Web Application Security
Explore web application security vulnerabilities and learn how ethical hackers identify and exploit them. This category covers SQL injection, cross-site scripting (XSS), CSRF, file upload vulnerabilities, authentication bypass, API security flaws, and session management issues. You’ll find hands-on tutorials, payload examples, exploitation labs, and prevention techniques to secure web applications. Ideal for bug bounty hunters, penetration testers, and developers who want to build and test secure web platforms.
100 articles
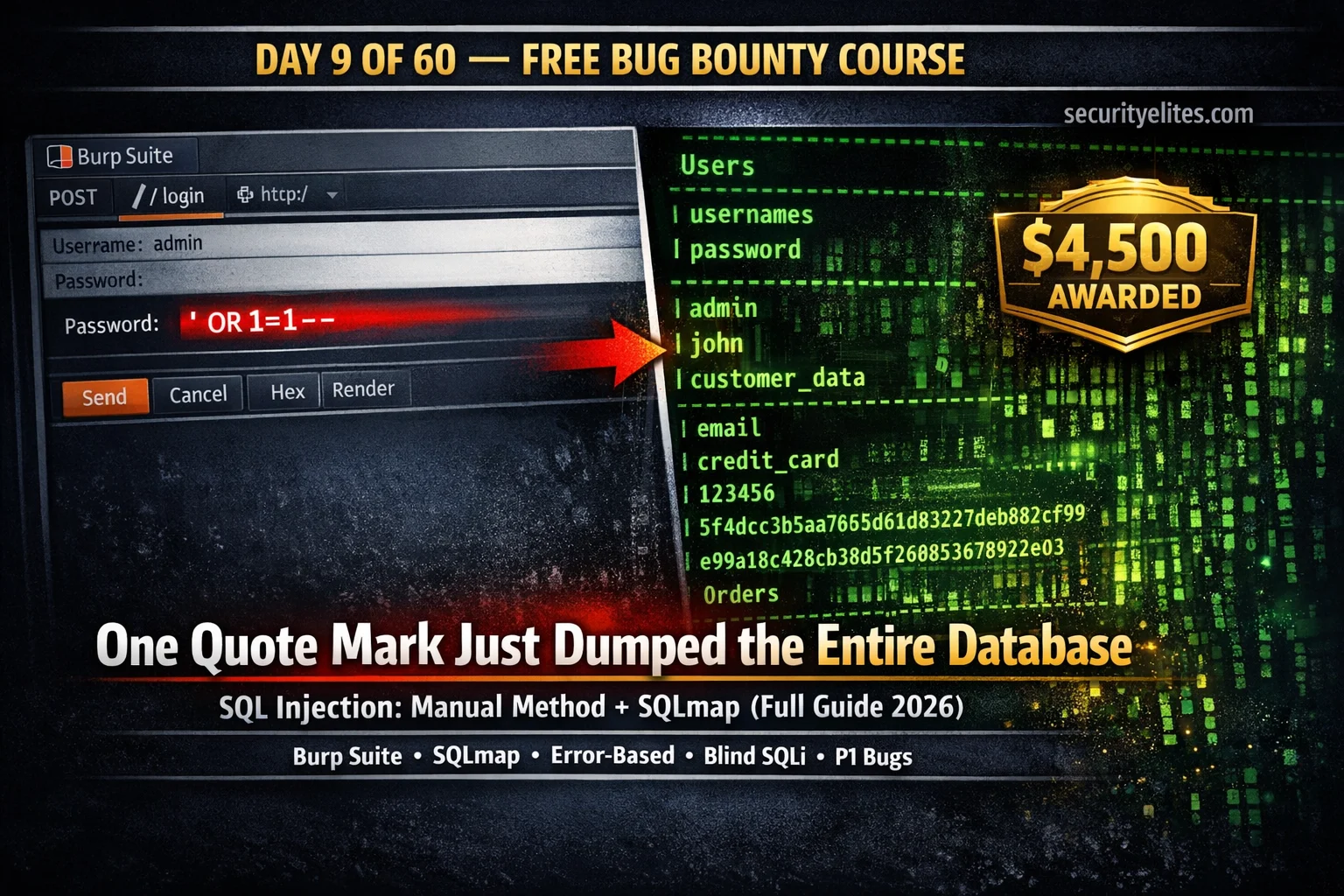
Day 9: SQL Injection for Bug Bounty 2026 — Manual Testing + SQLmap Complete Guide
Day 9 of 60. Learn SQL injection for bug bounty: manual testing with Burp Suite, error-based, UNION-based, blind SQLi, SQLmap…
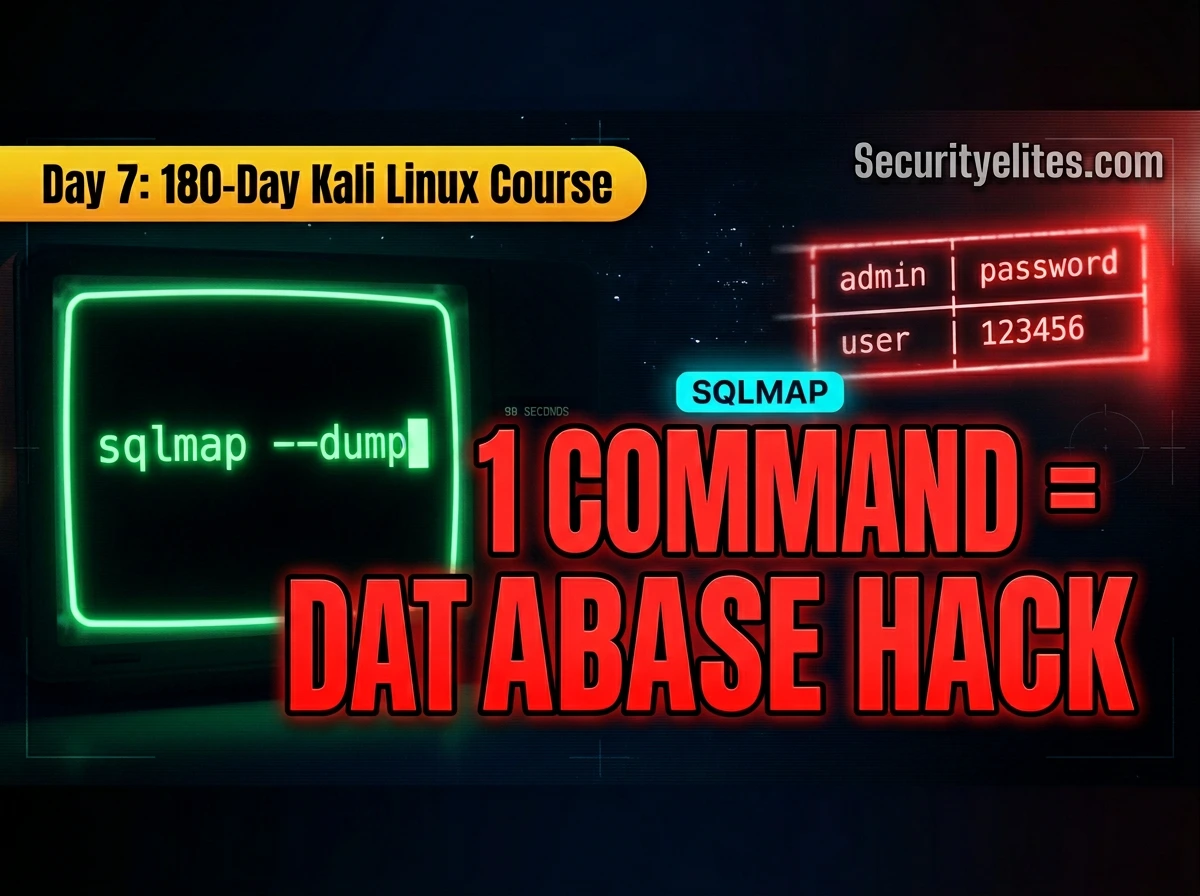
Kali Linux Day 7: SQLmap Tutorial (2026) — Automate SQL Injection Like a Pro 🔥
Complete SQLmap tutorial for Kali Linux — detect SQL injection, enumerate databases, extract tables, dump credentials, use Burp request files,…
Kali Linux Day 6: Nikto Tutorial (Kali Linux 2026): Find CRITICAL Web Server Vulnerabilities in Minutes
