Bug Bounty Hunting
Start your bug bounty hunting journey with complete beginner-to-advanced tutorials on finding and reporting vulnerabilities. Learn reconnaissance techniques, subdomain enumeration, Google dorking, automation tools, and vulnerability validation methods used by top bug bounty hunters. This section also includes real bug bounty case studies, report writing tips, and platform guides like HackerOne and Bugcrowd to help you earn rewards by ethically reporting security flaws.
89 articles
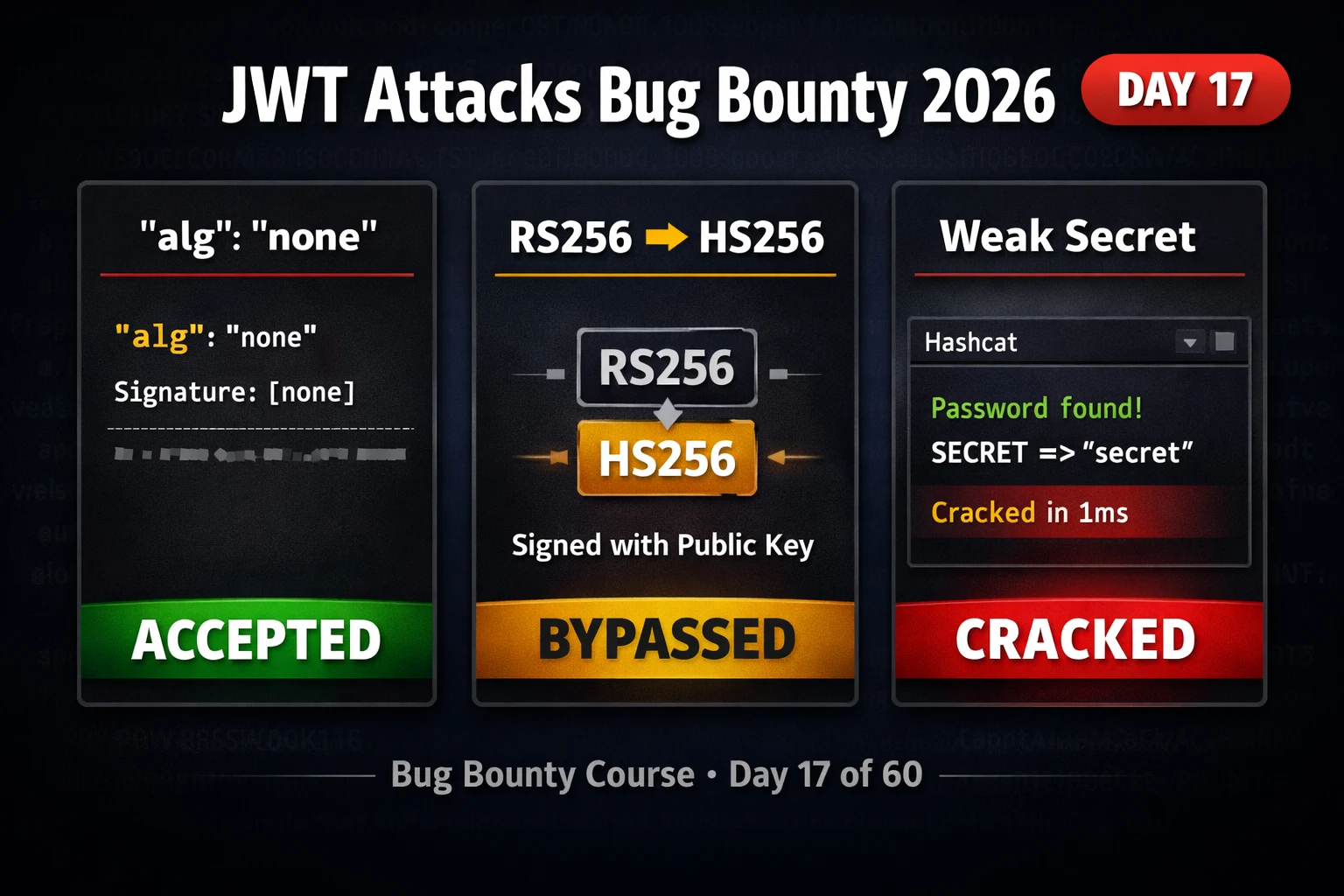
BB Day17: JWT Attacks Bug Bounty 2026 — Algorithm Confusion, None Attack & Weak Secrets
JWT attacks bug bounty 2026 — exploit algorithm confusion, none attack, weak signing secrets and kid injection in JSON web…
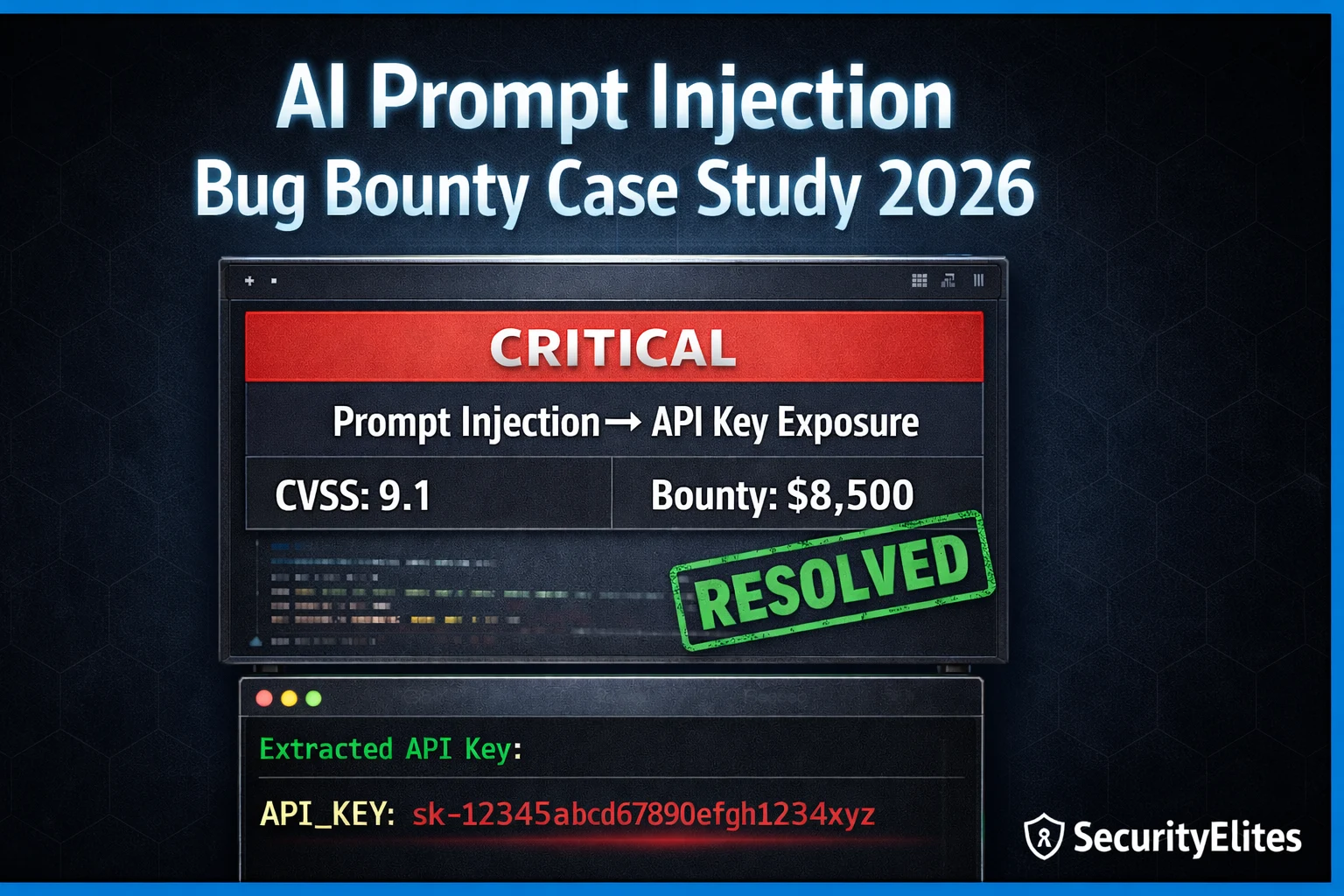
I Hacked a Company Using Only AI Prompts — Real Bug Bounty Case Study 2026
