Part of the Metasploitable Lab Series
🎯 What You’ll Master in Lab 3
⏱️ 40 min · 3 exercises · Lab 3 of 10
✅ Before You Start
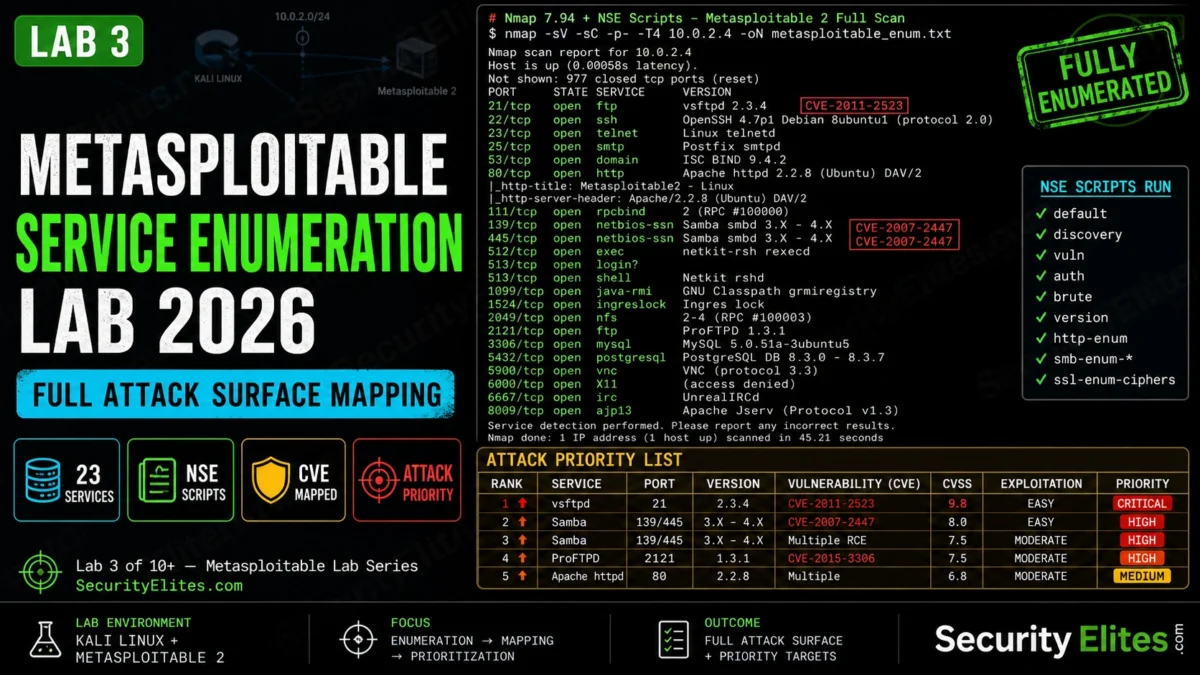
- Lab 2 — Nmap Enumeration — the four-stage scan from Lab 2 confirmed all 23 open ports. Today I take those ports and run targeted NSE scripts to get service versions, CVE indicators, and the full attack surface map.
- Metasploitable 2 running on host-only network · Kali Linux on same host-only adapter · You know Metasploitable’s IP from Lab 2
📋Metasploitable Service Enumeration Lab – Contents
The attack surface I build organises the Metasploitable target for every subsequent lab. After Lab 2’s Nmap scan, this lab adds depth. The full exploitation sequence continues in Lab 4 where I run the first Metasploit module against the highest-priority service found today. The Metasploitable hub has the complete series. Use the Port Scanner Tool to verify port status before each lab.
NSE Scripts — Service-Specific Enumeration
Nmap’s NSE (Nmap Scripting Engine) adds targeted checks on top of basic port scanning. The scripts I run on Metasploitable cover the six highest-value service categories: FTP, SSH, SMB, HTTP, databases, and vulnerability detection. Each script category extracts information the basic version scan misses.
⏱️ 20 minutes · Kali Linux + Metasploitable 2 on host-only network
Run the NSE script chain against each high-priority service. The vsftpd backdoor check and SMB enumeration results will shape the attack plan for Labs 4 and 5.
Step 1: FTP NSE check
nmap -sV -p21 –script ftp-anon,ftp-vsftpd-backdoor TARGET_IP
Did the vsftpd backdoor check trigger? What did it return?
Is anonymous FTP enabled?
Step 2: SMB NSE enumeration
nmap -p139,445 –script smb-os-discovery,smb-enum-shares,smb-security-mode TARGET_IP
What OS did smb-os-discovery return?
What shares are available?
Is SMB signing enforced?
Step 3: HTTP title and enumeration
nmap -p80 –script http-title,http-enum TARGET_IP
List every web path http-enum found.
How many web applications are running on port 80?
