Kali Linux
Master Kali Linux with step-by-step tutorials covering installation, configuration, commands, and penetration testing tools. This section includes detailed guides on wireless attacks, password cracking, reconnaissance tools, and exploitation frameworks available in Kali Linux. Learn how to set up hacking labs, use terminal commands efficiently, and perform real-world security testing using tools like Aircrack-ng, Hydra, John the Ripper, and Wireshark. Perfect for beginners and cyber security professionals looking to enhance their penetration testing skills.
97 articles
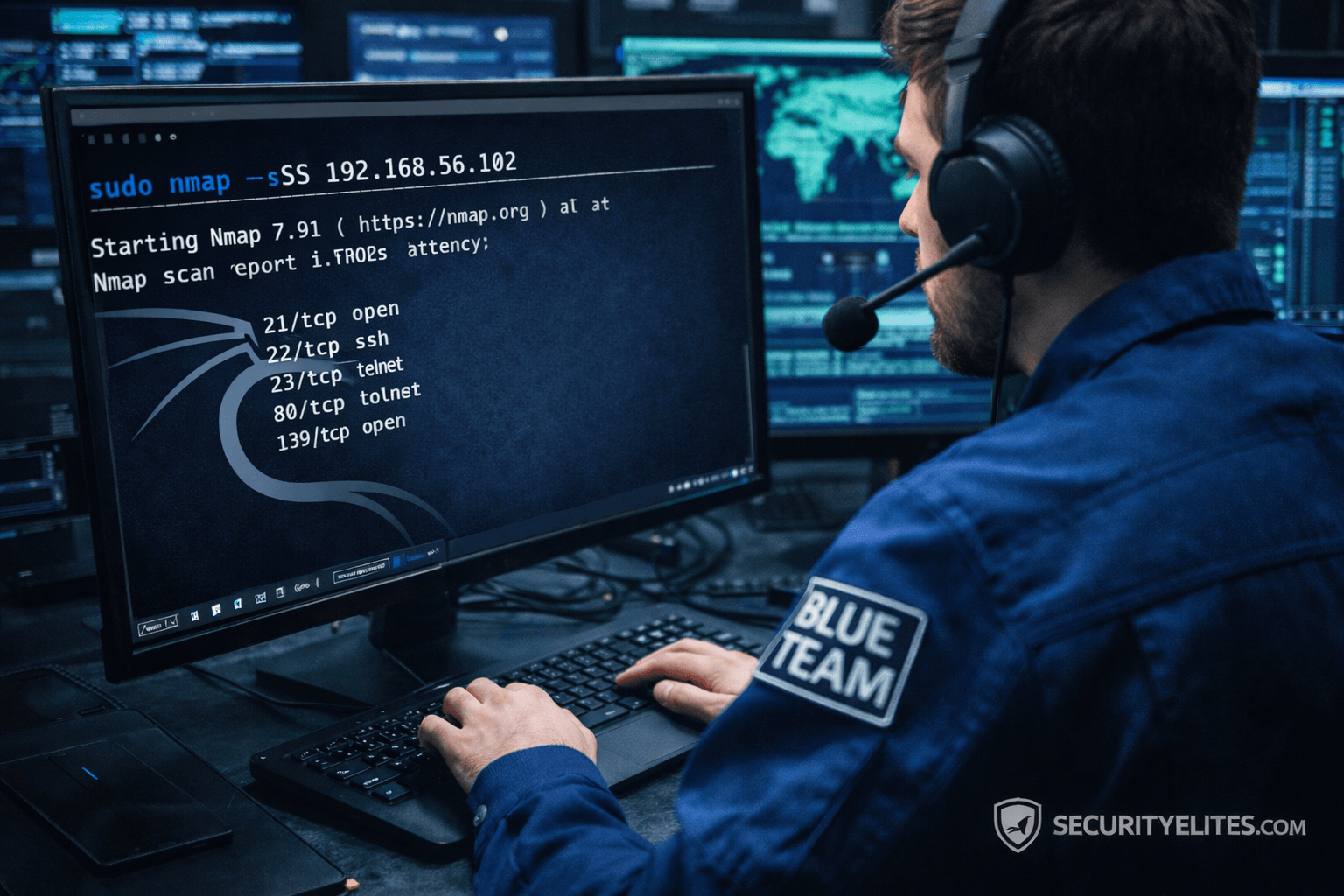
Network Scanning Tutorial Using Nmap Day 3 — Port Scanning Techniques Deep Dive
Network Scanning Tutorial Using Nmap Day 3 - Learn professional port scanning using Nmap including TCP SYN, Connect, UDP, and…