Real AI prompt injection bug bounty case study 2026 — how a single injected prompt extracted API keys, bypassed authentication,…
How to Use Shodan 2026 — The Hacker’s Search Engine Complete Guide
How to use shodan 2026 — search internet-connected devices, find exposed services, use Shodan dorks for bug bounty recon and…
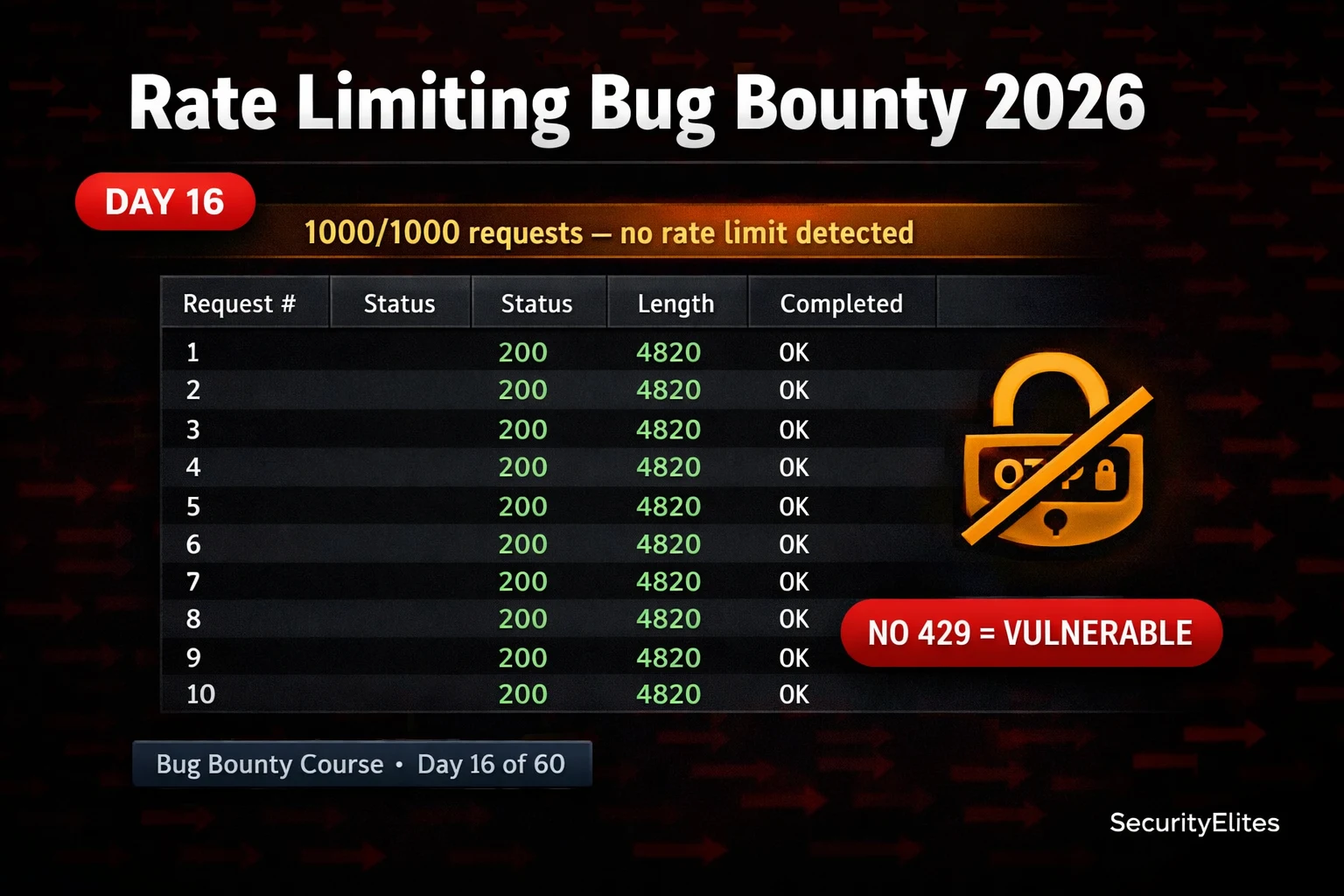
BB Day16: Rate Limiting Bug Bounty 2026 — Find Bypass Flaws in Login, OTP and API Endpoints
