Bug Bounty Hunting
Start your bug bounty hunting journey with complete beginner-to-advanced tutorials on finding and reporting vulnerabilities. Learn reconnaissance techniques, subdomain enumeration, Google dorking, automation tools, and vulnerability validation methods used by top bug bounty hunters. This section also includes real bug bounty case studies, report writing tips, and platform guides like HackerOne and Bugcrowd to help you earn rewards by ethically reporting security flaws.
89 articles
XXE Injection Bug Bounty 2026 — Day 13 Hack Server Files via XML
Master XXE injection bug bounty 2026 — find XML external entity vulnerabilities, read server files, SSRF via XXE, blind XXE…
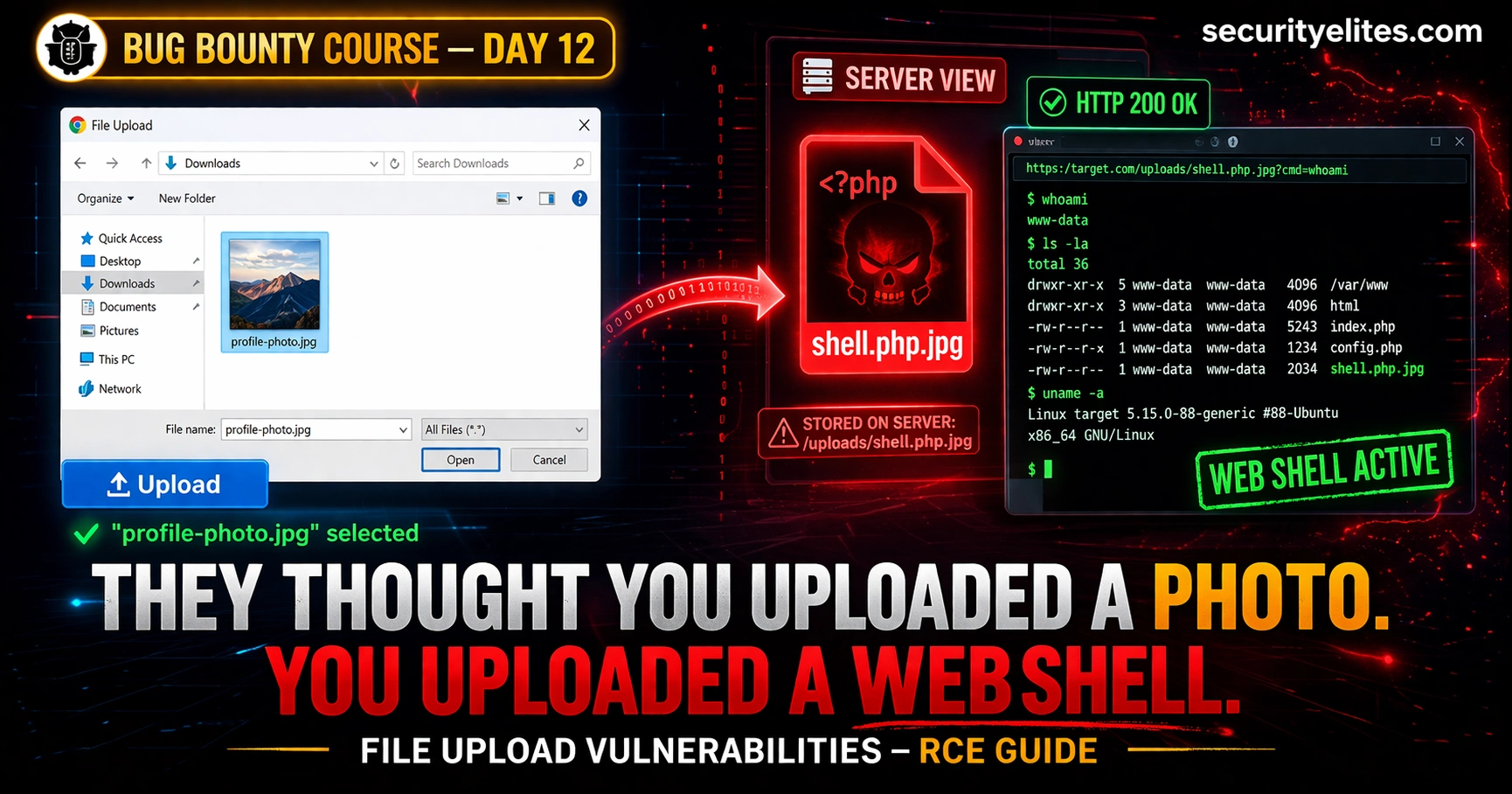
Day 12: File Upload Vulnerabilities — From Bypassing Filters to Remote Code Execution (Bug Bounty 2026)
File upload vulnerabilities bug bounty are among the highest-paying bugs in bounty programs. Day 12 covers every bypass technique—from MIME…
Day 11: Open Redirect Bug Bounty Hunting 2026 — Find, Chain and Report the Vulnerability That Turns $200 Bugs Into $5,000 Findings
Day 11 of 60. Master open redirect bug bounty hunting with manual testing, bypass techniques, OAuth chaining for account takeover,…
Day 10: SSRF — Server-Side Request Forgery Hunting (2026 Bug Bounty Complete Guide)
