Those numbers don’t mean 81% of all passwords are crackable. They mean 81% of the passwords in that particular dataset — which represent how real users choose passwords — were crackable. The passwords that weren’t cracked were the randomly generated ones, the long ones, and the ones protected by slow hashing algorithms that limited the guess rate. The ones that were cracked were the human-pattern ones: words with substitutions, words followed by numbers, names plus dates.
AI password cracking is improving. But the defences have been available for decades — and they still work.
🎯 After This Tutorial
⏱️ 18 min read · 3 exercises
📋 AI Password Cracking – Contents
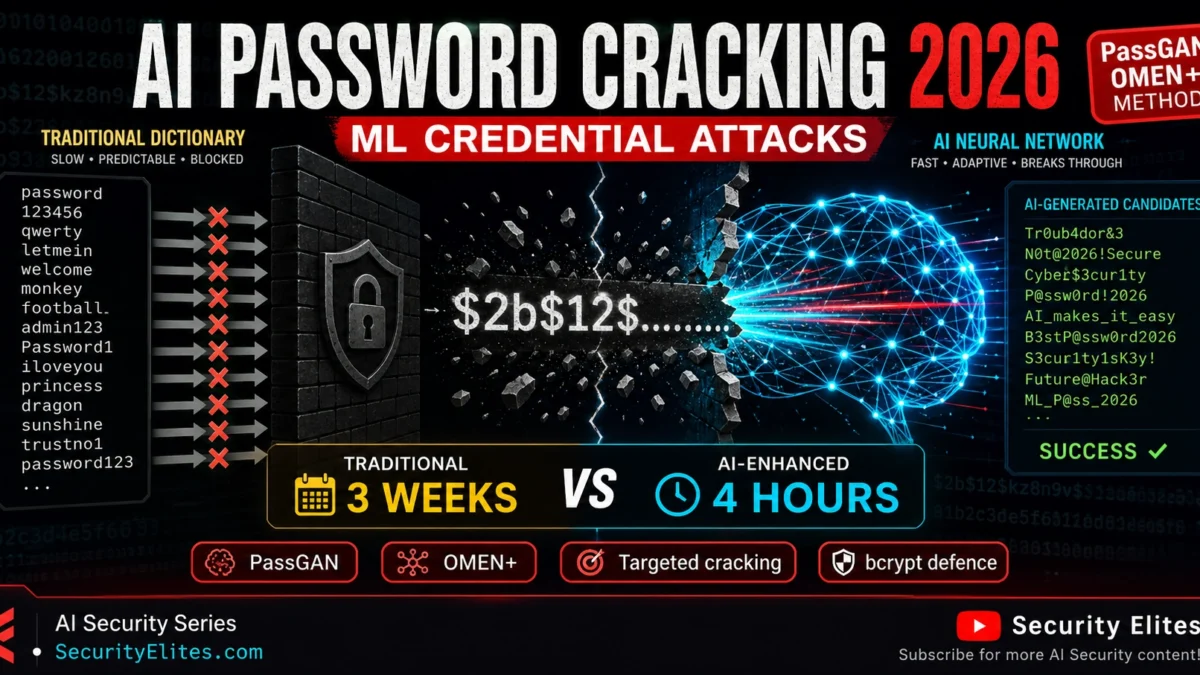
PassGAN — Generative Password Cracking
PassGAN is the model I benchmark first when evaluating AI password cracking capability — the GAN approach produces qualitatively different output from rule-based generators. My defence recommendations against AI password cracking focus on increasing attacker cost rather than preventing attacks entirely. PassGAN applies Generative Adversarial Networks to password cracking. A GAN consists of two competing neural networks: a generator that produces candidates and a discriminator that evaluates whether they look realistic. Trained on a large dataset of real leaked passwords, the PassGAN generator learns the statistical properties of human password choice — which character combinations occur together, what transformations people apply to base words, how length distributes across real passwords. The output is a generative model that produces novel password guesses that match how humans actually create passwords, not just how attackers traditionally guess them.
The practical improvement over rule-based cracking: traditional hashcat rules encode known human patterns explicitly (capitalise first letter, append number, leet speak substitution). PassGAN learns patterns implicit in training data that no human thought to encode as a rule — unusual character combinations, regional password patterns, emerging trends in how people chose passwords in specific breach datasets. At shorter password lengths and human-chosen passwords, PassGAN’s coverage exceeds rule-based attacks. At longer lengths and randomly generated passwords, it offers no advantage — randomly generated passwords have no statistical patterns to learn.
OMEN+ and Probabilistic Cracking
OMEN+ is the probabilistic cracker I use most often in authorised password audits — it outperforms hashcat rules on complex datasets. OMEN (Ordered Markov ENumerator) and its neural-network-enhanced variant OMEN+ use probabilistic models trained on password datasets to order guesses by likelihood — testing the most probable passwords first within a given compute budget. Traditional dictionary attacks test guesses in wordlist order. Rule-based attacks test transformed dictionary words in rule order. OMEN+ tests passwords in order of their statistical probability given the target character sequence, using Markov chain analysis of real password datasets to determine that probability.
