Web Application Security
Explore web application security vulnerabilities and learn how ethical hackers identify and exploit them. This category covers SQL injection, cross-site scripting (XSS), CSRF, file upload vulnerabilities, authentication bypass, API security flaws, and session management issues. You’ll find hands-on tutorials, payload examples, exploitation labs, and prevention techniques to secure web applications. Ideal for bug bounty hunters, penetration testers, and developers who want to build and test secure web platforms.
100 articles
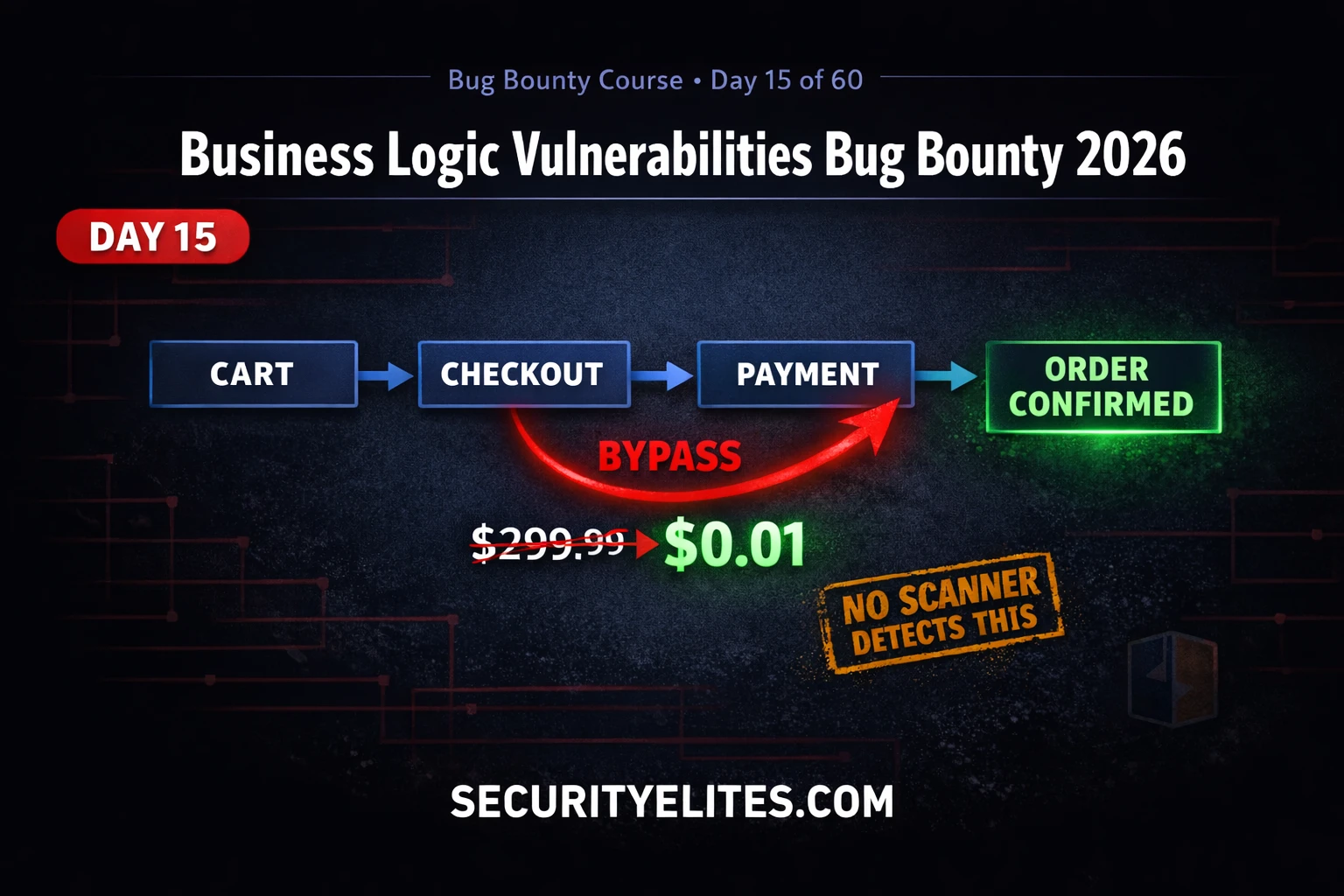
BB Day15: Business Logic Vulnerabilities Bug Bounty 2026 — Bypass Payment Like a Hacker