Step 4: MySQL empty password check
nmap -p3306 –script mysql-empty-password,mysql-info TARGET_IP
Is the MySQL root account accessible without a password?
What databases are listed?
Step 5: Comprehensive vuln scan
nmap –script vuln -p21,22,23,80,139,445,3306 TARGET_IP -oN vuln_output.txt
cat vuln_output.txt | grep “VULNERABLE\|CVE\|EXPLOIT”
How many vulnerable services does it identify?
Document: full output from each scan. Note: service, version, finding.
📸 Screenshot showing vsftpd backdoor detection result. Share in #metasploitable-labs.
Version Analysis — CVE Mapping
After version detection, I map each service version to known CVEs. The table I build from this mapping is the attack priority list — services ranked by exploitation likelihood and impact, with the Metasploit module path for each.
Web Application Enumeration — Port 80
Port 80 on Metasploitable runs Apache hosting multiple intentionally vulnerable web applications. The http-enum NSE script finds most of them, but I always follow up with direct browsing to understand what’s actually exposed.
⏱️ 15 minutes · Kali + browser
Enumerate every web application running on port 80 and document what attack surface each one offers.
nmap -p80 –script http-enum TARGET_IP
List all paths returned.
Step 2: gobuster directory scan
gobuster dir -u http://TARGET_IP/ -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -t 30 -o web_enum.txt
What paths does gobuster find that http-enum missed?
Step 3: Browse each application
Open browser to each found path.
For each app note:
– What is it? (DVWA, phpMyAdmin, CMS, etc.)
– What are the default credentials? (check online)
– What vulnerability class does it practice?
Step 4: phpMyAdmin — MySQL access
http://TARGET_IP/phpMyAdmin/
Login: root / (empty password)
Does it work?
What databases are visible?
Document: application name, URL path, default credentials, attack surface.
📸 Screenshot showing phpMyAdmin logged in as root. Share in #metasploitable-labs.
Building the Attack Priority Matrix
The attack surface document I build from enumeration organises every finding by exploitation difficulty and impact. This is the reference document I carry through every subsequent lab — it tells me which target to hit when I want to demonstrate a specific technique.
⏱️ 10 minutes · compile and document your findings
Consolidate everything from Labs 2 and 3 into the attack matrix document that drives the rest of the series. This is the deliverable you’d include in a real pentest report’s attack surface section.
For each service/application found, record:
PORT | SERVICE | VERSION | CVE/FINDING | PRIORITY | EXPLOIT METHOD | METASPLOIT MODULE
Template rows (fill in from your scan output):
21 | vsftpd | 2.3.4 | CVE-2011-2523 | CRITICAL | backdoor port 6200 | exploit/unix/ftp/vsftpd_234_backdoor
445 | Samba | 3.0.20 | CVE-2007-2447 | CRITICAL | username map script | exploit/multi/samba/usermap_script
1524 | shell | direct | no CVE needed | CRITICAL | nc TARGET 1524 | manual
[add all others from your scans]
Sort by: CRITICAL first, then HIGH, then MEDIUM.
Final check:
cat attack_matrix.txt
How many CRITICAL priority targets did you find?
Which 3 would you exploit first and why?
📸 Screenshot your completed attack_matrix.txt. Share in #metasploitable-labs.
📋 Lab 3 Command Reference
🏆 Lab 3 Complete — Service Enumeration
NSE script enumeration, CVE mapping, web application discovery, and the attack priority matrix. Lab 4 is where the work pays off — I take the vsftpd 2.3.4 backdoor finding and run the first complete Metasploit module against a real vulnerable service.
🧠 Quick Check
❓ Frequently Asked Questions
What services run on Metasploitable 2?
What is the vsftpd 2.3.4 backdoor?
How do you enumerate SMB on Metasploitable?
What web applications are on Metasploitable port 80?
What Nmap NSE scripts are most useful for Metasploitable?
What is the attack priority order for Metasploitable?
Lab 2 — Nmap Enumeration
Lab 4 — Metasploit First Module
📚 Further Reading
- Lab 2 — Nmap Enumeration — The four-stage scan that produced the port list this lab’s NSE scripts build on. Required context for understanding why each NSE script targets the specific ports it does.
- Metasploitable Lab Series Hub — All 10 labs in sequence. The service enumeration output from Lab 3 is referenced in Labs 4 through 10 — every exploitation lab targets a service identified here.
- Port Scanner Tool — Quick external port verification before starting any Metasploitable lab session — confirms the target is up and the host-only interface is correctly configured.
- Nmap NSE Documentation — The complete NSE script library reference. Every script used in this lab is documented here with parameters, output examples, and category classification for building targeted scan commands.
- Rapid7 Vulnerability Database — The CVE database behind Metasploit module targeting. Look up each CVE found in your enumeration output to understand the vulnerability details and available exploitation options.