap Commands with Examples 2026 — The Complete Reference (Every Flag, Every Scan Type, Free PDF Cheat Sheet)
Every Nmap commands with examples — covering all scan types, timing options, output formats, NSE scripts, firewall evasion techniques, and…
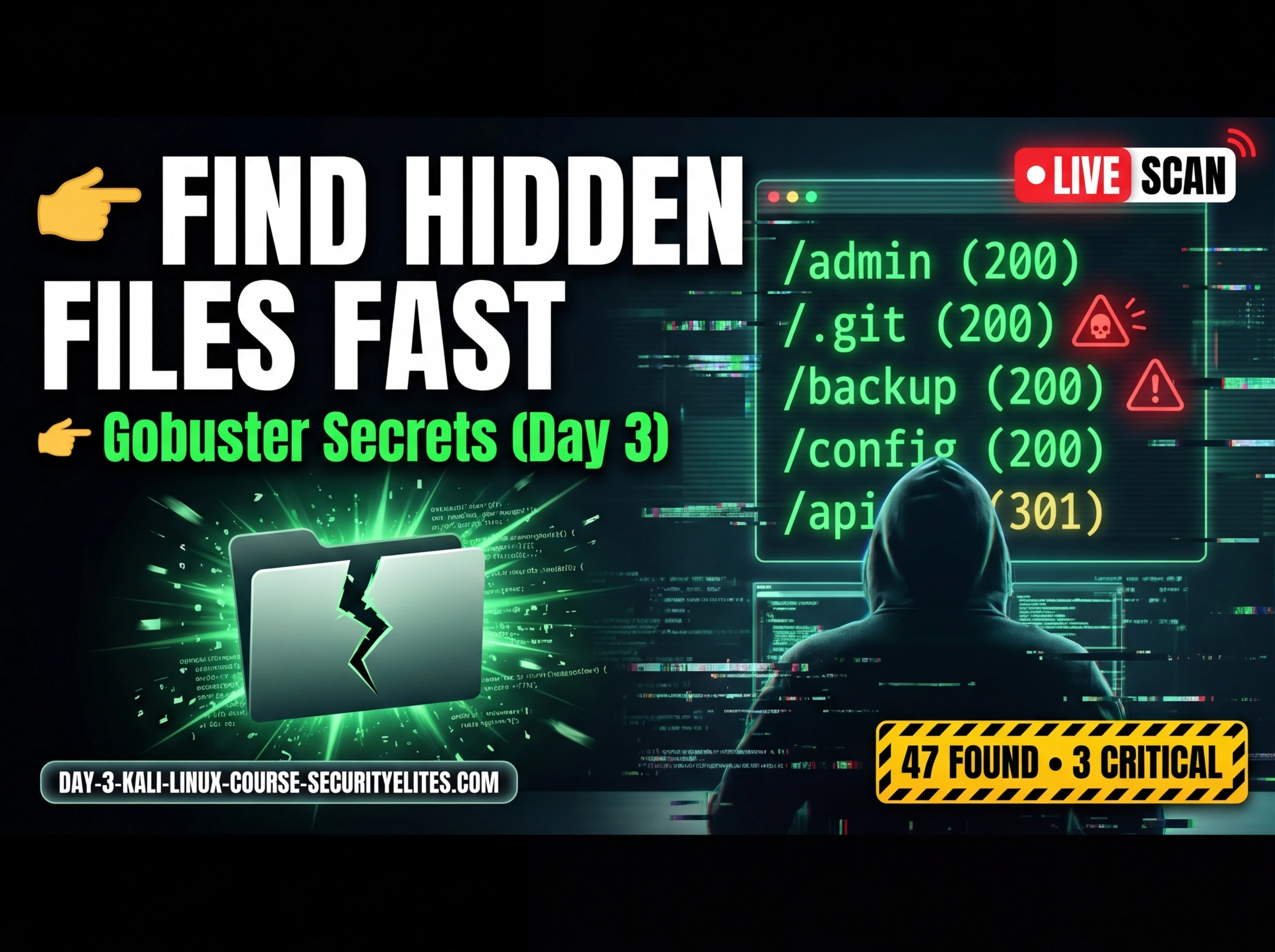
Kali Linux Day 3: Gobuster Tutorial — Find Hidden Directories, Files & Subdomains (Complete Beginner Guide 2026)
Complete Gobuster tutorial for Kali Linux — dir mode, dns mode, vhost mode, wordlists, status code filtering, file extension discovery,…