Business logic vulnerabilities bug bounty 2026 — find price manipulation, workflow bypass and privilege escalation flaws that scanners miss. Day…
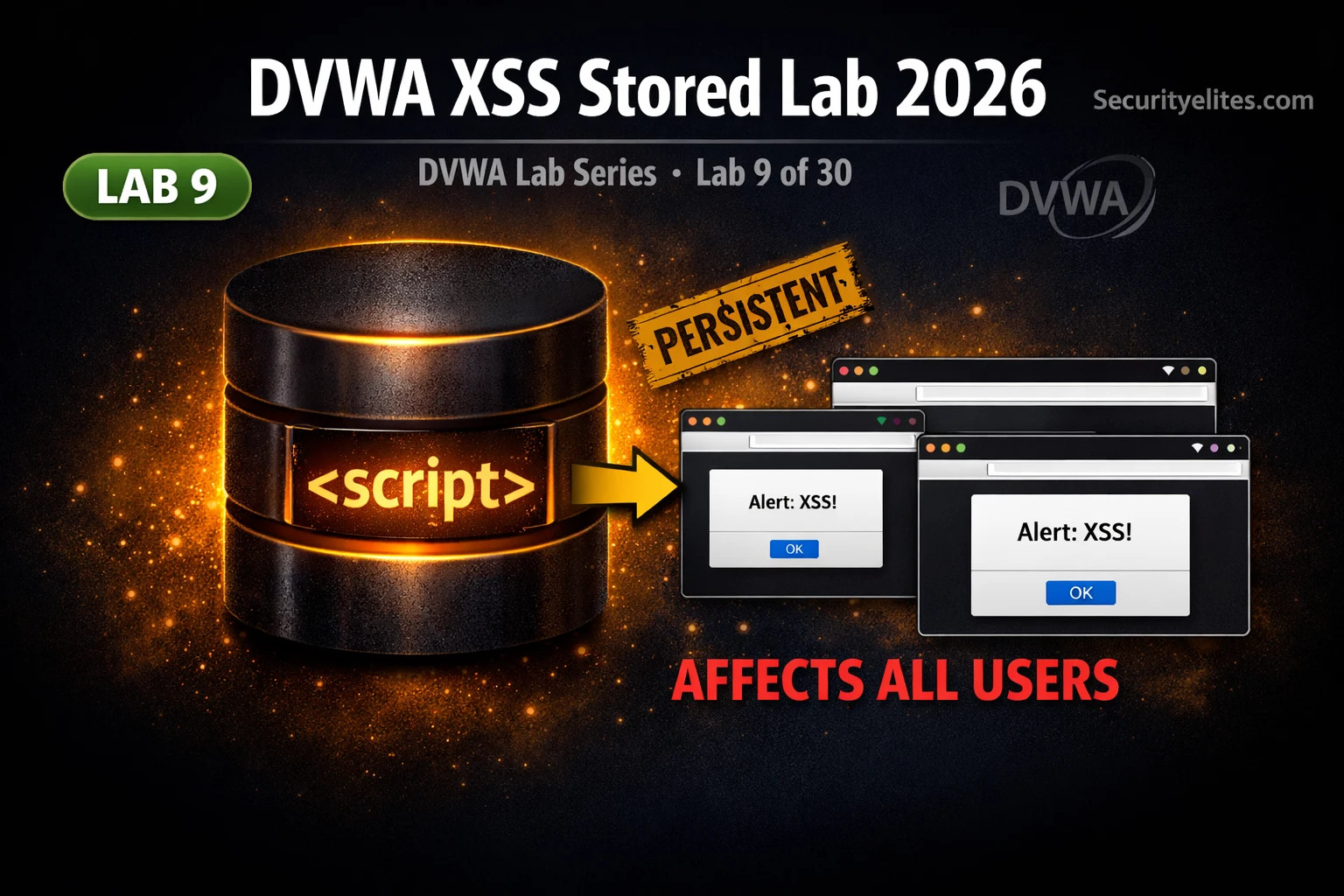
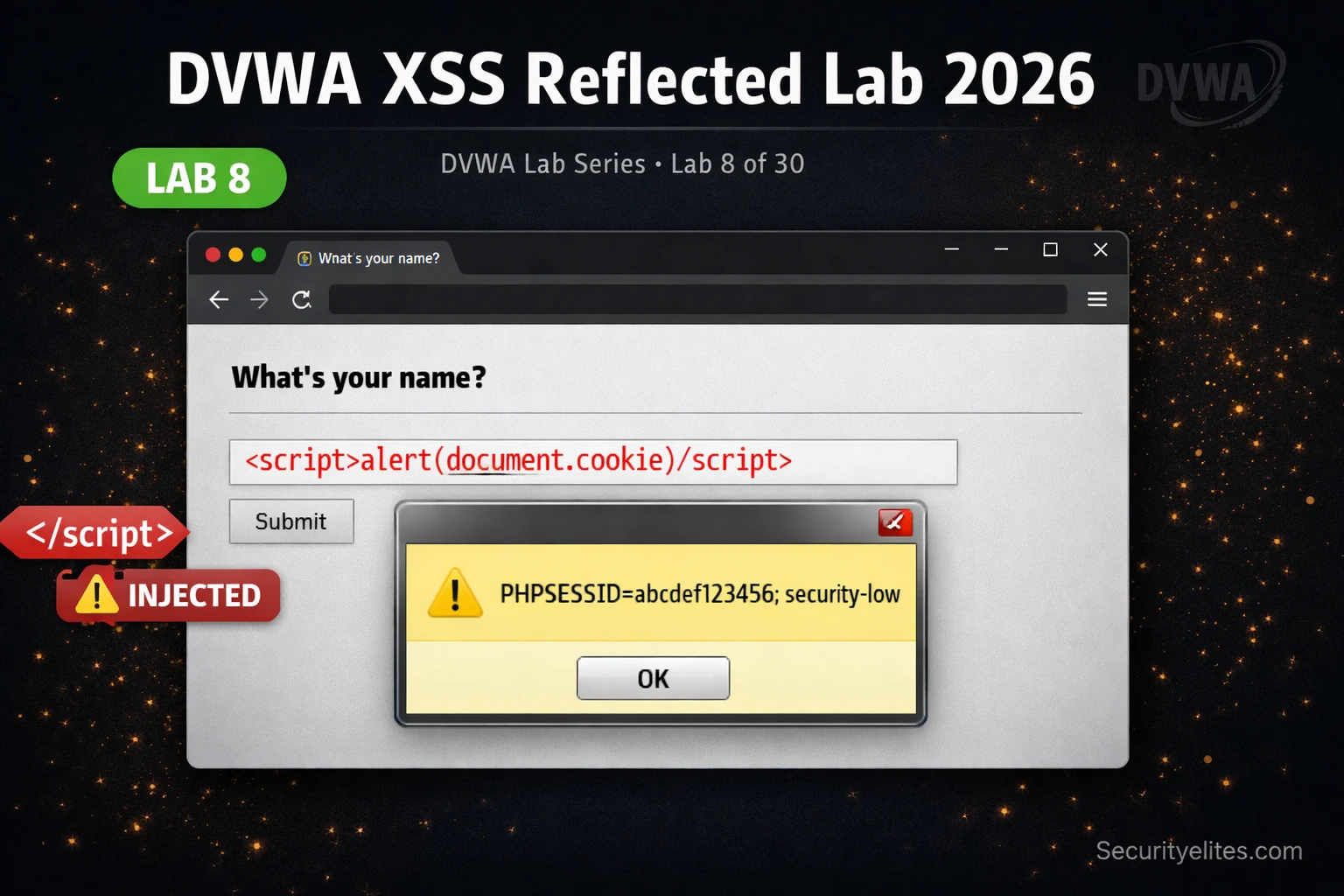
Lab 8: DVWA XSS Reflected Lab 2026 — Steal Cookies in Seconds & Bypass Filters Like a Hacker