Burp Suite Beginner Guide: Complete Ethical Hacking & Web Testing Tutorial
Burp Suite Beginner Guide to learn Burp Suite step-by-step with this beginner ethical hacking guide covering interception, vulnerability testing, attacker…
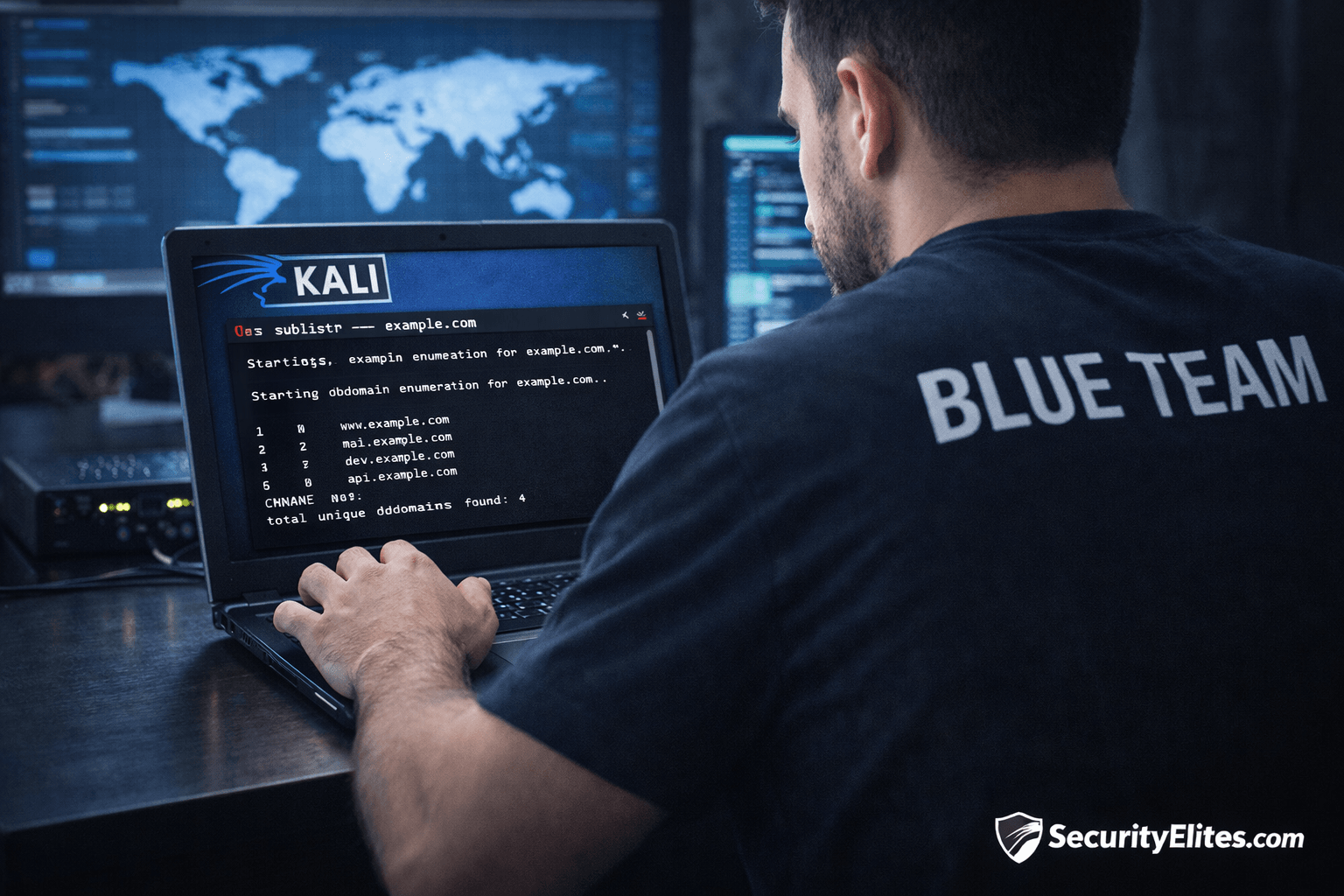
Information Gathering Using Kali Linux Day 3: Subdomain Enumeration with Sublist3r
Information Gathering Using Kali Linux Day 3 - Learn Information Gathering using Kali Linux with Sublist3r step-by-step. Discover hidden subdomains…