The practical improvement is efficiency at constrained compute budgets: OMEN+ finds more passwords per hour than rule-based hashcat attacks against human-chosen password sets because it’s testing in probability order rather than rule-coverage order. For penetration testing and password auditing, this means OMEN+ can identify a higher proportion of weak passwords in a fixed-time assessment window — which produces a more accurate picture of password policy effectiveness against real-world attack efficiency.
Length
vs MD5
vs bcrypt (w12)
8 chars
Seconds
Hours — AI improves speed vs rules
9 chars
Minutes
Days — AI covers patterns rules miss
13 chars
Hours
Months — work factor dominates
16 chars
Years (GPU farm)
Computationally infeasible
⏱️ 15 minutes · Browser only
The original PassGAN research and the 2023 Home Security Heroes study are the two primary data sources for AI password cracking performance — reading the actual numbers gives you the evidence base for password policy recommendations.
Search: “Home Security Heroes PassGAN AI password cracking study 2023”
Find the study with the breakdown by password length and complexity.
What percentage of 8-character passwords were cracked in under a minute?
What percentage of 12-character passwords were cracked in the same timeframe?
Step 2: Find the original PassGAN research paper
Search: “PassGAN password cracking generative adversarial networks Hitaj 2019”
Read the abstract and key results.
How did PassGAN compare to HashCat with best rules in the original research?
Step 3: Test password strength estimators
Go to: security.org/how-secure-is-my-password/ or similar
Test: “Password1!” — what crack time is estimated?
Test: “correct-horse-battery” — what crack time is estimated?
Test: a 16-character random string — what crack time is estimated?
Do these estimators account for AI cracking or only traditional methods?
Step 4: Check Have I Been Pwned
Go to: haveibeenpwned.com/Passwords
Test 5 common passwords you’d expect to be in breach datasets.
How many times does “password123” appear in breaches?
What does HIBP say about a randomly generated 16-char string?
Step 5: Find bcrypt work factor recommendations for 2025+
Search: “bcrypt work factor recommendation 2025 OWASP”
What work factor does OWASP currently recommend for bcrypt?
What’s the performance impact at that work factor on typical web server hardware?
📸 Share the passphrase vs random string crack time comparison from Step 3 in #ai-security.
Targeted AI Cracking — Personal Data as Attack Surface
Targeted AI cracking is the scenario I find most alarming from a defensive perspective — personal data as attack surface changes the threat model completely. Targeted cracking generates a personalised attack wordlist using information about the specific target — name, birthdate, family members’ names, sports teams, employer, pet names, significant locations, and any other personal details available from public sources or prior reconnaissance. Tools like CUPP (Common User Password Profiler) automate the generation of personalised wordlists. AI-enhanced versions augment CUPP-style targeted lists with generated variations that match the statistical patterns in the training data.
Executives and public figures with extensive public profiles are the most vulnerable to targeted cracking. A CEO with LinkedIn profiles, conference keynote bios, and press interviews has enough public personal information for a targeted wordlist covering their likely self-chosen password patterns. Password audits for high-value accounts should include targeted cracking attempts using publicly available personal information — if the account password appears in the targeted wordlist, the password must be replaced regardless of how complex it appears.
Defences That Work Against AI Cracking
My defence recommendations against AI password cracking focus on what actually raises attacker cost. Slow hashing algorithms (bcrypt, Argon2, scrypt) are the foundational defence — they make each guess computationally expensive, limiting the rate at which any cracking approach can test candidates regardless of how efficiently they’re generated. AI cracking’s advantage is in guess efficiency, not in defeating the computational cost of the hash function. A slow hash at an appropriate work factor makes the guess rate so low that even perfectly optimal AI-generated guesses can’t feasibly reach a 12+ character random password.
MFA is the control that makes password cracking largely irrelevant as an account takeover vector. Even a perfect cracking attack that recovers the exact password cannot access the account without the second factor. For any account where password cracking would represent a high-impact compromise, MFA should be the primary control rather than password strength alone.
⏱️ 15 minutes · No tools — analysis only
Evaluating a password policy from the attacker’s perspective — what proportion of compliant passwords would a well-configured AI cracking attack cover? — gives the data-driven argument for specific policy improvements.
– Minimum 8 characters
– Must include: uppercase, lowercase, number, symbol
– Must not contain username
– Must change every 90 days
– Last 5 passwords cannot be reused
TASK 1 — Compliance Distribution
Think about how real users comply with this policy in practice.
List 10 “creative compliance” passwords that meet all requirements.
(e.g., Summer2024!, Company@1, P@ssw0rd!, etc.)
What percentage of real users do you estimate choose these predictable patterns?