DVWA xss reflected lab 2026 — inject JavaScript payloads at all 4 security levels, steal session cookies with Burp, bypass…
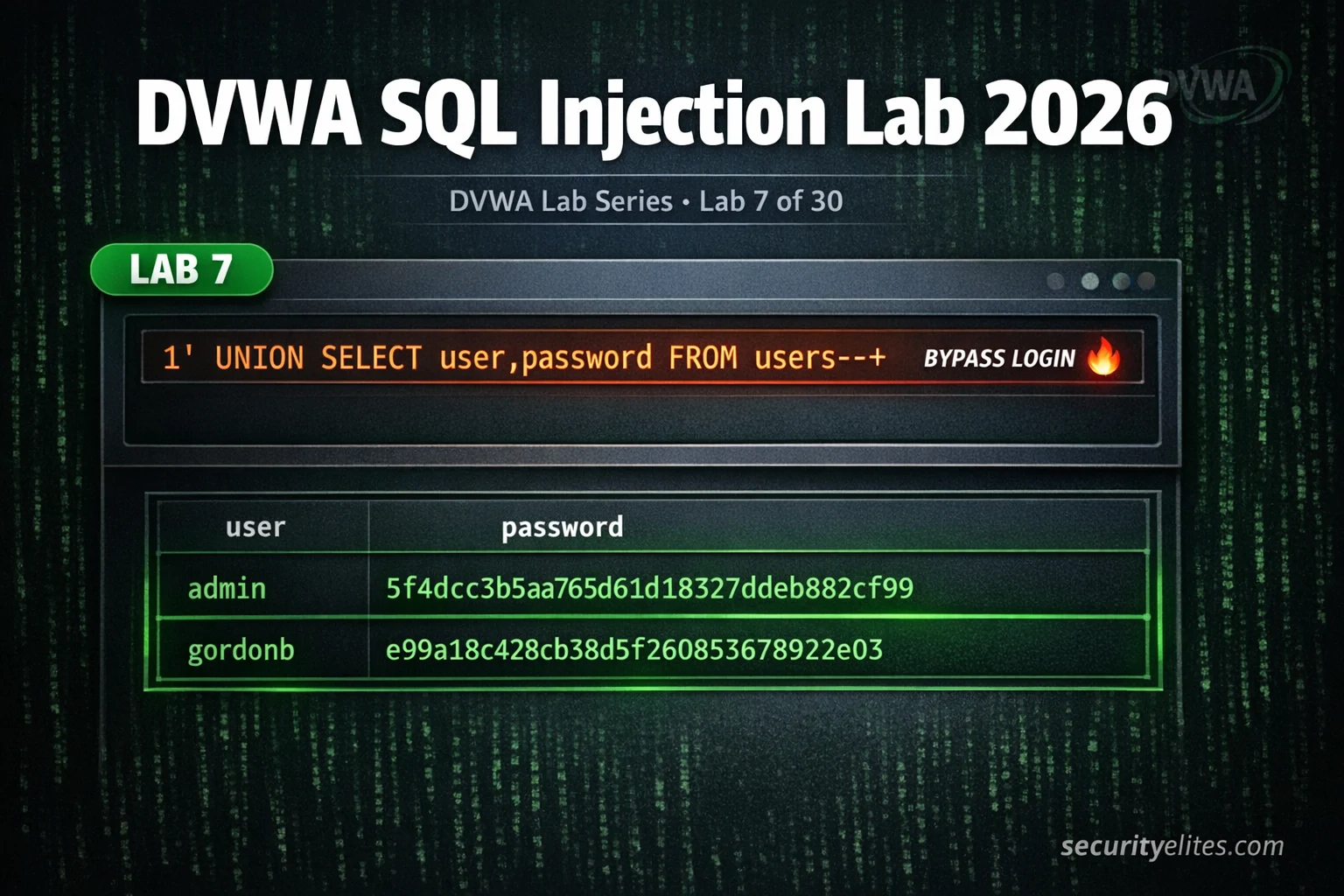
Lab 7: DVWA SQL Injection Lab 2026 — Manual Injection to Full Database Dump Complete Guide
DVWA sql injection lab 2026 — manual injection at all 4 security levels, extract usernames and passwords, bypass filters and…