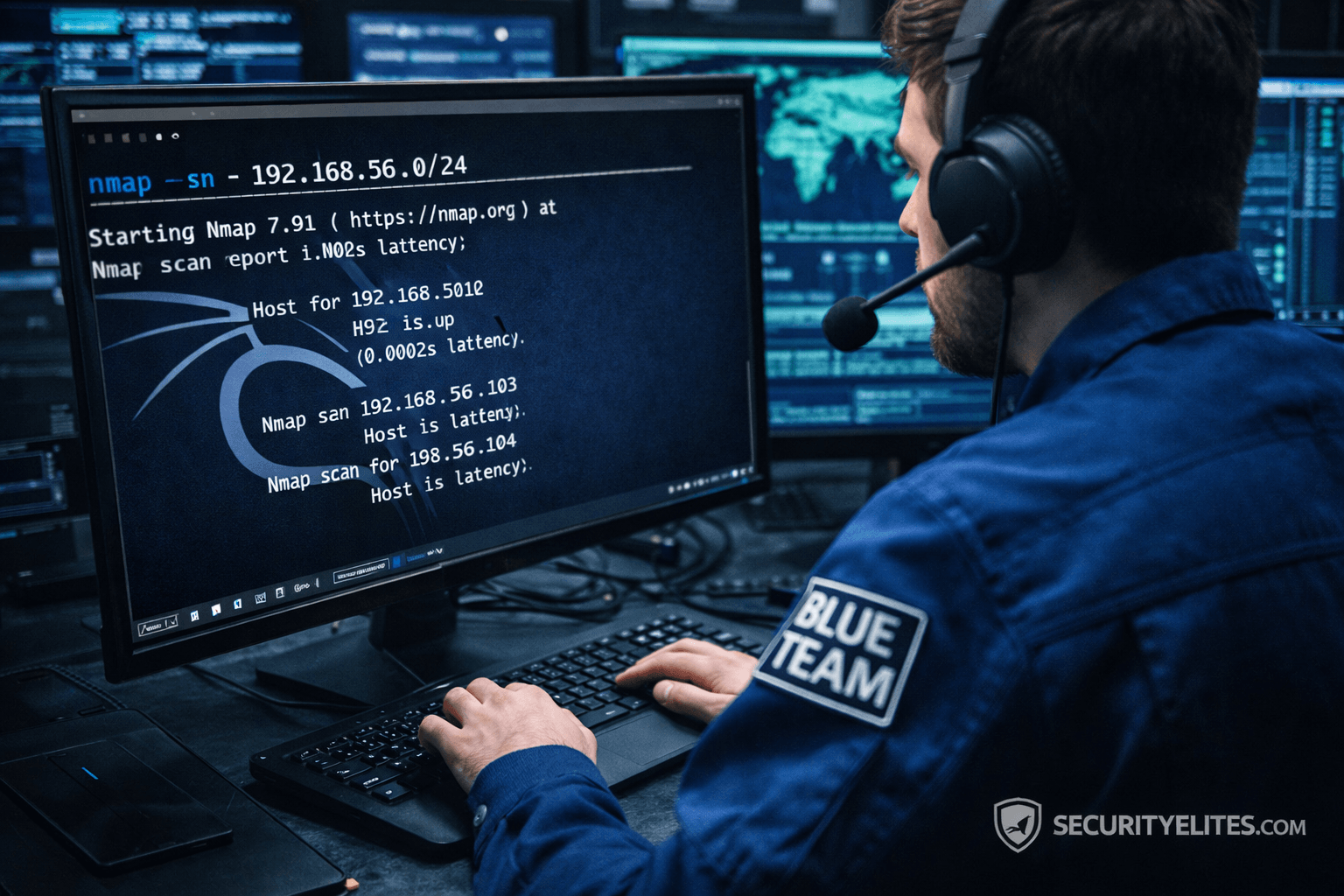
Network Scanning Tutorial Using Nmap Day 2— Host Discovery & Network Mapping
Network Scanning Tutorial Using Nmap Day 2 - Learn host discovery and network mapping using Nmap like professional ethical hackers.…
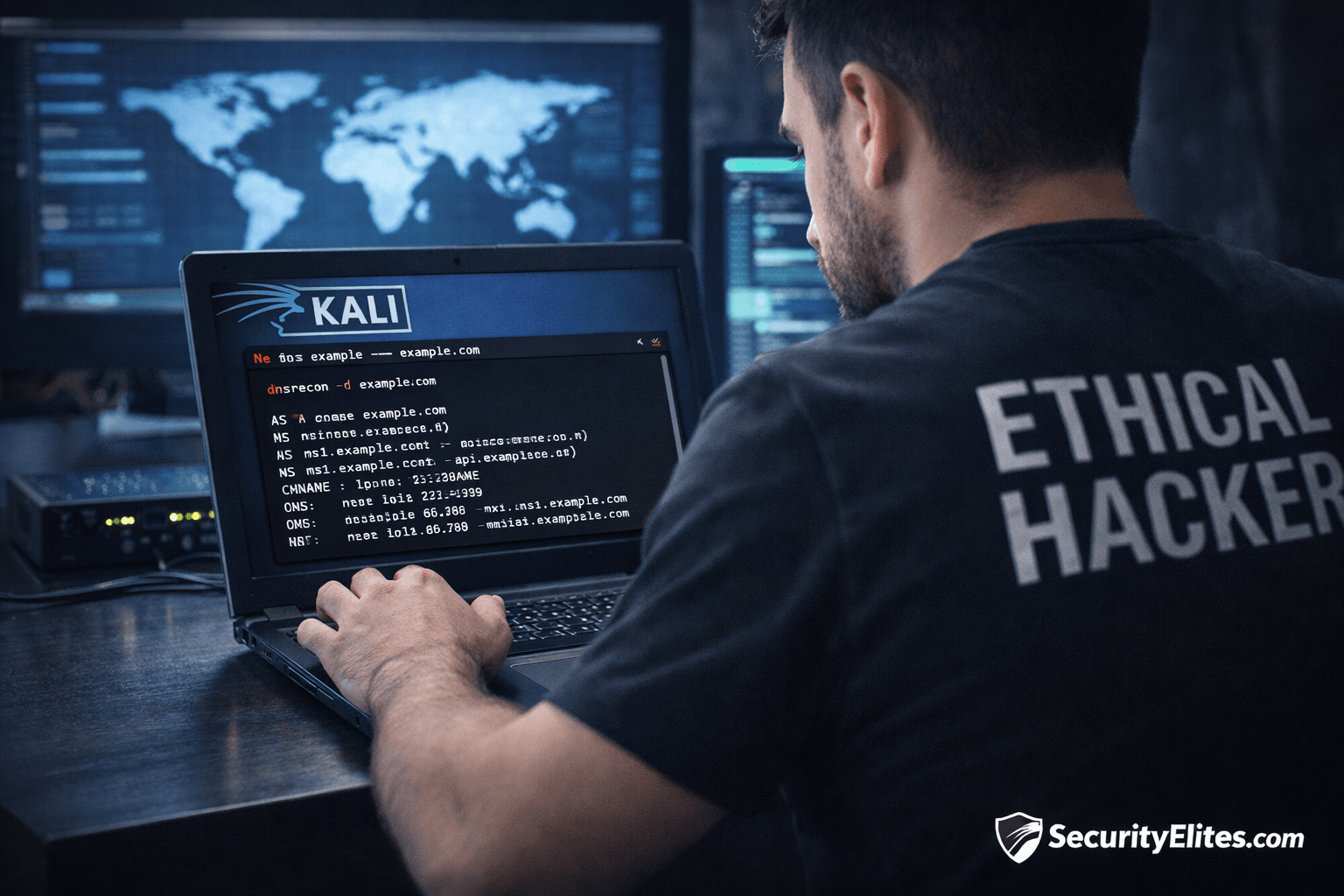
Information Gathering Using Kali Linux Day 2: DNS Reconnaissance with dnsrecon
