Ethical Hacking Courses
71 articles
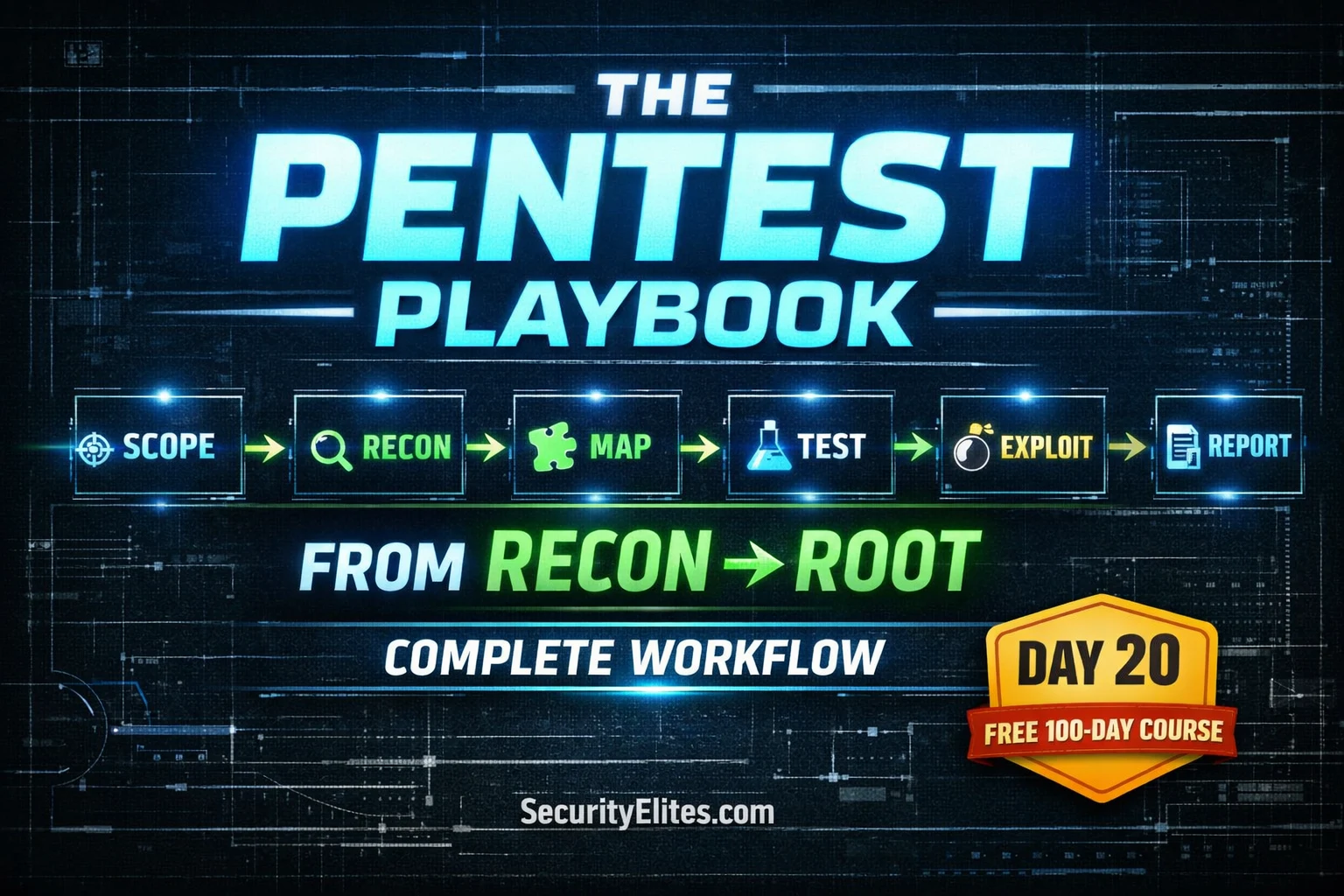
Day 20: Web Application Penetration Testing Methodology 2026 — Zero to Pro Hacker Workflow (Complete Guide)
Day 20 of 100. Master the complete web app pentesting methodology—scoping, reconnaissance, mapping, testing, exploitation, and reporting. A professional framework…
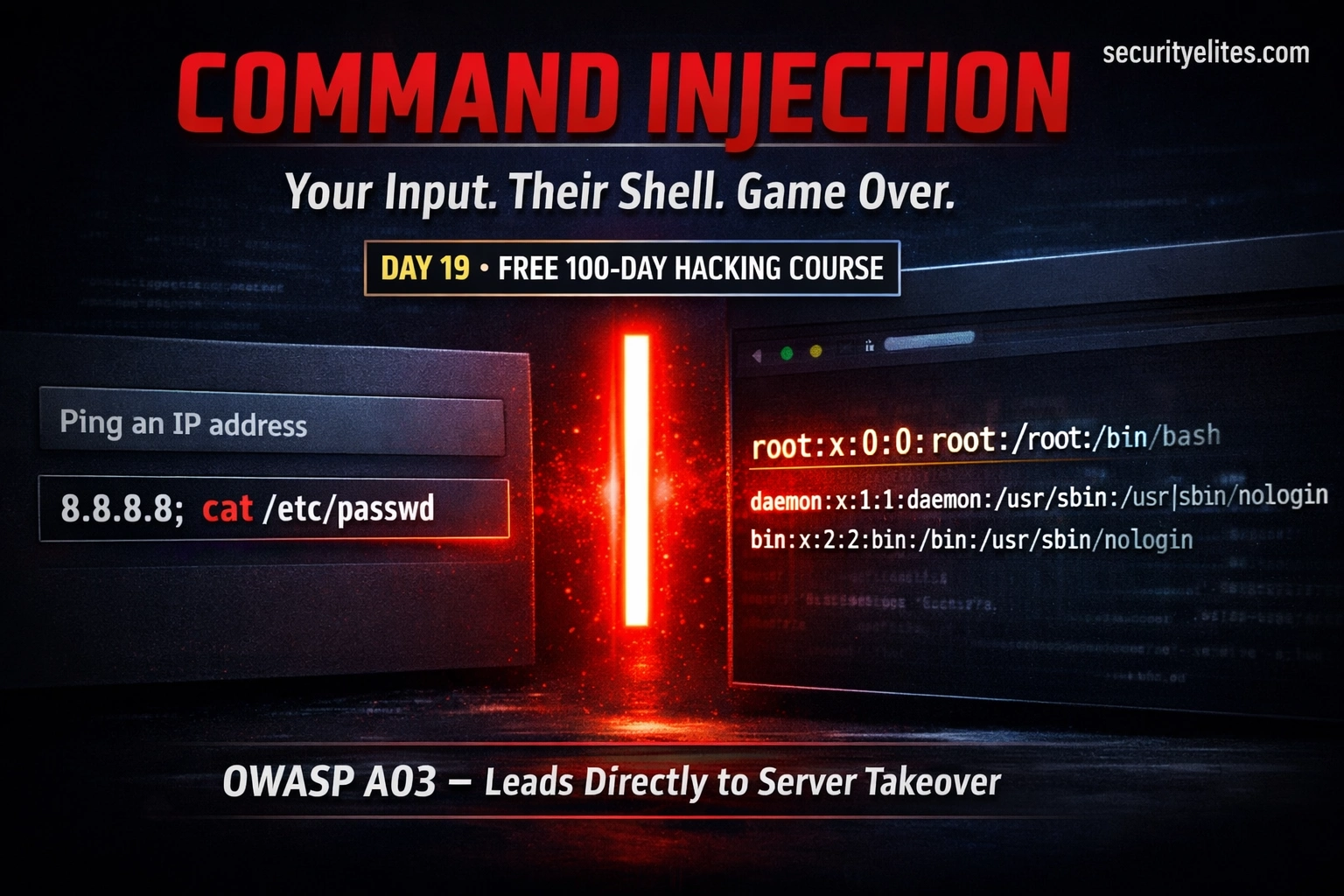
Day 19: Command Injection — When User Input Reaches the OS Shell (2026)
Day 19 of 100. Learn OS command injection, shell metacharacters, blind injection, DVWA lab walkthrough, and secure coding practices. One…
Day 18: File Upload Vulnerabilities — From Image Upload to Web Shell (2026)
Understand file upload vulnerabilities from first principles — how validation is bypassed, how web shells work, full DVWA demos at…