How to Hack AWS S3 Buckets (Ethically) 2026 — 5 Real Misconfigurations Exposed
Hack aws s3 buckets ethically 2026 — discover 5 real S3 misconfigurations, enumerate public buckets, test ACL weaknesses and report…
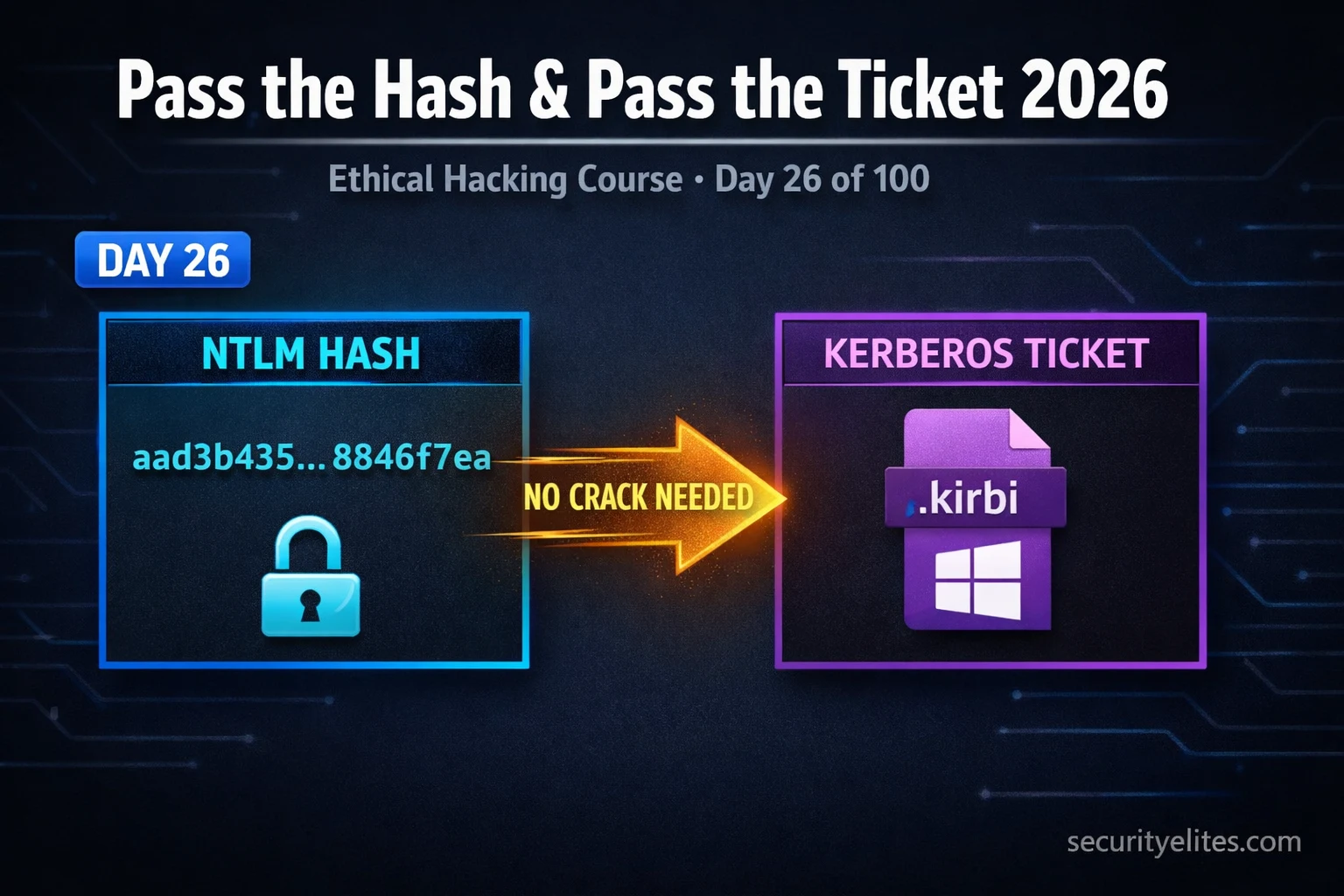
Day 26: Pass the Hash & Pass the Ticket 2026 — Lateral Movement With NTLM & Kerberos