Information Gathering Using Kali Linux Day 2 - Learn Information Gathering using Kali Linux with dnsrecon step-by-step. Discover DNS records,…
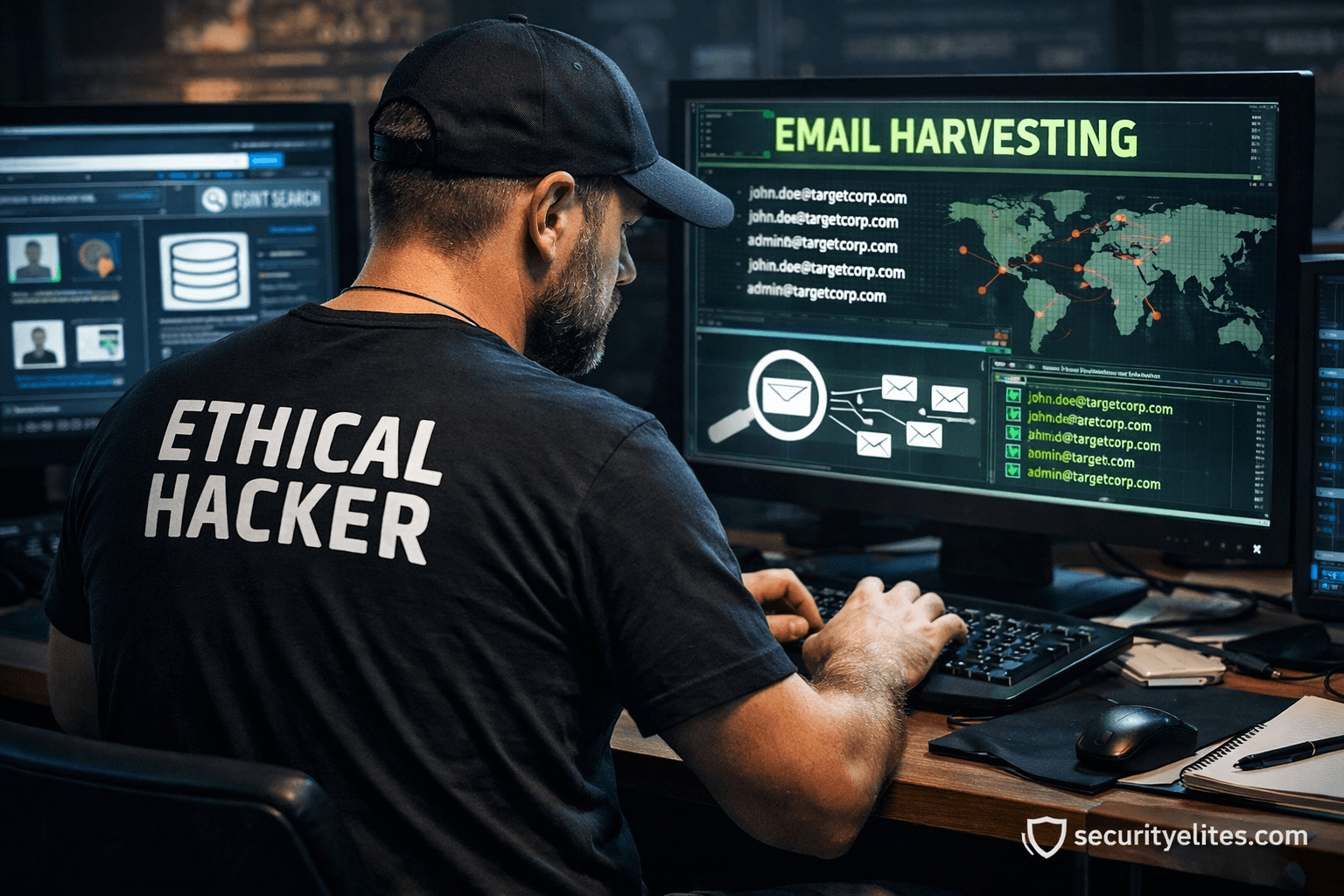
Email Harvesting Tutorial for Ethical Hackers – Beginner to Pro Guide
Email Harvesting Tutorial step-by-step with practical ethical hacking lab, OSINT reconnaissance workflow, tools, attacker mindset, and enterprise defense strategies.