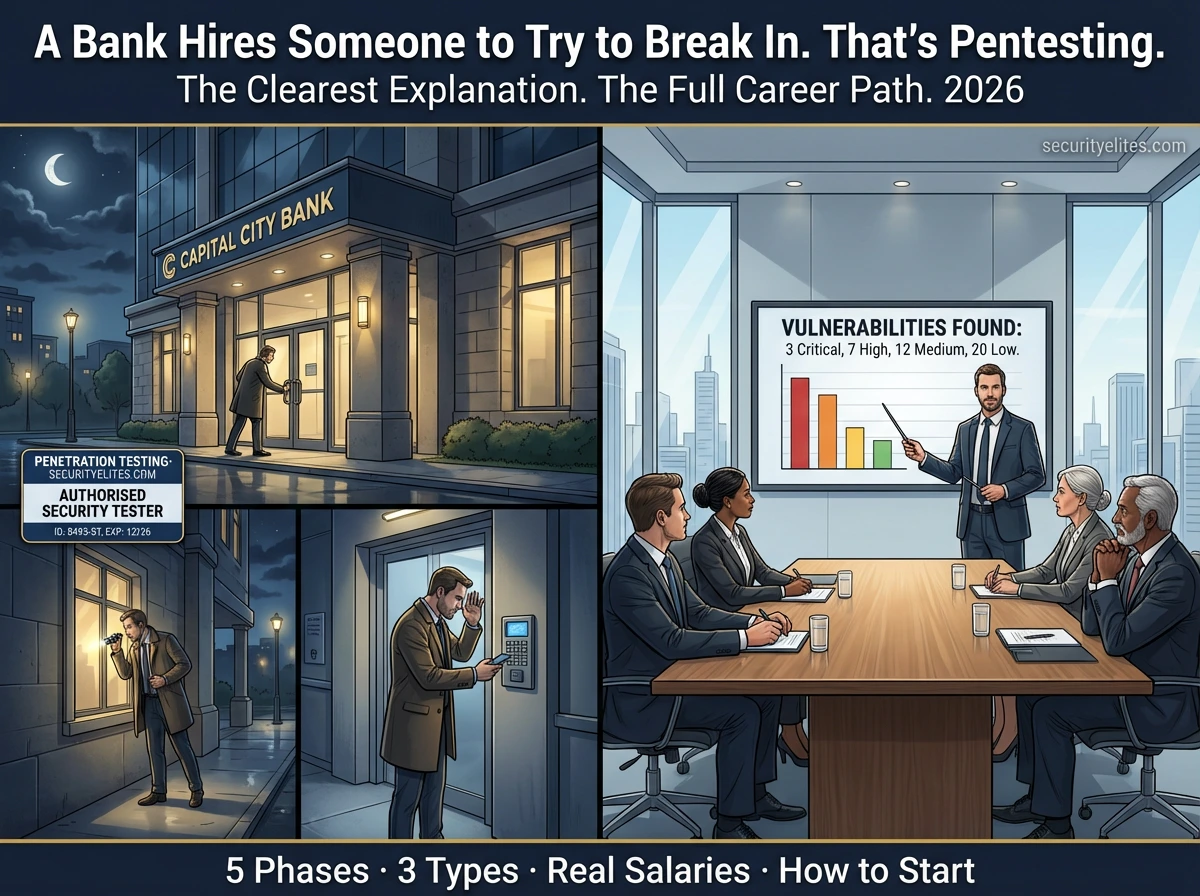
What Is Penetration Testing? The Simplest Explanation You Will Ever Read — With Real-World Examples (2026)
What is Penetration testing explained simply — how it works, the 5 phases professionals follow, types of pentest, who hires…
Day 17: Security Misconfiguration — The Easiest Vulnerabilities to Find (2026)
Day 17 of 100. Learn security misconfiguration — default credentials, verbose errors, exposed admin panels, open cloud buckets, directory listing,…
Kali Linux Day 3: Gobuster Tutorial — Find Hidden Directories, Files & Subdomains (Complete Beginner Guide 2026)
Complete Gobuster tutorial for Kali Linux — dir mode, dns mode, vhost mode, wordlists, status code filtering, file extension discovery,…
What Certifications Do Ethical Hackers Need 2026 — Honest Ranking (CEH vs OSCP vs eJPT vs Security+ Compared)
The honest, unaffiliated comparison of ethical hacking certifications in 2026 — CEH, OSCP, eJPT, CompTIA Security+, PNPT, eCPPT. Cost, difficulty,…
Bug Bounty Hunting for Beginners — The Complete Step-by-Step Guide From Zero to First Paid Finding (2026)
The most completeguide on bug bounty hunting for beginners 2026 — platform setup, reconnaissance, vulnerability testing, professional report writing, and…
Free Ethical Hacking Course for Beginners 2026 — 100 Days from Zero to Professional (No Credit Card Ever)
The most comprehensive free ethical hacking course online — 100 days, 100 topics, from absolute zero to professional penetration tester.…