Web Application Security
Explore web application security vulnerabilities and learn how ethical hackers identify and exploit them. This category covers SQL injection, cross-site scripting (XSS), CSRF, file upload vulnerabilities, authentication bypass, API security flaws, and session management issues. You’ll find hands-on tutorials, payload examples, exploitation labs, and prevention techniques to secure web applications. Ideal for bug bounty hunters, penetration testers, and developers who want to build and test secure web platforms.
100 articles
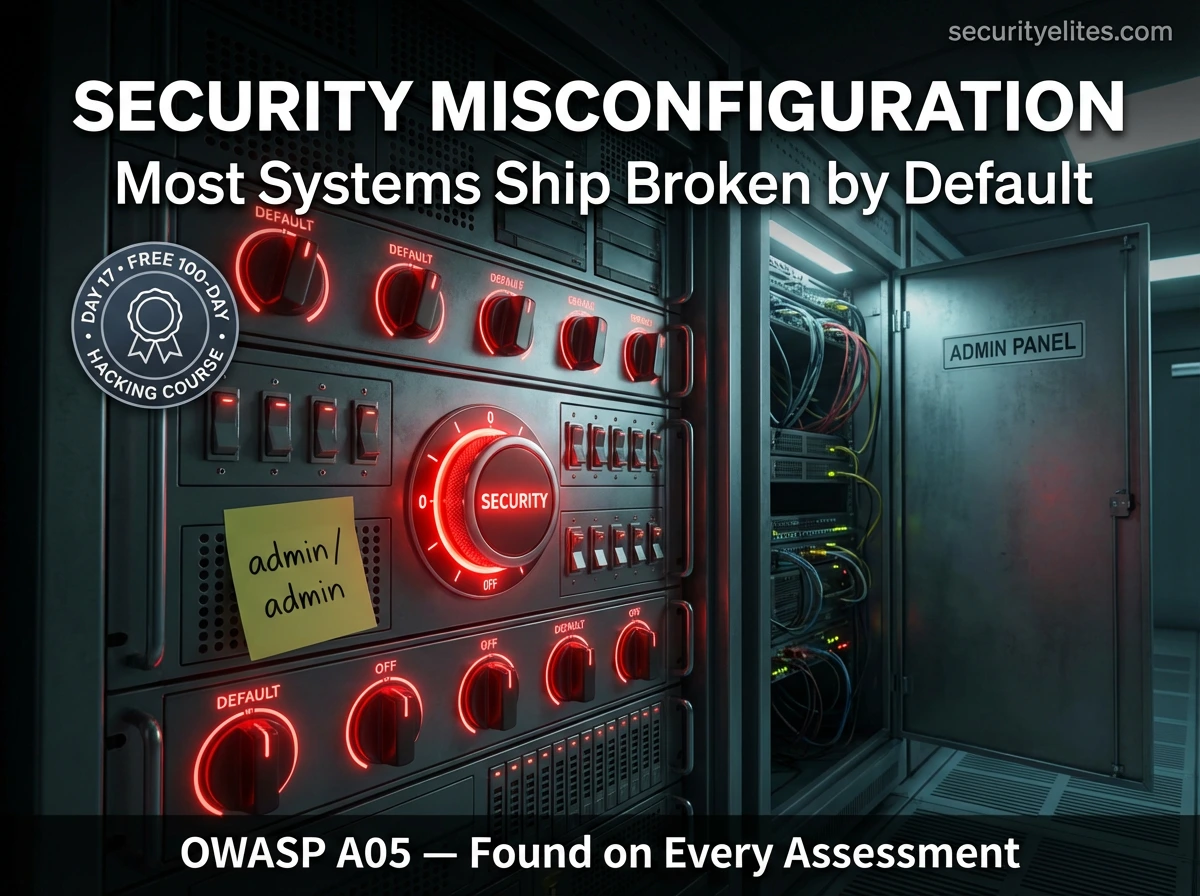
Day 17: Security Misconfiguration — The Easiest Vulnerabilities to Find (2026)
Day 17 of 100. Learn security misconfiguration — default credentials, verbose errors, exposed admin panels, open cloud buckets, directory listing,…
How to Secure Gmail Account From Hackers — The Ultimate 2026 Protection Guide (Block Every Attack)
Complete step-by-step guide on how to secure Gmail account — enabling 2-Step Verification with an authenticator app, reviewing account activity,…