Pass the hash & pass the ticket 2026 — exploit NTLM hashes and Kerberos tickets for lateral movement in Active…
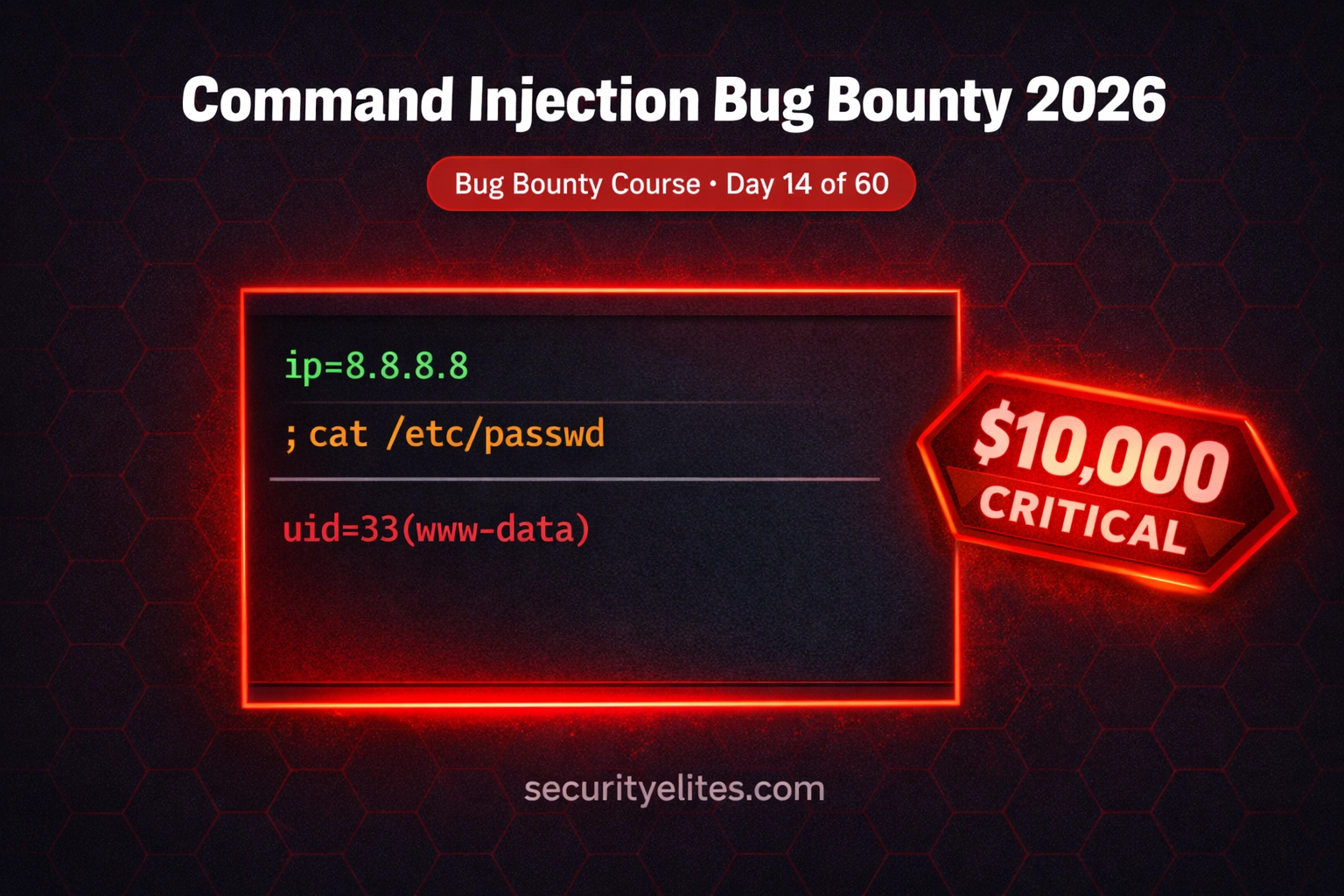
BB Day 14: Command Injection Bug Bounty 2026 — Find OS Injection in Web Apps & APIs That Pay
Command injection bug bounty 2026 — find OS command injection in web apps and APIs, bypass filters, chain with SSRF…