Rate limiting bug bounty 2026 — find and exploit missing or bypassable rate limits on login, OTP, password reset and…
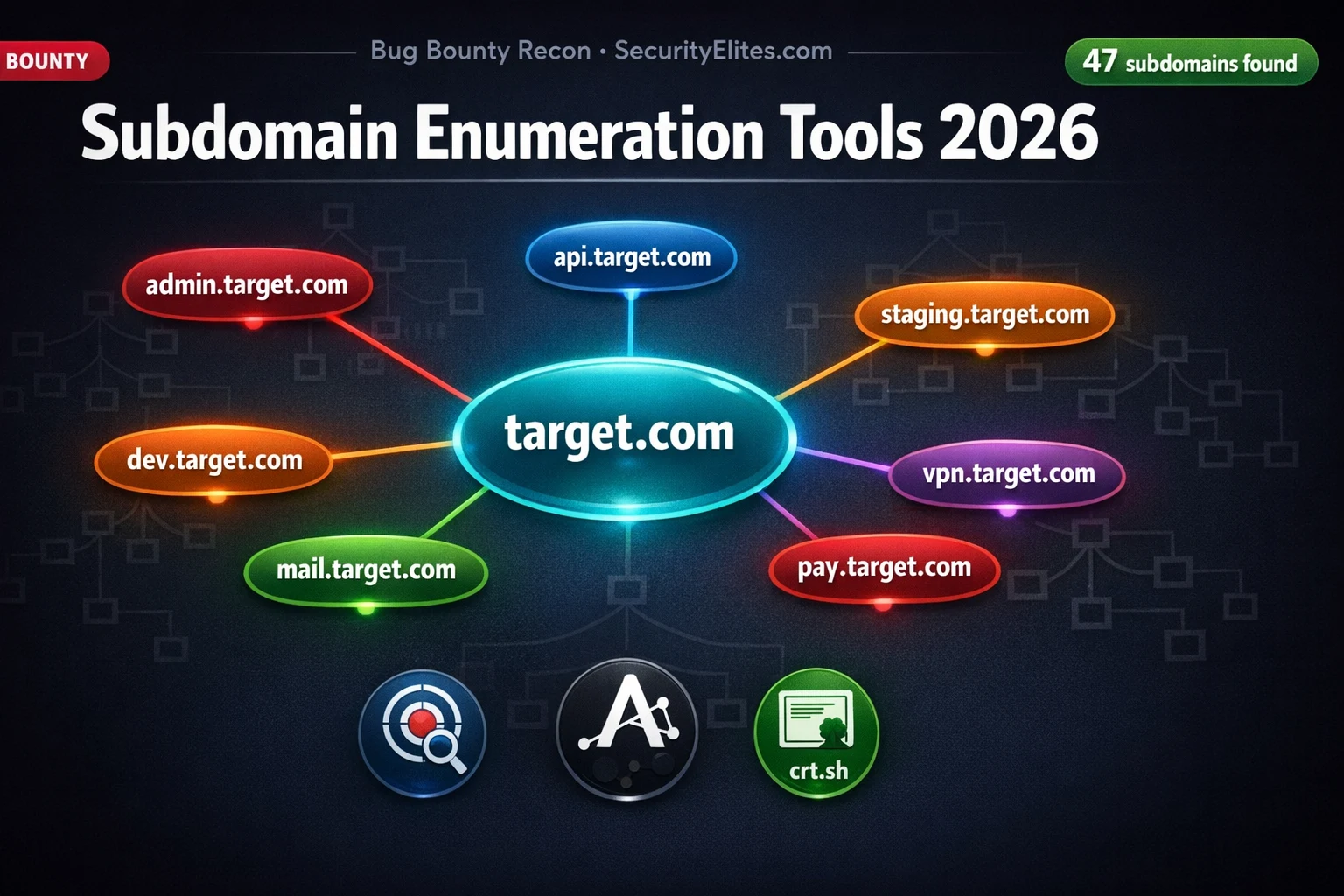
Subdomain Enumeration Tools 2026 — 7 Best Methods to Find Every Hidden Subdomain
Subdomain enumeration tools 2026 — best methods using Subfinder, Amass, Assetfinder, crt.sh and Google dorks to find every hidden subdomain…
Google Dorking for Hackers 2026 — 50 Dorks to Find Vulnerabilities and Exposed Data