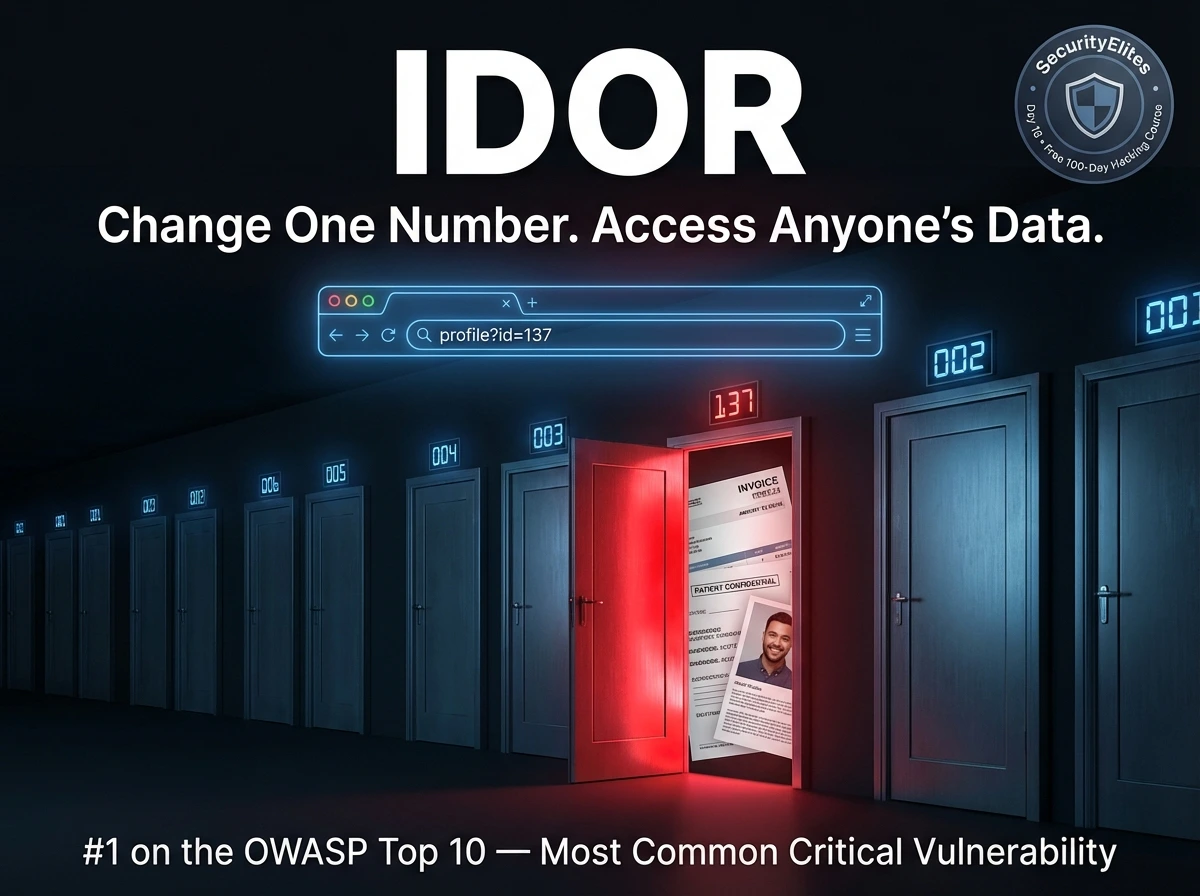
Day 16: Broken Access Control & IDOR — The #1 Web Vulnerability Explained (2026)
Day 16 of 100. Master Broken Access Control — including IDOR, horizontal & vertical privilege escalation, directory traversal, and mass…
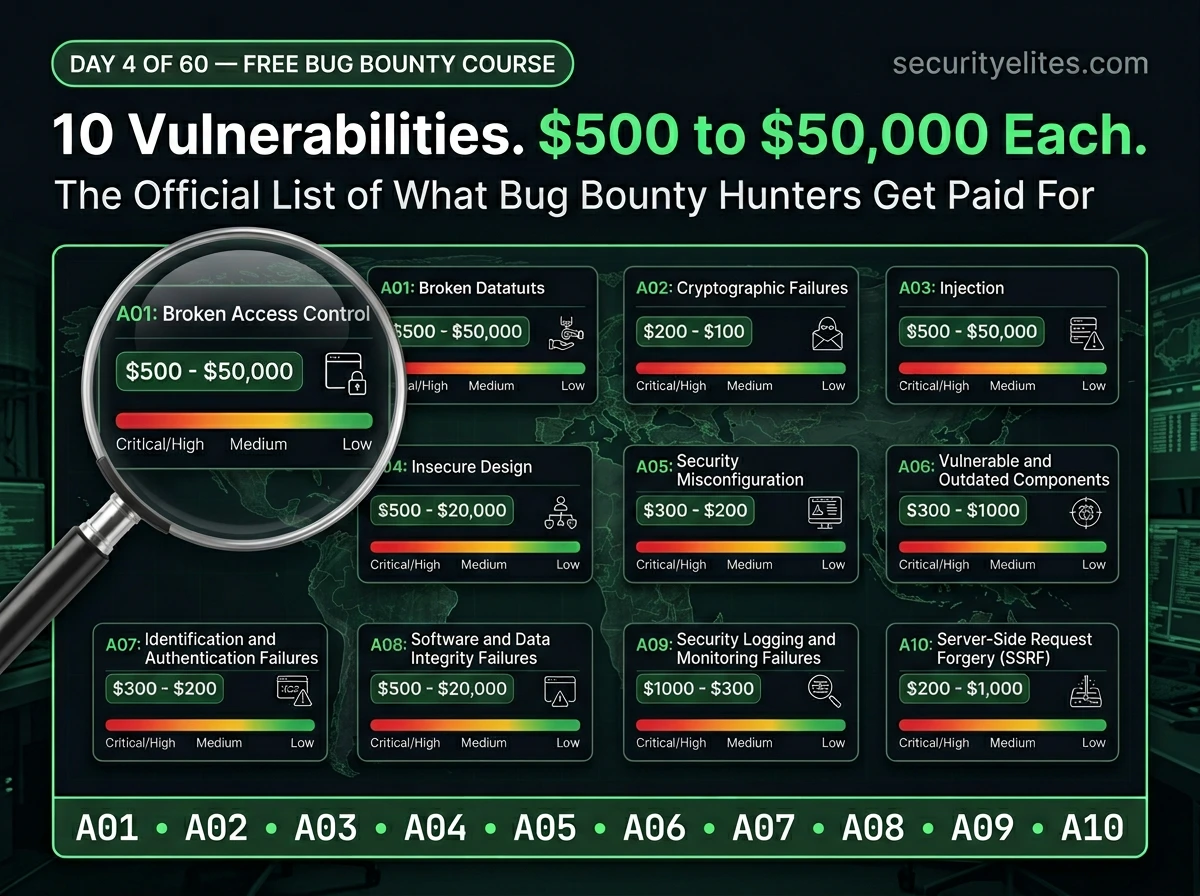
Day 4: OWASP Top 10 Explained — The Official Bug Bounty Vulnerability Map Every Hunter Needs (2026)
Day 4 of 60. Learn the OWASP Top 10 in plain English — what each vulnerability is, how it’s exploited,…
Day 15: CSRF & Authentication Bypass — When Web Requests Get Forged (2026)