Day 10 of 60. Learn SSRF bug bounty hunting — discover server-side request forgery vulnerabilities, cloud metadata exploitation, blind SSRF…
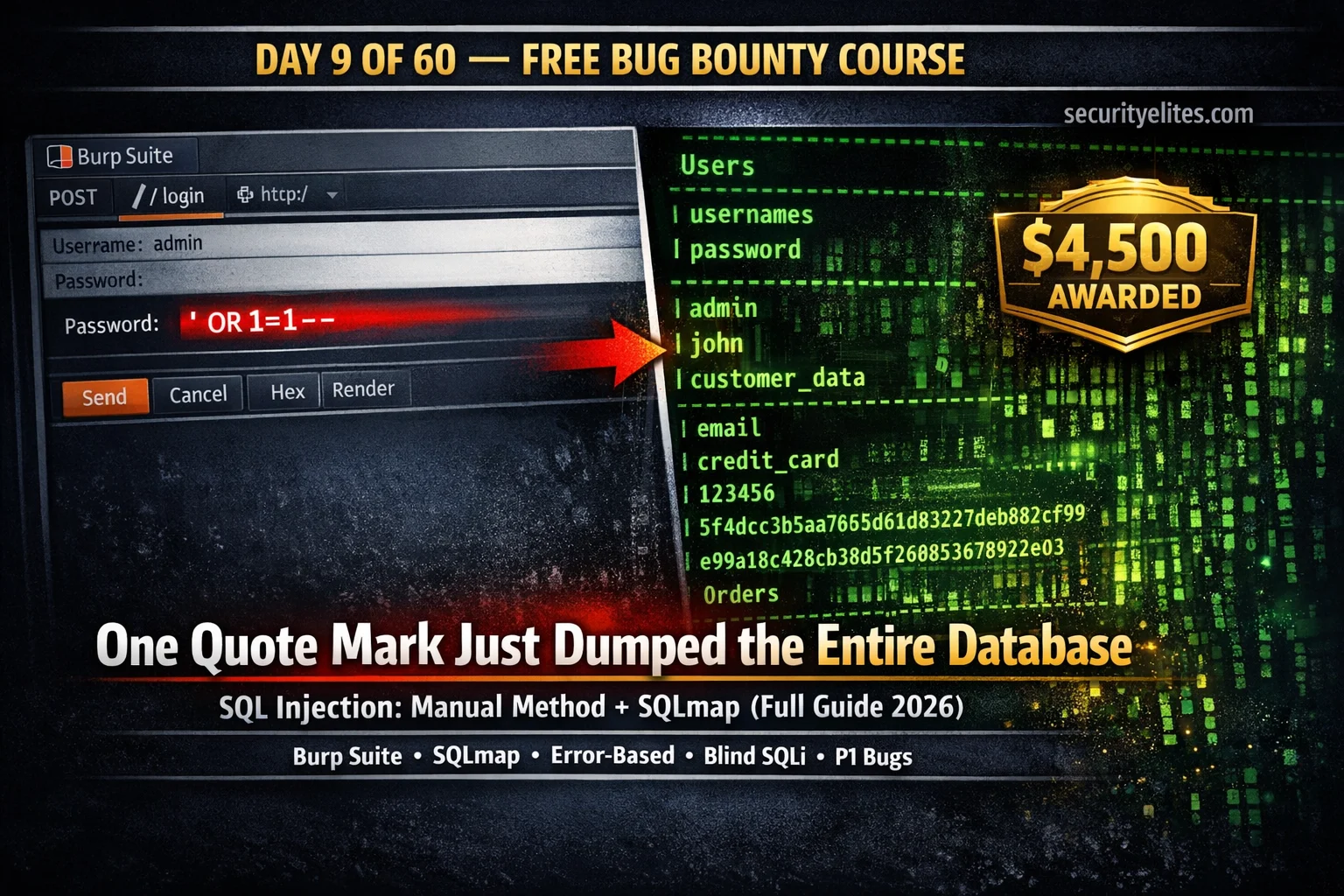
Day 9: SQL Injection for Bug Bounty 2026 — Manual Testing + SQLmap Complete Guide
Day 9 of 60. Learn SQL injection for bug bounty: manual testing with Burp Suite, error-based, UNION-based, blind SQLi, SQLmap…
Passive vs Active Reconnaissance — 90% of Beginners Do This Wrong (2026 Hacker Guide)
Master Passive vs Active Reconnaissance for ethical hacking and bug bounty. Learn passive recon (OSINT, WHOIS, certificate transparency) vs active…
Day 8: IDOR Bug Bounty Hunting — Find Insecure Direct Object Reference Vulnerabilities That Pay (2026)
Complete IDOR bug bounty hunting guide — what IDOR is, horizontal vs vertical privilege escalation, where to find IDORs, Burp…
Metasploit Tutorial for Beginners 2026 — First Exploit to Root Shell in Your Home Lab (Step-by-Step)
The complete Metasploit tutorial for beginners 2026 — covering msfconsole basics, finding exploits, setting payloads, Meterpreter commands, post-exploitation, and a…
Day 7: XSS Bug Bounty Hunting — Find, Exploit & Report Cross-Site Scripting Bugs That Pay (2026)
Complete XSS bug bounty hunting guide — where to find reflected, stored, and DOM XSS, Burp Suite Repeater workflow, filter…