Complete Nikto tutorial for Kali Linux: learn basic scans, HTTPS testing, output formats, tuning categories, evasion techniques, authentication, and a…
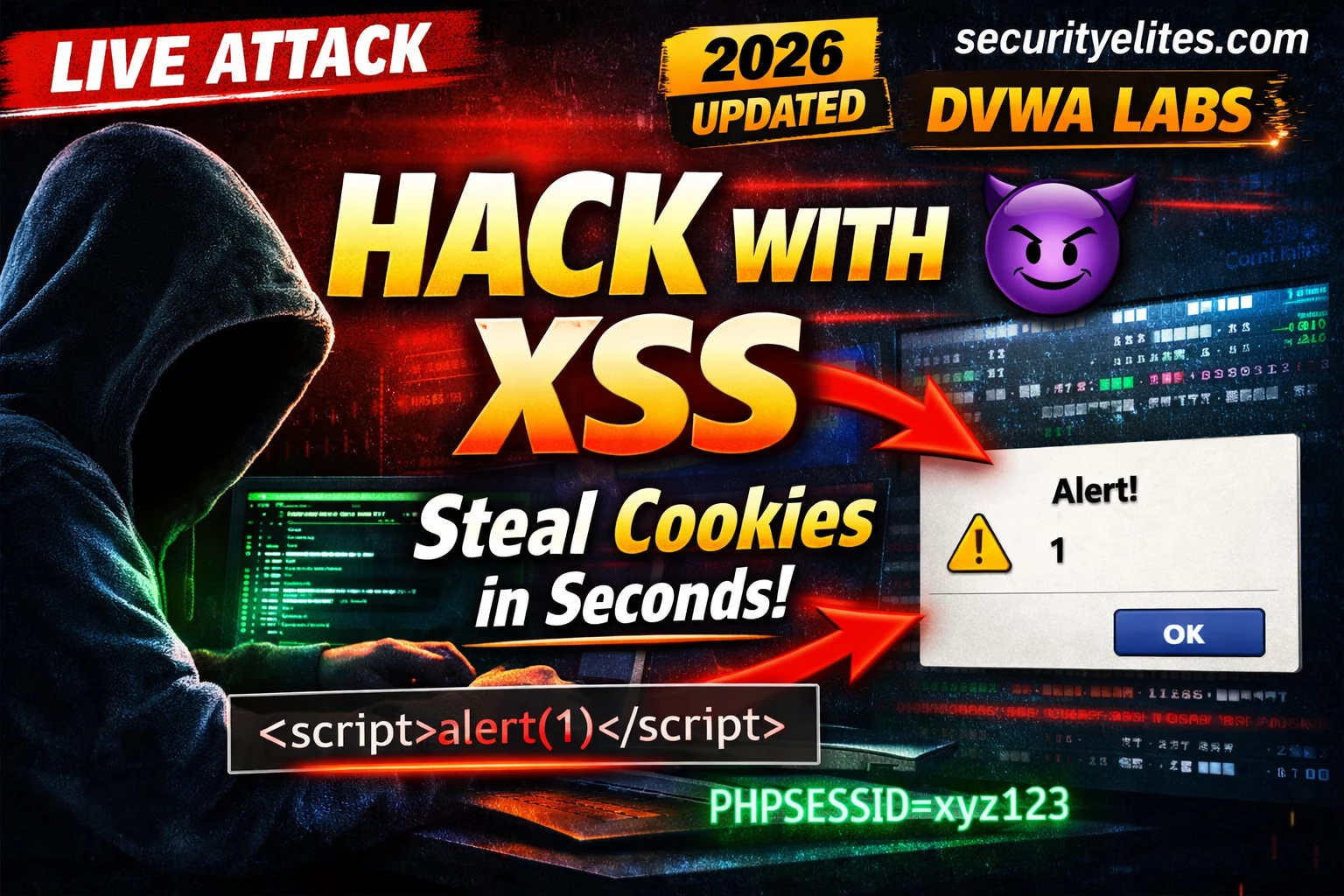
XSS Cross Site Scripting Tutorial 2026 — Hack Any Website? 3 Types, Real Payloads & DVWA Labs (Beginner to Pro)
Complete XSS Cross Site scripting tutorial for beginners—learn how cross site scripting works, including all three types (Reflected, Stored, and…
Day 8: IDOR Bug Bounty Hunting — Find Insecure Direct Object Reference Vulnerabilities That Pay (2026)