TASK 2 — AI Coverage Estimate
For your 10 example compliant passwords:
How many would likely appear in PassGAN’s output trained on breach data?
How many would be in a CUPP-generated targeted list for a typical employee?
What’s your estimated cracking success rate against this policy?
TASK 3 — Policy Weaknesses
The 90-day rotation requirement — does it improve or worsen password quality?
How do users typically respond to forced rotation? (Summer2024! → Summer2024@ → Fall2024!)
Is this policy actually more secure than “no rotation, but longer minimum length”?
TASK 4 — Improved Policy
Write a replacement policy that:
– Produces passwords more resistant to AI cracking
– Doesn’t increase user friction significantly
– Can be implemented without new tools (no password manager mandate)
Maximum 3 policy requirements.
TASK 5 — Password Manager Policy
If the organisation mandated password manager use:
How would that change the AI cracking risk profile?
What new risks does password manager use introduce that the policy should address?
📸 Share your 3-requirement improved policy in #ai-security. Better than the 4-requirement original?
Password Security Assessment Methodology
The password security assessment methodology I follow starts with a baseline crack rate before introducing AI tools. A password security assessment for AI cracking resilience covers three components: hash algorithm audit (are passwords stored with appropriate slow hashing?), policy effectiveness testing (what proportion of policy-compliant passwords does AI cracking cover?), and MFA coverage audit (what proportion of high-value accounts have MFA enabled?). The first component is the most critical — a fast-hash vulnerability makes all other password security work partially moot.
⏱️ 15 minutes · Browser only
NIST SP 800-63B is the authoritative government guidance on password policy and has been updated to reflect modern cracking capabilities — including AI-enhanced attacks. Reading the current guidance gives you the evidence-based foundation for any password policy update.
Search: “NIST SP 800-63B password guidance current 2024 2025”
Or: pages.nist.gov/800-63-4/sp800-63b.html
What does NIST say about:
– Mandatory password rotation?
– Complexity requirements (uppercase/lowercase/number/symbol)?
– Minimum password length?
– Checking passwords against breach databases?
Step 2: Find OWASP password security cheat sheet
Search: “OWASP authentication cheat sheet password 2024”
What hash algorithms and work factors does OWASP currently recommend?
What does OWASP say about password length vs complexity?
Step 3: Find enterprise password manager security research
Search: “password manager security enterprise 2024 attack surface”
What are the documented security risks of enterprise password managers?
Has any major password manager been breached? What was the impact?
Step 4: Find Have I Been Pwned Passwords API documentation
Go to: haveibeenpwned.com/API/v3#searchingPwnedPasswordsByRange
How does the k-anonymity model work for HIBP API password checking?
How can you integrate HIBP into a password change flow without sending the full hash?
Step 5: Write a 5-item AI-resistant password policy
Based on your NIST and OWASP research: write a 5-requirement policy.
Each requirement should be evidence-based (cite NIST/OWASP).
Format: requirement + rationale + implementation note.
📸 Share your 5-item evidence-based policy in #ai-security. Tag #AIPasswordCracking
📋 Key Commands & Payloads — AI Password Cracking 2026 — How Machine Learning B
✅ Complete — AI Password Cracking 2026
PassGAN and GAN-based password generation, OMEN+ probabilistic cracking, targeted cracking with personal data, slow hash defences, and the NIST-aligned password policy framework. The consistent finding: AI cracking improves efficiency against human-pattern passwords under fast hashing — the defences that worked before AI cracking (slow hashing, random generation, MFA) still work. Day 9 begins with next tutorial Prompt Injection in RAG Systems.
🧠 Quick Check
❓ Frequently Asked Questions
What is AI password cracking?
What is PassGAN?
What password length defeats AI cracking?
Does AI cracking affect bcrypt passwords?
What is targeted password cracking?
What is the most effective defence against AI password cracking?
Shadow AI Security Risks 2026
Prompt Injection in RAG Systems 2026
📚 Further Reading
- AI-Assisted Recon and Attack Surface Mapping 2026 — targeted password cracking depends on the same personal data reconnaissance that AI-assisted recon automates: OSINT on individuals to build targeted cracking wordlists.
- AI-Automated Credential Stuffing 2026 — the downstream use of cracked passwords in automated credential stuffing attacks: how cracked credentials from one breach become attack input for thousands of other services.
- Password Cracking Hub — The SecurityElites password cracking category — traditional hashcat methodology, wordlist construction, and rule writing that provides the baseline context for understanding what AI techniques improve upon.
- NIST SP 800-63B — Digital Identity Guidelines — The authoritative US government guidance on password policy, including current recommendations on length, complexity, rotation, and breach database checking that directly informs AI-resistant password policy design.
- Have I Been Pwned — Pwned Passwords — The breach password database used for HIBP integration — searchable via k-anonymity API, directly integrated into password change flows to prevent selection of already-breached passwords regardless of complexity.