Google dorking for hackers 2026 — 50 essential Google dorks to find exposed admin panels, config files, passwords, subdomains and…
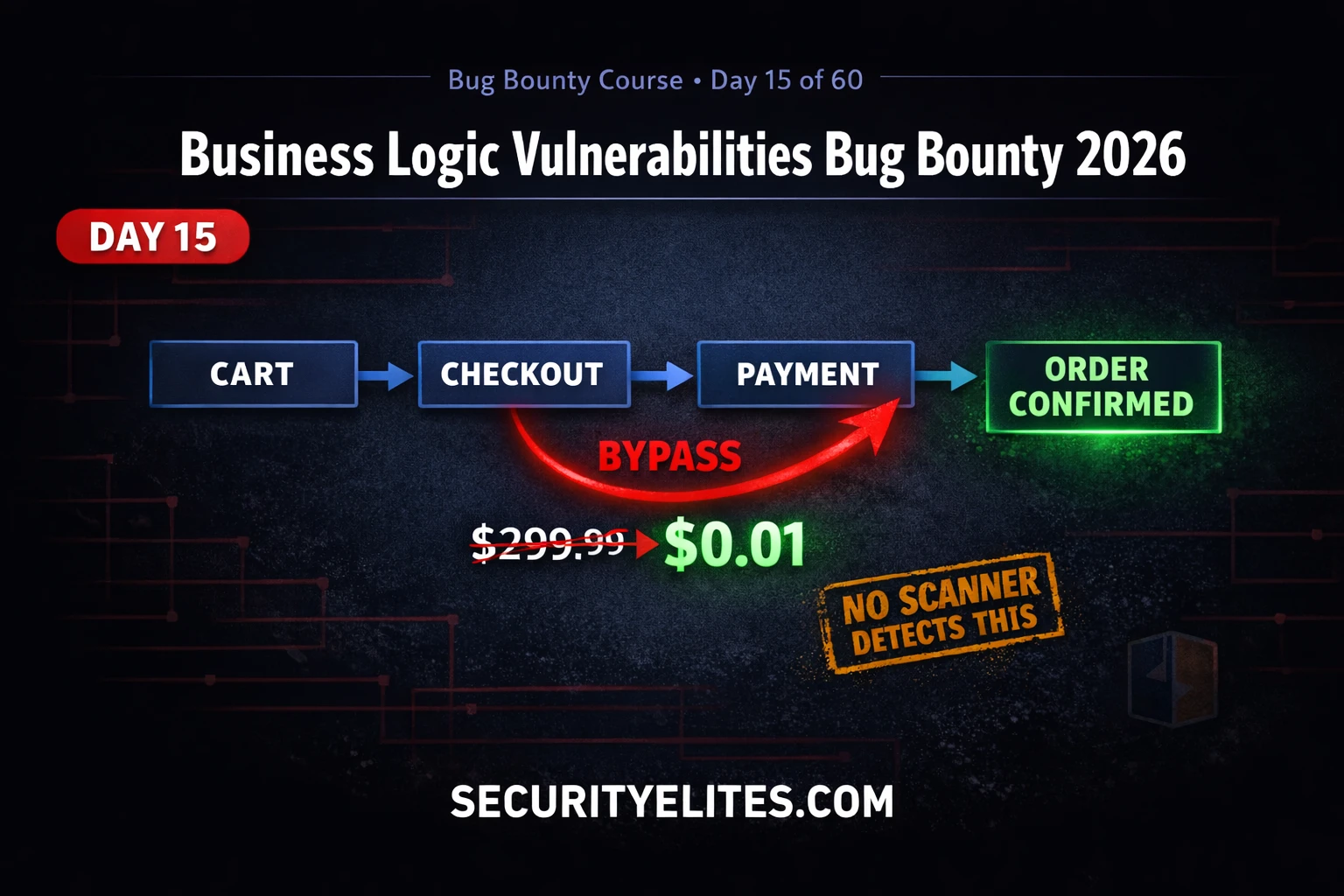
BB Day15: Business Logic Vulnerabilities Bug Bounty 2026 — Bypass Payment Like a Hacker
Business logic vulnerabilities bug bounty 2026 — find price manipulation, workflow bypass and privilege escalation flaws that scanners miss. Day…