Complete IDOR bug bounty hunting guide — what IDOR is, horizontal vs vertical privilege escalation, where to find IDORs, Burp…
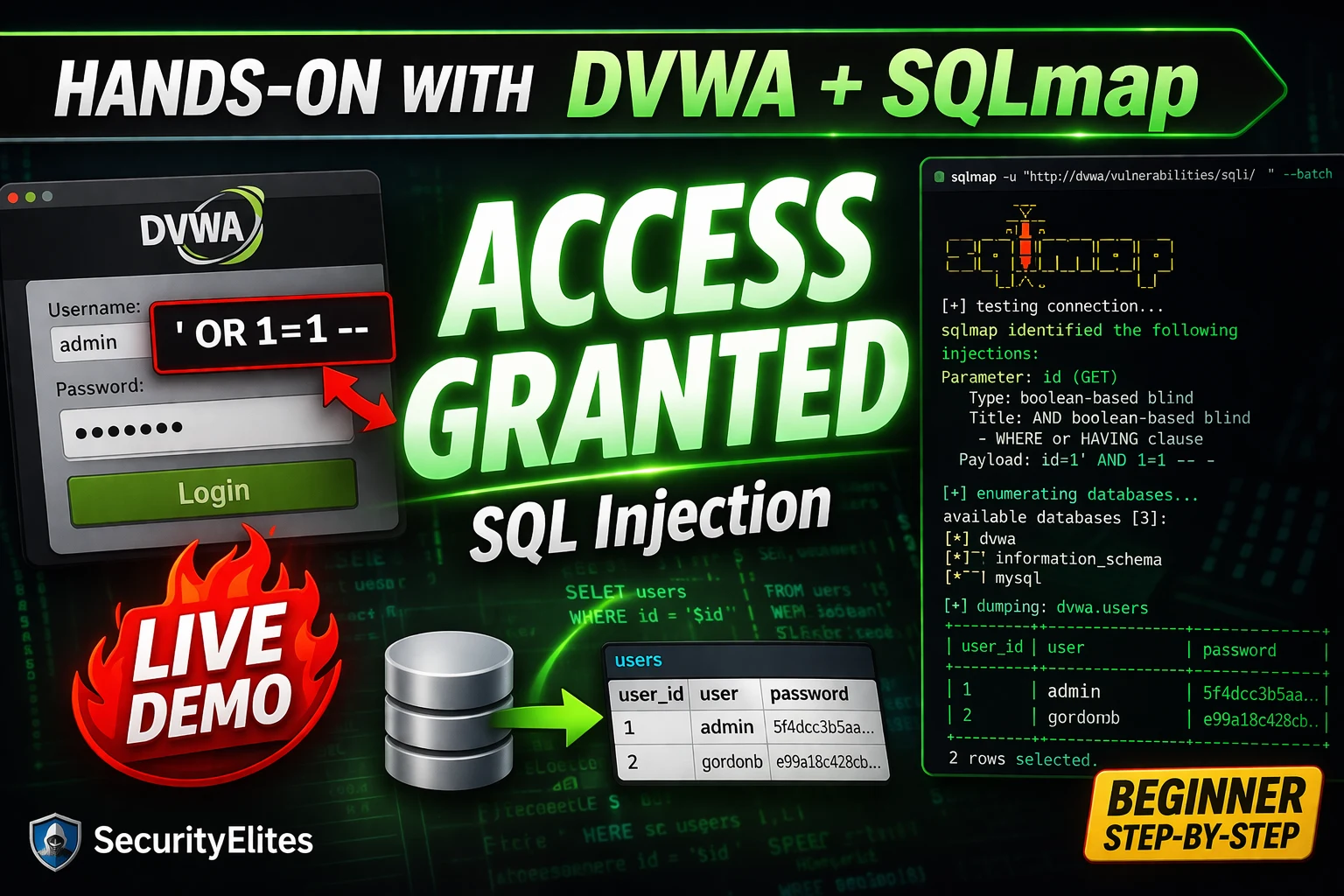
SQL Injection Tutorial for Beginners 2026 — From First Quote to Database Dump (Hands-On with DVWA + SQLmap)
SQL injection Tutorial from scratch in 2026 — what it is, why it works, manual exploitation step-by-step, DVWA lab setup,…
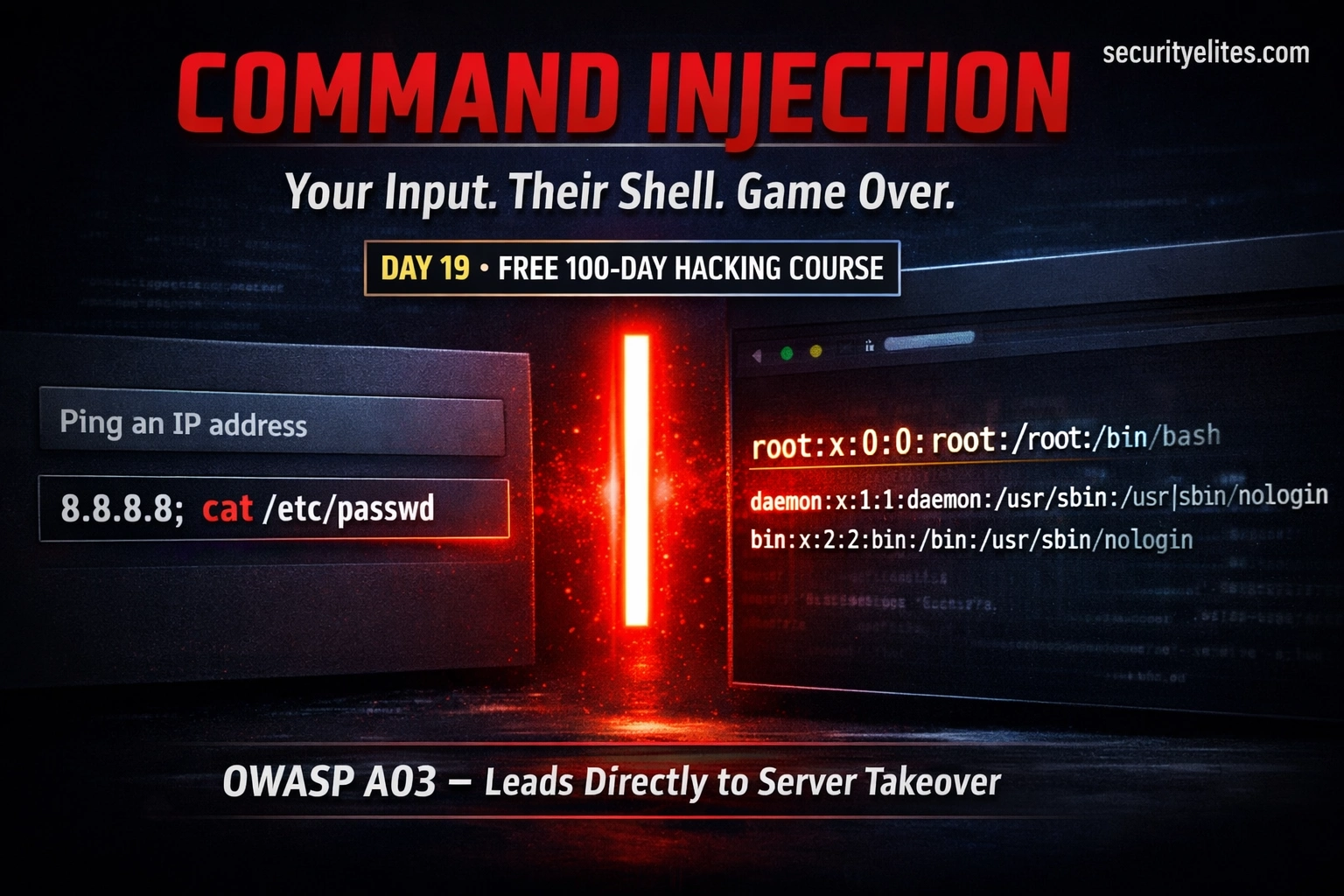
Day 19: Command Injection — When User Input Reaches the OS Shell (2026)
Day 19 of 100. Learn OS command injection, shell metacharacters, blind injection, DVWA lab walkthrough, and secure coding practices. One…
Day 7: XSS Bug Bounty Hunting — Find, Exploit & Report Cross-Site Scripting Bugs That Pay (2026)
Complete XSS bug bounty hunting guide — where to find reflected, stored, and DOM XSS, Burp Suite Repeater workflow, filter…
Day 18: File Upload Vulnerabilities — From Image Upload to Web Shell (2026)
Understand file upload vulnerabilities from first principles — how validation is bypassed, how web shells work, full DVWA demos at…