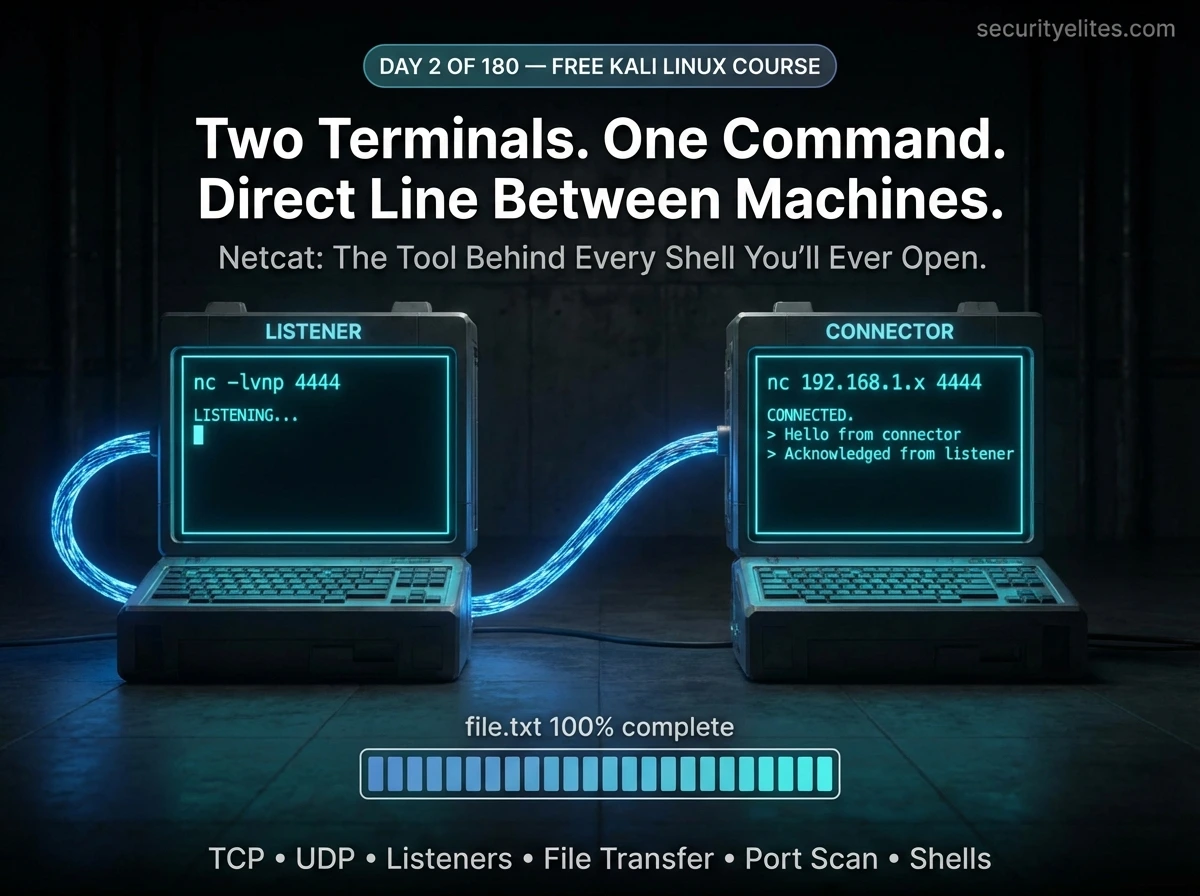
Day 2: Netcat Tutorial for Beginners — Master the Swiss Army Knife of Networking in Kali Linux (2026)
Day 2 of 180. Netcat tutorial from scratch — make TCP/UDP connections, transfer files, set up listeners, perform port scanning,…
Hydra Cheat Sheet (60+ Commands, Examples & Hands on Lab) – 2026 Guide
Master Hydra with this ultimate hydra cheat sheet. 60+ commands, real examples, and hands-on labs for beginners and professionals.