How to Hack AWS S3 Buckets (Ethically) 2026 — 5 Real Misconfigurations Exposed
Hack aws s3 buckets ethically 2026 — discover 5 real S3 misconfigurations, enumerate public buckets, test ACL weaknesses and report…
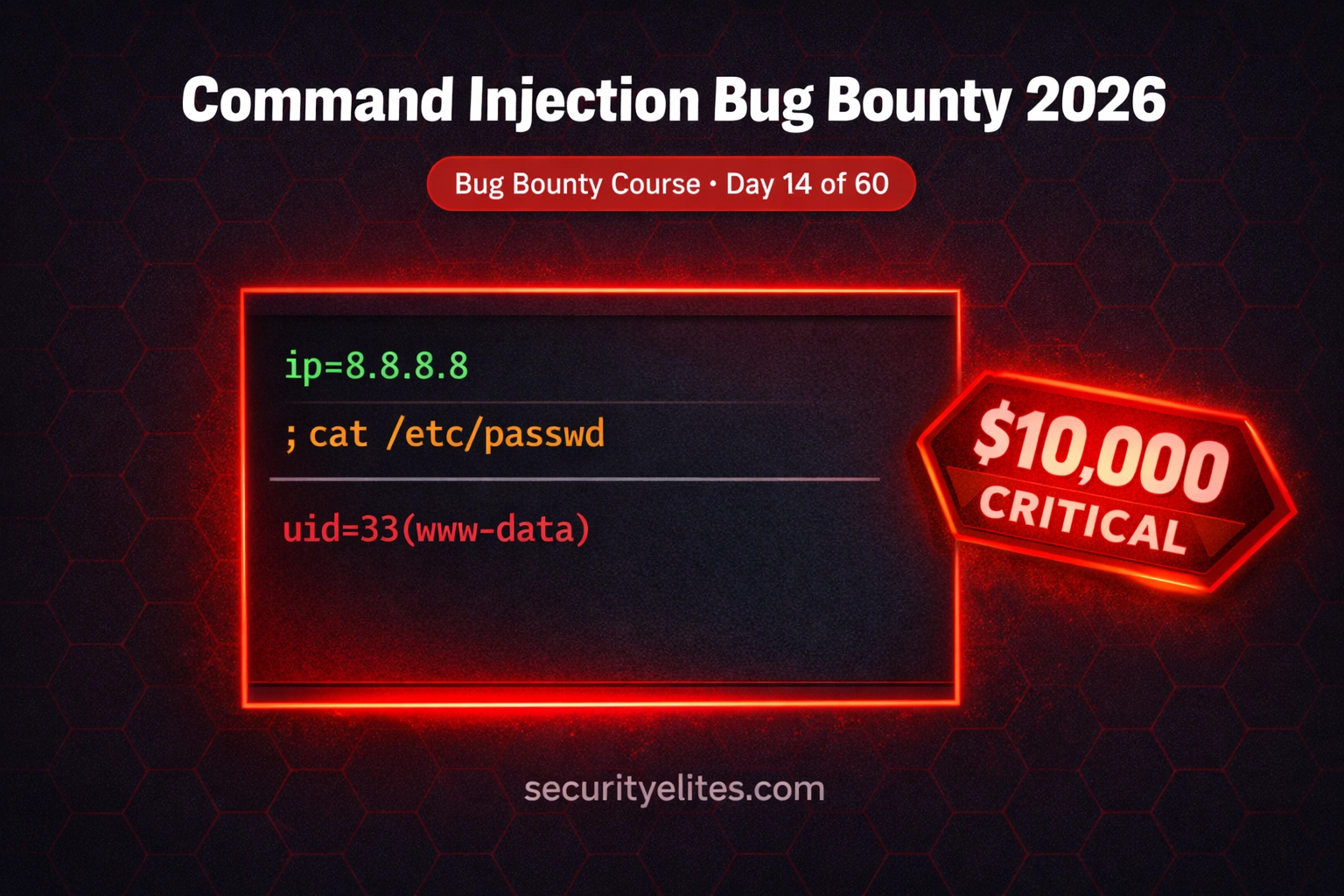
BB Day 14: Command Injection Bug Bounty 2026 — Find OS Injection in Web Apps & APIs That Pay
Command injection bug bounty 2026 — find OS command injection in web apps and APIs, bypass filters, chain with SSRF…