Cyber Security Tools
Discover the most powerful cyber security tools and ethical hacking tools used by penetration testers and security researchers. This category features detailed tutorials, installation guides, and usage walkthroughs for reconnaissance, exploitation, OSINT, wireless testing, and password cracking tools. Explore both free and premium security tools, compare their features, and learn how to use them effectively in real penetration testing scenarios.
81 articles
theHarvester Cheat Sheet (60+ Commands, Examples & Kali Linux Guide) – 2026
Master theHarvester with this ultimate theHarvester cheat sheet. Learn 60+ commands, OSINT techniques, and real penetration testing scenarios using Kali…
Masscan Cheat Sheet (70+ Commands & Examples) – Complete Masscan Guide 2026
Master Masscan with this ultimate Masscan cheat sheet featuring 70+ commands, Kali Linux installation, real hacking scenarios, and practical cybersecurity…
Amass Cheat Sheet (70+ Commands & Examples) – Ultimate 2026 Guide for Recon & Bug Bounty
Master the Amass Cheat Sheet with 60+ commands, real examples, and hands-on labs. Learn domain enumeration for bug bounty and…
Password Cracking Explained: 12 Powerful Techniques, Tools & Prevention (2026 Guide)
Learn how password cracking works, the tools hackers use, and proven ways to prevent password attacks. Complete cybersecurity guide with…
NMAP Cheat Sheet (60+ Commands, Examples & Hands-on Lab) – Ultimate 2026 Guide
Complete NMAP Cheat Sheet with 60+ commands, real examples, Kali Linux installation, and hands-on labs. Learn NMAP penetration testing fast.
Information Gathering Using Kali Linux Day 10: Metadata Intelligence with Metagoofil
Information Gathering Using Kali Linux Day 10 - Learn Information Gathering using Kali Linux with Metagoofil step-by-step. Extract hidden metadata…
FFUF Guide for Ethical Hackers – 10 Steps Web Fuzzing Tutorial Kali Linux
Learn web fuzzing using FFUF in this beginner friendly FFUF Guide. Discover hidden directories, parameters, and APIs using Kali Linux…
Gobuster Tutorial: 9 Powerful Steps to Discover Hidden Directories (Kali Linux Guide)
Learn Gobuster directory enumeration with this complete Gobuster tutorial. Discover hidden directories using Kali Linux with step-by-step ethical hacking labs.
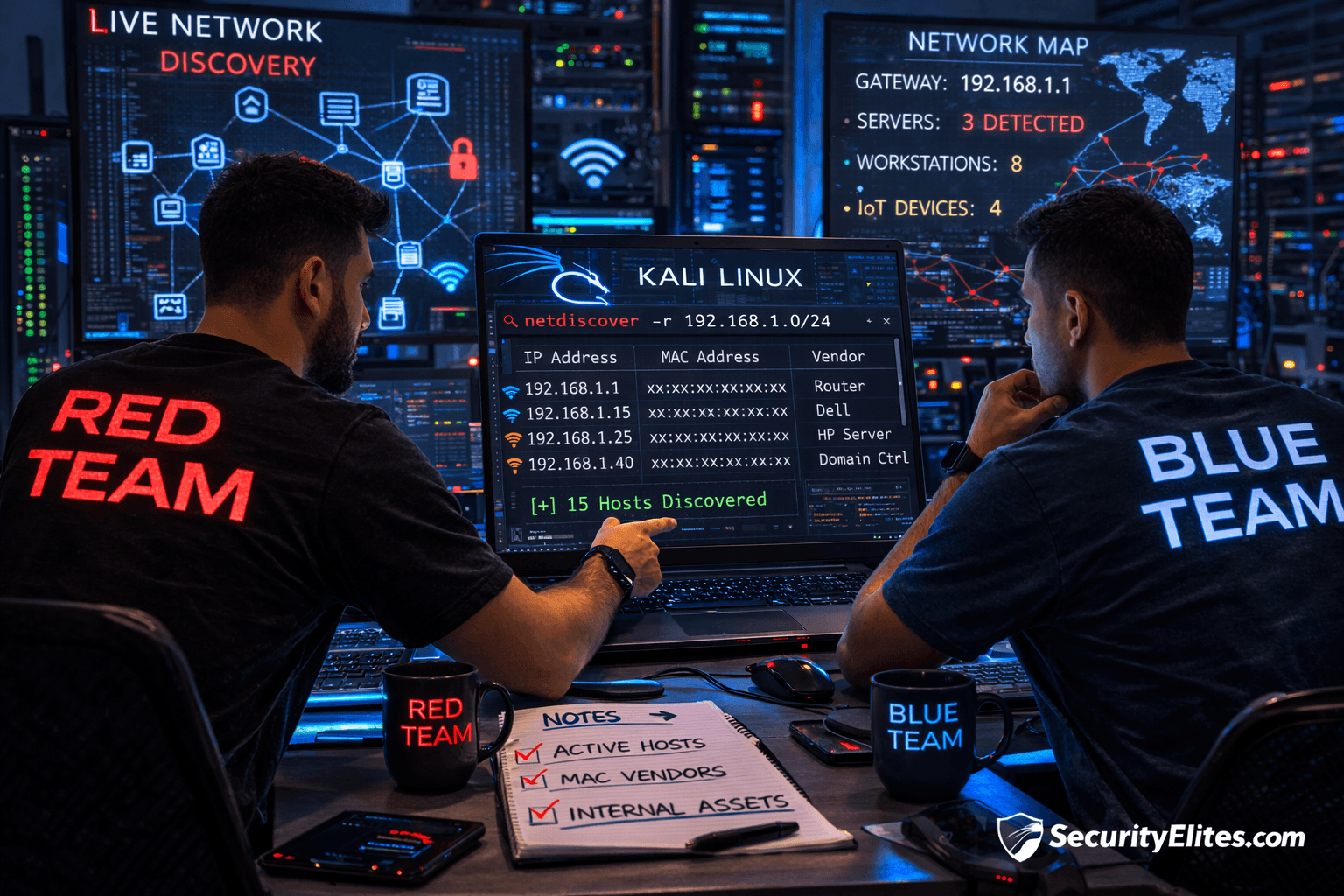
Information Gathering Using Kali Linux Day 9: Internal Network Discovery with Netdiscover
Information Gathering Using Kali Linux Day 9 - Learn Information Gathering using Kali Linux with Netdiscover step-by-step. Discover live internal…