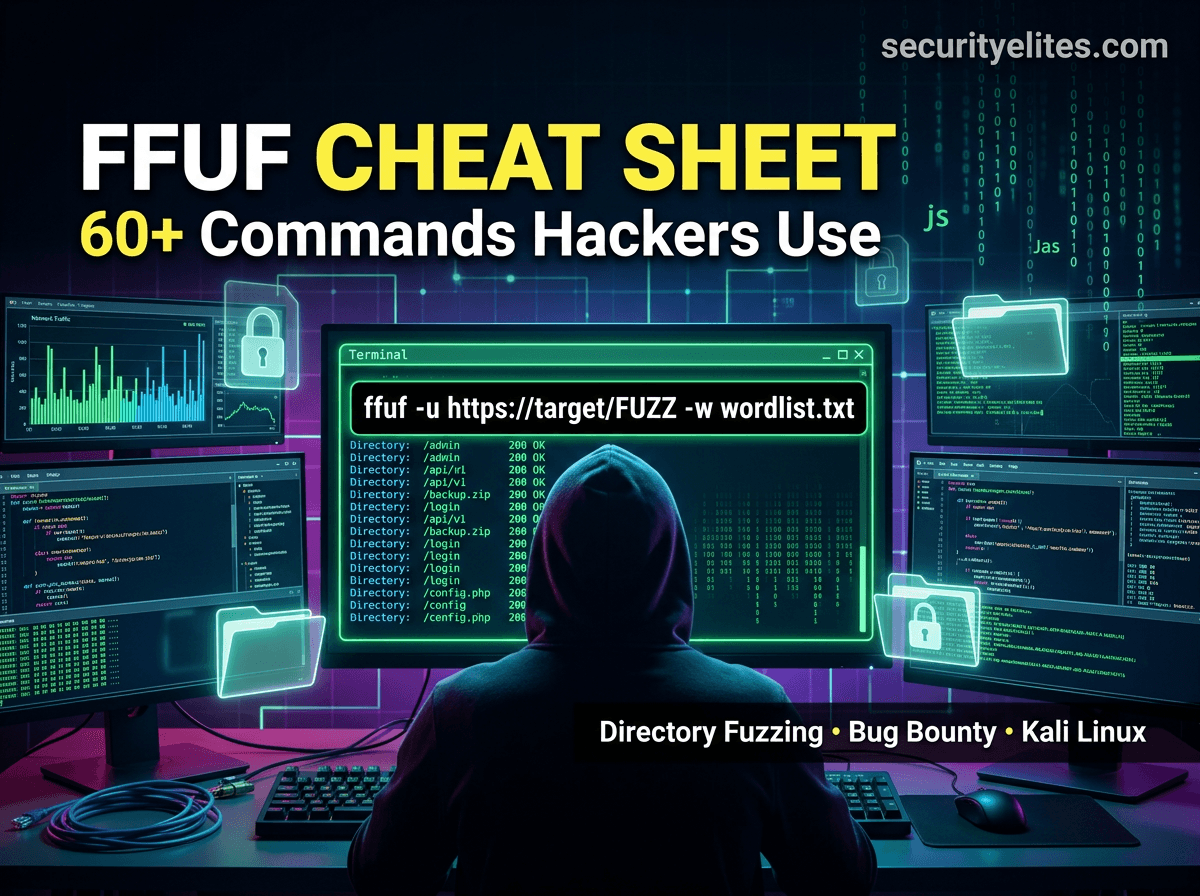
FFUF Cheat Sheet (60+ Commands & Examples) – Ultimate 2026 FFUF Guide for Kali Linux
Complete FFUF Cheat Sheet with 60+ commands, examples, and hands-on labs. Learn FFUF for penetration testing, bug bounty, and ethical…
15 Best Ethical Hacking Tools Used by Hackers in 2026 (Complete Guide)
Discover the 15 best ethical hacking tools used by hackers in 2026. Learn how penetration testers use cybersecurity tools to…