Web Application Security
Explore web application security vulnerabilities and learn how ethical hackers identify and exploit them. This category covers SQL injection, cross-site scripting (XSS), CSRF, file upload vulnerabilities, authentication bypass, API security flaws, and session management issues. You’ll find hands-on tutorials, payload examples, exploitation labs, and prevention techniques to secure web applications. Ideal for bug bounty hunters, penetration testers, and developers who want to build and test secure web platforms.
100 articles
Lab 4: DVWA CSRF Lab 2026 — Forge Cross-Site Requests & Bypass Token Validation
Complete DVWA CSRF lab 2026 — forge cross-site requests, change passwords, bypass token validation at all 4 security levels. Hands-on…
Lab 3: DVWA Command Injection Lab 2026 — Inject OS Commands & Get a Reverse Shell
Master DVWA command injection lab 2026 — inject OS commands at all 4 security levels, bypass filters & establish a…
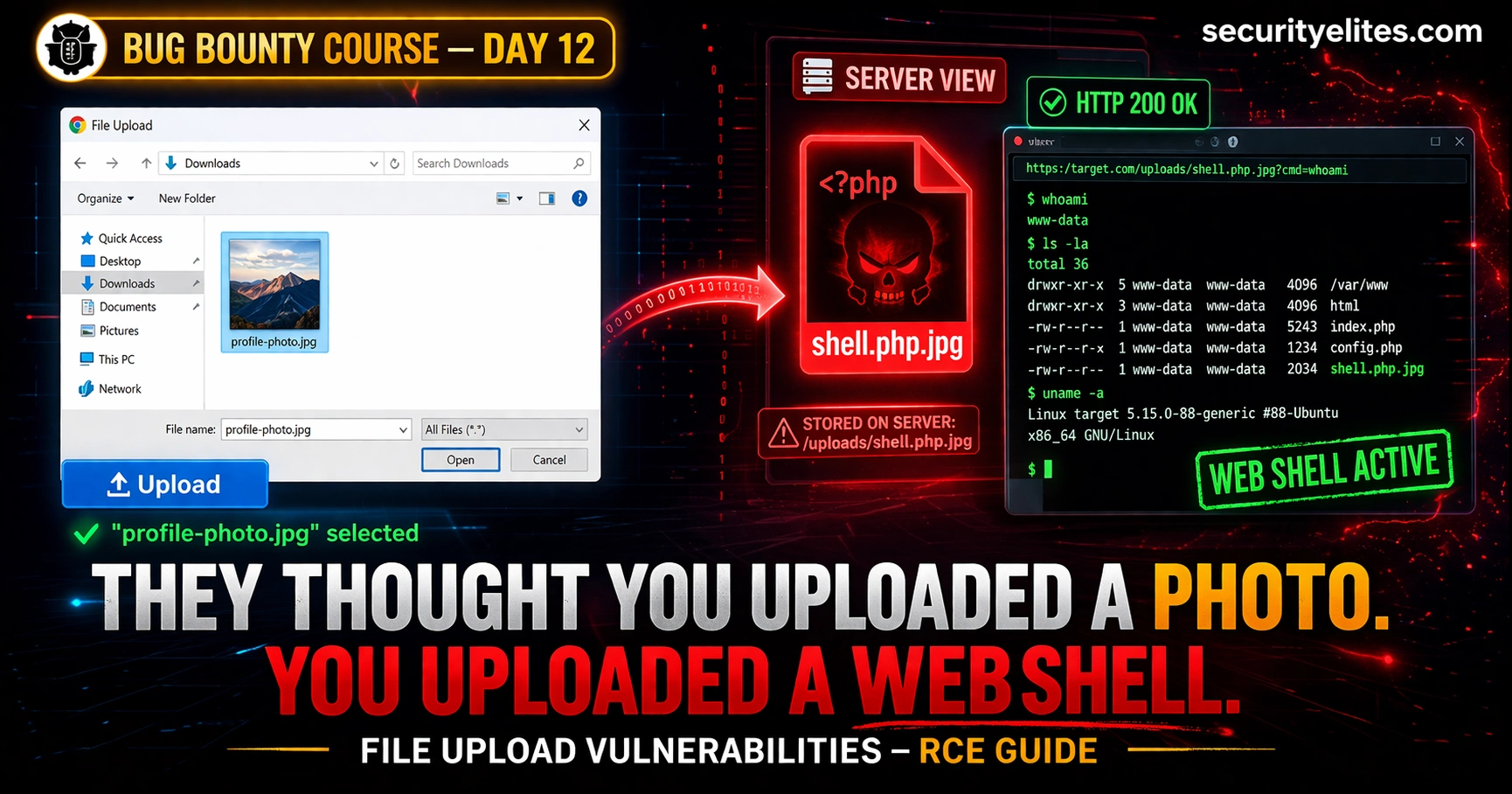
Day 12: File Upload Vulnerabilities — From Bypassing Filters to Remote Code Execution (Bug Bounty 2026)
File upload vulnerabilities bug bounty are among the highest-paying bugs in bounty programs. Day 12 covers every bypass technique—from MIME…
Browser-Based Attacks 2026 — AITM Phishing, ClickFix and Session Hijacking Are Driving the Biggest Breaches Right Now (Complete Guide)
AITM phishing, ClickFix malware and session hijacking are behind today's biggest corporate breaches. Here's exactly how browser-based attacks works and…
Cisco CVE-2026-20093 — CVSS 9.8 Authentication Bypass Explained: How Hackers Get Admin Access Without a Password (2026)
Cisco patched Cisco CVE-2026-20093 authentication bypass, a CVSS 9.8 critical flaw letting unauthenticated attackers bypass authentication and gain admin access.…
Day 11: Open Redirect Bug Bounty Hunting 2026 — Find, Chain and Report the Vulnerability That Turns $200 Bugs Into $5,000 Findings
Day 11 of 60. Master open redirect bug bounty hunting with manual testing, bypass techniques, OAuth chaining for account takeover,…
Cloud Security Hacking 2026 — How Attackers Exploit AWS, Azure & GCP (Ethical Hacker’s Guide)
Cloud security hacking is the highest-demand offensive skill of 2026. Learn IAM misconfiguration exploitation, S3 bucket attacks, SSRF to cloud…
Identity Based Attacks 2026 — Credential Abuse, MFA Bypass & Account Takeover (Complete Guide)
Identity based attacks are the #1 breach vector in 2026. Learn credential stuffing, password spraying, MFA fatigue, pass-the-cookie, SIM swapping,…
Day 10: SSRF — Server-Side Request Forgery Hunting (2026 Bug Bounty Complete Guide)
Day 10 of 60. Learn SSRF bug bounty hunting — discover server-side request forgery vulnerabilities, cloud metadata exploitation, blind SSRF…