Day 15 of 100. CSRF attacks explained, understand authentication bypass — how forged requests exploit user trust, CSRF tokens, SameSite…
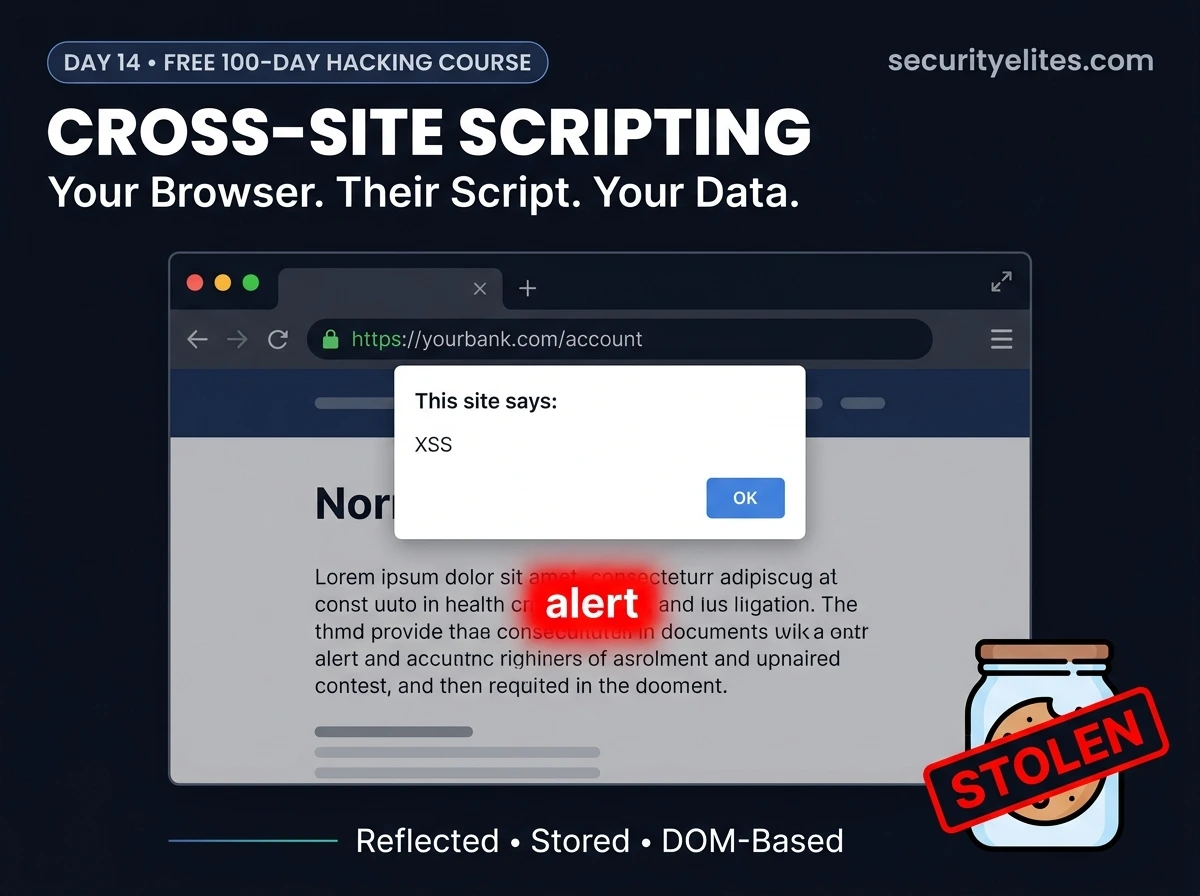
Day 14: XSS Cross-Site Scripting — How Hackers Steal Cookies & Take Over Accounts (2026)
Day 14 of 100. Understand XSS Cross Site Scripting —reflected, stored, and DOM-based—with DVWA demos in Burp Suite, cookie theft…
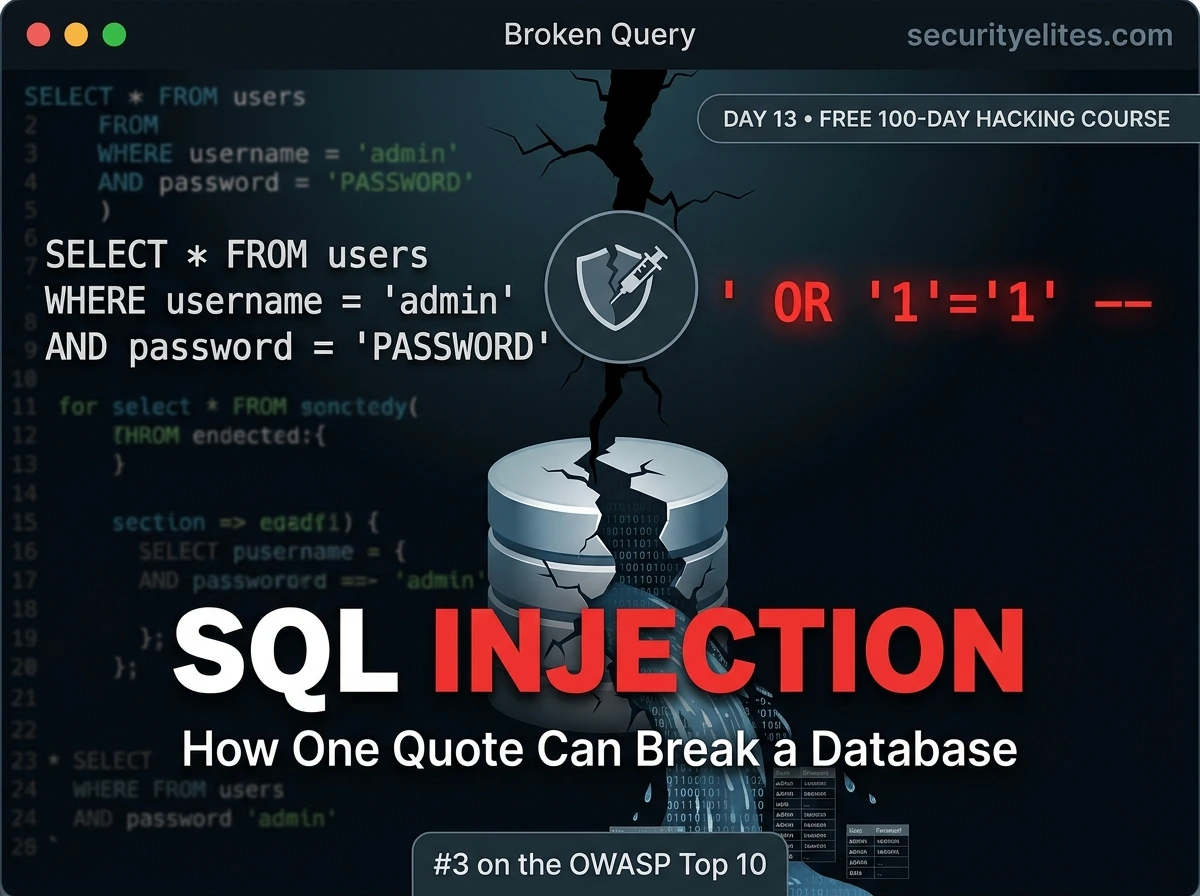
Day 13: SQL Injection Explained — From First Quote to Finding the Vulnerability (2026)
Day 13 of 100. SQL injection tutorial from first principles — how databases work, why injection happens, how to identify…
How Instagram Accounts Actually Get Hacked — And How to Stop It Happening to You (2026)
Learn exactly how Instagram accounts get hacked in 2026 — phishing, credential stuffing, SIM swapping, third-party apps, and more. Understand…
Your Gmail Can Be Hacked Without a Password (2026): 5 Methods & How to Stop Them
Hackers don't need your Gmail password in 2026. Learn the 5 silent attack methods — Your Gmail can be hacked…