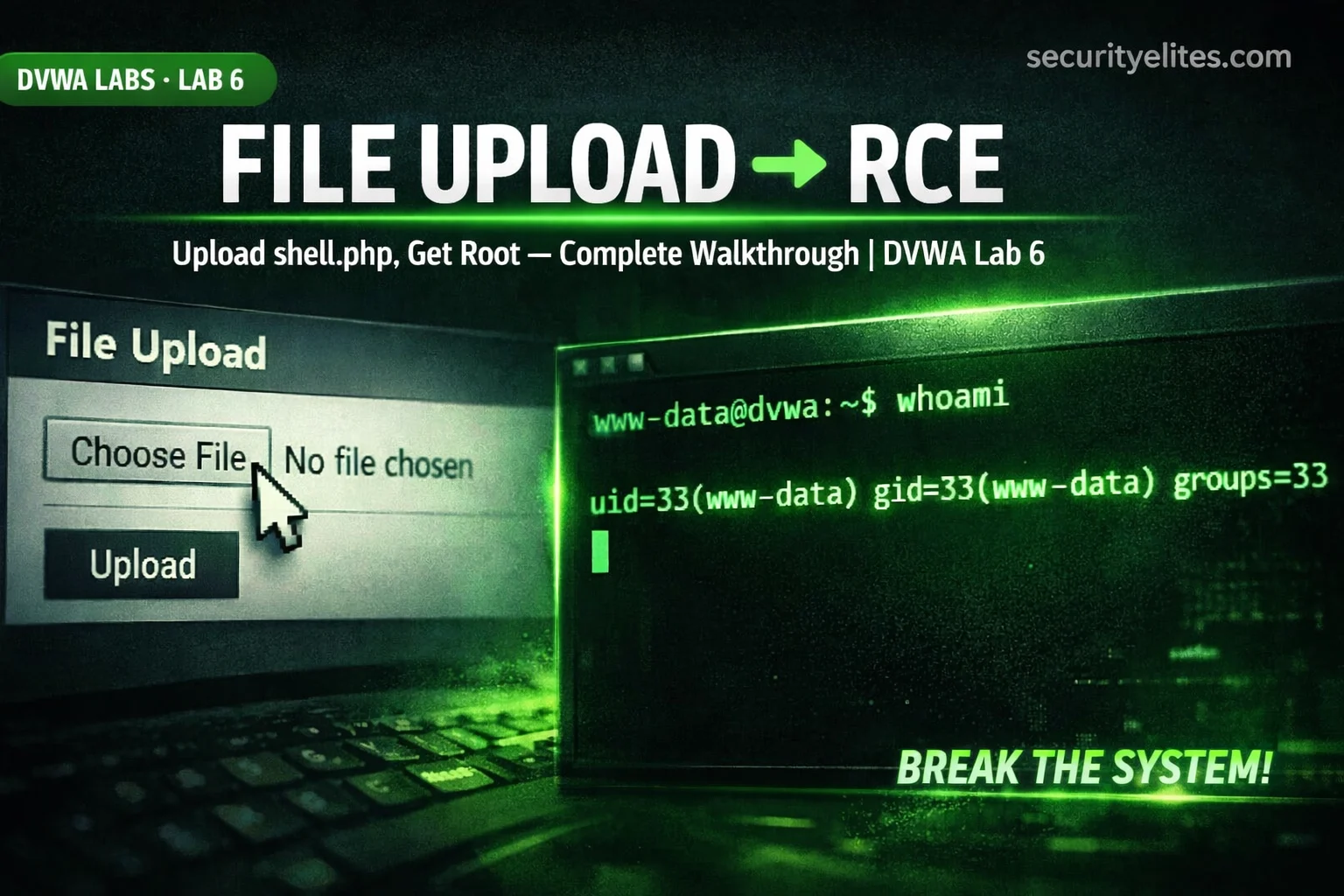
Lab 6: DVWA File Upload Lab 2026 — Ultimate Guide to Upload PHP Webshells & Get RCE Fast
Complete DVWA File Upload lab 2026 — upload PHP webshells, bypass MIME type checks, extension filtering, and achieve RCE at…
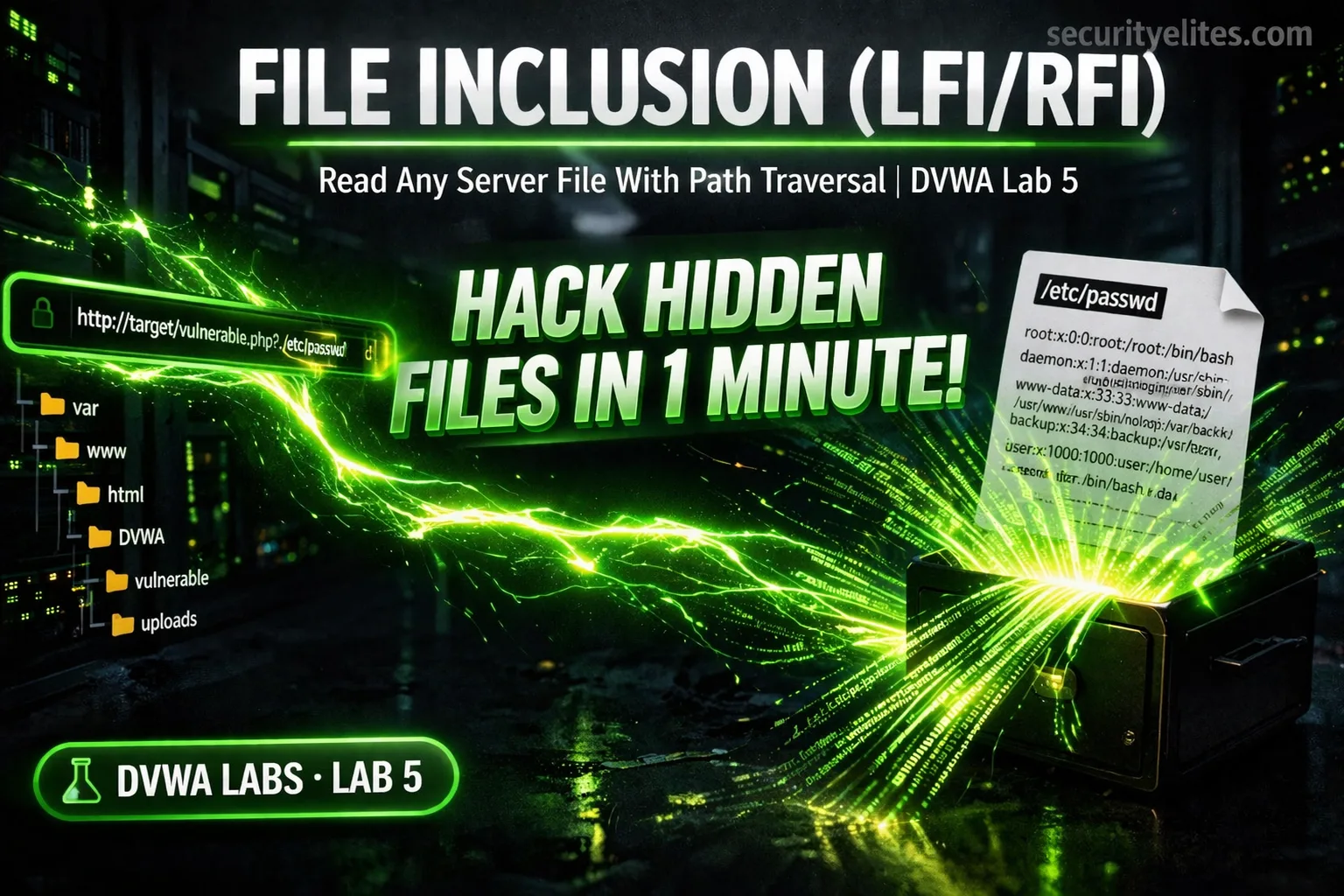
Lab 5: DVWA File Inclusion Lab 2026 — Hack Hidden Files in 1 Minute
Complete DVWA File Inclusion lab 2026 — exploit LFI to read /etc/passwd, path traversal, PHP wrappers, and RFI remote code…
Day 25: Kerberoasting 2026 — Attack & Defend Service Account Passwords in Active Directory
Master Kerberoasting in 2026 — request Kerberos service tickets, extract TGS hashes, crack offline with Hashcat, and detect attacks as…